L
125 posts



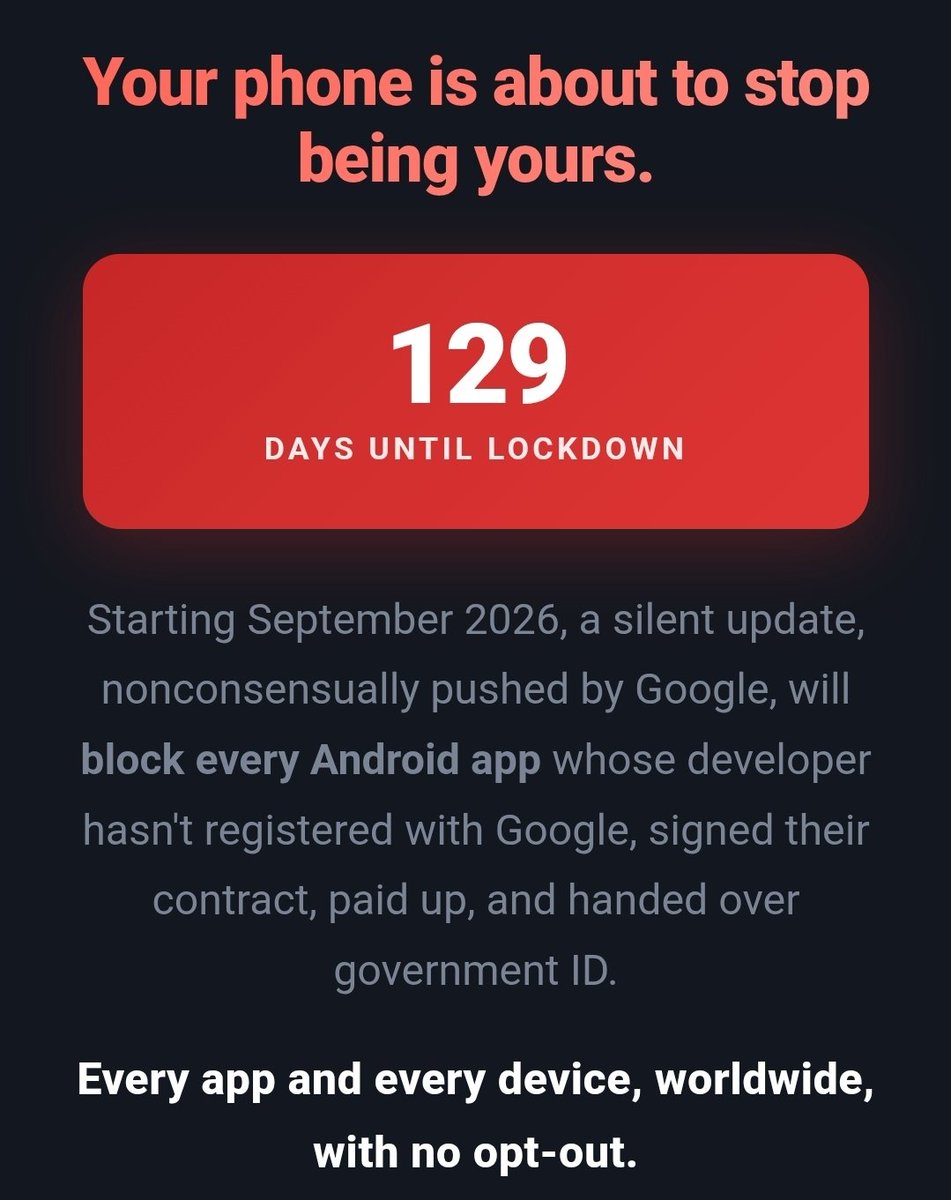
@nopolygons @AdamSimecka so to combat google get an OS that only works on google phones.. makes sense lol
English
L retweetledi
L retweetledi
L retweetledi
![Chef Winters [$BTC]](https://pbs.twimg.com/profile_images/1848772489952038914/9yKnQXFP.jpg)
@DoingFedTime my child is repeating sudo airmon-ng start wlan0 in their sleep, someone help
English
@DoingFedTime The "dark web" is actually a honeypot and your IP can be successfully unmasked 80% of the time.
English
L retweetledi

