OSSTMM retweetledi
OSSTMM
358 posts


OSSTMM
@osstmm
The official account for the Open Source Security Testing Methodology Manual. Pronounced "aw-stem". A tool designed to research how security works.
Katılım Şubat 2014
10 Takip Edilen409 Takipçiler
OSSTMM retweetledi
OSSTMM retweetledi
OSSTMM retweetledi

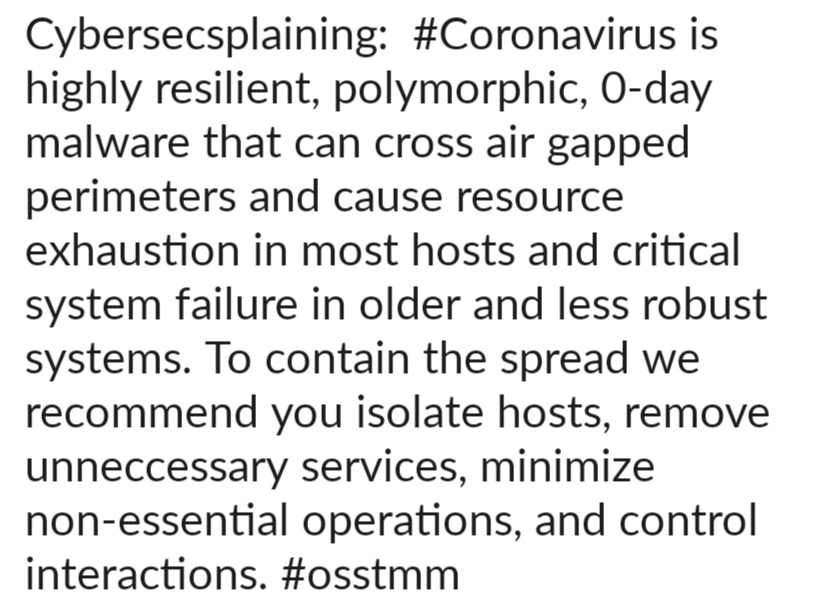
#coronavirus This is not rocket biology my #cybersecurity friends. You've got this. Create a physical separation between the threat and the asset. Reduce interactions. Apply both ingress and egress filtering. Stay strict with your hygiene. Beware misinformation.
#Covid_19 #OSSTMM
English
OSSTMM retweetledi

#coronavirus Keep calm and react. This is about security not Risk. Reduce your Attack Surface and protect your interactions. Remove unneeded services. Use controls for necessary operations. Remember a compromised host is a danger to other hosts.
#Covid_19 #CyberSecurity #OSSTMM
English
OSSTMM retweetledi

#Cybersecurity Island, the Unfortunate Reality Show. The show starts as contestants are forced to grab all the cybersecurity products they can off a boat and get to shore. With just their wits and a default Windows install, they must survive... @peteherzog bit.ly/33rhwlF

English
OSSTMM retweetledi
OSSTMM retweetledi
OSSTMM retweetledi

Training AI through Social Engineering Techniques on Feb. 25th in Cardiff! Just got my invite! Come see the presentation and the demo! Details here: eventbrite.co.uk/e/ai-for-finte…
English
OSSTMM retweetledi

There is something pathetically optimistic about cybersafety.
There is something quietly unsettling about cybersecurity.
There’s something nauseously helpless about being breached.
What to do guidelines for what to do when you're breached: threatvector.cylance.com/en_us/home/so-…
English
OSSTMM retweetledi
OSSTMM retweetledi

#Cybersecurity Island, the Unfortunate Reality Show. The show starts as contestants are forced to grab all the cybersecurity products they can off a boat and get to shore. With just their wits and a default Windows install, they must survive... @peteherzog bit.ly/33rhwlF

English
OSSTMM retweetledi
OSSTMM retweetledi

#Cybersecurity Island, the Unfortunate Reality Show. The show starts as contestants are forced to grab all the cybersecurity products they can off a boat and get to shore. With just their wits and a default Windows install, they must survive... @peteherzog bit.ly/33rhwlF

