outoflegend
348 posts



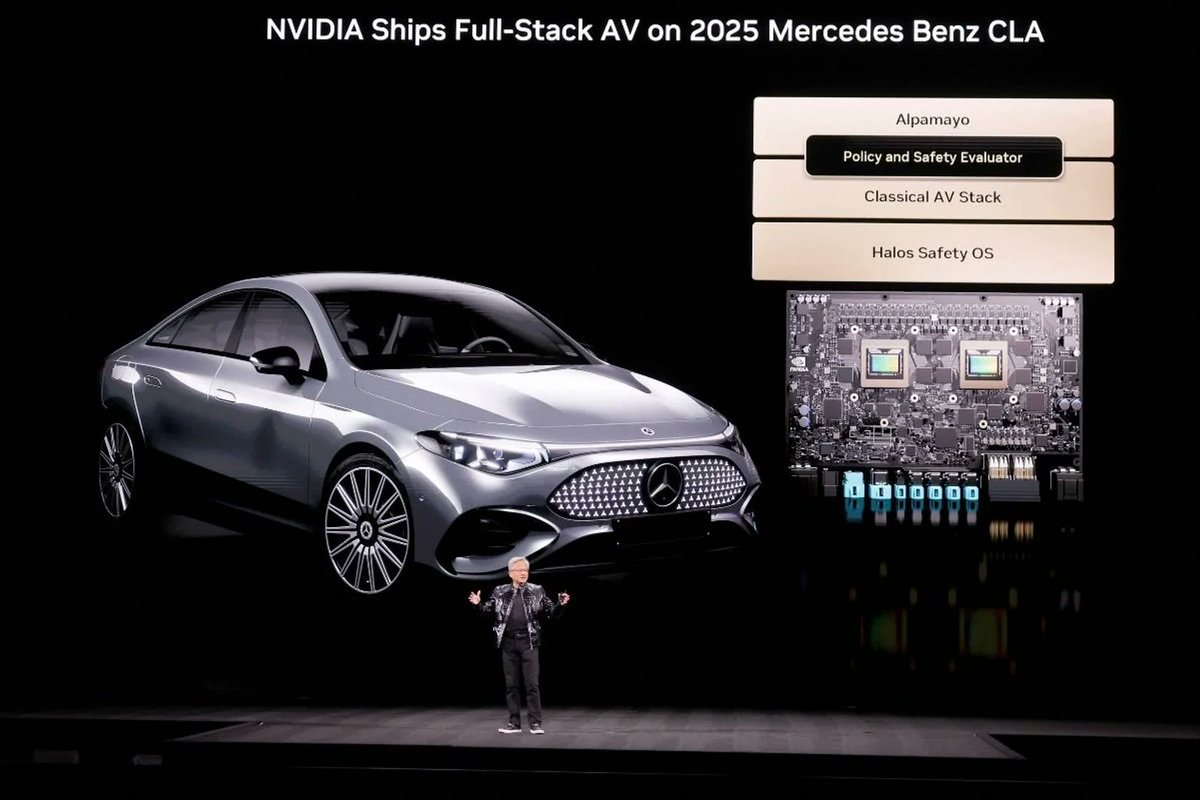
Loved Jensen's self-driving presentation! The approach is just like ours @comma_ai . Open-source, end-to-end, worldmodel simulator, and they make their own computers/datacenter.
Only small difference is they have 100x the people, 1000x the funding and they make their own chips!
English
outoflegend retweetledi
Fixed in 2018, but many user wallets got hacked in 2023. @teawaterwire and I are one of them. The Lubian hack is not related with Trust Wallet. This is the FUD part. However, Trust Wallet team lied about many things in their statement.
Trust Wallet admitted their product had a vulnerability in 2018 but vehemently denies that it affected their users in the mass wallet theft incident of 2023. They claim to have notified all affected users back in 2018 to migrate their assets, which is clearly a lie fabricated for PR purposes.
We previously disclosed the vulnerability in Trust Wallet for iOS from 2018. Any security issue related to Binance easily turns into FUD, which in turn triggers a knee-jerk reaction from Trust Wallet. It's actually normal for any software to have security vulnerabilities; what matters most is how they are handled properly.
Here is our previous disclosure post about the Trust Wallet iOS vulnerability: x.com/ErrNil/status/…
And here is Trust Wallet's announcement after the issue gained traction: x.com/TrustWallet/st…
After the last incident, I was quite disappointed with Trust Wallet's response and lost interest in following up on the case. However, whenever I see PR statements that I find obviously incorrect and illogical, I always feel uncomfortable and have to speak my mind. So I'm taking this opportunity to discuss some of these points, just to leave a record.
Trust Wallet mentioned that the number of affected users at the time was about 10,000 early adopters, and that they had notified each one and provided an asset migration plan. They claim no users suffered losses and all affected wallets have been deprecated.
In fact, this is highly counterintuitive. Trust Wallet was extremely popular in 2018, which led to its acquisition by Binance. In such a situation, notifying 10,000 users about a security issue with their wallets and getting them to migrate would have been a tricky affair. If they had really done it, it would have almost certainly made the news. My own first Trust Wallet address was also generated in 2018 and was drained in the July 2023 incident. I have no memory of ever receiving any notification. This user's situation is the same as mine: x.com/teawaterwire/s…
