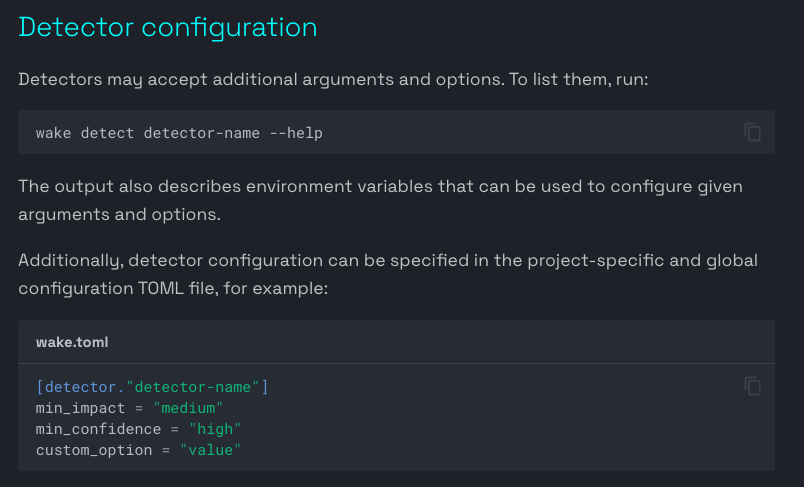
Dajma
345 posts


Dajma
@khimcdmy
Ethereum Security Researcher & Static Analysis Developer
Katılım Şubat 2022
216 Takip Edilen42 Takipçiler

Four AI auditing tools. Fourteen protocols. The shape tells the story.
Wake Arena 3.1's blue area contains the other three on every axis.
Where all systems struggle — Burve, Notional — the gap closes.
Where the work matters — Lend, Munchables, Virtuals — the edge is visible and consistent.
What the chart doesn't show: 49 of the 63 found vulnerabilities were confirmed by more than one Wake Arena agent independently.
The shape reflects consensus, not a single model's guess.
Learn more ↓

English
Dajma retweetledi

@WakeFramework This is exactly why debugging smart contracts is painful.
One function → 6 internal calls → 3 contracts → hidden side effects
Wake’s call flow visualization lets you see the entire execution path directly in VS Code — before running anything, before adding logs before deploy
English

When your toughest competition is your previous version, you're doing something right.
Wake Arena 3.1 vs 3.0, same 94 vulnerabilities, same 14 protocols:
Lend: 13/28 → 20/28
Virtuals: 4/6 → 6/6
Burve: 2/9 → 4/9
Phi: 4/7 → 6/7
Total: 43 → 63
+47% in a single version
The four protocols already at 100% in v3.0: still at 100% in v3.1.
Learn more ↓

English

@WakeFramework exactly! it is how you make difference against others - you create your own tooling
English

@WakeFramework exactly! DDG and CFGs is the wild combo-wobmo (also for debugging detectors with them😅)
English