English
OSSTMM retweetledi

Hacking for College Students: Here's an excerpt from my book-in-process- linkedin.com/pulse/fake-ids…
#CollegeStudent #college #hacking #privacy #homemadeartwork
English
OSSTMM retweetledi
OSSTMM retweetledi

Is this more like cyber-deterrence or social engineering? #CyberWarfare #cyberwar
@hackerhigh @osstmm

English
OSSTMM retweetledi
A repeat of our annual Black Friday Offer:
Create as many Canarytokens as you want, completely free¹ at canarytokens.org.
At this price, you’d be crazy not to sprinkle some around your network.
__
¹ Tokens only free till heat death of Universe;
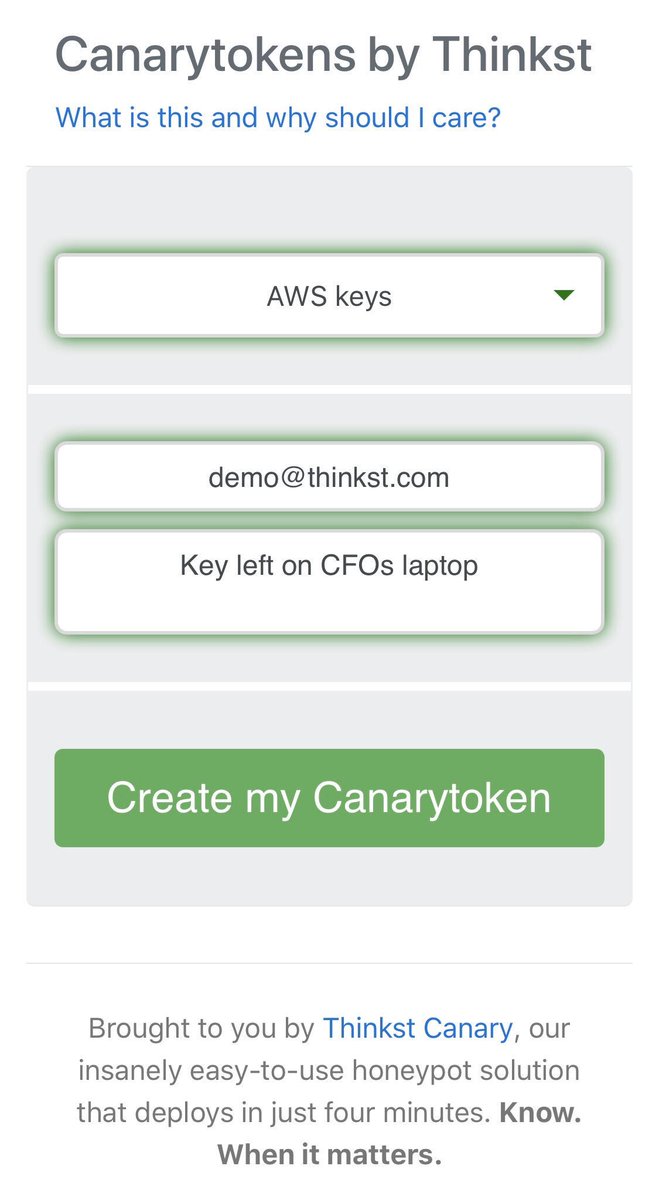
English
OSSTMM retweetledi

#Cybersecurity Island, the Unfortunate Reality Show. The show starts as contestants are forced to grab all the cybersecurity products they can off a boat and get to shore. With just their wits and a default Windows install, they must survive... @peteherzog bit.ly/33rhwlF

English
OSSTMM retweetledi

I can attest to the fact that defenders prefer to have PoCs to better understand, prioritize, and fix security issues.
As a researcher, it’s your own bug — you can do whatever you want with it.
And please stop saying “responsible” disclosure. No need for moral judgements here.
Maddie Stone@maddiestone
@Fox0x01 We clearly disagree on this 😏 Providing POCs helps defenders more than attackers. Defenders often use POCs to build detections and develop new solutions to mitigate not just the big but also exploit techniques.
English