kettelab
32 posts


@G0LDEN_infosec @infosec_au @assetnote Come on, it's open source! You could contribute to the community instead of spreading hate.
English

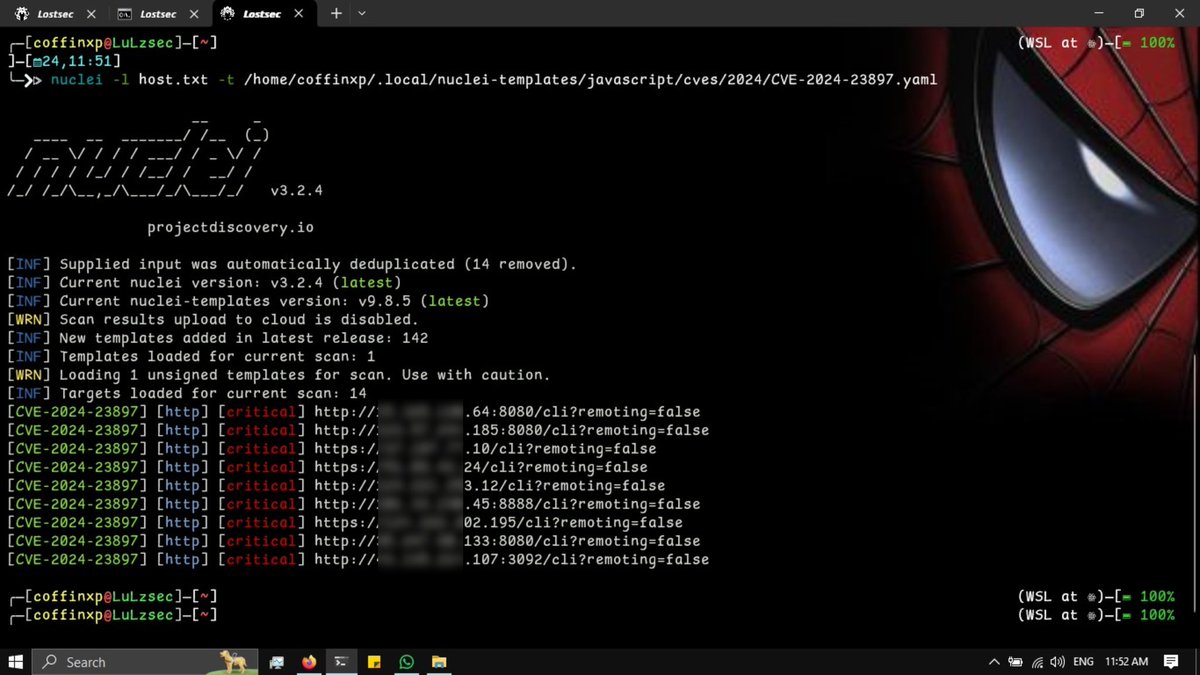
If you are looking for this issue... **READ THIS** ⬇️... I already found multiple confirmed vulnerable assets with a custom template built the way @infosec_au and the @assetnote gang checks that the public PD template does NOT flag as vulnerable!
shubs@infosec_au
We recently looked deeper at the authentication bypass vulnerability in Next.js (CVE-2025-29927) and discovered some intelligent and comprehensive ways to check for the vulnerability. Read more in our blog post: slcyber.io/assetnote-secu…
English
and the dupe party starts...
Dhiyaneshwaran@DhiyaneshDK
🚨 Scan for Adobe Commerce & Magento - XXE (CVE-2024-34102) discovered by Sergey Temnikov using Nuclei Template @pdnuclei 🔍 Details: github.com/spacewasp/publ… 📑 Nuclei Template: @dhiyaneshwaran/5SMcoU4iodifizkQHgDFL6" target="_blank" rel="nofollow noopener">cloud.projectdiscovery.io/@dhiyaneshwara…
🔧 GitHub PR: github.com/projectdiscove… #bugbounty #adobe #pdteam #infosec English
kettelab retweetledi

Everyone needs to read this. Kudos to @FT. This is not behind a paywall and worth your time and attention. ig.ft.com/taiwan-battleg…
English

@Cobratate someone selling fake course with your name.
cosmofeed.com/vp/64f45660e0e…
English
kettelab retweetledi
kettelab retweetledi

