lin ⌘
122 posts


@monad_xyz any interaction with this tweet will make you eligible for the monad airdrop
drop your monad address below 👇
English

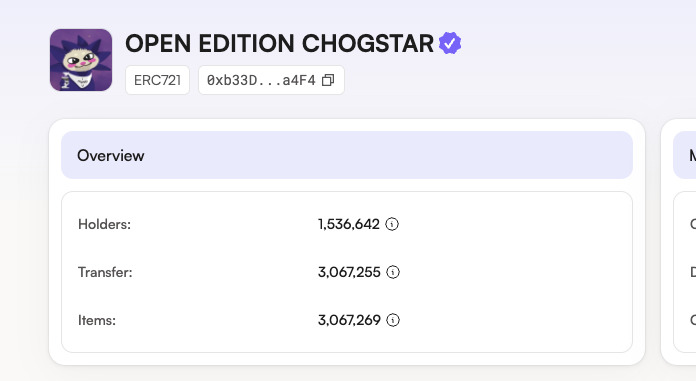
@monad_xyz drop your Monad address below within the next 24 hours to receive your Chogstars Open Edition Soulbound NFT
English

@monad_xyz Drop your Monad address below within the next 24 hours to receive your soulbound NFT

English

@monad_xyz drop your monad address below to receive love from us 💜
English
lin ⌘ retweetledi

SecWareX New Task Alert🚨
Bitlayer announced the launch of its first Mining Gala Event.💥
Learn how to identify the official Bitlayer website on SecWareX and share more EBs and STH surprise!
Be cautious in discerning!👇
secwarex.io/task-detail/131
English
lin ⌘ retweetledi

Please note that the top promoted link for @Stake_Stone in Google search results is a phishing website⚠⚠⚠
Completing the task of identifying phishing websites in Google search results can earn you up to 150 Energy Blocks.
secwarex.io/task-detail/132
English
lin ⌘ retweetledi

Beware of Chrome Browser Plugin Hijacking Leading to Theft of Cookies and Assets
A Chinese user has recently fallen victim to a Chrome browser plugin hijacking incident. The installation of the "Aggr" extension led to the compromise of their browser cookies, resulting in asset losses exceeding $1 million.
Browser plugins (extensions) are designed to handle a portion of the web page information on their behalf. However, these plugins can not only access and modify the original web content, but also obtain sensitive data such as location, clipboard, cookies, browsing history, and even capture screenshots and keystrokes. In other words, these plugins can not only acquire information like cookies, but they can also directly control the content that we see on web pages.
Web-based attacks within the browser are difficult for system security mechanisms to detect, as the browser cannot recognize whether the plugin's access is authorized by the user. Theoretically, the attack behavior of browser plugins is more challenging to identify compared to client-side software.
The GoPlus security team recommends the following measures to safely use browser plugins:
1. Only install plugins (extensions) from official markets, and avoid using ones from unknown sources.
2. Even official plugins may be compromised by hackers, such as through direct replacement of the installation package or supply chain attacks. When using plugins, be sure to control the access permissions and do not grant unnecessary permissions. Set the plugin permissions to "When you click this extension" or "On specific sites" to effectively prevent malicious extensions from accessing cookies.
3. Use a separate browser for plugin installation, isolated from the one used for trading and financial activities.
4. Avoid web-based login to exchanges, and use incognito browsing for sensitive operations. Log out immediately after completing trading tasks, and regularly clear the browser cache and cookies.

English
lin ⌘ retweetledi

We've been cooking up something BIG 🌋
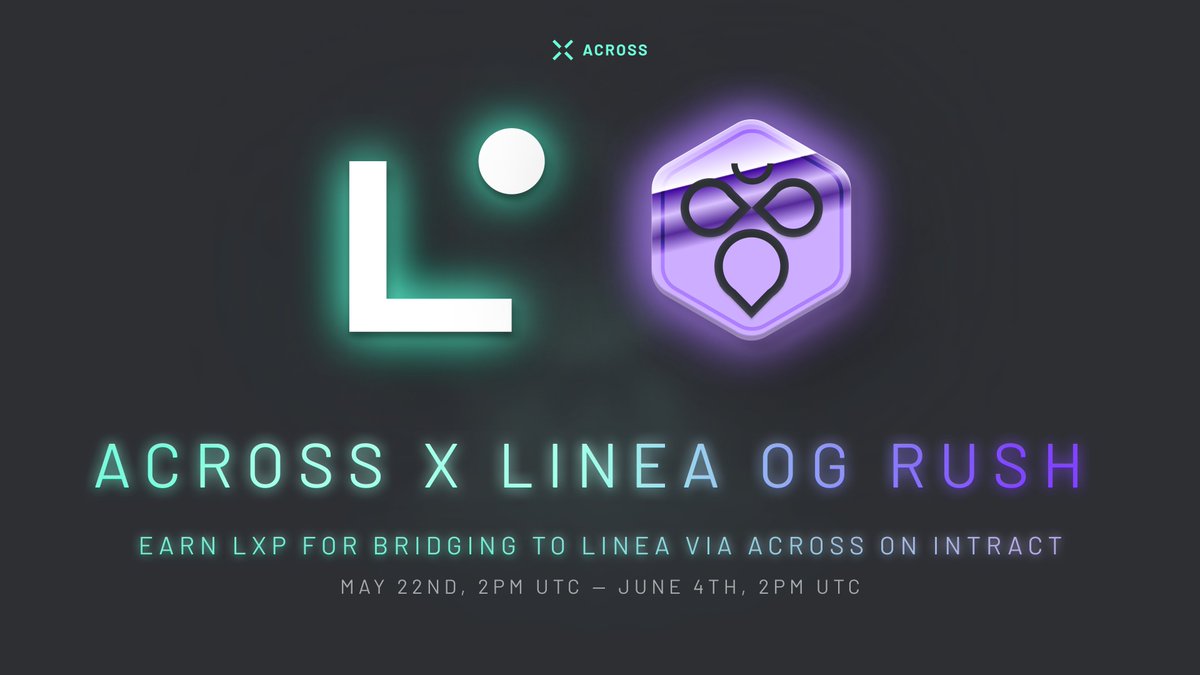
Now bridging to @LineaBuild via Across can earn you 50 LXP!! The Linea OG Rush campaign is live from May 22 - June 4 on @IntractCampaign 💫
Earn your LXP here: link.intract.io/LineaOGRush
English
lin ⌘ retweetledi

lin ⌘ retweetledi

The second phase of the Binance MegaDrop project, @lista_dao , has attracted massive phishing accounts on X. Make sure to identify the official website and X account to avoid any asset loss! Click to earn up to 150 EB!!!
secwarex.io/task-detail/129
English