
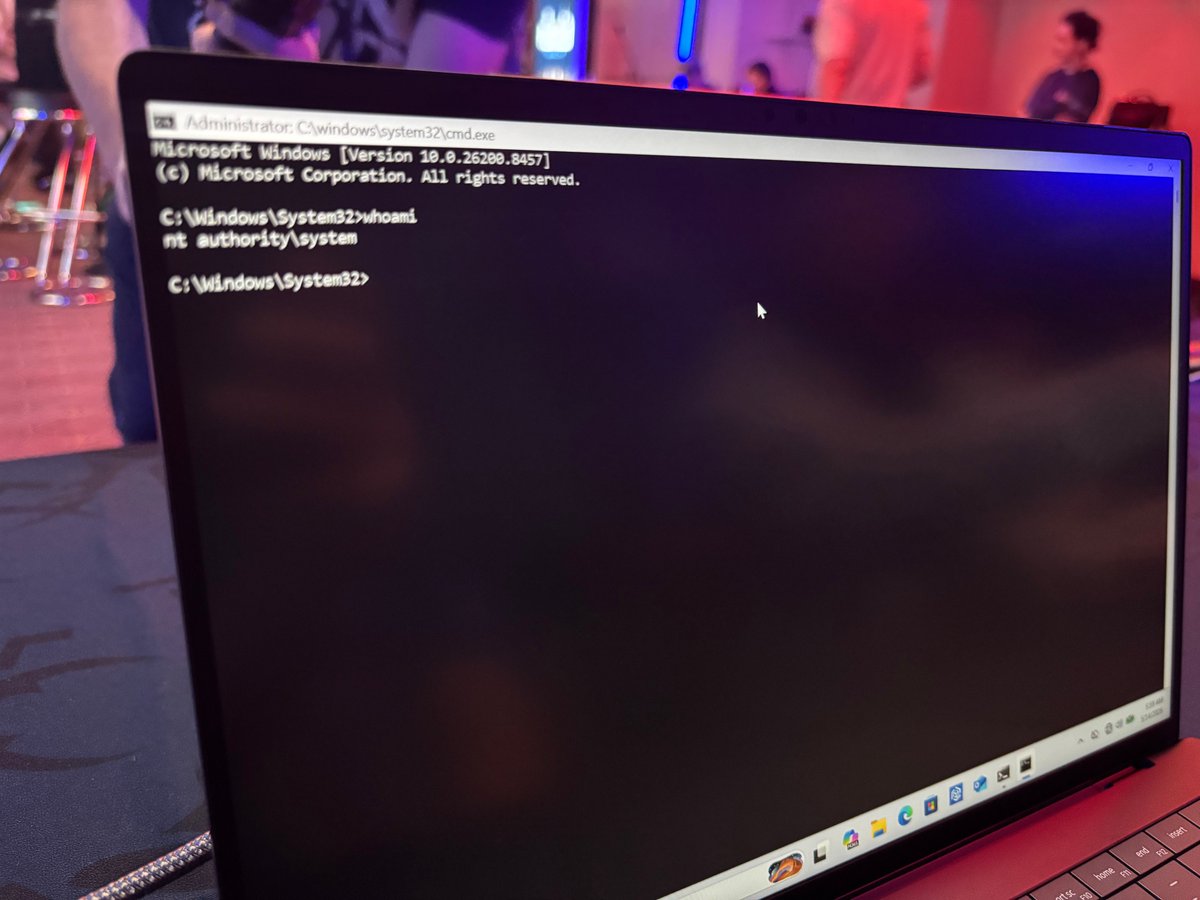
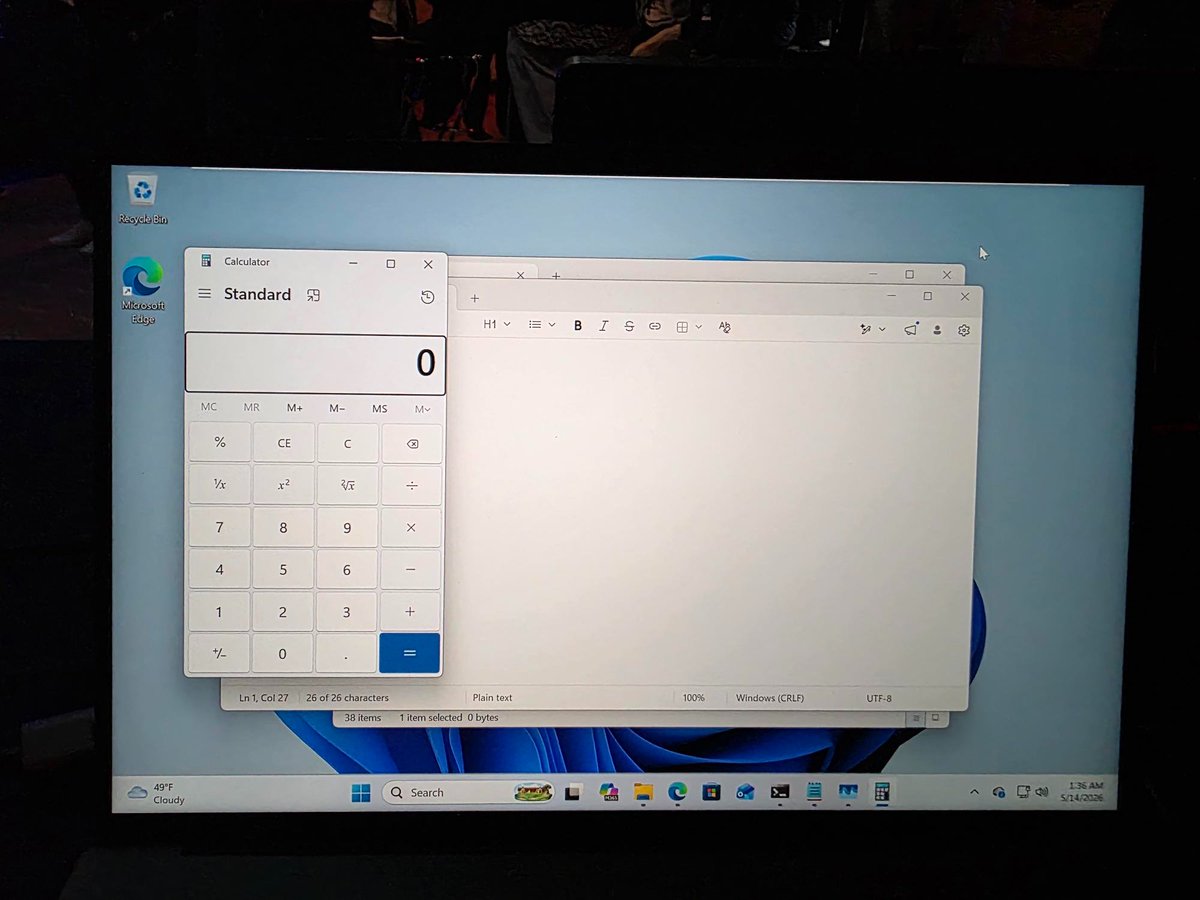
Confirmed! Orange Tsai (@orange_8361) of DEVCORE Research Team (@d3vc0r3) chained 4 logic bugs to achieve a sandbox escape on Microsoft Edge, earning $175,000 and 17.5 Master of Pwn points. Full win! #Pwn2Own #P2OBerlin
LJP
90 posts


