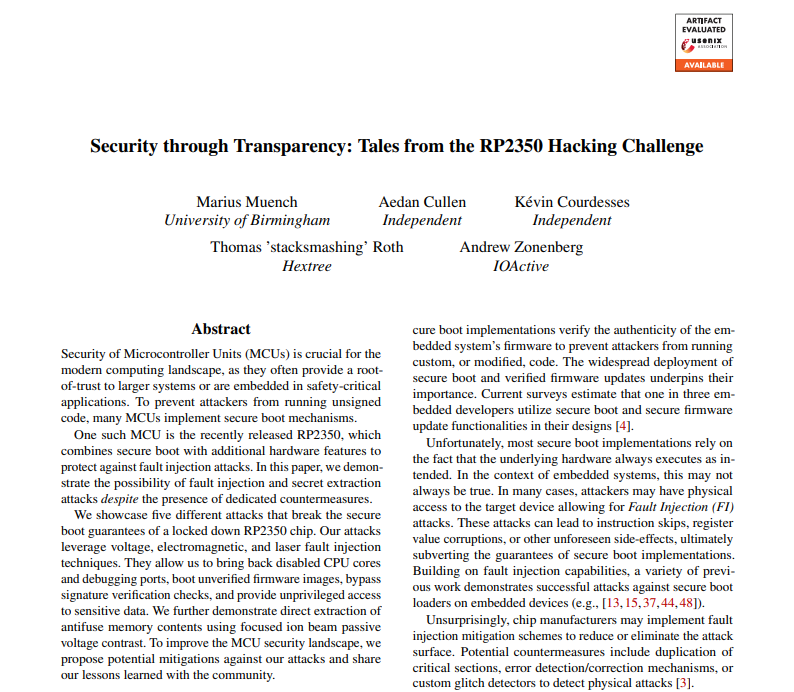
nSinus-R (@[email protected]) retweetledi

A virtual iteration of our training on fuzzing custom embedded systems is coming up end of March.
One cool story about this: The participants of our training in 2024 exploited a bunch of devices at Pwn2Own Tokyo 2026!🔥
Details: ringzer0.training/countermeasure…

English