n3mo retweetledi

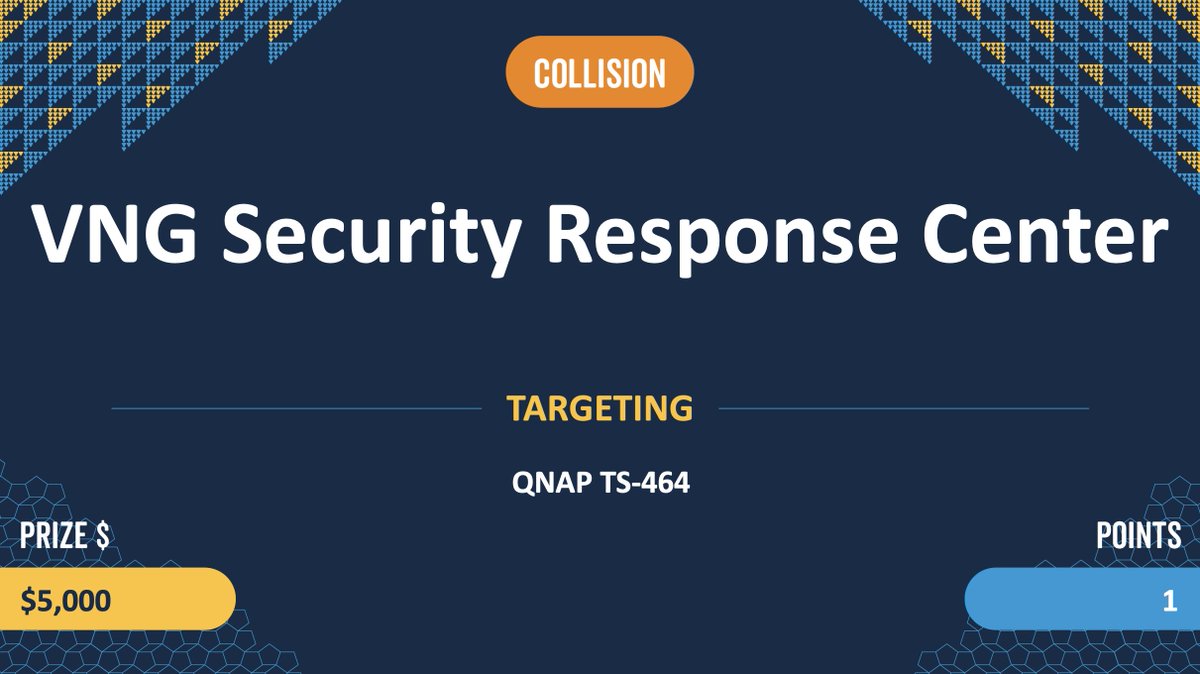
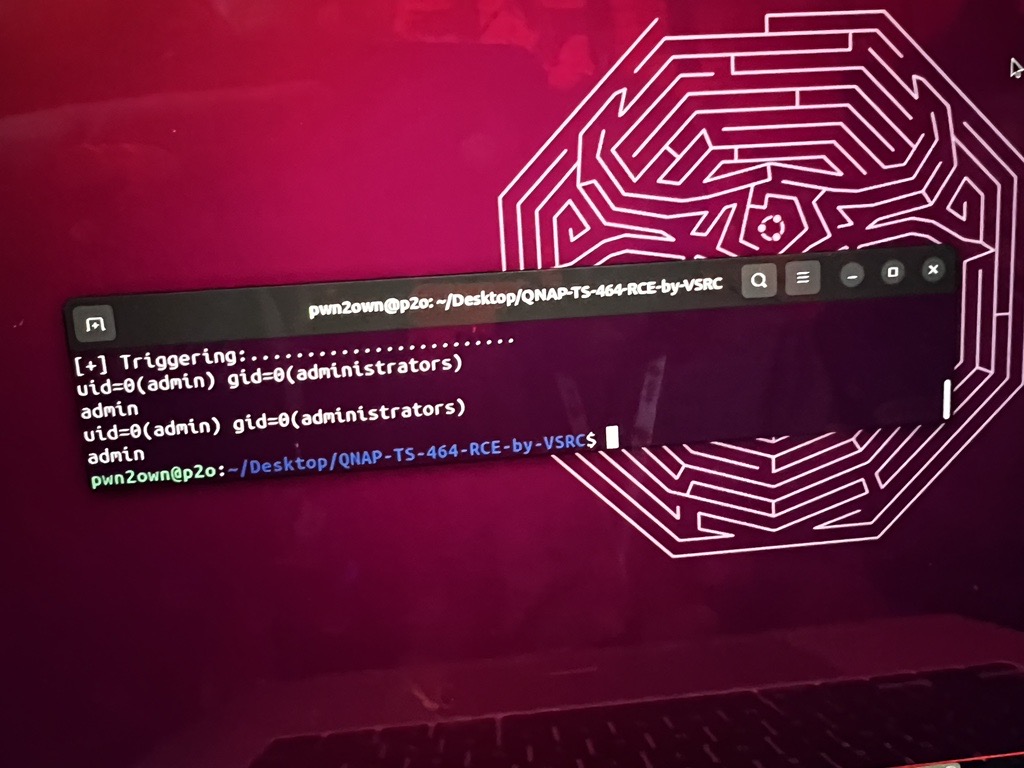
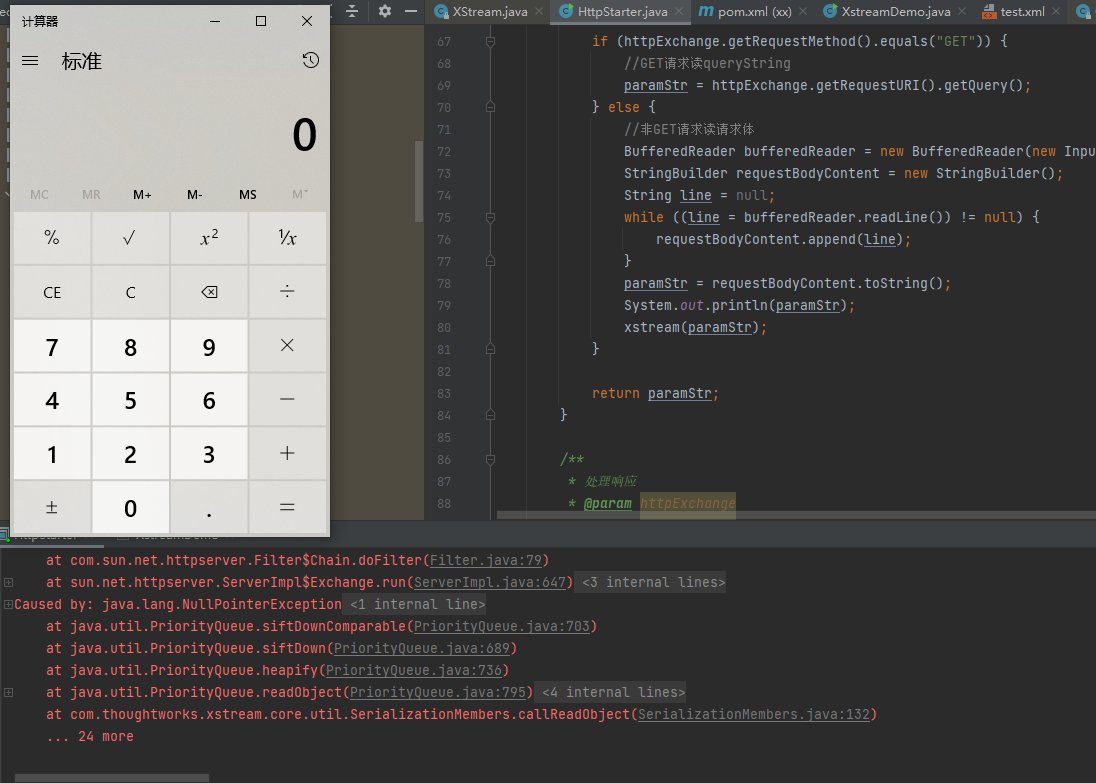