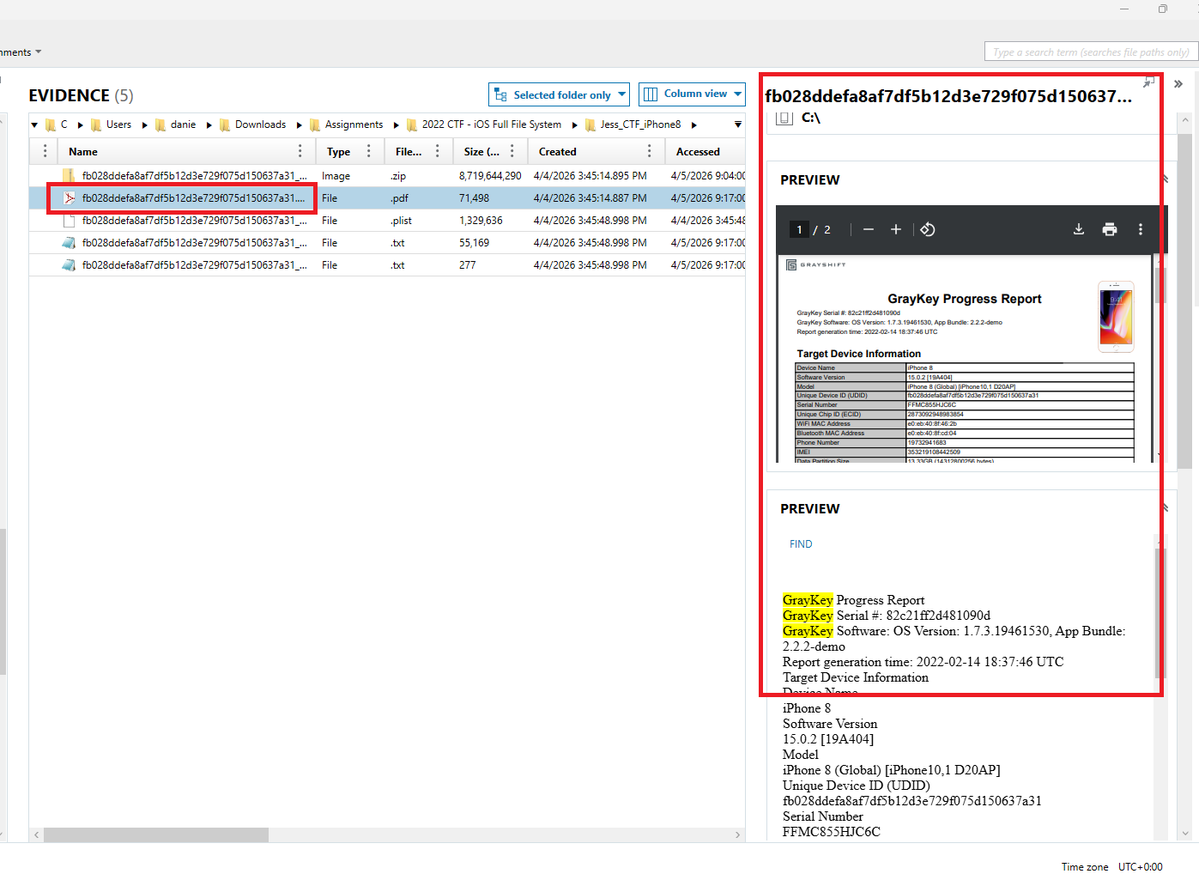
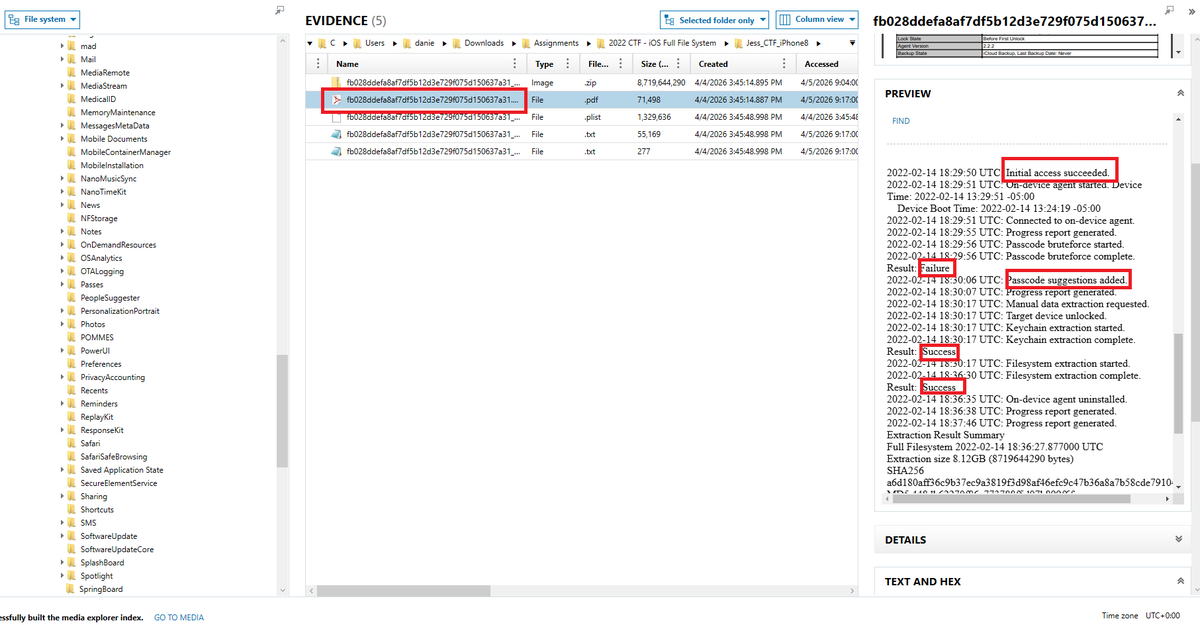
WHEN A LAW ENFORCEMENT OFFICER ATTEMPTS TO UNLOCK YOUR MOBILE DEVICE BY BRUTE-FORCEING IT USING TOOLS LIKE GRAYKEY OR VERAKEY.
I pulled a trace of gray key that was used in the iPhone while hunting for spywares and brute-force attacks.
If the FBI or a law enforcement officer, like police, seizes your phone and returns it, you can know if they performed a brute-force attack on it if you know you didn't give them the password to your phone. They Often use GRAY KEY or VERA KEY
Modern mobile operating systems and their underlying firmware maintain detailed security and diagnostic logs that can record authentication attempts and forensic access activity.
As a result, when tools such as GrayKey or other law enforcement-grade extraction systems are used to perform password brute forcing or advanced device access, traces of these operations may be recorded within system logs, diagnostic artifacts, or security event records on the device.
Attackers or suspects may also try to hide activity, but system-level artifacts can still reveal failed brute-force attempts.
FUN FACT
iOS devices often keep behind-the-scenes logs showing things like:
a. when a brute-force attempt started
b. when the device was finally unlocked
c. and even when extraction tools connected and disconnected.
That means a forensic examiner can sometimes tell not just that data was extracted… but how it was extracted and how long it took.
English