Today I am finally releasing a new 3-part browser exploitation series on Chrome! This was written to help beginners break into the browser exploitation field.
Part 1 covers V8 internals such as objects, properties, and memory optimizations. Enjoy! jhalon.github.io/chrome-browser…
English
kettelab retweetledi

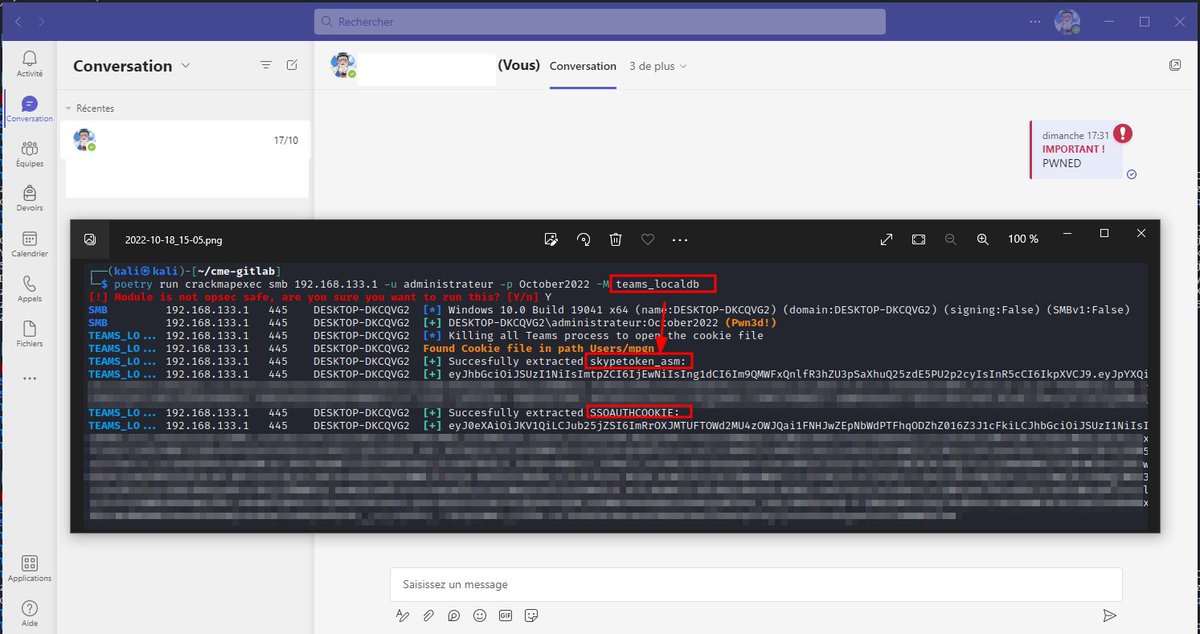
New CrackMapExec module to dump Microsoft Teams cookies thanks to @KuiilSec contribution✌️
You can use them to retrieve informations like users, messages, groups etc or send directly messages in Teams 🔥
Initial discovery by @NoUselessTech 🪂
English
kettelab retweetledi
kettelab retweetledi
kettelab retweetledi
kettelab retweetledi
kettelab retweetledi

@NinjaParanoid Always exciting :) Some comments are very interesting as well - twitter.com/0gtweet/status…
Grzegorz Tworek@0gtweet
Did they tell you "This function is included only in Windows XP." at docs.microsoft.com/en-us/windows/… ? They lied :P Feel free to try it at home: rundll32 keymgr,KRShowKeyMgr
English
kettelab retweetledi

This 3D video by @Maxar shows the Russian military convoy northwest of Kyiv (not the entire 40-mile length, but gives a good impression). Note: this is from the previously Feb. 28 satellite imagery. It's been too cloudy for new satellite imagery updates.
English
kettelab retweetledi

#Learn365 - Day 33:
☑️Intro to Android Architecture and Security - Video
Link: mobisec.reyammer.io/slides
☑️ Android Security Part 1- Understanding Android Basics - Writeup
Link: payatu.com/blog/amit/Need…
English
kettelab retweetledi
#exploit
1. CVE-2022-21371:
Oracle WebLogic Server 12.1.3/12.2.1.3/12.2.1.4/14.1.1
- Local File Inclusion
gist.github.com/picar0jsu/f3e3…
2. CVE-2021-20038:
SonicWall SMA-100 Unauth RCE Exploit
github.com/jbaines-r7/bad…
English