jmpews
112 posts


jmpews
@jmpews
Security Researcher | Alibaba | sharedpage
Katılım Haziran 2013
197 Takip Edilen1.7K Takipçiler
jmpews retweetledi

Our very first blog post: “iOS 17, new version, new acronyms” #iOS17 #DFF #sptm #txm
df-f.com/blog/ios17
English

@rh0main @fridadotre other tricks to trace syscall:
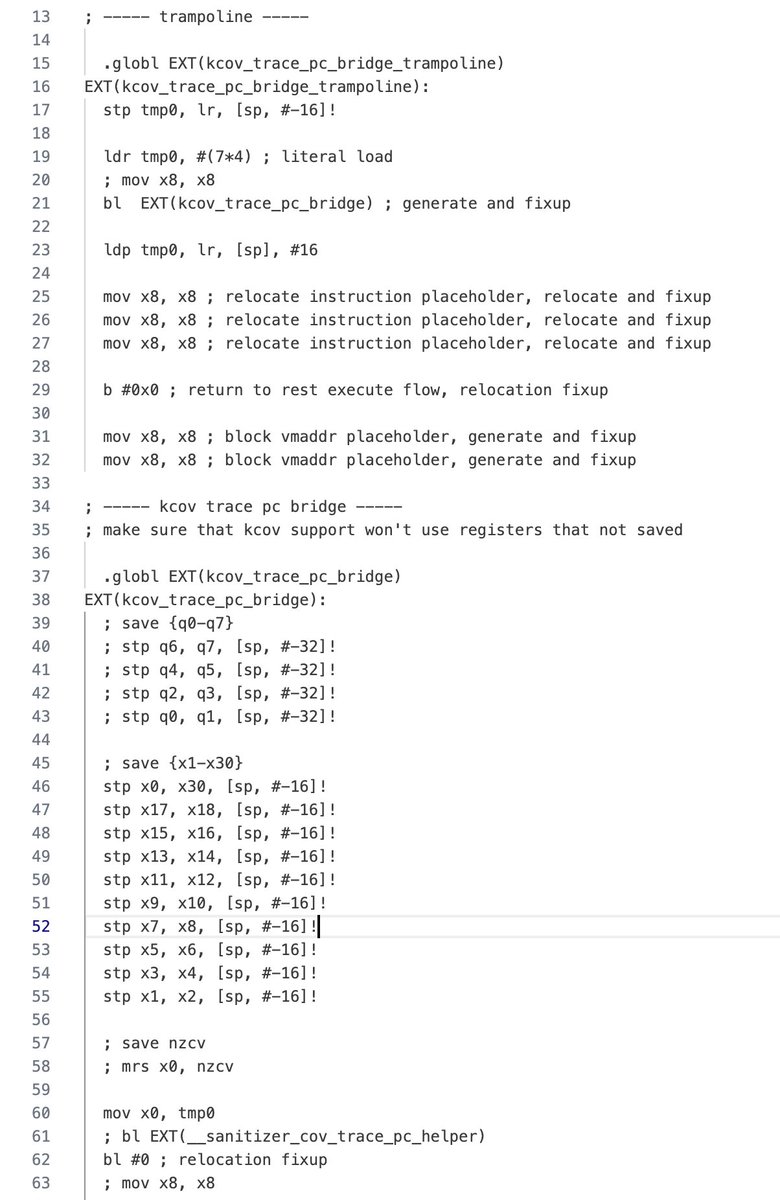
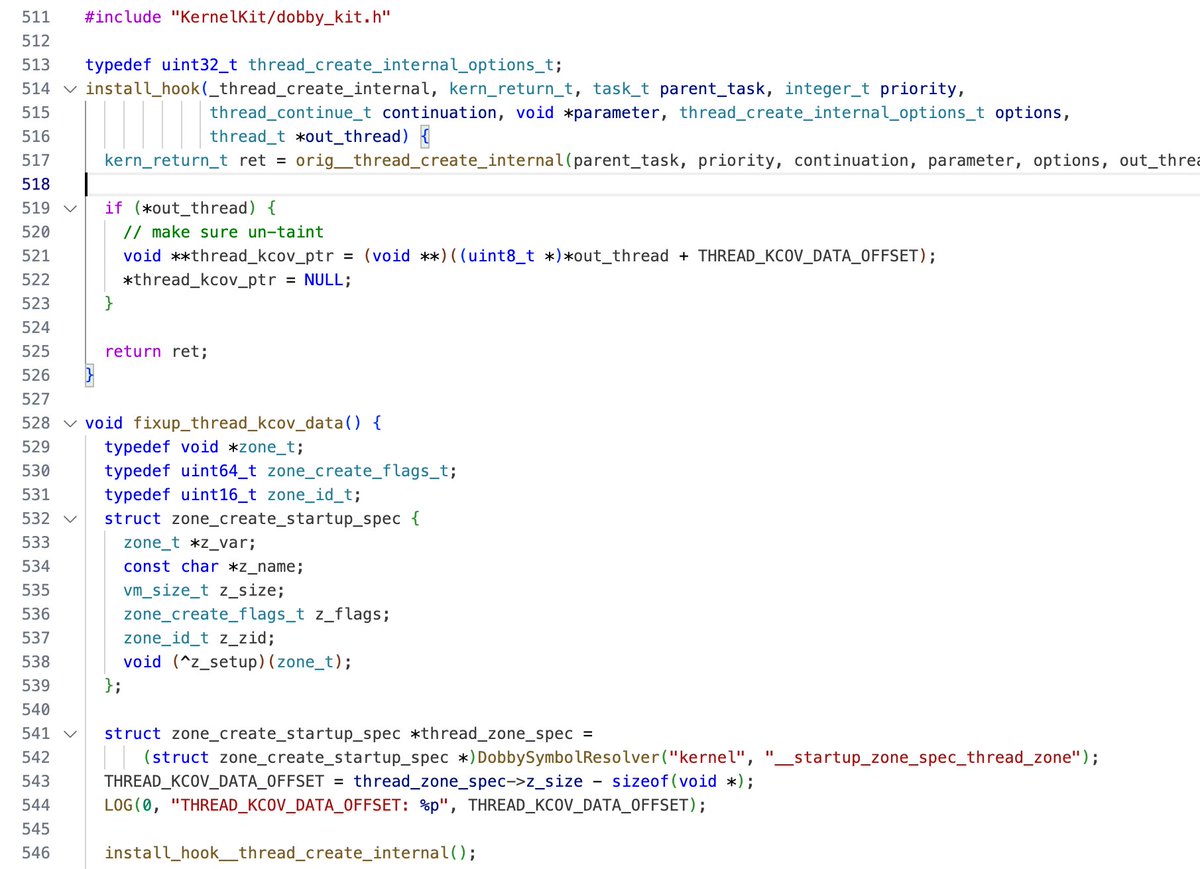
1. trace with dobby instrument(single instruction)(usersapce level)(github.com/jmpews/Dobby/b… maybe compile failed)
2. trace with kperf support(ktrace + ktrace_event_t parser)(kernel level)
3. dtrace on silicon(manual spawn app)(kernel level)
English

