Sabitlenmiş Tweet
Mohammad
42 posts


Mohammad
@m0hammad_y4ser
Application Security Consultant @ https://t.co/d2Pfm2x1kq | OSWE "always forward, never backward."
Katılım Haziran 2021
722 Takip Edilen837 Takipçiler
Mohammad retweetledi

𝗧𝗶𝗿𝗲𝗱 𝗼𝗳 𝘂𝗽𝗱𝗮𝘁𝗶𝗻𝗴 𝗰𝗼𝗼𝗸𝗶𝗲𝘀 𝗶𝗻 𝗲𝘃𝗲𝗿𝘆 𝗥𝗲𝗽𝗲𝗮𝘁𝗲𝗿 𝘁𝗮𝗯? 🍪
Burp extension that auto-replaces expired cookies/headers — perfect for retesting old requests without manual copy-paste.
🔗github.com/0xbartita/Cook…
#bugbountytip #bugbountytips #PenTest
English

@0xbartita 🔗 Advisory available on GitHub Security Advisories: github.com/laravel/reverb…
🔗 CVE Record: cve.org/CVERecord?id=C…
🔗 NIST NVD: nvd.nist.gov/vuln/detail/CV…
English

I and my friend @0xbartita responsibly disclosed a critical vulnerability in Laravel Reverb (CVSS 9.8/10), now patched and disclosed by the Laravel team.
CVE-2026-23524: github.com/laravel/reverb…
#bugbountytips #bugbountytip #CVE #Laravel #PHP #Reverb

English

🎯 Officially OSWE certified! Grateful for the grind, lessons, and late nights that led here. Huge thanks to @offsectraining for the great training.
credentials.offsec.com/74832a62-7658-…
#OSWE #AWAE #OffSec #OffensiveSecurity #Offensive_Security
English

Proud to have earned OSCP, OSWA, OSWP, and OSWE from Offensive Security
Each cert was a new challenge and a sharpening of my skills
Big thanks to Offensive Security for setting the bar high and inspiring specialists in the field
#OffSec #CyberSecurity #Security #Hacking #Hacked




English

@spaceboy2O @mux0x they do not know that i can change the CPU register to AAAAAAAAAAAA...
English

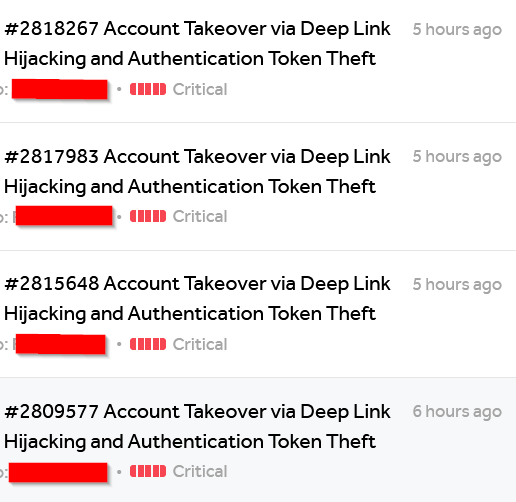
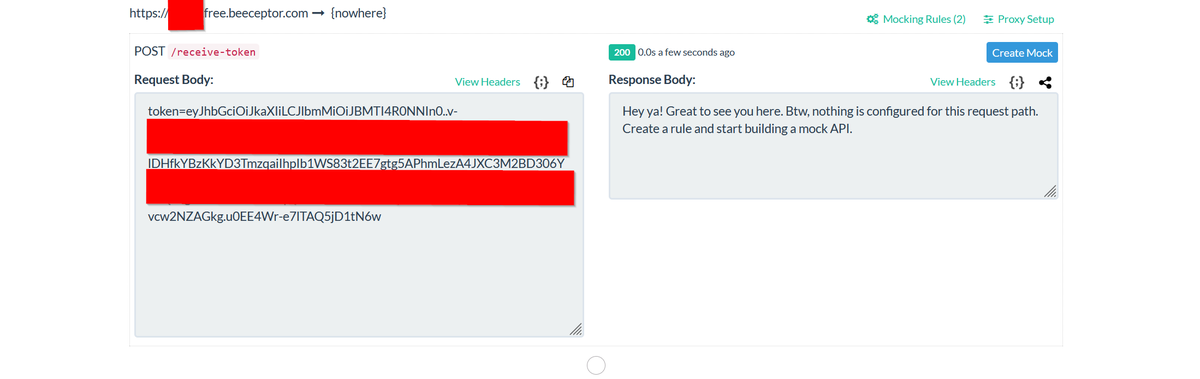
Deep Link Hijacking to Full Account Takeover: A Complete Guide
In this blog, I dive into how I exploited deep link vulnerabilities in Android applications to achieve full account takeover.
Check it out here: @soliman_almansor/deep-link-hijacking-to-full-account-takeover-complete-guide-3074b7ba82e3" target="_blank" rel="nofollow noopener">medium.com/@soliman_alman…
English

I’m looking forward to hearing updates about one of my best bugs being accepted as critical 9.1. 🔥💸
I feel great! Hard work pays off. Happy weekend, everyone! 😃
#bugbounty @Hacker0x01

English

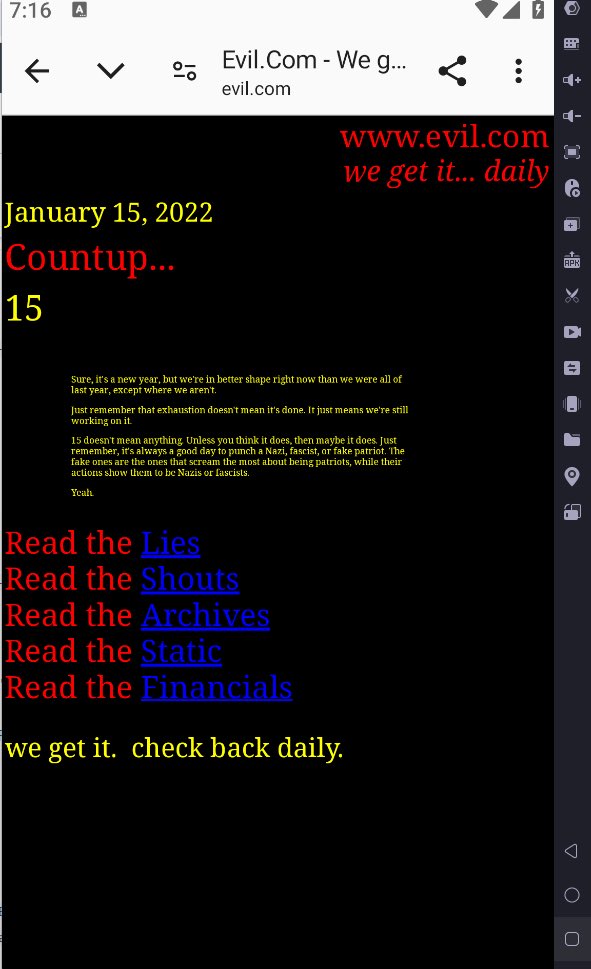
Deeplink bypass that worked with me
payload :-
`https://<button%20onclick=%22window.location.href='https:%2F%2Fevil.com'%22>Click%20Me</button>.com.cn`

English