Trust Wallet mentioned that since July 2018, all new wallets created by Trust Wallet users are no longer affected by this vulnerability.
This is also patently false. How can you guarantee that every single one of those 10,000 users updated their software to the latest version? If someone downloaded the problematic version at the time and never updated the app, then all addresses created with that version of the wallet would be permanently insecure and vulnerable to theft.
Trust Wallet mentioned that the comprehensive evidence suggests the 2023 attacks did not originate from a Trust Wallet vulnerability, but were more likely caused by a combination of multiple sources. They state they have full confidence that the 2018 vulnerability was not the root cause of this incident.
This is a very clever, but highly inaccurate, turn of phrase. In reality, while the 2018 Trust Wallet vulnerability was not the *sole* root cause of all the wallets drained in July 2023, it was a major contributor. The reasons are as follows: real Trust Wallet users were affected; the affected addresses could be reproduced using Trust Wallet's code from that time; and the activity timeline of the affected wallets highly correlates with Trust Wallet's code commit history. We discussed this in more detail in our original disclosure article, so I won't repeat it here.
Trust Wallet mentioned that in addition to fixing the vulnerability, the founder of Trust Wallet proactively contacted affected users to provide them with a secure migration path, ensuring no users remained at risk. They also state that the relevant affected addresses have all been confirmed to no longer hold any balance.
The part about confirming the relevant addresses no longer hold a balance is the most ridiculous part, because these addresses were cleaned out in July 2023.
I am also a heavy Trust Wallet user. The theft from my first Trust Wallet address in July 2023 prompted me and my colleague @outoflegend to conduct an in-depth investigation.
However, what truly made me lose my "Trust" in it was Trust Wallet's subsequent response and handling of this vulnerability. I can partly understand, as every wallet provider wants to have a perfect security record. I sincerely hope Trust Wallet can do better, provide more evidence, and dispel the community's doubts.
I have deliberately not deleted my first Trust Wallet address; I just added "Rekt" to its name.
@cz_binance @heyibinance I have great respect for you. Were you also deceived by your team, or were you in on it too?
I hope they/you can provide any valid evidence that they notified 10,000 users to migrate.
English

