Guz
7.1K posts


Guz
@ibuGs_
iOS Developer 💻 beer, sleep, code & repeat. !⃝ 𝗧𝗵𝗶𝘀 𝗮𝗰𝗰𝗼𝘂𝗻𝘁 𝗵𝗮𝘀 𝗯𝗲𝗲𝗻 𝗱𝗶𝘀𝗽𝘂𝘁𝗲𝗱 𝗯𝘆 no one.

🚨 CRITICAL CYBERINTELLIGENCE ALERT: MASSIVE NATIONAL IDENTITY BREACH – DIGERCIC ECUADOR 🇪🇨👤📂🔓 [STATUS: EXTREME THREAT] A catastrophic compromise has been detected within the infrastructure of Ecuador's General Directorate of Civil Registry, Identification, and Cedulation (DIGERCIC). Threat actor "GordonFreeman," operating under the collective L4TAMFUCKERS, claims to have completely breached the national system, exfiltrating the identity data of virtually the entire population holding national ID cards. 🏢 Affected Entity: DIGERCIC (Ecuador's Civil Registry). 👤 Threat Actors: GordonFreeman, Izanagi, and YoSoyGroot (L4TAMFUCKERS). 📂 Compromised Assets: SQL database and a massive repository of identification images. 📊 Leak Volume: 14.8 million data records (10.8 GB in SQL). 10.6 million high-definition images of national ID cards (165 GB). 📅 Publication Date: May 4, 2026. 📊 Breach Scope (PII and Facial Biometrics) The magnitude of this attack implies that the attackers possess the capability to reconstruct the legal identity of the majority of Ecuadorian citizens: Alphanumeric Data: Full names, national ID numbers, dates of birth, marital status, digitized fingerprints, and signatures. Visual Evidence: The 10.6 million HD images correspond to facial photographs captured for the issuance of identity documents, thereby enabling biometric impersonation attacks. Infrastructure: The use of SQL dumps suggests deep-level access to the Civil Registry's master tables. 🛡️ Immediate Response Recommendations 🔒 Isolation of Critical Servers: DIGERCIC must declare a state of cybersecurity emergency and audit all data exfiltration points within its internal networks. 🔑 Financial System Alert: Banks and credit unions in Ecuador must enhance their identity verification protocols, exercising caution regarding validations based solely on photos of national ID cards. Monitor: analyzer.vecert.io #CyberSecurity #Ecuador #DIGERCIC #DataBreach #L4TAMFUCKERS #RegistroCivil #Identity #PII #VECERT #InfoSec 🇪🇨🛡️⚠️🚨👤


‼️🇬🇹🇪🇨 Azzorti, a Latin American direct-sales beauty and fashion brand operating across Guatemala and Ecuador, has allegedly been breached, with the entire database from intranet.azzorti.com and intranet.azzorti.gt offered for sale. ⠀ ‣ Threat Actor: NyxarGroup (in collaboration with Petro_Escobar & ArcRaidersPlayer) ‣ Category: Data Sale ‣ Victim: Azzorti ‣ Industry: Retail / Direct Sales / Cosmetics ⠀ The actor is selling access to two intranet sites belonging to Azzorti, claiming the dataset includes business operations data alongside customer/consultant PII. The leak is offered for $400. ⠀ What's in it: ⠀ ▪️ Internal documents ▪️ Power BI reports ▪️ Supplier information ▪️ Product catalogs ▪️ Sales records ▪️ Business charts ▪️ Quotes ▪️ 2 databases with the following structure: ▪️Codigo (code), Identificacion (ID), Consec ▪️Zona (zone) ▪️Nombres / Apellidos (first/last names) ▪️Direccion (address) ▪️Telefonos (phone numbers) ▪️Distrito / Provincia (district/province) ▪️Camp Ingr, Digito, Cupo ▪️Pedidos (orders) ▪️Digito Anterior ▪️Direccion Referencia (reference address)



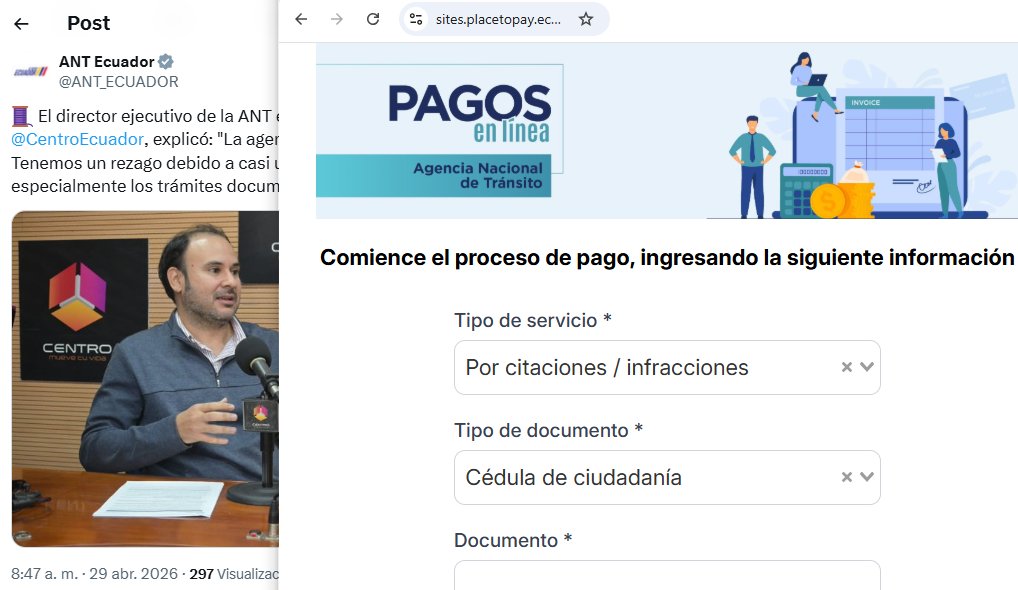
@ANT_ECUADOR @rocurun @Pau88g @skueffner @ghserrano #AlertaDigitalEC Se alerta de filtración de 17 millones de registros de una base al 2026 de @ANT_ECUADOR; la institución indica que los campos de muestra no corresponden a su base pero que información de automotores los tienen varias instituciones x.com/ANT_ECUADOR/st…



