Ahmed Najeh
79 posts


Ahmed Najeh
@im4x7
Bug Bounty Hunter 🍳 Vulnerability Analyst https://t.co/dFaiVVBTsg #bugbounty
Katılım Ocak 2023
34 Takip Edilen2.7K Takipçiler

🥳Finally got some students interested in CTFs, and we played one over the weekend.
Here's my write-up for the web challenges from CYBERGON CTF 2024.
benkyou.tech/2024/12/11/cyb…
English

New Blog post: DUCTF 2024 ESPecially Secure Boot Writeup
elttam.com/blog/ductf24-e…
English

My @securitytrails #reconmaster methodology/thoughts in a thread. I started somewhat late, many people already in the millions of hosts discovered. My first instinct was to automate the submission of Certstream data. 1/n
English
Ahmed Najeh retweetledi

Congratulations to @xXABooDIZXx @im4x7 @BhavarHrishi and @itheodorakos808 for clearing our Certified Red Team Professional exam!
#ADLab #CRTP #AlteredSecurity cc @nikhil_mitt
alteredsecurity.com/adlab

English
Ahmed Najeh retweetledi

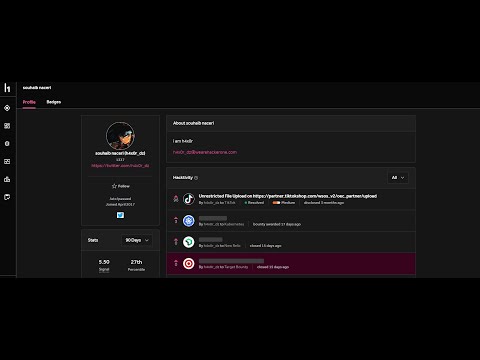
I ranked #1 in both Reports and Reputation and placed #14 overall at the Live Hacking Event #H1-702 in Las Vegas by HackerOne.
During the event, I Reported [Critical/High/Medium/low] vulnerabilities in TikTok and Epic Games. This was my first Live Hacking Event, and I'm really proud of what I achieved.
Thank you @Hacker0x01 For the Opportunity
#bugbounty

English

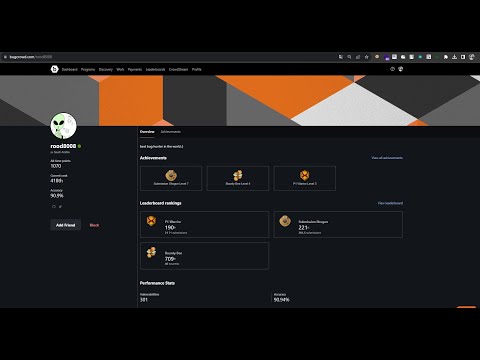
Exciting times at the #AmbassadorWorldCup with @Hacker0x01!
Proud to have collaborated with some incredible 🇮🇶 hackers!



English

@Suryesh_92 @zomato You are threatening to publish a vulnerability and you want them to give you a reward
Brother, things don't work like that here
Respect the field you are in
And dealt with professionally
English

@CBhelpline Son of a bitch, fake account
I'm having a problem and you're trying to fool me, you idiot
English

@im4x7 إبراهيم حجازي
محمد فتحي
مؤمن علي
احمد ربيع موسي
احمد سلطان
فارس وليد
يوسف الجنرال
العربية

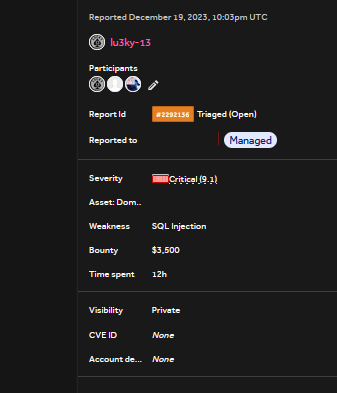
@lu3ky13 @Hacker0x01 I always follow you and I am proud of your work 😍
English

Despite the limited time I had for bug hunting in 2023, the results were unexpectedly rewarding. My engagements were sporadic, fitting into the rare pockets of free time in my schedule. Nonetheless, I managed to earn $45,000 on H1 and > 10,000$ on other platforms
#bugbounty

English

@Mosa_A101 When it causes a bypass to protect what will be acceptable
English

#bugbountytips #bugbounty #cybersecurity #Pentesting #Hacking #bugcrowd #Hackerone #IDOR #XSS #SQLi
in the beginning
The whole problem lies in not setting a specific limit for sending and receiving data
I found a private domain name
Requires login
I tried logging in using my account on the main site, but it did not work
There I got `reset the password`
I entered my email, but it was written to me that this email is not linked to an account
I learned that this is domain-specific to the site and it is not possible to create an account within it
__________
At first, I tried to search on Google through the company name for the emails associated with them, but I did not find an email registered in the site’s database.
_________
Therefore, I decided to collect all the names of employees within the company through the company’s page on LinkedIn and saved them in a txt file. name.txt
Through tools programmed in Python, I get a list of emails with domain like photo
python3 namely.py -nf name .txt -d domain.com
________
Then I took the form to reset the password
And I brute force on the emails
Until inside the script, I got a result from an email that was different from the other emails
I tried using email to reset the password and an OTP box appeared
I tried to enter random numbers to check whether there was a limit on attempts, but there was not
So I also decided to brute force the OTP
And I entered his board
It was a company-specific system and contained sensitive information about employees
*The picture is only a representation and does not contain information about the actual web

English

@im4x7 did the otp box tell you how many numbers should the otp be ?
English