I'm happy to publish the second part of the series about iOS (de)Obfuscation and RASP protections.
romainthomas.fr/post/22-09-ios…
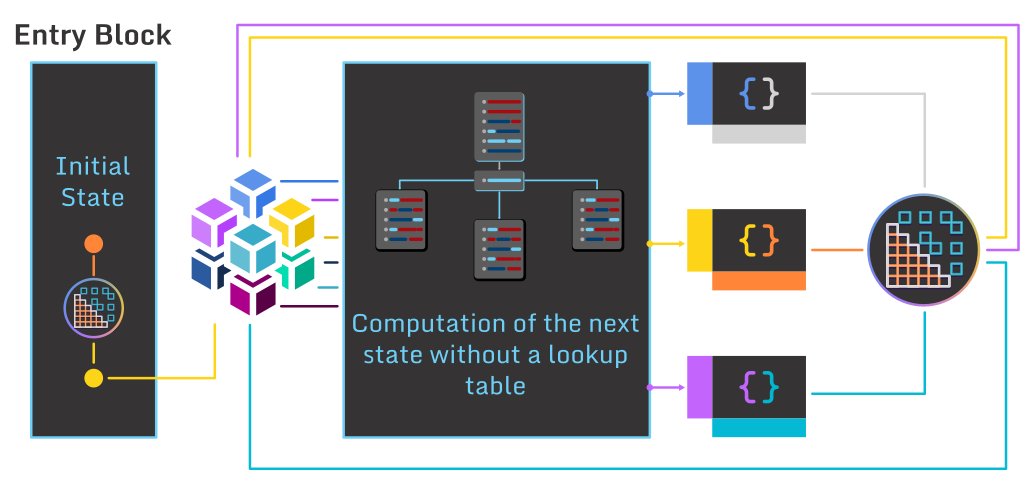
In particular, it introduces a new technique to "hook" syscalls on AArch64 based on
'gum_memory_patch_code' from @fridadotre
English
jmpews retweetledi
jmpews retweetledi