La ANT ha incumplido su obligacion legal de notificar Este evento a la superintendencia de datos y a @EcuCERT_EC de Arcotel segun articulo 43 de la ley. Ademas incumplido su obligacion legal de avisar de esta vulneracion a Los titulares de datos segun articulo 46 id. Habra multas


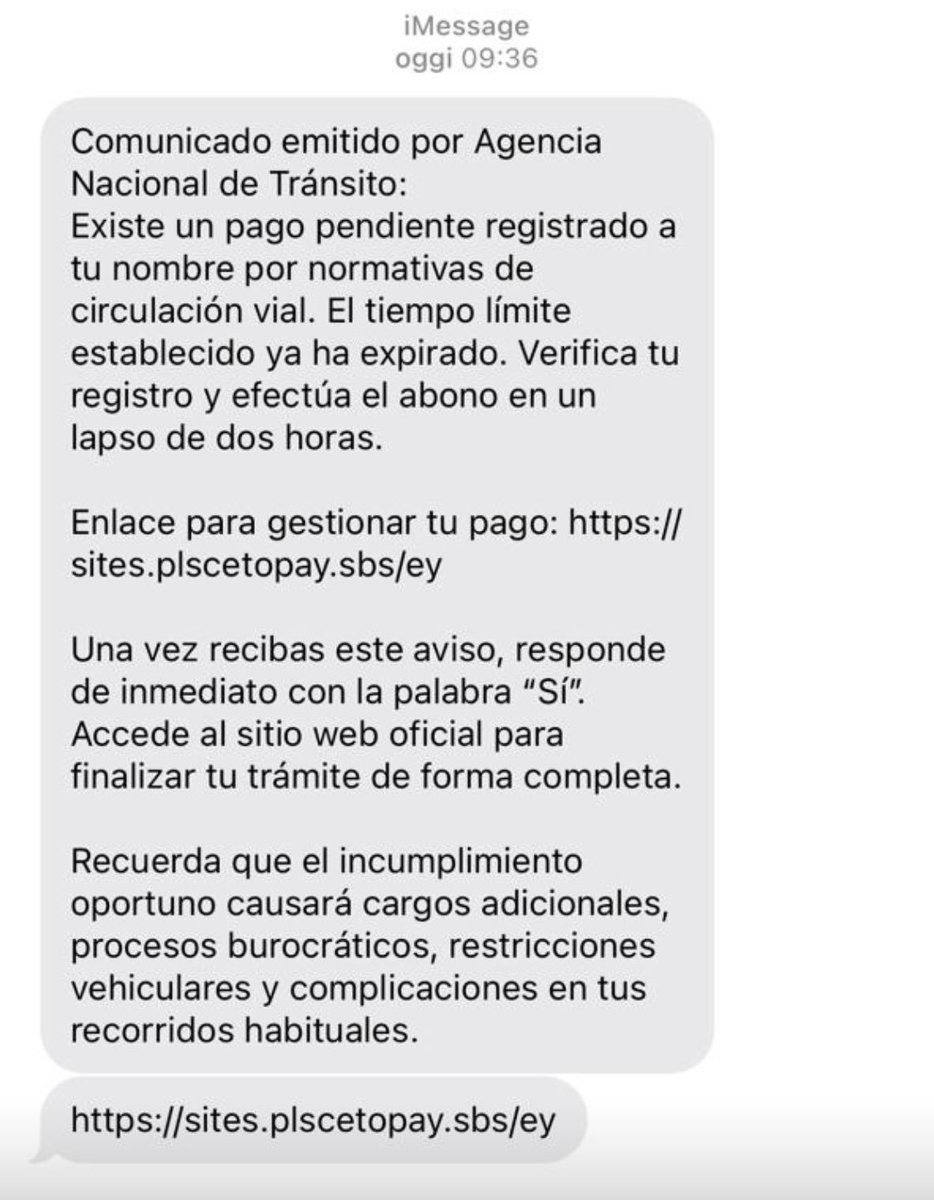
Me intentaron estafar vía iMessage




LinkedIn extrae información privada tuya y la envía a empresas de seguridad Israelíes Microsoft y LinkedIn está llevando a cabo una de las mayores operaciones de espionaje corporativo de la historia moderna. Cada vez que alguno de los mil millones de usuarios de LinkedIn entra, un código oculto busca en su ordenador el software instalado, recopila los resultados y los transmite a los servidores de LinkedIn y a empresas externas, entre ellas una firma de ciberseguridad estadounidense-israelí. Al usuario nunca se le pregunta. Nunca se le informa. La política de privacidad de LinkedIn no lo menciona. browsergate.eu





🇺🇸 | La asesora espiritual de la Casa Blanca, Paula White, compara a Trump con Jesucristo, afirmando que fue traicionado, arrestado y acusado falsamente. Ella dice que Trump resucitó como Jesús, venció a la muerte y vencerá a todos sus enemigos.