marce retweetledi
marce
154 posts


marce retweetledi
marce retweetledi
marce retweetledi

I've written a post on SELinux and some public bypasses for Android kernel exploitation. It's especially relevant for Samsung and Huawei devices due to their use of hypervisors. Check it out here: klecko.github.io/posts/selinux-…
English
marce retweetledi

🚀 We're back with a fresh blog redesign! Dive into @Diego_AltF4's latest post, which offers an in-depth analysis of CVE-2023-22098, including a reliable PoC to escape VirtualBox. 🛠️ Unleash your virtualization magic now! Link below ⬇️
English
marce retweetledi

🚨🚨ATENCÓN🚨🚨
#HackOn2025 ya tiene fecha oficial🎉. Por primera vez, el evento tendrá lugar durante dos días:
28 de febrero y 1 de marzo
⏳Próximamente comunicaremos más novedades de esta edición⌛️

Español
marce retweetledi

🚀 New blog alert! 🚀
Dive deep with our latest posts:
🍎 "TCC Overview and Internals" - Learn how one of the main macOS protections work
🐝"Intro to Development Using eBPF" - Start your journey with eBPF and Docker!
Hope you enjoy the new content made by @esquilichii
English
marce retweetledi

Beyond Android MTE: Navigating OEM's Logic Labyrinths by @patateqbool @maxpl0it @MateuszFruba and @munmap now live!
English
marce retweetledi

This is what I've been doing for the last few weeks! I'm trying to write a hypervisor-based fuzzer to fuzz linux userspace binaries at native speed while having fast memory resets and code coverage
github.com/klecko/kvm-fuzz
English
marce retweetledi

Patch candidate for Chrome v8 Use-after-free to RCE bug (CVE-2024-3914) exploited by @0x10n at Pwn2Own 2024 Vancouver against both Chrome and Microsoft Edge. Patched in Chrome 124.0.6367.60/.61
This is not "quite" v8 - it's kinda blink reachable from v8. Classic array neutering bug?!

