Sabitlenmiş Tweet

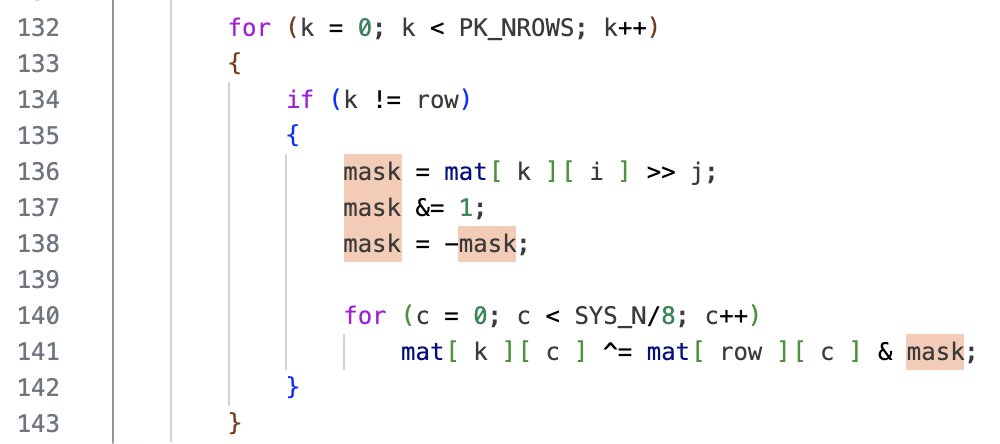
@TrueSkrillor joins the infosec community with a bang: A new attack class against the SSH protocol!
English
-
2.3K posts

@lambdafu
https://t.co/tI4jg6u8vL // @[email protected]














This feels like as good a time as any to disclose another critical Signal vulnerability I found. TLDR is that prior to mid 2021, Signal *didn’t delete* disappearing messages after they “disappeared.” So say you had a message from 2016 that you thought disappeared years ago, nope!