
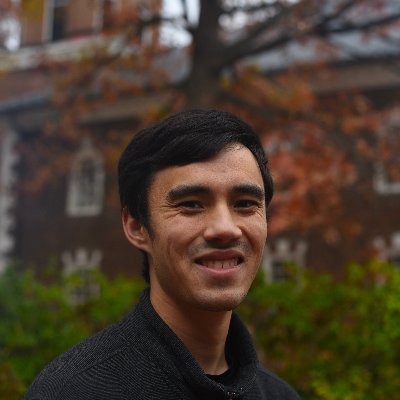
Ivan Fratric 💙💛
1.3K posts

Ivan Fratric 💙💛
@ifsecure
Tech lead and security researcher at Google Project Zero. Author: Jackalope, TinyInst, WinAFL, Domato. PhD. Tweets are my own. Backup @[email protected]


.@__sethJenkins updated our 0-click exploit chain to work on a Pixel 10 with an eye-popping driver bug! We’ll be presenting this work Saturday @offensive_con projectzero.google/2026/05/pixel-…








Part 2 of @tiraniddo’s Windows Administrator Protection journey is here! projectzero.google/2026/02/window…



No security feature is perfect. @tiraniddo reviewed Windows’ new Administrator Protection and found several bypasses. projectzero.google/2026/26/window…

Today, Project Zero released a 0-click exploit chain for the Pixel 9. While it targets the Pixel, the 0-click bug and exploit techniques we used apply to most other Android devices. projectzero.google/2026/01/pixel-…