🚨 do you understand what just happened to your passwords
cpuid one of the most trusted sites in PC hardware.
hacked. April 10th, 2026. CPU-Z and HWMonitor. both compromised.
> fake CRYPTBASE.dll ships inside the installer
> connects to C2, downloads a C# file
> compiles it silently using YOUR own Windows tools
> injects into memory. never touches disk. AV sees nothing.
> opens Chrome's password vault. dumps everything.
the chain:
cpuid → HWMonitor installer → DLL hijack
→ supp0v3[.]com → silent .NET compile
→ in-memory injection → Chrome credentials stolen
same group. same C2 domain. hit FileZilla in March 2026.
they got lazy. that's the only reason we caught it.
vx-underground@vxunderground
Mr. Titus Tech is correct. cpuid-dot-com is indeed delivering malware right now. As I began poking this with I stick I discovered this is not your typical run-of-the-mill malware. This malware is deeply trojanized, distributes from a compromised domain (cpuid-dot-com), performs file masquerading, is multi-staged, operates (almost) entirely in-memory, and uses some interesting methods to evade EDRs and/or AVs such as proxying NTDLL functionality from a .NET assembly. The C2 domain present in one of the binaries is a clear IoC. This is the same Threat Group who was masquerading FileZilla in early March, 2026. They've been busy.
English
L retweetledi

This is Senate House in London. When George Orwell wrote 1984, the building served as the model for the headquarters of the Ministry of Truth (the propaganda ministry). The Ministry of Truth decided what was true, for example that 2+2=5. It was responsible for censorship and rewriting history, and it banned the word “free” in the sense of freedom.
When we projected our banned TV ads onto buildings in London, we thought this would be a fitting location. Nineteen Eighty-Four was supposed to be a warning, not an instruction manual.

