Jim Borrowinson 🍚 ⛓
14K posts


Jim Borrowinson 🍚 ⛓
@jimborrowinson
Giacomino, guardiano della galassia e dell'iperspazio 🐈

























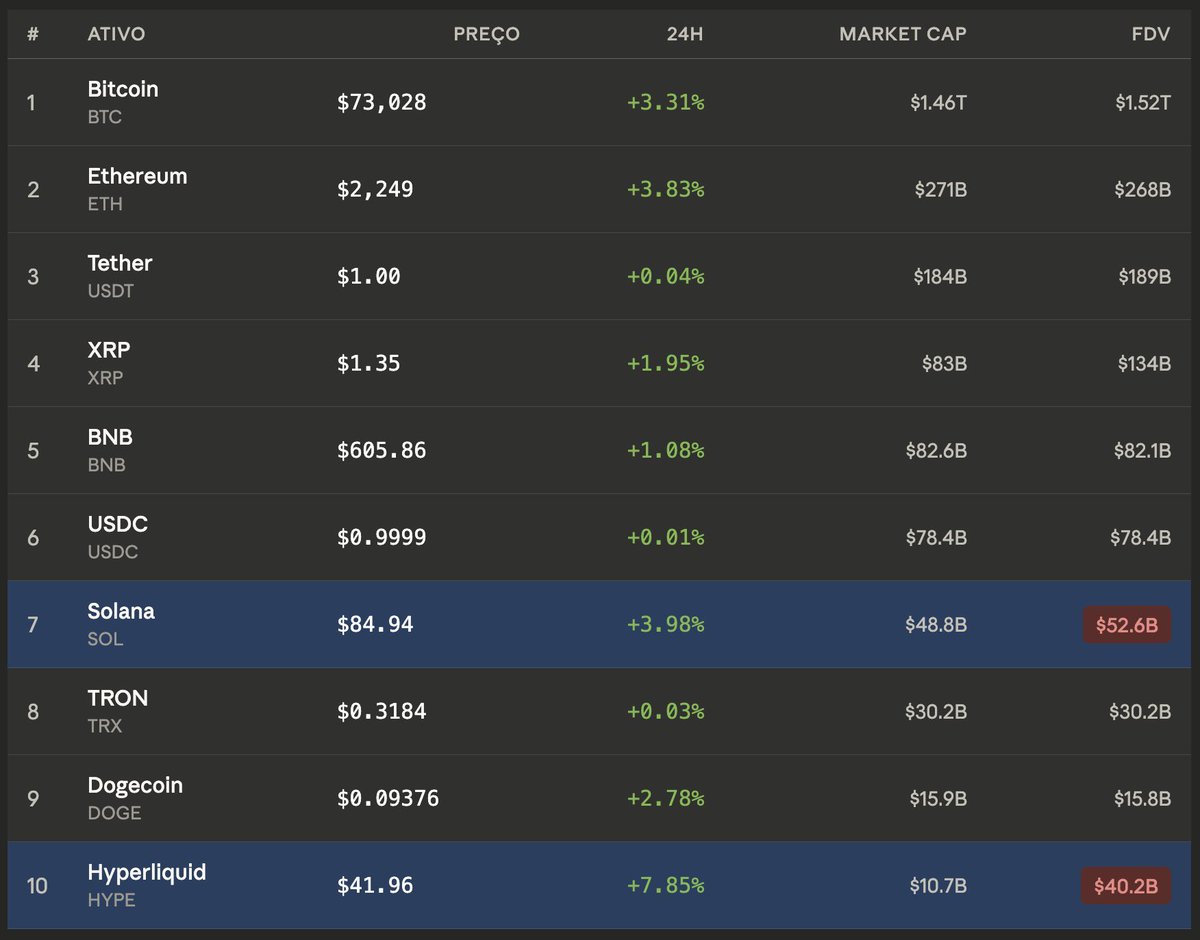
Protocols or networks that you should not trust or about to die: Resolv Labs - major fumble, reputation is done, but USR collateral is safe Cardano - dead since 2022 MegaETH - their public sale turned into a scam called KPI unlock, trust lost Aave - founder did a hostile takeover and killed the DAO, user lost $50 mil on a swap, v4 will likely be the end of AAVE dominance Ethena - USDe mcap crashed 8 bil since the depeg, why take that risk for 3.5% yield? Morpho - its curators will get your LP drained like with USR and many others Unichain - the chain that never needed to exist, pointless. TVL crashed 95% YieldBasis - promised huge BTC yields, delivered Temporary Redemption Discounts or negative yields Plasma - 24h chain revenue $473. TVL crashed 89%, XPL down 95% Story - IP token down 96% since founder bailed. Chain TVL $300k XRP - never had a use case, never will have a use case. Treat it as a meme coin ICP - token down 99%. 12M TVL Liquity - LUSD and LQTY had their run, now -99% in price and mcap List is not exhaustive. What did I miss? Hit a follow @duonine for my next list on protocols or networks you should actually trust.