Based on the rate of research, you could say fuzzing is kind of a big deal. So many papers are being published it’s hard to track it all, let alone read it all. These repos are doing a good job indexing the papers:
github.com/0xricksanchez/…
github.com/wcventure/Fuzz…
English
jmpews retweetledi
jmpews retweetledi

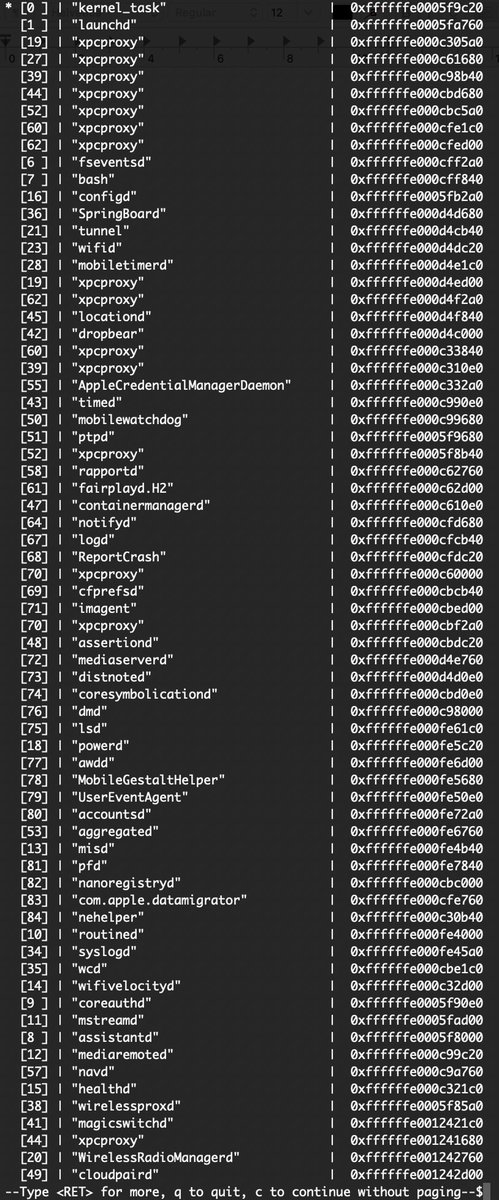
Now you can hook kernel functions with custom code and sniff all mach messages passed in the system. github.com/alephsecurity/…

English
jmpews retweetledi

[BLOG] "Fuzzing binaries with LLVM's libFuzzer and rev.ng" by @antoniofrighez
rev.ng/blog/fuzzing/p… #firstblood #revng #decompiler
English
jmpews retweetledi

Here are the slides from my BlackHat talk "iOS Kernel PAC, One Year Later", in which I consider how kernel PAC CFI has changed since its introduction in iOS 12 and examine 5 ways to bypass it in iOS 13: bazad.github.io/presentations/…
English
jmpews retweetledi