English

A technical glitch in the mobile apps of Lloyds, Halifax, and Bank of Scotland allowed some UK customers to briefly view other users' transactions, including wages, payments, and personal details
“I can see another person’s bank account, he got paid £6,000 yesterday ... I can see where they work, almost their whole identity”
Via: dexerto


English
L retweetledi
L retweetledi
L retweetledi
L retweetledi
L retweetledi
L retweetledi

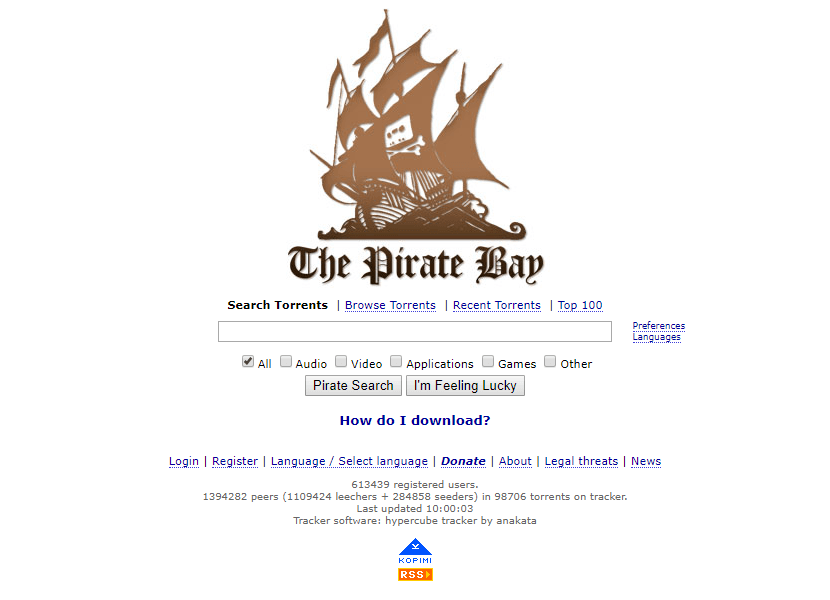
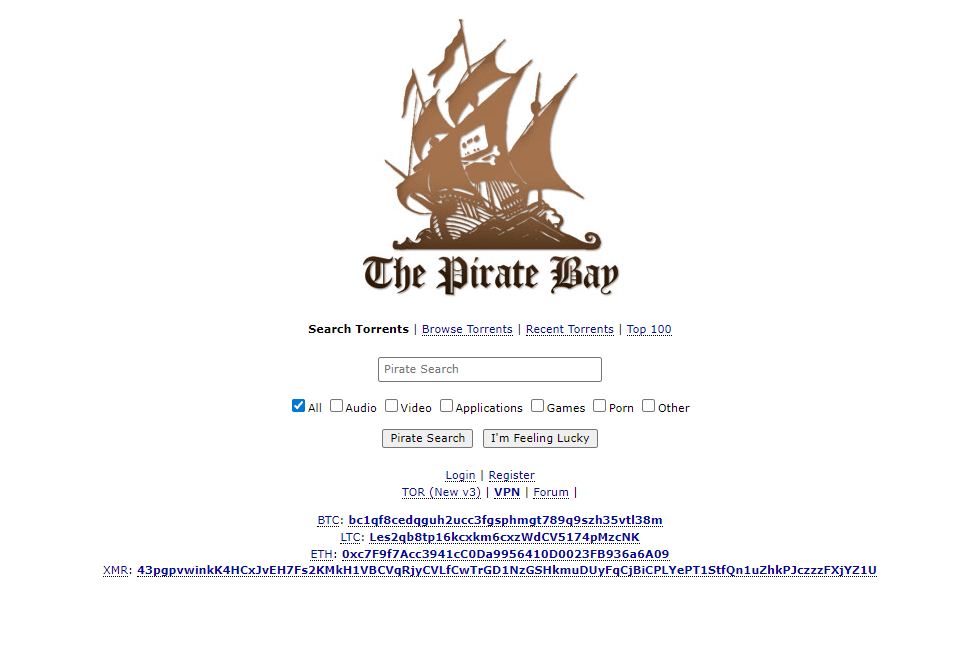
21 years of evolution of web design trends.
The Pirate Bay homepage in 2005
vs.
The Pirate Bay homepage in 2026
#WebDesignHistory
English