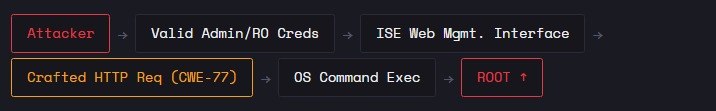
🚨 THREAD: 1,300+ Microsoft SharePoint servers are still wide open to an actively-exploited zero-day — CVE-2026-32201. No auth. No user click.
techgines.com/post/cve-2026-…
#CVE202632201 #SharePoint #CyberSecurity #ZeroDay

English
Techgines
325 posts

@nxtgen579255
🚀 Daily Tech & Business Updates 🔍 Breaking AI, Startup, & Industry Trends 📊 Insights on Innovation & Growth 📩 Stay Ahead. Stay Informed. #Tech #AI #business