Confirmed! Orange Tsai (@orange_8361) of DEVCORE Research Team (@d3vc0r3) chained 4 logic bugs to achieve a sandbox escape on Microsoft Edge, earning $175,000 and 17.5 Master of Pwn points. Full win! #Pwn2Own #P2OBerlin







💥 Introducing "Dirty Frag" A universal Linux LPE chaining two vulns in xfrm-ESP and RxRPC. A successor class to Dirty Pipe & Copy Fail. No race, no panic on failure, fully deterministic. ~9 years latent. Ubuntu / RHEL / Fedora / openSUSE / CentOS / AlmaLinux, and more. Even if you've applied the "Copy Fail" mitigation, your Linux is still vulnerable to "Dirty Frag". Apply the Dirty Frag mitigation. Details: dirtyfrag.io








(CVE-2025-8880)[TBD][433533359][wasm]Race Condition chromereleases.googleblog.com/2025/08/stable… Reported by Seunghyun Lee (@0x10n)

(CVE-2025-5063)[411573532][vt/cc]Add ViewTransitionRequest -> NotifyTransitionRequestsFinished -> synchronous callback execution -> JS initiates new transition -> re-enter container modification -> vector reallocation/iterator invalidation -> erase invalid iterator (UAF)







I'm giving a talk on POC2024 (Nov. 7, Korea) and CODE BLUE 2024 (Nov. 14, Japan) on my VR adventures on Wasm engines in browsers (mostly Chrome). Unfortunately I can't talk about ~10 recent bugs, but there still will be several others and a whopping 10 v8sbx bypasses to share :)