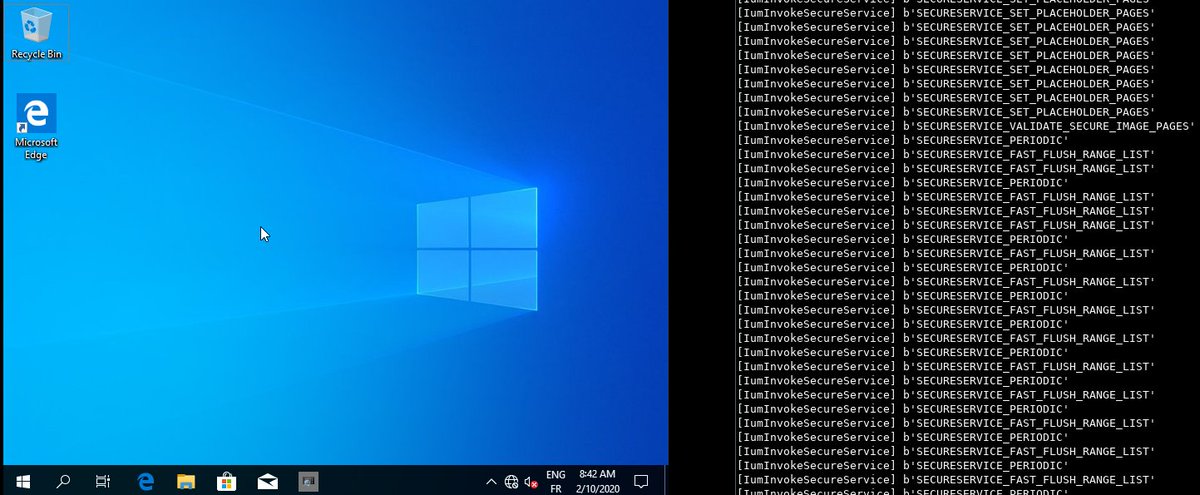
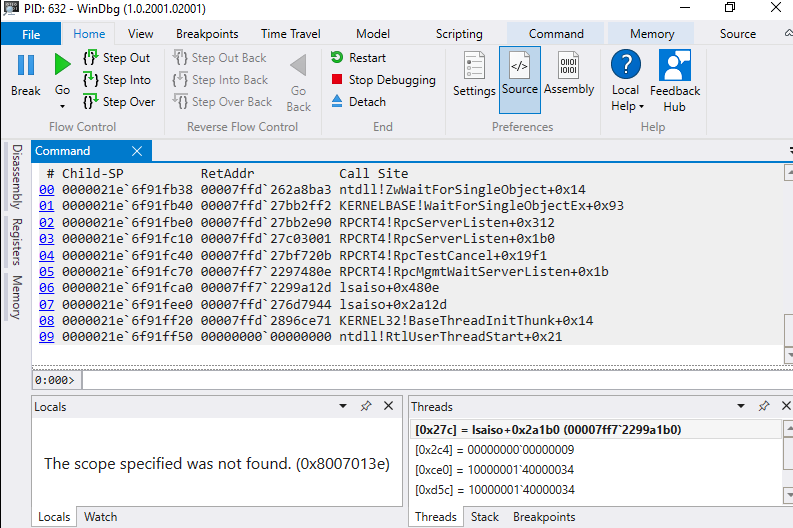
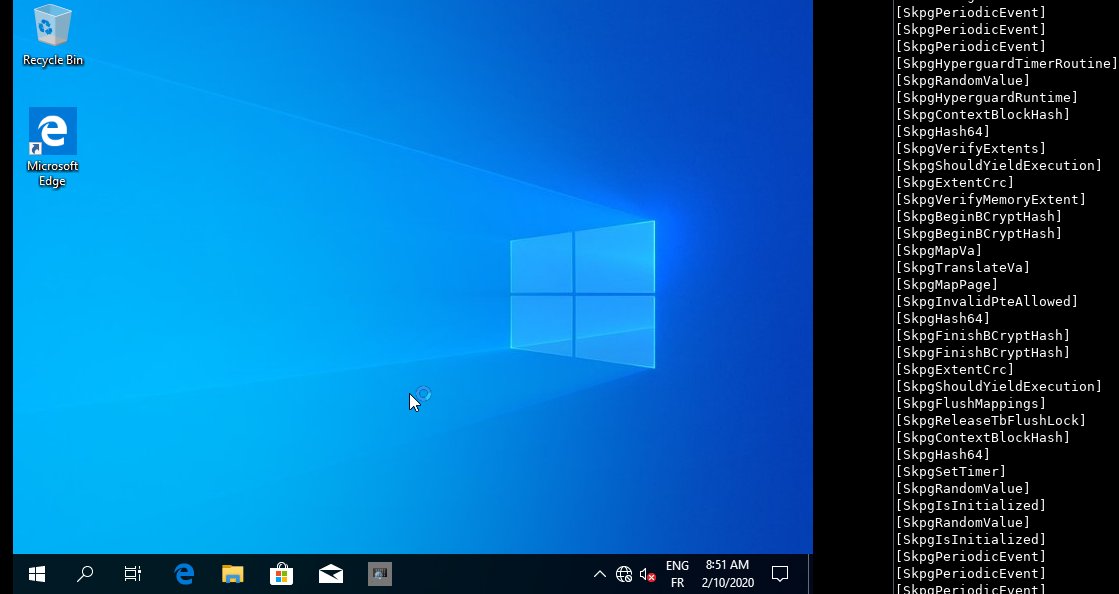
PoC gdb debugging of Win10 secure kernel, on top of QEMU-KVM github.com/commial/experi…
Tiny examples includes debugging LsaIso, logging Skpg* function calls or logging secure services calls
English
jmpews retweetledi

