Sabitlenmiş Tweet

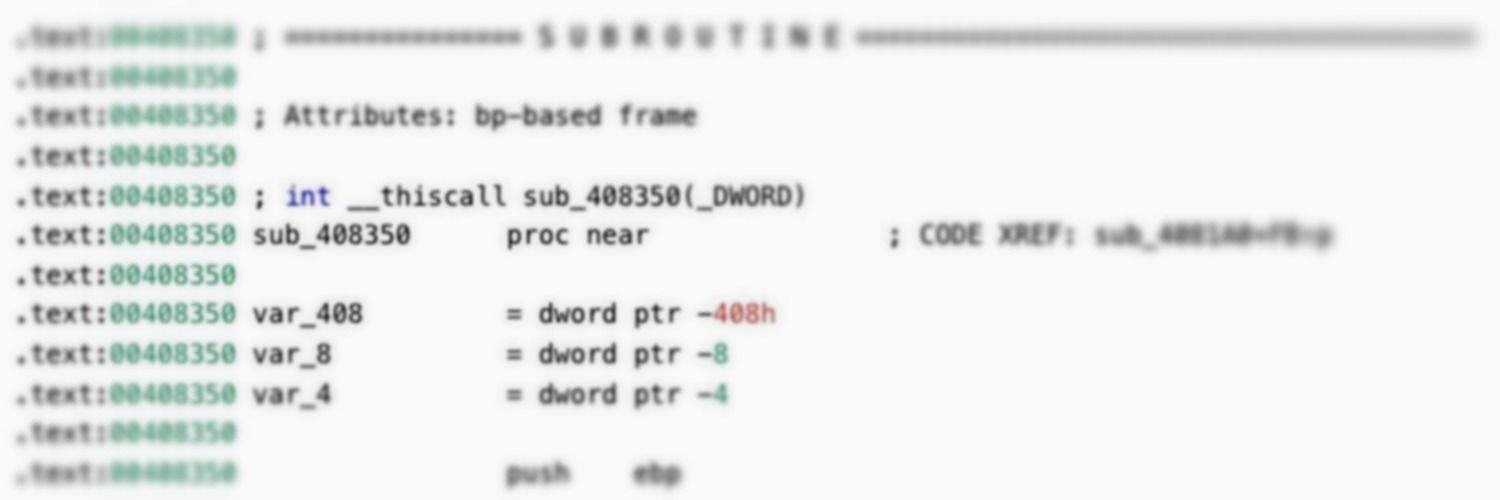
Dropping this today: ChamelGang & Friends | Cyberespionage Groups Attacking Critical Infrastructure with Ransomware
In collaboration with @JulianVoeg from @RecordedFuture
🧵A quick summary and a few thoughts on the use of RSW by APTs
s1.ai/Chamel-b
English