Kuldeep Pandya retweetledi

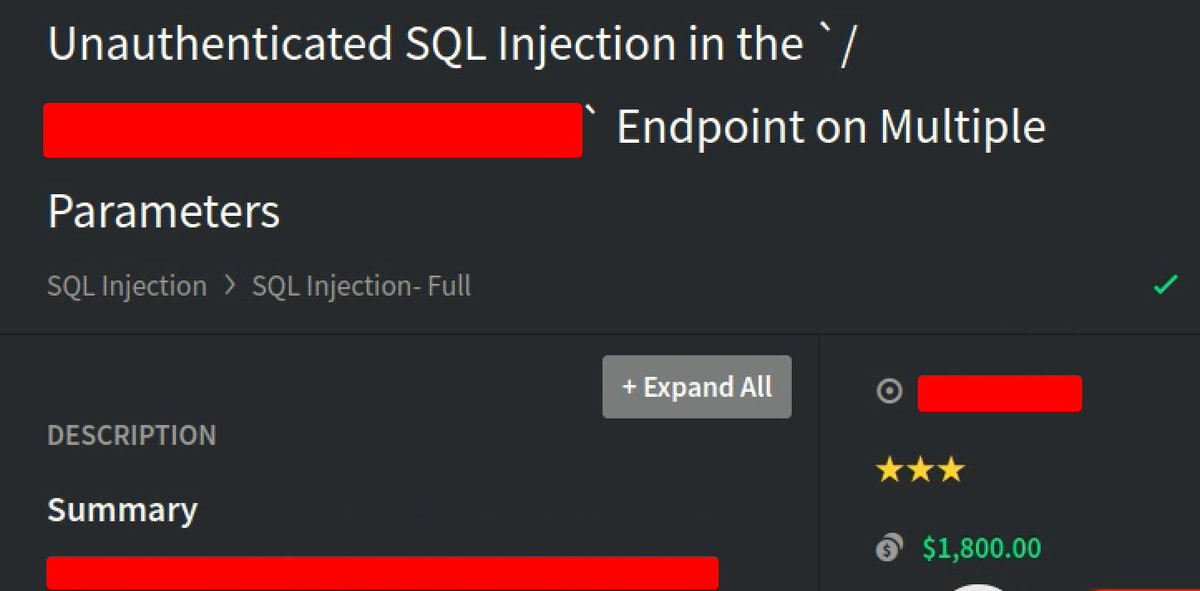
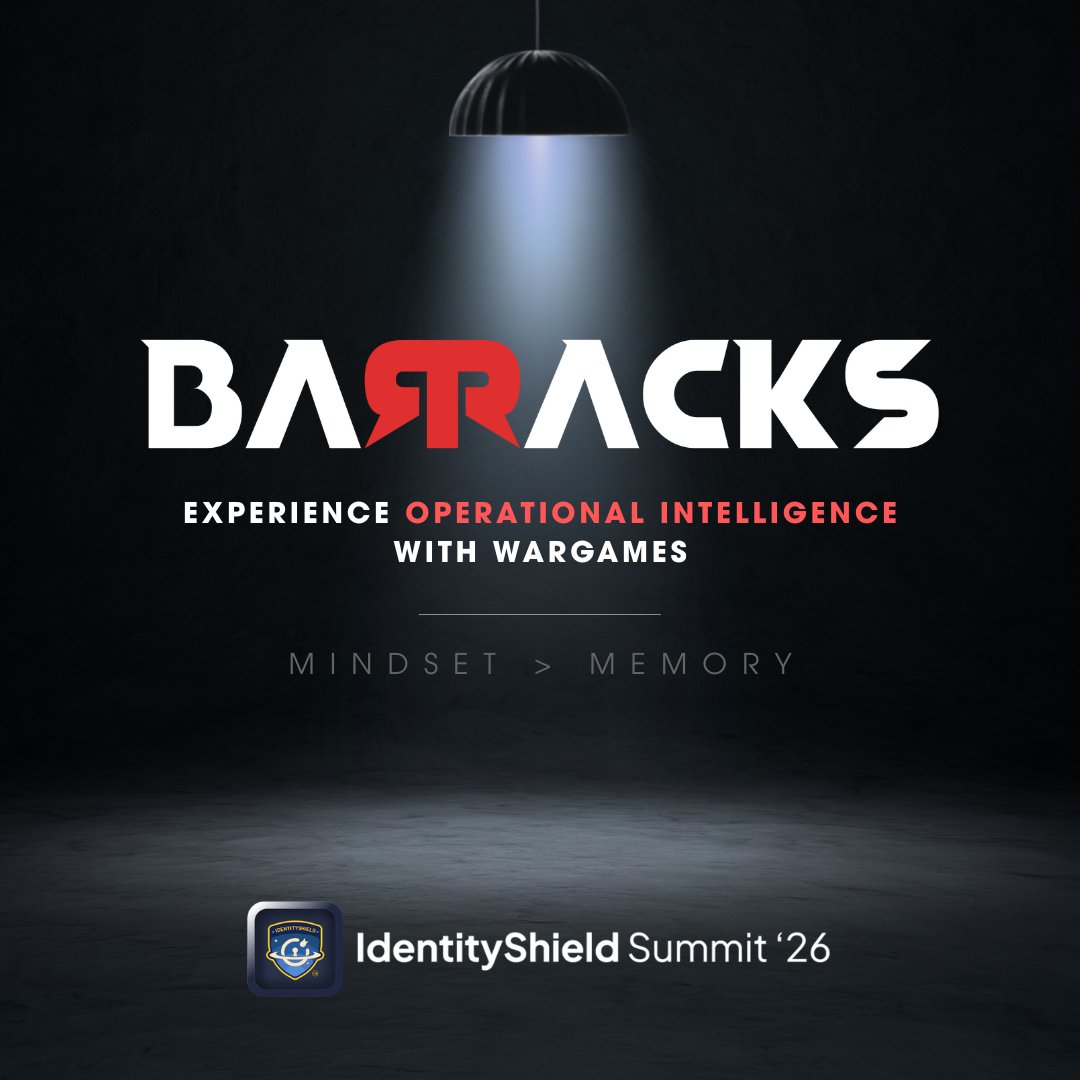
