Sabitlenmiş Tweet

Went on a bit of a side quest and got my first IOS App Published!
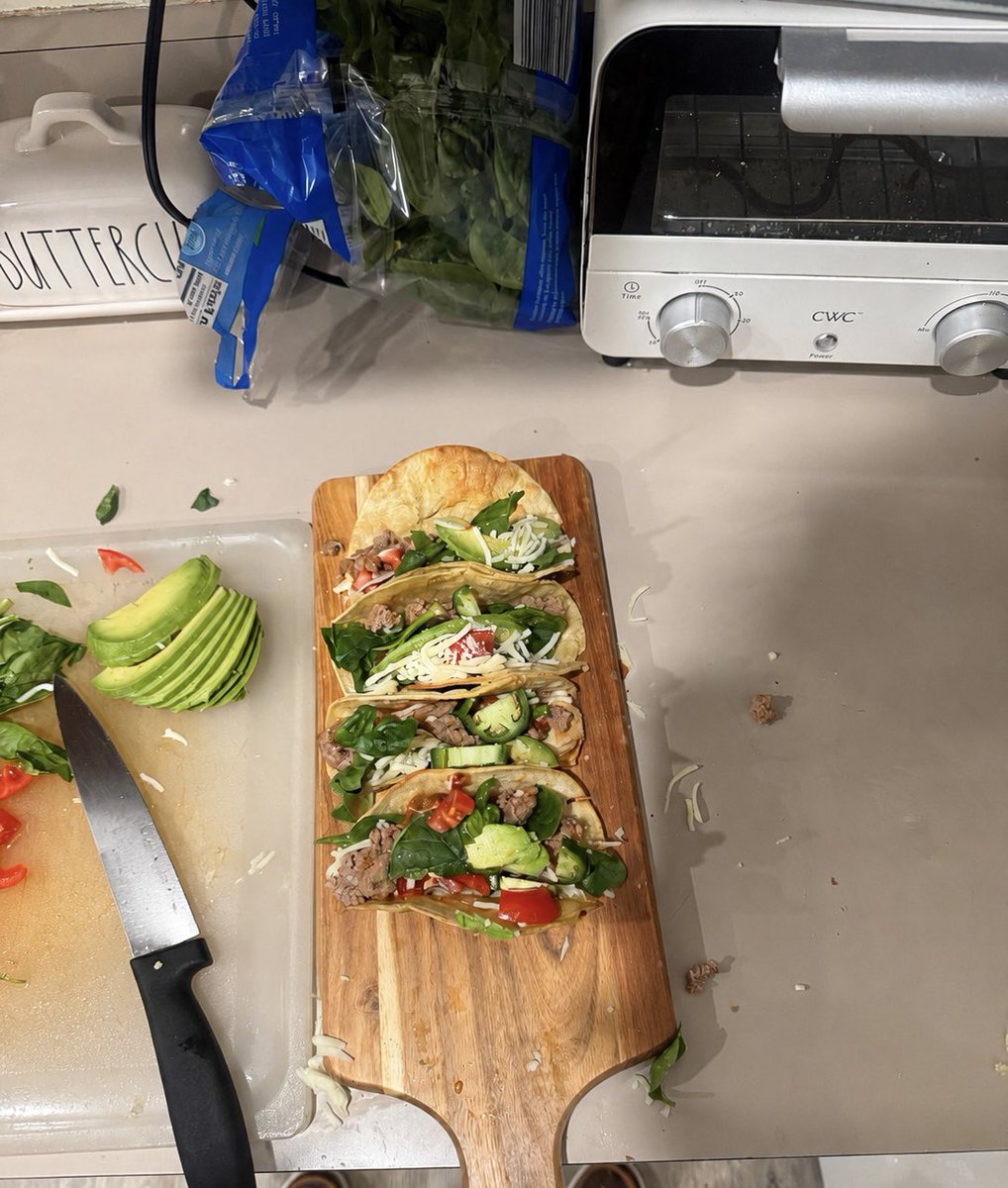
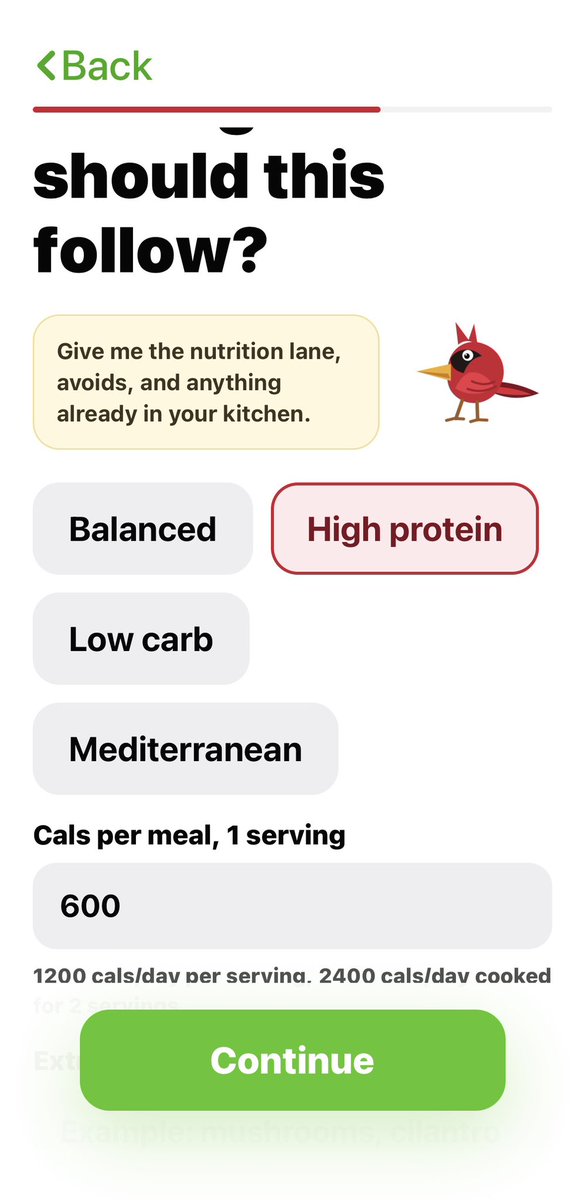
CutPlate AI is a free app focused on creating a healthy meal plan for the week while giving you a grocery list