Ståle Pettersen
2K posts


Ståle Pettersen
@kozmic
Security enthusiast that work with Application security and Cloud security. Bsky: https://t.co/BBjeSkfQg0



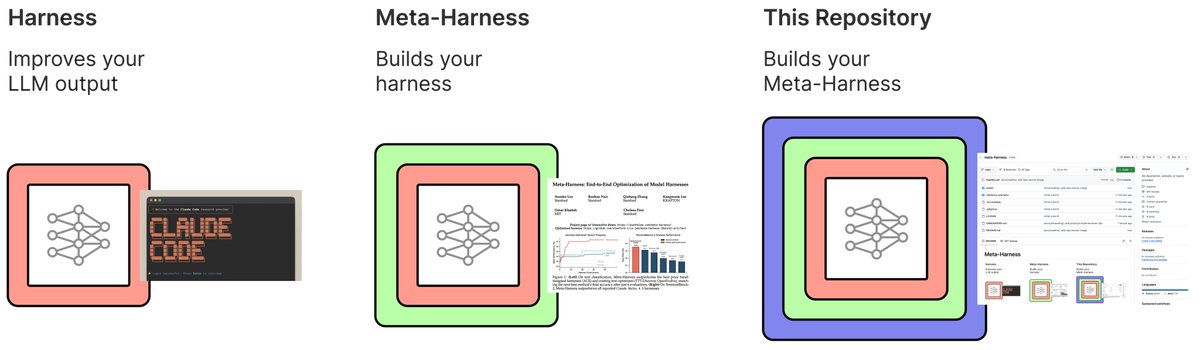
Proposal: if you publish about an LLM finding vulns, please publish precise costs. Given the different levels of competence, verbosity etc per model, knowing token counts and cost per token is essential.




How can we autonomously improve LLM harnesses on problems humans are actively working on? Doing so requires solving a hard, long-horizon credit-assignment problem over all prior code, traces, and scores. Announcing Meta-Harness: a method for optimizing harnesses end-to-end


Technical report released: The AI-Assisted Breach of Mexico’s Government Infrastructure gambit.security/blog-post/a-si…

Claude code source code has been leaked via a map file in their npm registry! Code: …a8527898604c1bbb12468b1581d95e.r2.dev/src.zip


someone at ANTHROPIC just showed CLAUDE finding ZERO DAY vulnerabilities in a live conference demo claude has found zero day in Ghost, 50,000 stars on github, never had a critical security vulnerability in its entire, history... it found the blind SQL injection in 90 minutes, stole the admin api key, then did the exact, same thing to the linux kernel







