nico_security
22 posts

nico_security
@nicoweb3audit
web3 security,I hope you can follow me. Thank you!



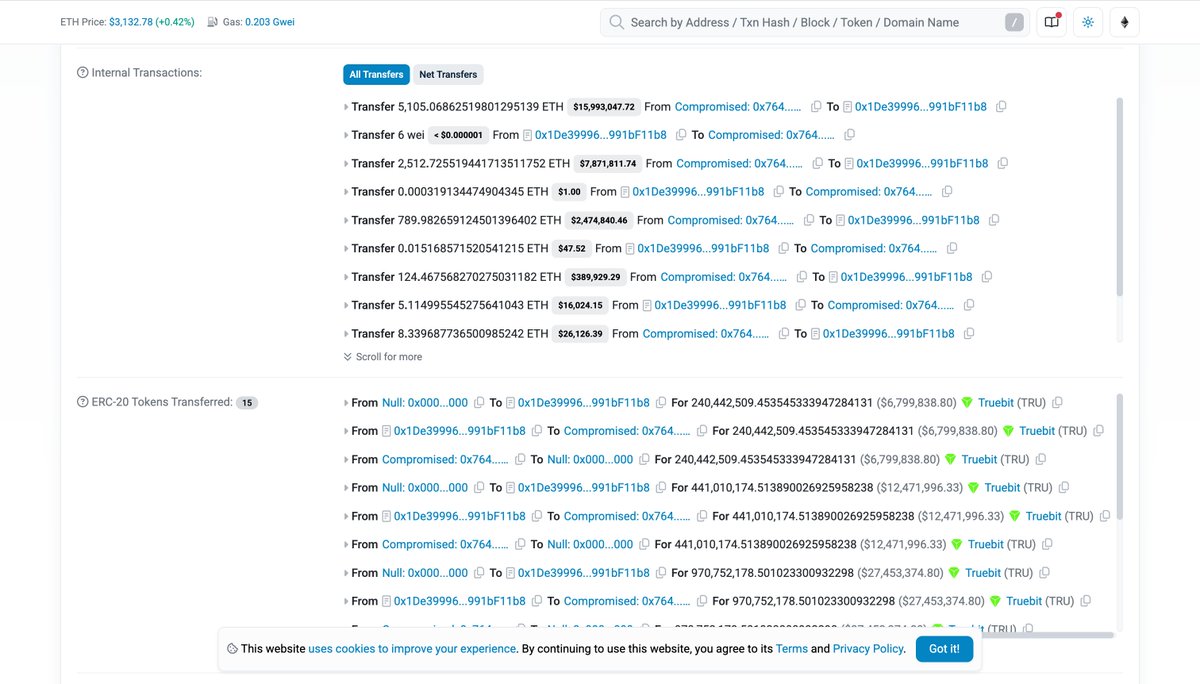



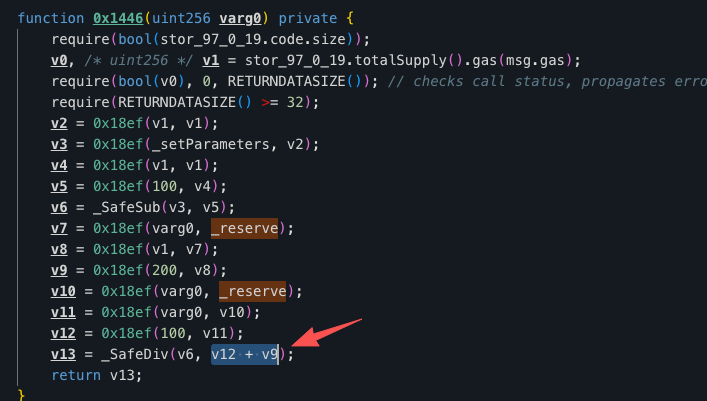
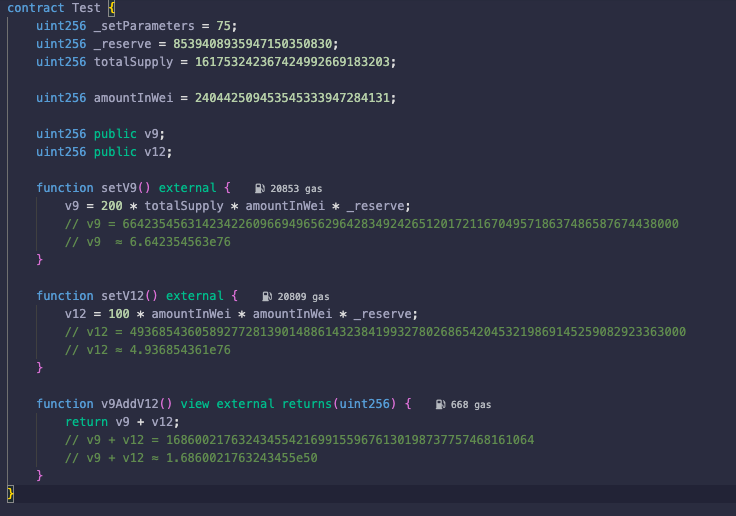
Another 26M hack. @Truebitprtocol I haven't decompiled the vulnerable code yet, but the root cause appears to be a mispriced minting function of its purchase contract that allows anyone to purchase TRU token at a very low price. The first attacker (26M profit): 0xcd4755645595094a8ab984d0db7e3b4aabde72a5c87c4f176a030629c47fb014The second attacker (~250k profit): 0x71496352b02f974a3898c1b743e9fc2befb935e6c2a3e421134ec09b63052f4b@Truebitprotocol This contract has been a very old contract deployed ~5 years ago... It seems old contracts are getting more "popular" among attackers now. btw a friend of mine shared me a screenshot of the second hacker celebrating in his chat group 😂 (not sure if it's genuine) --- Disclaimer: This is my prelminary analysis and I may make mistakes.