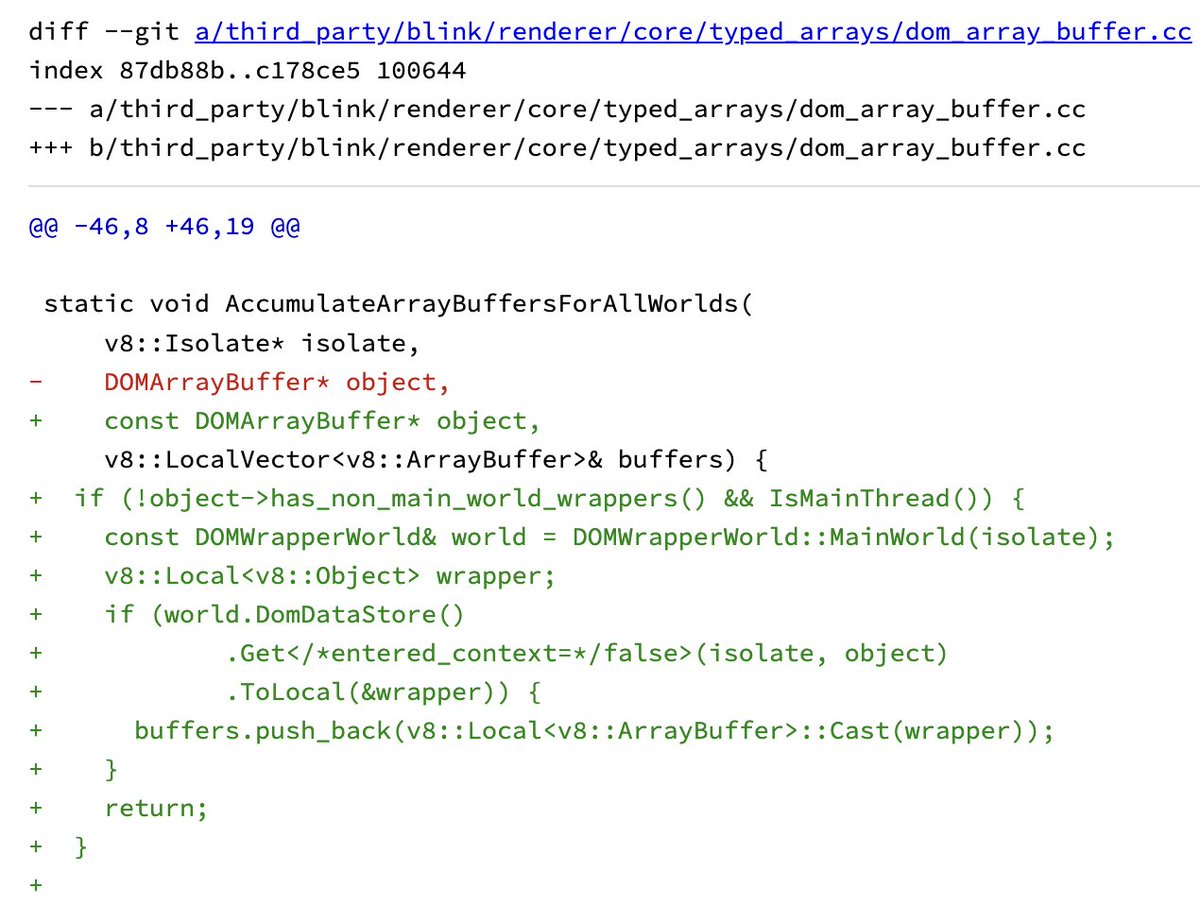

English

Check this out. Some friends and I decided to set up a blog. Hope you like it, feedback is welcomed :)
zeroclick.sh@zeroclicksh
New post is up!! . Tired of not solving FSOP challenges on the latest libc? You don't need to look any further;) Intro to FSOP exploitation and House of Paper by @pop_rdi_ret zeroclick.sh/posts/fsop-int…
English
marce retweetledi

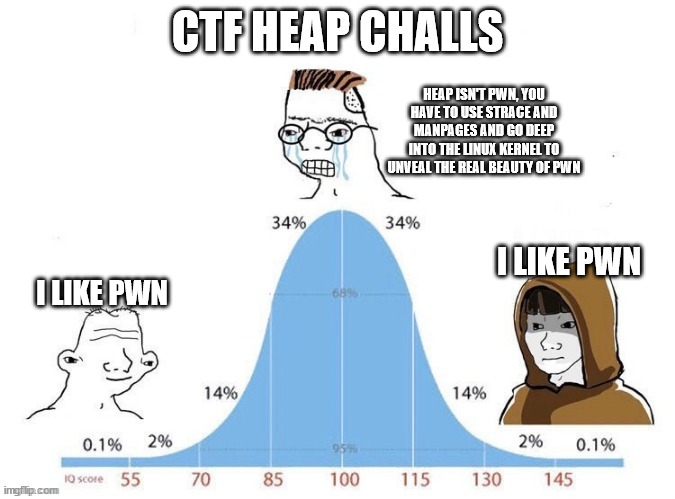
Easy right? Well then here is the writeup for a CTF pwn challenge that requires both linux heap and FSOP exploitation techniques.
@pop_rdi_ret is the creator of both the challenge and the write up.
zeroclick.sh/posts/la-casa-…
zeroclick.sh@zeroclicksh
New post is up!! . Tired of not solving FSOP challenges on the latest libc? You don't need to look any further;) Intro to FSOP exploitation and House of Paper by @pop_rdi_ret zeroclick.sh/posts/fsop-int…
English
marce retweetledi

New post is up!! . Tired of not solving FSOP challenges on the latest libc? You don't need to look any further;)
Intro to FSOP exploitation and House of Paper by @pop_rdi_ret
zeroclick.sh/posts/fsop-int…

English
marce retweetledi

Keep calm and Qemu on!!
If you want to see how to exploit a vulnerable PCI device and escape from Qemu, take a look at the writeup that @Diego_AltF4 and @t0ct0u have prepared about their HackOn 2024 challenge.
zeroclick.sh/posts/quememu-…
GIF
English
marce retweetledi

This looks like a candidate for Chrome v8 0day bug used by @_manfp in his Pwn2Own 2024 exploit (CVE-2024-2887, just patched in Chrome stable 123.0.6312.86/.87)
wasm module decoder had a missing check of type section size in a branch of DecodeTypeSection, easy to spot manually:

English
marce retweetledi
marce retweetledi

Empezamos a calentar motores para #HackOn2024 🔥, por eso sorteamos 1 entrada para la @rootedcon de Madrid.
Para participar debes:
📝Seguirnos @HackOnURJC
🔁RT
🗓️Asistir el día 22 al evento
Tienes hasta el día 21 de febrero para participar.
¡Suerte a todos!🍀
Español
marce retweetledi

🚨Confirmamos cuarto taller🚨
Daniel Monzón (@stark0de1) y Diego Palacios (@Diego_AltF4), alumno del grado de Ingeniería de la Ciberseguridad, impartirán un taller utilizando la técnica Fuzzing para el crasheo de programas. 👨💻
Gracias por participar en la #HackOn2024.🎉

Español
marce retweetledi

Hello, are you a nerd who likes malware? Us too! Our sponsor @MalDevAcademy has hooked us up with 3 lifetime licenses to their courses.
Thank you to @mrd0x for the gifts!
Leave a comment below for a chance to win!
English