Sabitlenmiş Tweet
ProjectDiscovery
2.8K posts


ProjectDiscovery
@pdiscoveryio
Detect real, exploitable vulnerabilities. Harness the power of Nuclei for fast and accurate findings without false positives.
Katılım Temmuz 2019
142 Takip Edilen41.6K Takipçiler

Full walkthrough with a shared Neo task link:
neo.projectdiscovery.io/share/4d1b194e…
English

[NEW BLOG]
Red-Teaming Cloud Infrastructure with Neo
We gave Neo a single prompt against an test AWS environment - no step-by-step guidance, no hints. It exploited a CI/CD auth bypass, extracted production secrets from build configs, pivoted to AWS via IMDS, and chained through a private subnet to reach the production database.
11 findings. 3 Critical. ~2.5 hours.
projectdiscovery.io/blog/red-teami…
English

When AI agents run security tasks, there's no easy way to see what network requests they're making behind the scene -- whether it's CLI tools, scripts, or browser automation.
Neo now captures all agent HTTP traffic and surfaces it in a Network tab. Agents can also search and replay their own captured traffic mid-task for smarter, context-aware testing.
Full changelog: neo.projectdiscovery.io/changelog
English

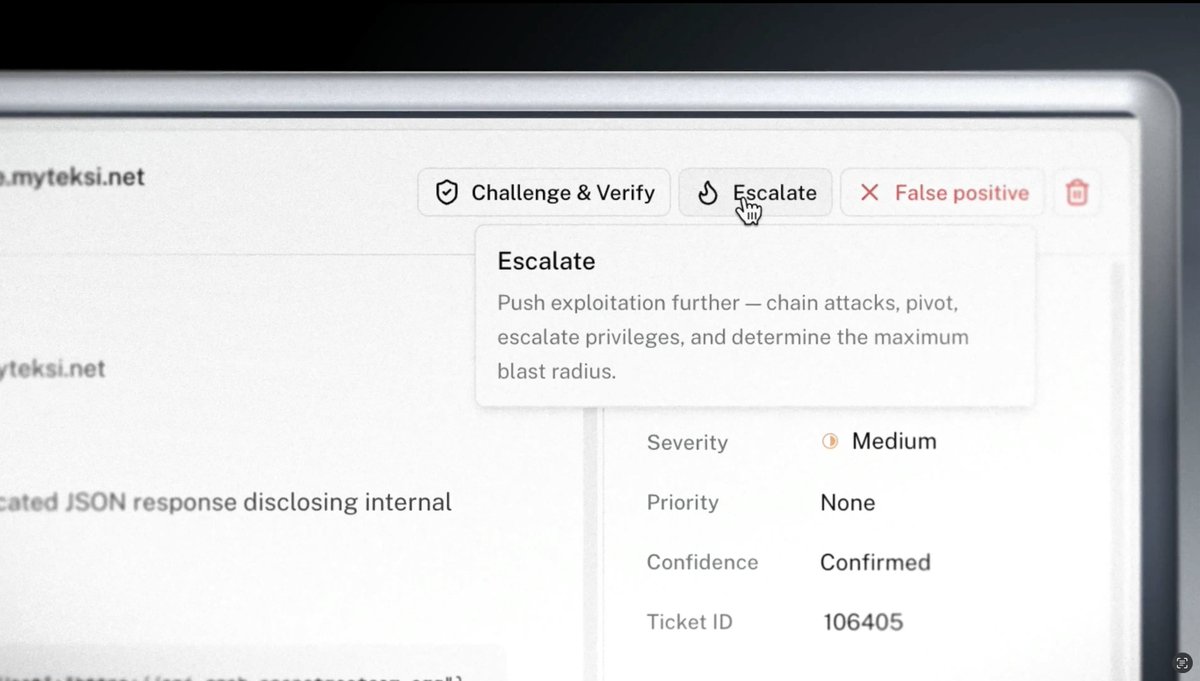
Using Neo, you can perform granular tasks like attack surface mapping or vulnerability identification which leads to deeper, high-quality findings.
projectdiscovery.io/request-demo
English

Don't run Nuclei on your printers.
(People have learned this the hard way.)
Our CEO @ehrishiraj + @todb get into this, the bug bounty program, and how time-to-exploit collapsed, all on runZero Day. Check it out:
youtube.com/watch?v=798Sy0…