that includes all the ingredients you may need so there is limited waste
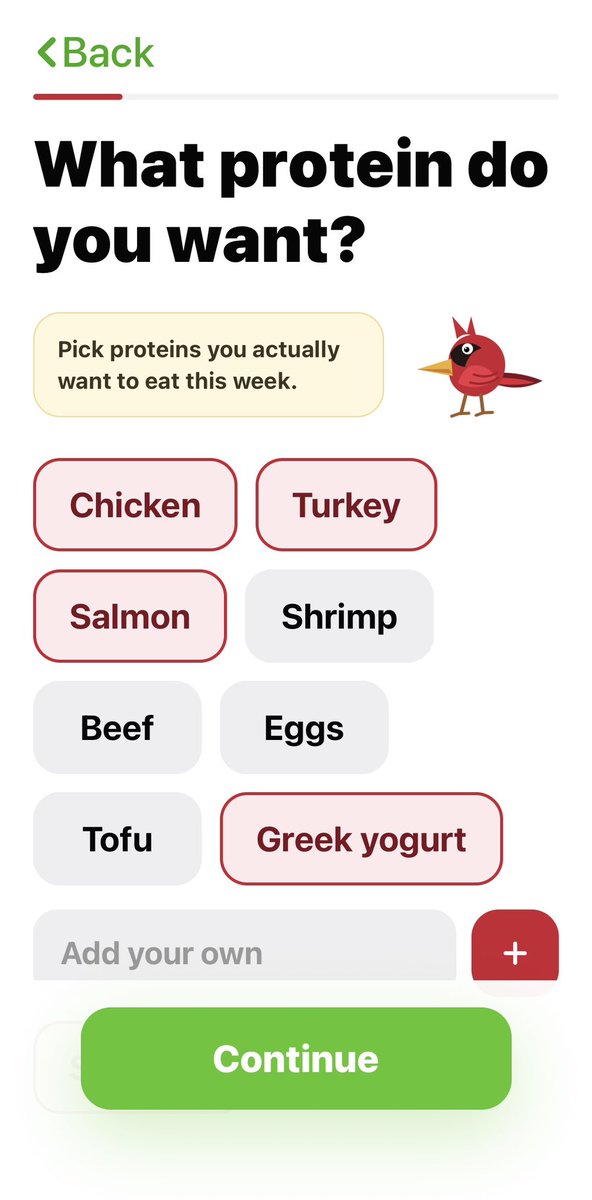
The app finds recipes for you based on what protein you select, any allergies, and your budget
Check it out at the App Store and let me know what you think!


English