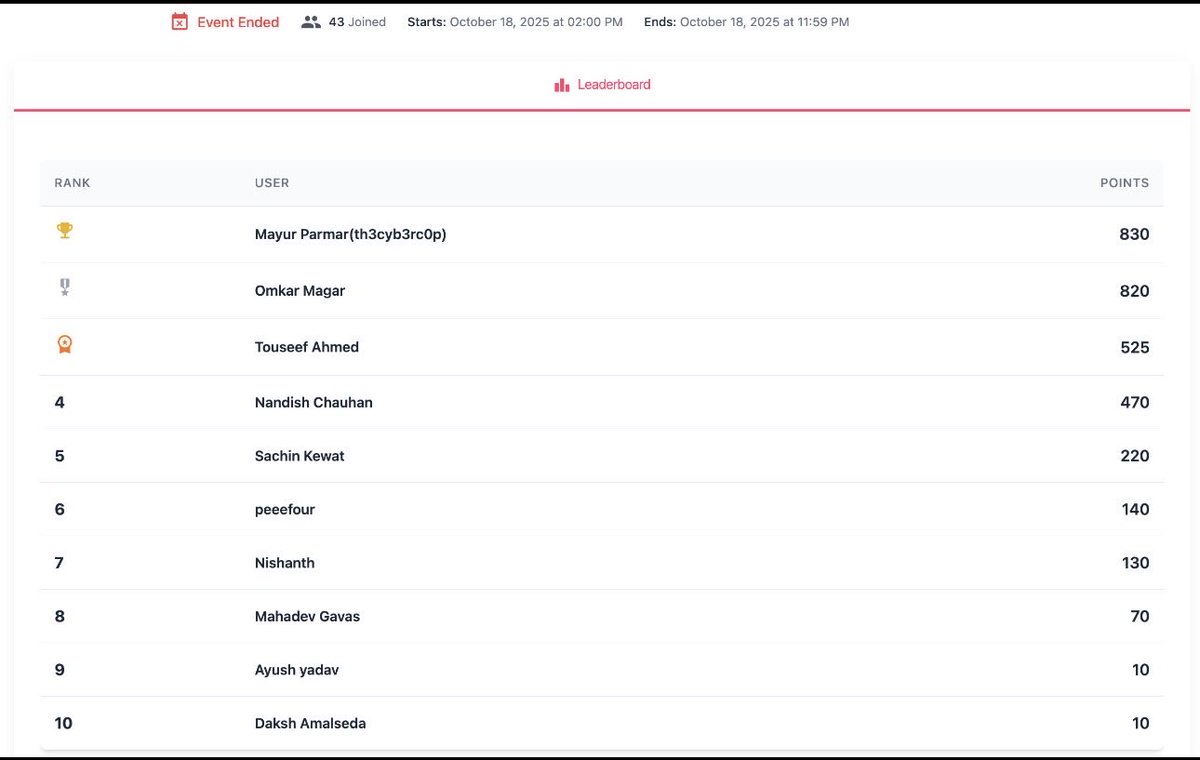
One of our own just hit their first 3-digit bounty. 🛡️
Every bounty has a story behind it.
