Off By One Security
137 posts

Off By One Security
@offby1security
New streams every Friday! All channel proceeds go back to the community! Check out https://t.co/um6KVfwMFJ for our AI-powered offensive security testing platform!
California, USA Katılım Haziran 2024
2 Takip Edilen1.5K Takipçiler
Off By One Security retweetledi
Off By One Security retweetledi

Automated Reverse Engineering with LibGhidra, GhidraSQL, and AI Agents x.com/i/broadcasts/1…
Română
Off By One Security retweetledi

The stream below with @allthingsida is tomorrow (Friday) at 11AM PT!
Stephen Sims@Steph3nSims
Join us next Friday, May 8th at 11AM with Elias Bachaalany (@allthingsida) for the next @offby1security stream on, "Automated Reverse Engineering with LibGhidra, GhidraSQL, and AI Agents! youtube.com/watch?v=9avSjD…
English
Off By One Security retweetledi
Off By One Security retweetledi

Join us next Friday, May 8th at 11AM with Elias Bachaalany (@allthingsida) for the next @offby1security stream on, "Automated Reverse Engineering with LibGhidra, GhidraSQL, and AI Agents!
youtube.com/watch?v=9avSjD…
YouTube
English
Off By One Security retweetledi

We at @offby1security saw an interesting defense against AI-powered offensive agents recently. Fingerprinting of the agents performing the testing resulted in misleading, honeypot-like responses, attempting to distract or redirect them. It didn't work but worth noting.
English
Off By One Security retweetledi

Please join me on the next @offby1security stream tomorrow (Friday) at 7AM PT / 4PM CEST with @Libranalysis for a session on "Live Malware Unpacking: Debugging AgentTesla with DotDumper!"
youtube.com/watch?v=n0P_JG…
YouTube
English
Off By One Security retweetledi

Would you be interested in a stream on the @offby1security channel covering the costs between using different Frontier models to discover the same vulnerabilities and the changes to the prompts and testing methodologies to find them?
English
Off By One Security retweetledi

Offensive Security in Web3 from Exploit Mindset to DeFi Precision Bugs with Josselin Feist x.com/i/broadcasts/1…
English
Off By One Security retweetledi

I will be on @offby1security's stream tomorrow with @Steph3nSims
We will be live, so come join and ask anything
Stephen Sims@Steph3nSims
Join me this Wednesday at 10AM PT for the next @offby1security stream with guest Josselin Feist (@Montyly) for a session on "Offensive Security in Web3: From Exploit Mindset to DeFi Precision Bugs!" youtube.com/watch?v=HuWi86…
English
Off By One Security retweetledi

Join me this Wednesday at 10AM PT for the next @offby1security stream with guest Josselin Feist (@Montyly) for a session on "Offensive Security in Web3: From Exploit Mindset to DeFi Precision Bugs!"
youtube.com/watch?v=HuWi86…