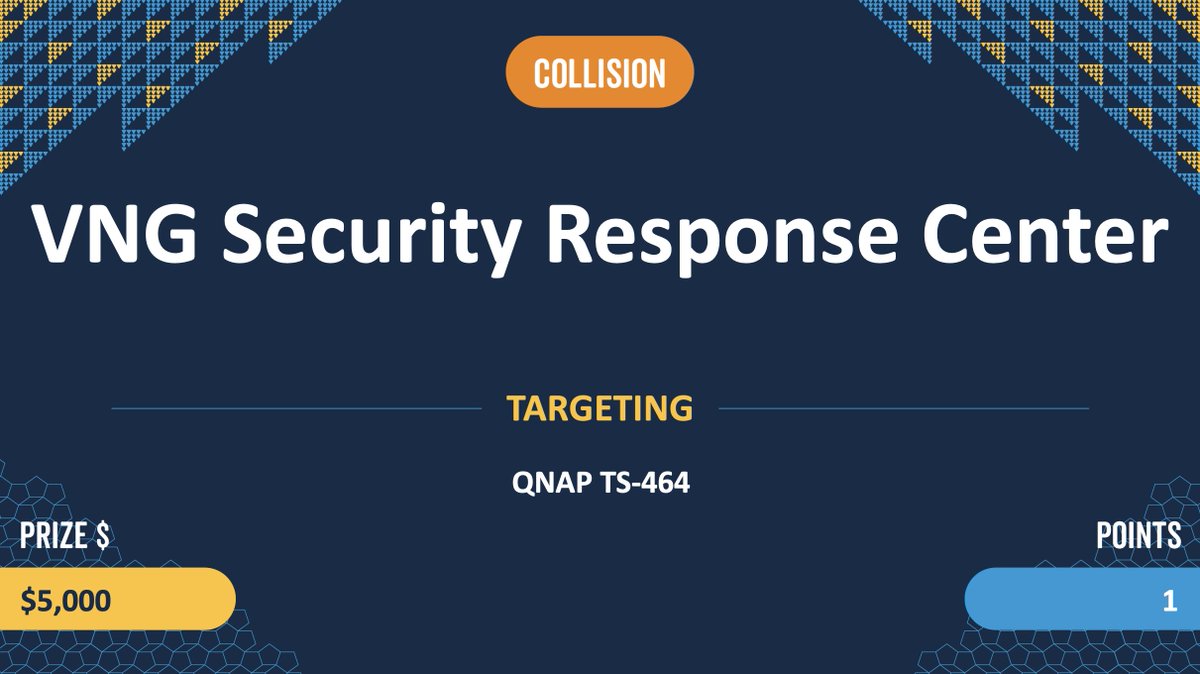
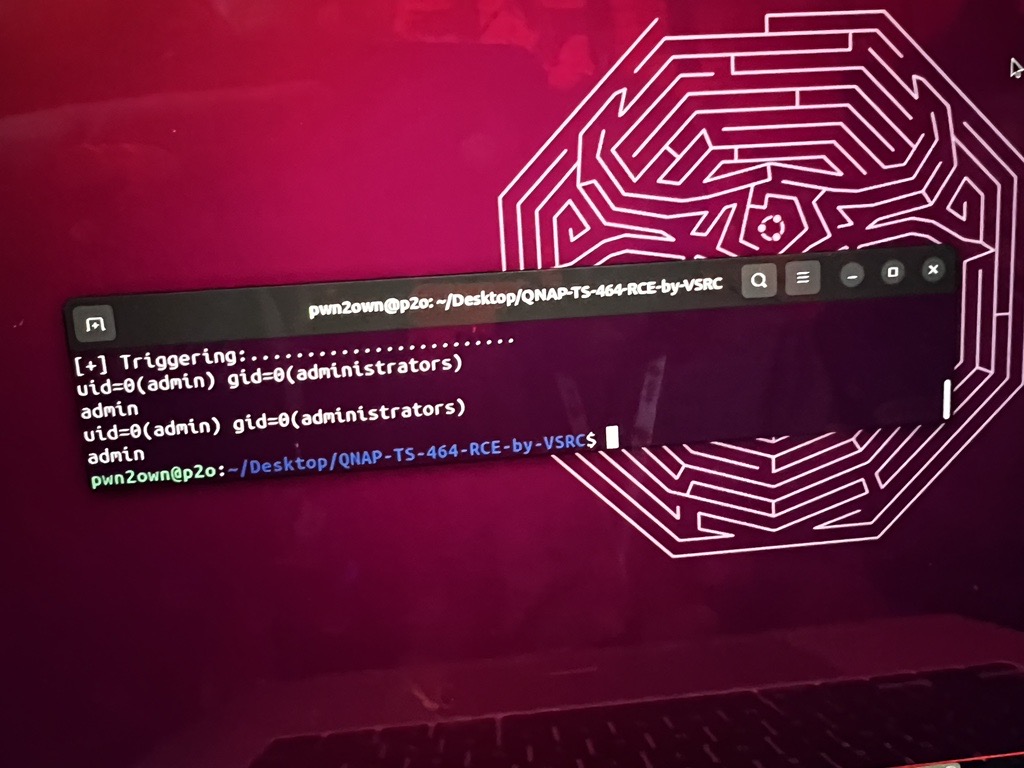
Collision – The VNG Security Response Center was able to execute a 2-bug chain against the QNAP TS-464. However, the exploit they used was previously known. They still earn $5,000 and 1 Master of Pwn point. #Pwn2Own
English
n3mo
21 posts