Late-night testing.
Duplicates.
Learning from labs.
Community support.
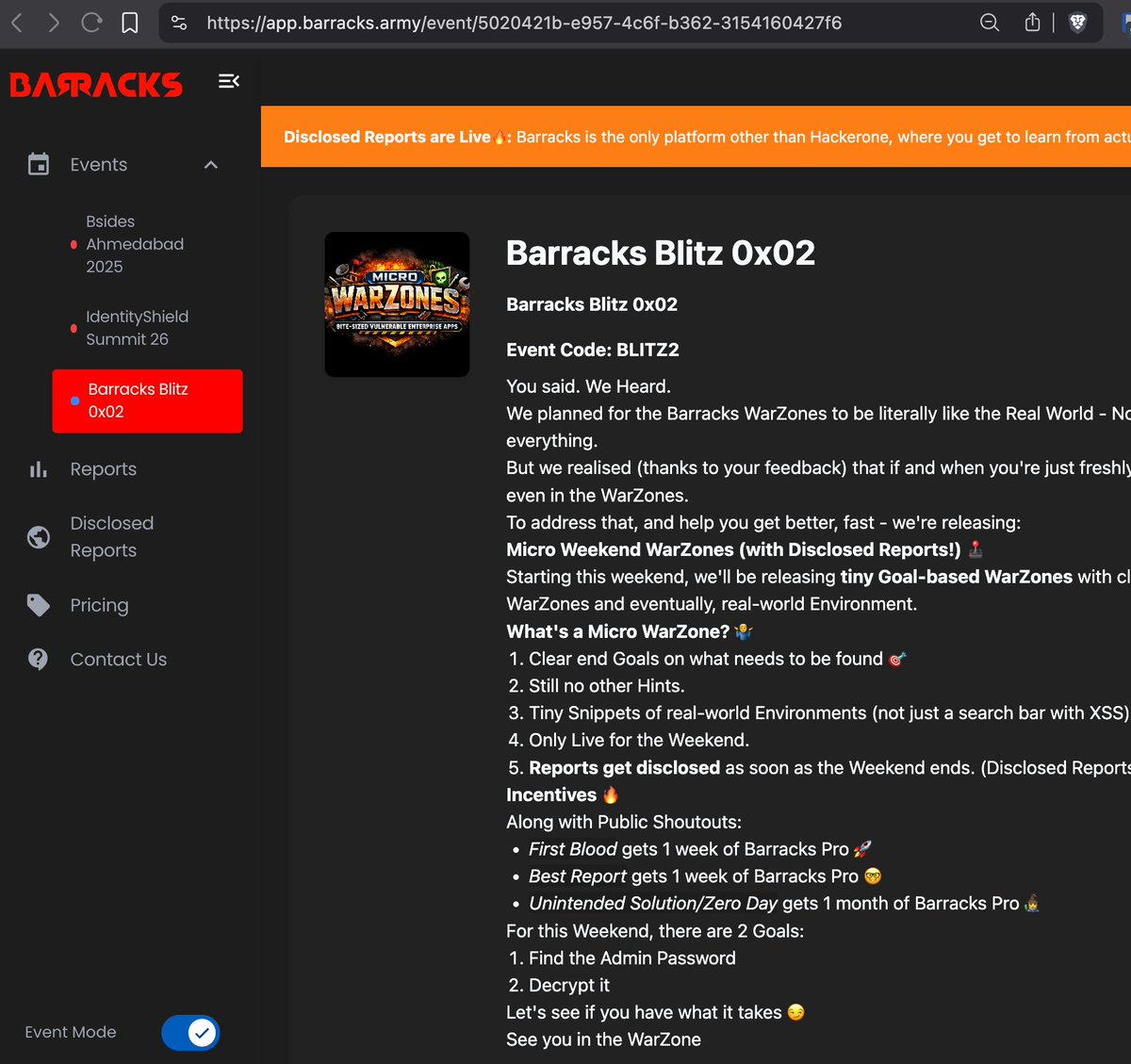
From learning web security fundamentals…
to solving labs…
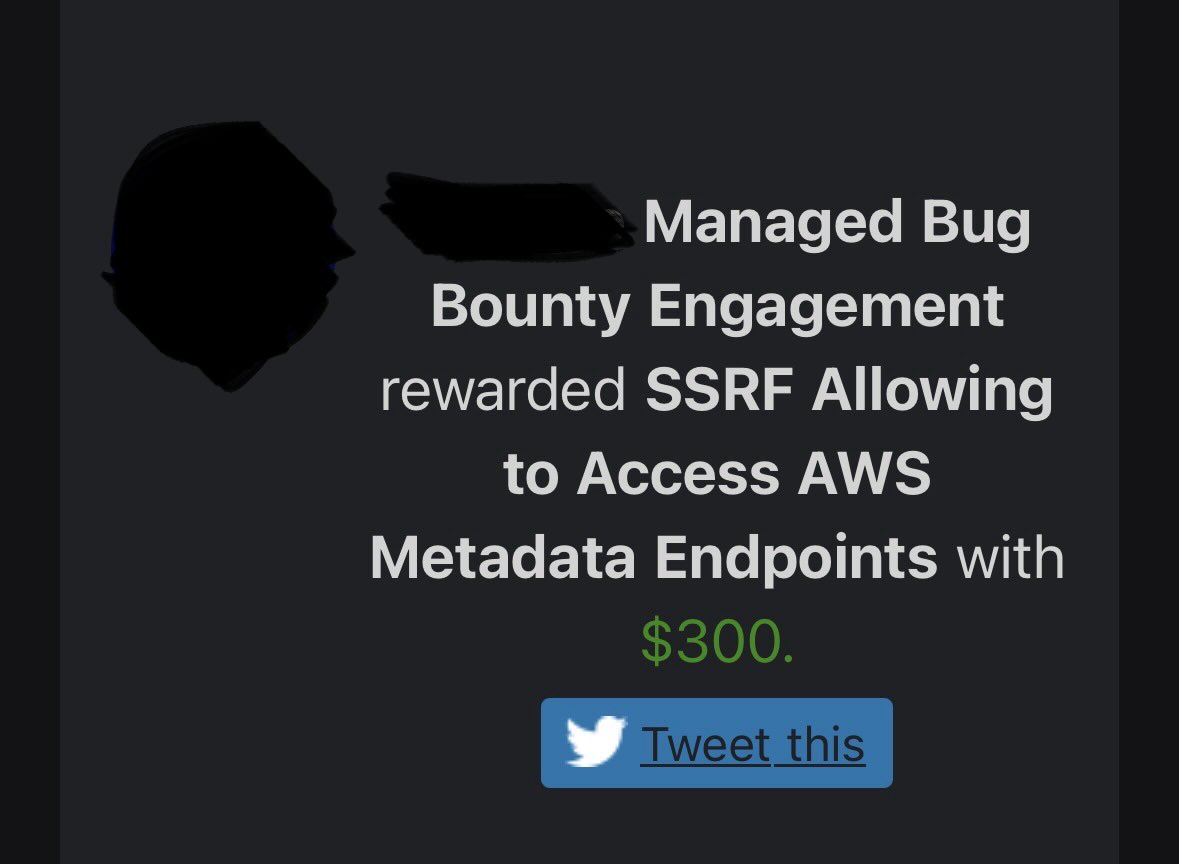
to attending community events…
to facing multiple duplicates before finally landing a valid bounty.
This is the journey most researchers go through - persistence is the real skill.
Huge congratulations on the milestone and thank you for sharing the journey.
We’re proud to see members of the Barracks community turning learning into real impact.
Welcome to the growing list of Barracks Graduates.
Full story in the comments 👇

English