YouTube

English
Off By One Security retweetledi

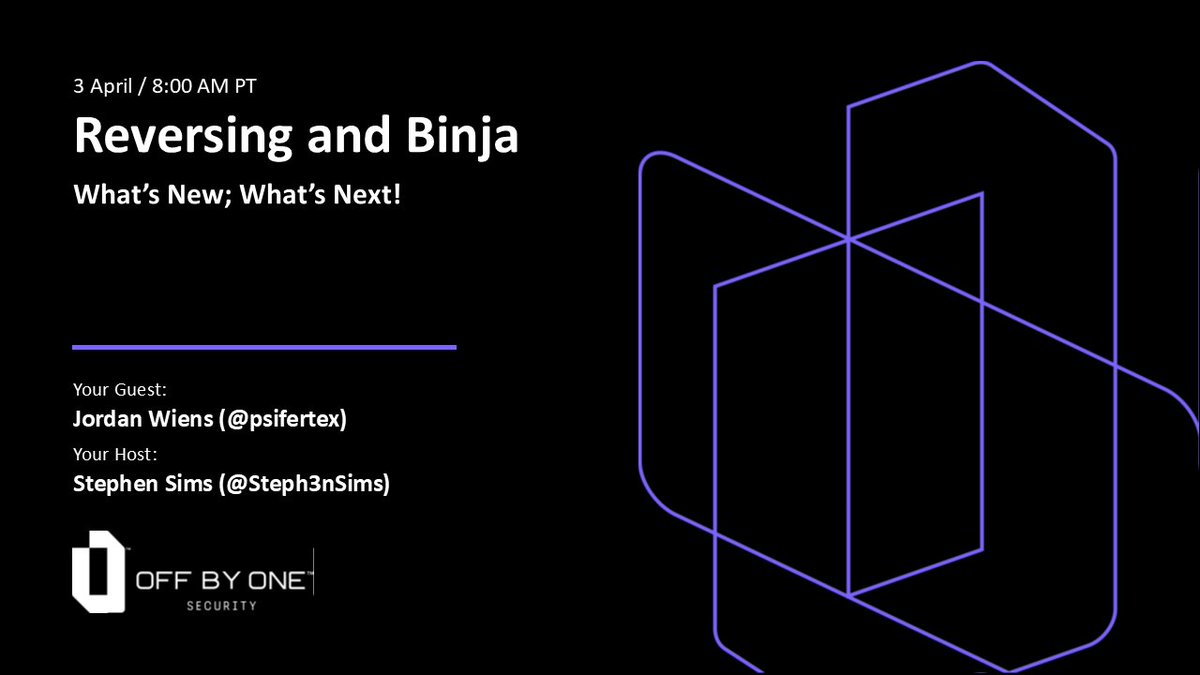
Great @offby1security stream with @psifertex today now available on YouTube here: youtube.com/watch?v=bJxEtx…
YouTube
English
Off By One Security retweetledi
Off By One Security retweetledi

Join me tomorrow, April 3rd at 8AM PT for the next @offby1security stream with @psifertex (Jordan Wiens) for a session on "Reversing and Binja: What's New; What's Next!"
youtube.com/watch?v=bJxEtx…
YouTube
English
Off By One Security retweetledi
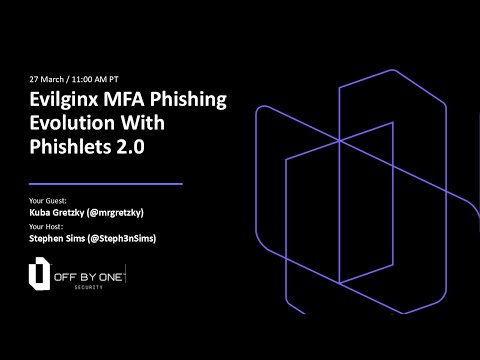
I'm very excited to announce that last Friday, I had the privilege of making the first public reveal of the upcoming Phishlets 2.0 update for Evilginx on the Off By One Security stream. 🪝🐟
The live demos consisted of:
- Examples of how the new Phishlets 2.0 format allows for modifying every part of reverse proxied HTTP traffic during a phishing attack.
- FIDO MFA downgrade phishing attack against a Microsoft account, through live modification of MFA configuration in JSON format.
- Reveal of the entirely new "Reverse Input Proxy" phishing technique, involving Evilpuppet and a background browser to perform a FIDO MFA downgrade phishing attack against a Google account (without the need to reverse proxy the targeted website).
I strongly hope the Phishlets 2.0 update will be a game-changer for phishing attack simulation, and that red teams will finally have all the tools they need to simulate the most advanced attacks in the wild.
If you have any suggestions, criticisms, or general feedback, this is the best time to let me know. I would love everyone, especially Evilginx Pro users, to share their opinions, as my priority is to make the red team's job easier and more fun!
And yes, I plan to release a batch of ready-to-use phishlets in the new format, with the Phishlets 2.0 update coming first to Evilginx Pro, in the upcoming months, to get everyone up and running.
Enjoy the watch!
Video: youtube.com/watch?v=eeauoO…
Learn more about Evilginx Pro: evilginx.com
YouTube
English
Off By One Security retweetledi