literallyHS
3.9K posts








Distributed trust is the cornerstone of robust security. We are diving deep with a 5-part technical series on how threshold systems eliminate single points of failure by requiring a quorum of participants to execute cryptographic operations. The first two modules are now live: 01 | Distributed Key Generation: An analysis of how groups jointly generate shared keys without any participant gaining knowledge of the full secret. This lesson covers Shamir's Secret Sharing, Lagrange interpolation, and honest-world key generation. 02 | Verifiable Secret Sharing: Moving beyond the honest-world assumption. This module explores Feldman’s VSS for share verification and Pedersen’s protocol for achieving DKG without a trusted dealer through complaint-based disqualification. Stay tuned for the remaining three parts of the series. Link below:




This is the most expansive piece on onchain credit infrastructure I've read this year. But it leaves open the most important question: What kind of scaffolding is actually missing? These are my thoughts in 10 parts 🧵

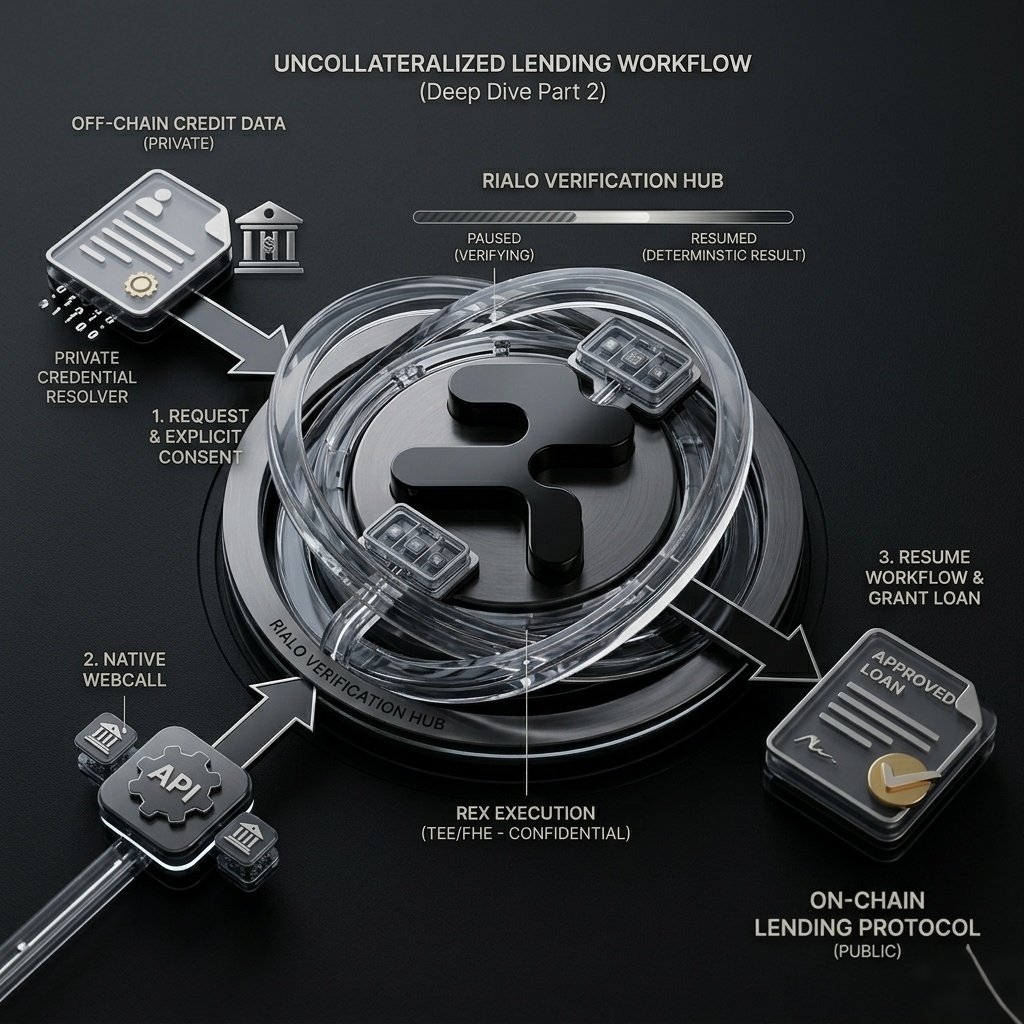
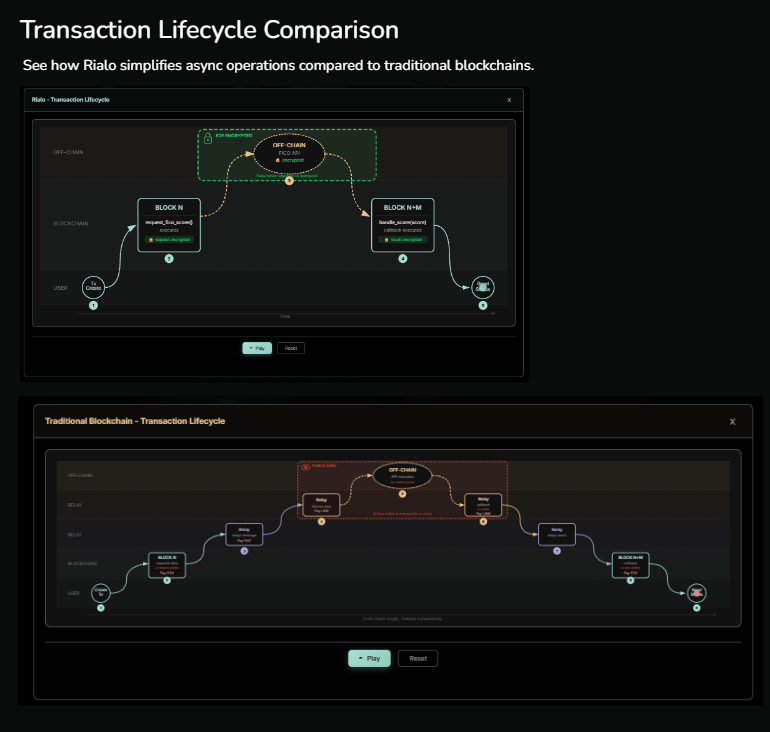
Rialo Deep Dive | Part 1: REX — The Architecture of Confidential Intelligence 🛡️ The biggest hurdle for institutional Web3 adoption isn't scalability—it's confidentiality. How do you process sensitive, real-world data on a public ledger without exposing it to the world? The answer lies within REX (Rialo Extended Execution). 1. The Orchestration Layer REX is not a single privacy tool; it is a high-level Confidential Computing Orchestrator. It manages the entire lifecycle of a secure request by coordinating three titan technologies of modern cryptography: MPC (Multi-Party Computation): REX shards the data across multiple independent nodes. No single