




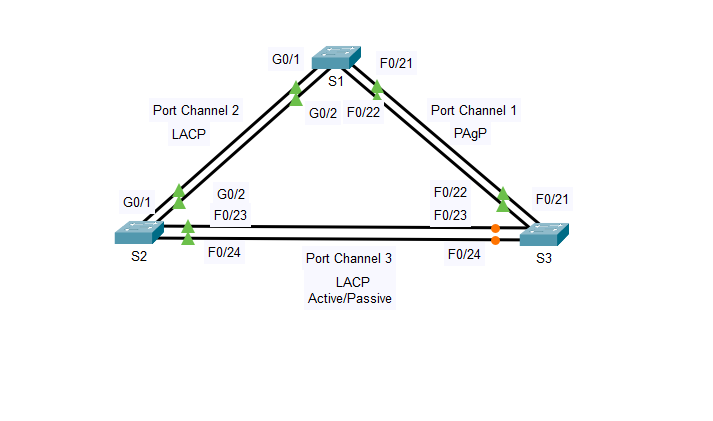
Day 65/100 of My Cybersecurity Journey Practiced a packet tracer lab configuring EtherChannel with cisco PAgP and LACP EtherChannel. Also configured redundant EtherChannel in the topology. #100DaysOfCyberSecurity @cyberjeremiah @CiscoNetAcad
Майкл
146 posts


@mike_dave47
Manchester united , Cybersecurity enthusiast, учиться в России🇷🇺





Day 65/100 of My Cybersecurity Journey Practiced a packet tracer lab configuring EtherChannel with cisco PAgP and LACP EtherChannel. Also configured redundant EtherChannel in the topology. #100DaysOfCyberSecurity @cyberjeremiah @CiscoNetAcad



Day 64/100 of My Cybersecurity Journey Completed a module on the various types of security . Security data consists of Alert Data, Session and Transaction Data, Full Packet Captures and Statistical Data. #100DaysOfCyberSecurity @cyberjeremiah @CiscoNetAcad @LearningatCisco

Day 63/100 of My Cybersecurity Journey Learned about some common protocols and how these protocols can be exploited by threat actors.E.g Email protocols such as SMTP, POP3 and IMAP can be used to spread malware and exfiltrate data #100DaysOfCyberSecurity @cyberjeremiah

Day 62/100 of My Cybsecurity Journey Today I watched some youtube videos on CCNA and practiced switching and Routing using available labs from practicalnetworking.net/stand-alone/pa… #100DaysOfCybersecurity @cyberjeremiah @NetworkQueenX @CiscoNetAcad @OnijeC

Day 61/100 of My Cybsecurity Journey Studied more on the Common Vulnerability Scoring System(CVSS) and its uses in risk assessment . Learned about the 3 CVSS metric group. The basic, Temporal and Environmental Metric group. #100DaysOfCyberSecurity @cyberjeremiah @CiscoNetAcad

Day 60/100 of My Cybsecurity Journey Studied a Module on Network profiling and Server Profiling . Also studied the elements that constitute the Network and Server Profiling. #100DaysofCybersecurity @cyberjeremiah @CiscoNetAcad @LearningatCisco @CISvolleyball

Day 59/100 of My Cybsecurity Journey Studied a Module on Endpoint Protection. How endpoints are protected using Host-based Malware Protection and how Host-based Intrusion Detection (HIDS) is designed to protect endpoints. #100DaysofCybersecurity @cyberjeremiah @CiscoNetAcad

Day 58/100 of My Cybersecurity Journey Learned more on cryptography. The two classes of encryption - Symmetric and Asymmetric encryption. Also studied the Public Key Infrastructure (PKI) and its applications. #100DaysofCybersecurity @cyberjeremiah @CiscoNetAcad @OnijeC


Day 57/100 of My Cybersecurity Journey. Completed the CCNA course on Switching, Routing and Wireless Essentials. Got my certificate and Verified Badge #100DaysOfCybersecurity @cyberjeremiah @NetworkQueenX @CiscoNetAcad @LearningatCisco @OnijeC


Day 56/100 of My Cybsecurity Journey Learned about the various types of Attacks and how to prevent them . Learned about the DNS Attacks, common Http Exploits , Email threats and Web-exposed Databases #100DaysOfCybersecurity @cyberjeremiah @NetworkQueenX @CiscoNetAcad