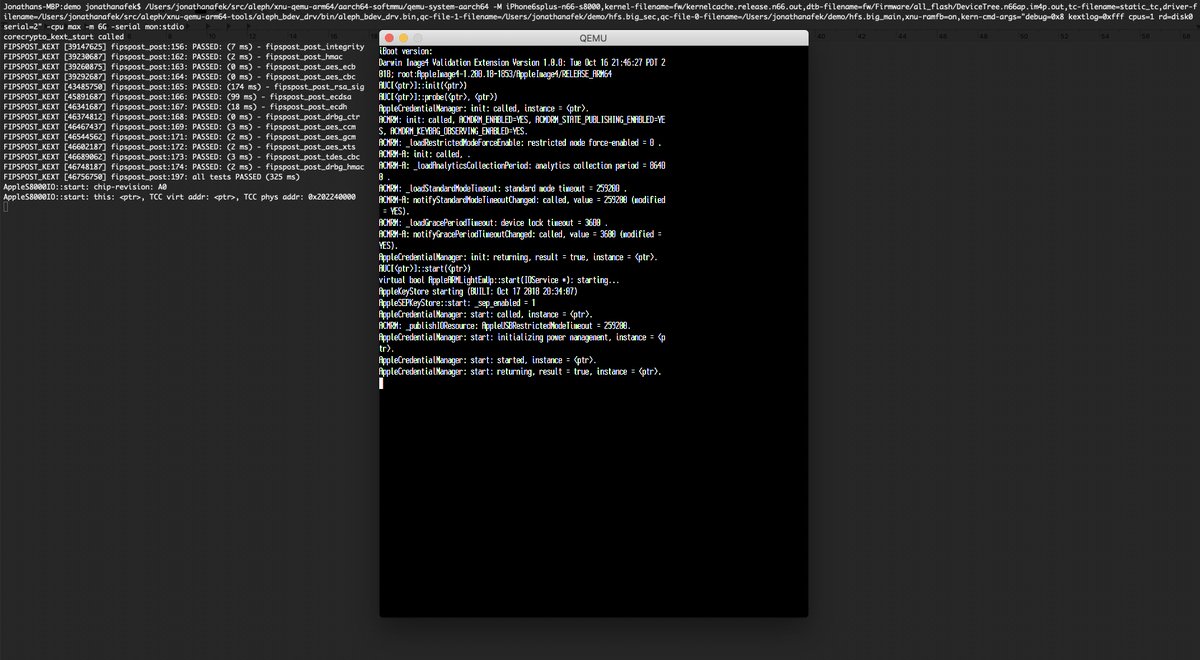
Can't wait to present the progress we've made since #BHEU at @offensive_con! tfp0, full disk mounts with our own block device driver, most of the iOS services running, ssh and a textual framebuffer. #offensivecon

English