node ever holds the complete dataset, eliminating central points of failure. FHE (Fully Homomorphic Encryption): This allows REX to perform mathematical operations on data while it remains encrypted. We compute the "truth" without ever seeing the raw input. TEEs (Trusted Execution Environments): For high-performance execution, REX utilizes hardware-level secure enclaves. This ensures that even the host machine cannot peek into the computation process. 2. From Consent to Determination Unlike traditional oracles that blindly push data, REX follows a strict Program Governance model. Every byte of data processed through REX requires Explicit Consent and follows a verifiable logic path. This transformation of raw, private data into a verifiable on-chain result is what bridges the Verification Gap. It’s how we move from "Don't be evil" to "Can't be evil." 3. The Result: Deterministic Workflows By combining these layers, REX enables what we call Deterministic Workflows. Whether it's verifying a bank wire via Native WebCall or triggering an Async Workflow for an RWA settlement, REX ensures the outcome is private, accurate, and immutable.

This is the most expansive piece on onchain credit infrastructure I've read this year. But it leaves open the most important question: What kind of scaffolding is actually missing? These are my thoughts in 10 parts 🧵



Builder Hub başladı, ben yerimi aldım 🚀 Siz de geç kalmadan katılın! Bu tarz etkinlikler sadece bir buluşma değil; 👉 Kendini göstermek 👉 Projeni anlatmak 👉 Topluluk içinde öne çıkmak için gerçek bir fırsat Aynı zamanda Builder Hub & Shark Tank sürecinde aktif olmak, Builder rolüne giden yolu açıyor. Bu rol gerçekten fark yaratıyor. Kısaca söylemek gerekirse: Ben katıldım, siz de hemen gelin ve bu sürecin içinde yerinizi alın 🔥 @RialoHQ @RialoTR @slymnogunc