Day 55/100 of My Cybsecurity Journey Learnt how Predictive AI is used to analyze Malware using Behavioural Analysis, Network Activity, Persistence Mechanisms , Indicators of Compromise and Exfiltration attempts to analyze the Malware #100DaysOfCybersecurity @cyberjeremiah

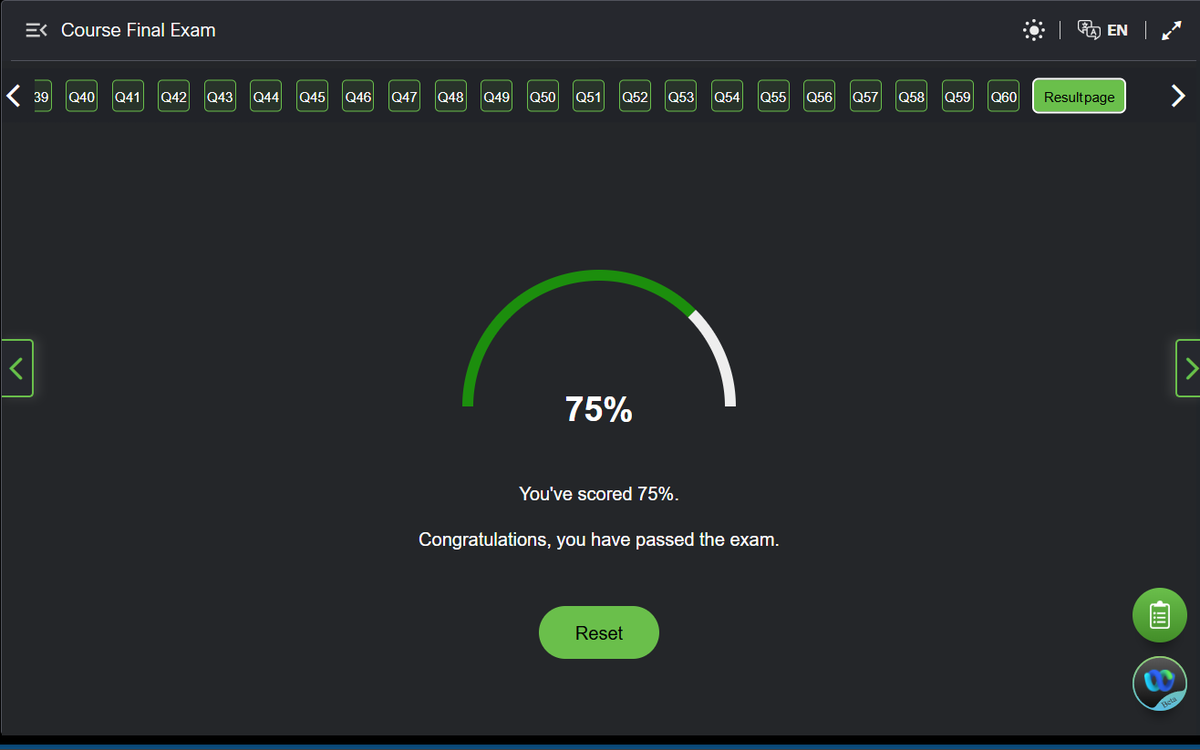
Day 54/100 of My Cybersecurity Journey Passed the final course exams on Switching, Routing and Wireless Essentials #100daysOfCybersecurity @NetworkQueenX @CiscoNetAcad @cyberjeremiah @OnijeC

Day 53/100 of My cybersecurity Journey Practiced and refreshed through the course on Switching,Routing, and wireless Essentials as I prepare to take the course final exams on netacad #100DaysofCybersecurity @cyberjeremiah @NetworkQueenX @CiscoNetAcad

Day 52/100 of My Cybsecurity Journey Learnt about how threat actors attack networks using different attack methods like the ICMP attacks , Spoofing attacks , TCP attacks, UDP attacks using vulnerabilities present in the network #100DaysOfCybersecurity @cyberjeremiah

Day 51/100 of My Cybersecurity Journey Studied a module on network security infrastructure on Netacad. devices used to protect networks like the Firewall, Intrusion detection system(IDS),and Intrusion Prevention System(IPS) #100DaysOfCyberSecurity @cyberjeremiah @NetworkQueenX