@outoflegend @comma_ai even comma ai cannot force a bmw to use turn signals
English

Lateral control completed.
BMW accepts steering angle control, I think OpenPilot can handle a U turn😄 @comma_ai
English

@Jonesderbozz @pauliusdotpro @comma_ai Ah, these are codes defined by manufacturers, they let us refer to specific models and years.
English

@outoflegend @pauliusdotpro @comma_ai Wayyyy to many abbreviations. If you want people to be interested, don't gate keep like that
English

@outoflegend @comma_ai Is this the low cost MITM with raspberry pi?
English

@pauliusdotpro @comma_ai BMW SP2018 with 5AU (currently the MITM module requires the SAS module, though this may change in the future).
The video shows a 2020 G38(same as G30) LCI.
English

@outoflegend @comma_ai Which bmw models /year would support it?
English

Many thanks to the author of this blog post @PD0WM , it was very inspiring: icanhack.nl/blog/audi-flex…
outoflegend@outoflegend
Hello @comma_ai , BMW porting is on the way. Use 2 cheap FlexRay transceivers and 1 Raspberry Pico2 to perform the MITM, it’s super low cost. github.com/dynm/pico-flex…
English

@siddzzz @comma_ai @Raspberry_Pi @PD0WM Yes.
But for now, it relies on the stock ADAS module to obtain the frame template and replace specific values so OpenPilot can take over.
English

@outoflegend @comma_ai @Raspberry_Pi @PD0WM @comma_ai does this open up ton of german cars ? That would be awesome… great job @outoflegend .. cant wait
English

Hello @comma_ai , BMW porting is on the way.
Use 2 cheap FlexRay transceivers and 1 Raspberry Pico2 to perform the MITM, it’s super low cost.
github.com/dynm/pico-flex…
English

I have a lot of respect for Solana but Starknet is better.
It has higher scale and a better approach to scale - which is not by increasing the CPU/memory of those who want to track the network and validate it.
Let me repeat that: NOT BY INCREASING CPU/MEMORY OF THOSE WHO WANT TO TRACK THE NETWORK AND VALIDATE IT.
Starknet can support massive compute (for perps, gaming, other TPS-hungry use cases) that Solana cannot offer, meaning Starknet's heavy-computing exchanges (like Extended and Paradex) will give better value to users.
We can process transactions in the thousands of TPS, including very complex ones.
Most crucially, as we continue to scale Starknet to 10K and 100K TPS we can do so *without* requiring end users to purchase a server.
Use the very same laptop as you do today🙂
English

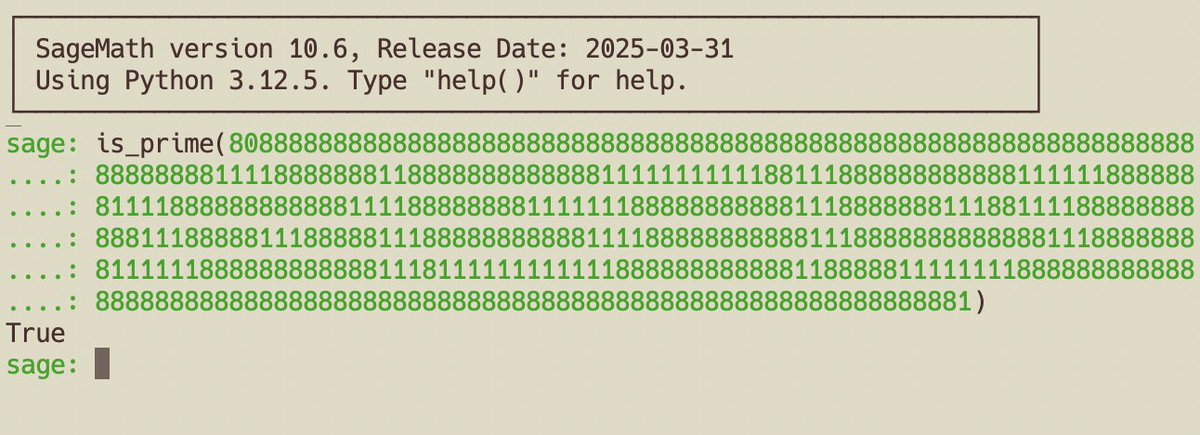
grok field? p=808888888888888888888888888888
888888888888888888888888888888
888888888888811118888888118888
888888888111111111118811188888
888888811111188888881111888888
888888111188888888111111188888
888888111888888811188111188888
888888111888881118888811188888
888888111188888888888111888888
888888811188888888111111888888
888888111811111111111188888888
888811888881111111188888888888
888888888888888888888888888888
888888888888888888888888888881
Nederlands

