Jeswin Mathai
927 posts


@jeswinMathai
Chief Architect, SquareX (@getsquarex)





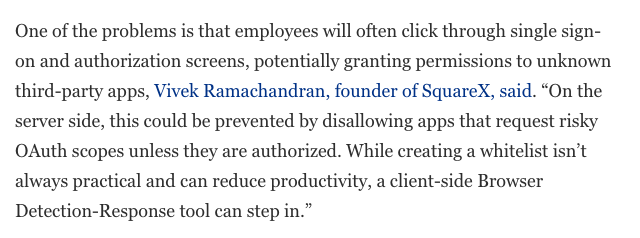


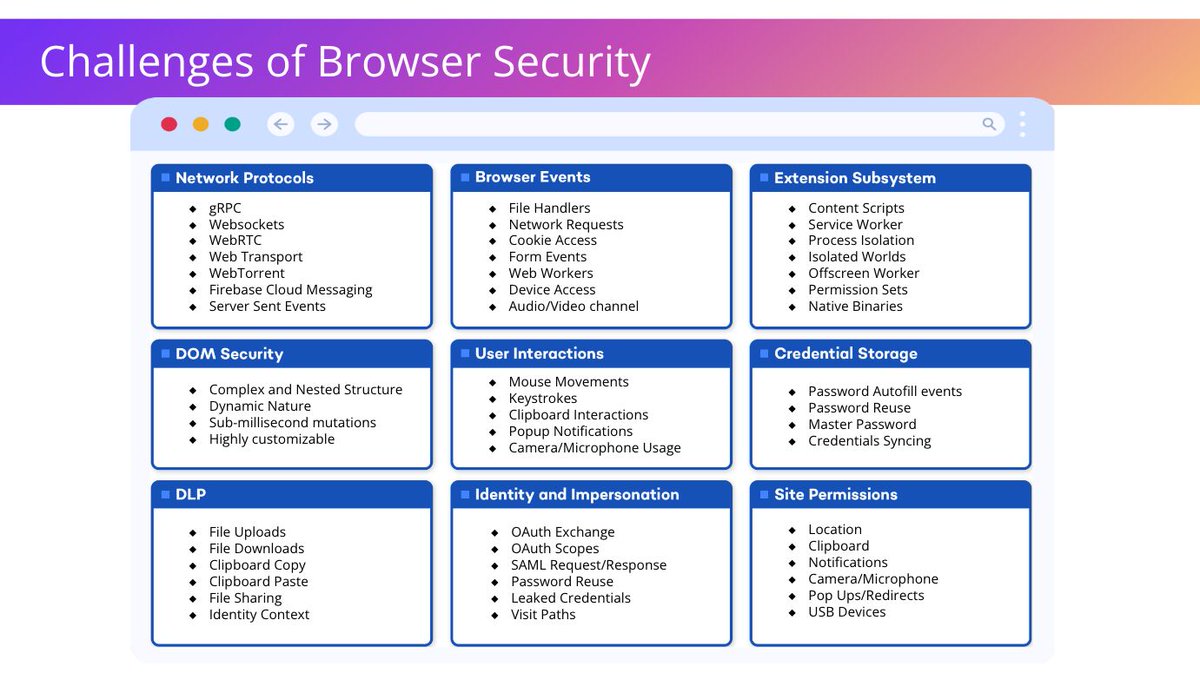
Can a Chrome Extension be taken over from the Chrome Store with just a few clicks? SquareX has uncovered targeted attacks on Chrome Extension developers aimed at taking over the chrome extension from the Chrome store - after this the attacker might try to push a malicious modification to the extension and attack it's users. Btw variants of these attacks have been used in the past to steal cloud data from google drive, one drive etc. So how does this attack work? At it's core this is an identity attack - the attacker creates a fake "Privacy Policy Application" which tries to connect to the developer's account and gain access to his Chrome store account. We show how SquareX's monitoring capabilities is able to detect this Attacker "shadow SaaS" app and how policies can be applied to block this attacks. We've given one example of such a policy but there are many ways our product can help build out attack mitigation for this. It is important to note that as this is an identity attack with entire life cycle in the browser - standard Remote Browser Isolation cannot detect this. For more information check out Identity attack demos: sqrx.com/usecases/ident…










Visitors at the booth are using scan.browser.security to assess their security posture using our tool that simulates real-life attacks and identify vulnerabilities in their current security stack. Test it for yourself against your existing solutions!