YouTube
English

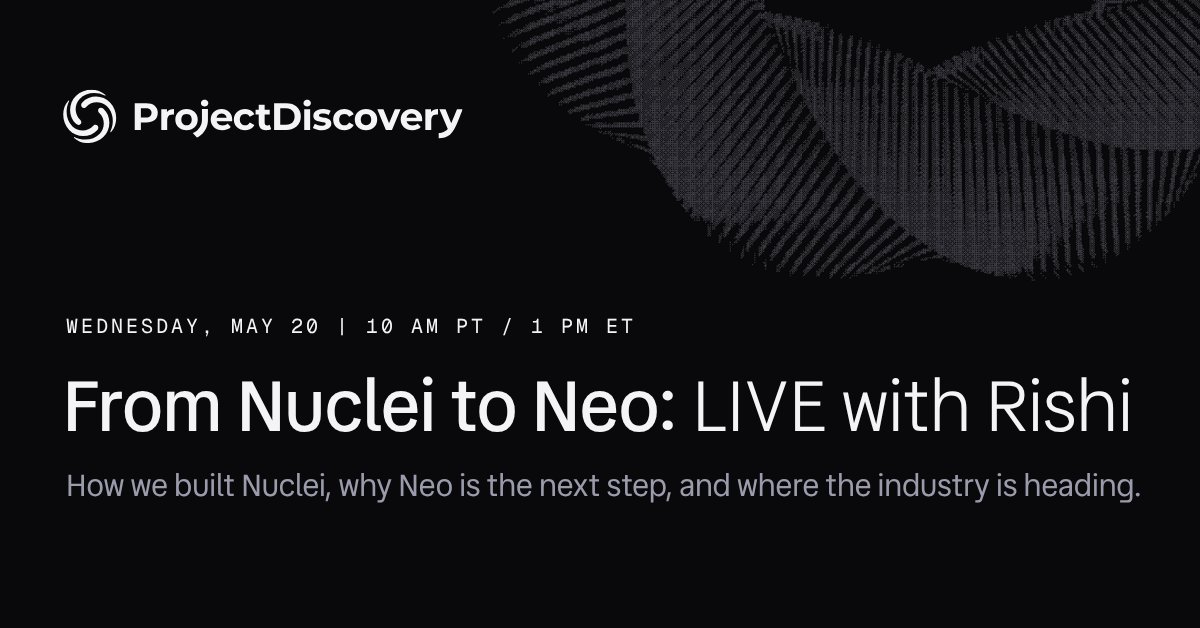
Tomorrow, our CEO @ehrishiraj is hosting a live webinar from San Francisco. Join to hear Nuclei's origin story, how Neo handles evals, false positives, and long-running workflows. We’ll close out with questions we hear from practitioners every day but never have enough time to answer.
⌛ Grab your spot → 10 AM PT / 1 PM ET. Register: bit.ly/4eLpCOk

English
ProjectDiscovery retweetledi

New agent tool: web_test_email for @neo_ai_engineer
Agents are goal-driven - when a capability is missing or a tool fails mid-run, they route around it, often reaching for public file hosts or external email services to keep going. Functional, but unscoped and risky.
Auth testing surfaces this constantly: signup flows, password resets, session handling, and host/origin trust checks all need disposable inboxes.
To close that gap, we shipped web_test_email, a purpose-built agent tool:
- Scoped to the authenticated Neo user account
- Provisions disposable inboxes on demand
- Wildcard prefix patterns for multi-account testing
- Inbox contents readable inline
See it in action in this demo: neo.projectdiscovery.io/share/715d4a78…
English

Next Wednesday, we’re hosting a live webinar to interview our cofounder and CEO, @ehrishiraj, on the inception of Nuclei, how we built the world's most widely used vulnerability scanner, and where Neo goes next.
We'll cover the questions we hear from practitioners every day, plus Rishi's take on what keeps him up at night in security.
🖤 Wed May 20, 10 AM PT / 1 PM ET. Reserve your spot: bit.ly/3PiI1HU
English

Nuclei became the world's most widely used vulnerability scanner because practitioners trusted it. On May 20th, our cofounder is going live to talk about how it happened, what we've learned, and where security tooling needs to go next.
May 20th at 10 AM PT / 1 PM ET. Spots are limited! Grab yours here: bit.ly/4eLpCOk
English
ProjectDiscovery retweetledi
🚀 Nuclei Templates April 2026 Recap is live.
226 new templates. 123 CVEs. ~10 actively exploited in the wild🔥
Running Fortinet, cPanel, Apache, WordPress, or AI/LLM infra in your environment? Time to refresh your templates
projectdiscovery.io/blog/nuclei-te…
#nuclei #infosec @pdnuclei
English
ProjectDiscovery retweetledi
@pdiscoveryio Congrats to the entire ProjectDiscovery team!
English

ProjectDiscovery has been named to @NotableCap's Rising in Cyber 2026 — 30 companies, voted by 150 CISOs.
Humbled to stand alongside this year's honorees and the alumni who came before us.
To our community: this one's yours. 🧡
notablecap.com/risingincyber
English
ProjectDiscovery retweetledi

CVE-2026-23870, CVE-2026-44575, CVE-2026-44579, CVE-2026-44574, CVE-2026-44578, CVE-2026-44573, CVE-2026-44581, CVE-2026-44580, CVE-2026-44577, CVE-2026-44576, CVE-2026-44582, CVE-2026-44572
github.com/dwisiswant0/ne…
Slovenščina