Many MEV bots monitor addresses with compromised private keys, instantly draining ETH mistakenly sent to them. For example, Hardhat’s default mnemonic, "test test test test test test test test test test test junk", derives the address 0xf39Fd6e51aad88F6F4ce6aB8827279cffFb92266.
With EIP-7702, anyone can set code for these addresses, effectively installing a hook. If ETH is sent to such an address, a fallback function can automatically redirect the funds to another address. For instance, this transaction (etherscan.io/tx/0xa85d9502f…) demonstrates this behavior.
Check #authlist7702" target="_blank" rel="nofollow noopener">etherscan.io/address/0xf39F…: the latest delegated address is 0x930FcC37d6042c79211EE18A02857Cb1Fd7F0D0b, which implements the fallback function.
The alarming part? Setting code for an address only requires a signature, included in the authorization_list of a type 0x04 transaction. This transaction’s to field can be any address, meaning there’s no direct on-chain interaction with the target address. You can’t easily detect if an address has been set with code by checking its transaction history.
Imagine this scenario: you create a new wallet, but its keys are accidentally leaked. Someone sets malicious code on your address. Later, when you receive ETH, the funds are automatically drained without your knowledge.
I urge wallet developers to implement a check using eth_getCode to alert users if their EOA has unexpected code, enhancing security against such risks.
@officer_secret @blockaid_ @elyx0
English

@DefiIgnas It's so simple to increase the gas limit, why wasn't it done before L2 was born?
English

$ETH ultrasound narrative is dead!
Or is it?
As EF scales the L1 and $ETH pumps, the ultrasound narrative is coming back. What a surprise :)
I'm not the first to write about it, but the market is yet to internalize the message.
The logic goes like this:
Gas limit (now ~36M) could hit 150M, boosting L1 scalability. Critics would say "oh that's bad, because lower fees burn less $ETH. Buy my alt-L1!"
That's the old thinking.
True that more txs per block = lower fees, but more activity could mean more ETH burned.
Higher gas limit → more txs outweigh lower fees → potentially more burn.
As @hanni_abu calculates, "at 36M and the deflationary threshold it 14.5 gwei.
At a 300M gas limit the deflationary threshold becomes 1.74 gwei (14.5gwei*36M/300M)."
He also adds that as gas prices drop, users are more willing to pay higher fees during congestion:
E.g., at $0.01, a 100% premium to $0.02 feels more acceptable than jumping from $5 to $10.
Lower prices make people less sensitive to congestion fees.
Sounds freaking amazing but here's a big question: Will users flock back to the L1?
Active addresses haven't grown on Ethereum for years.
Bad UX (approve+swap), slow and expensive txs are the main reasons but issues are being addressed (Pectra!)
So for ultrasound narrative to come back we need to see users and activity coming back to the L1.
It's a big pivot from pushing users out of the L1 to L2s.
Tbh, I do want users to come back, but it does put pressure on non-specialized L2s.
In any case, the following months and years are crucial for ETH: will users come back to the L1 and devs build new use cases on mainnet?
And if yes, will increase activity burn more ETH despite lower fees?
For the sake of my bags, I hope so!
As always, let me know what I might be missing here.
English

@cognitivecompai @ollama don’t forget to set the following parameters:
PARAMETER top_p 0.8
PARAMETER temperature 0.7
PARAMETER top_k 20
As recommended in the Best Practices section for non-thinking mode #best-practices" target="_blank" rel="nofollow noopener">huggingface.co/Qwen/Qwen3-235…
English
I installed Qwen3 with @ollama but I noticed it always thinks.
So, I made a Modelfile that lets you skip the thinking, if you want to. (for me I just need to generate a bunch of stuff with it, that doesn't require thinking)
By the way - any reasoning model can do this, if you add the empty block in the chat template like this it will skip thinking.

English
outoflegend retweetledi
Must-watch 38C3 @ccc talk on low entropy vulnerabilities
Props to Milk Sad team (@JohnNaulty, Christian Reitter & team) for their groundbreaking research 🔍
Proud our Trust Wallet research w/ @outoflegend @SECBIT_IO got featured
🎥: media.ccc.de/v/38c3-dude-wh…
English

Hi @zkbankai, we've just submitted our proposal for the Soulforge grants: github.com/zk-bankai/soul…
English

I also didn't expect that the tau of Ethereal Quest's SRS was Googled, constructing a fake proof.
p0n1 🦇🔊@ErrNil
Congrats on the success of this event. The participants were truly impressive, each bringing a unique and remarkable perspective to the same challenge. Learned much from their excellent write-ups. I contributed this puzzle: github.com/p0n1/familiar_…. One participant's approach even led me to discover an unexpected bug in my code.
English
outoflegend retweetledi
🚨 *Vulnerability Alert:* Trust Wallet's Fomo3D Summer 🚨
🔗 Full Disclosure: secbit.io/blog/en/2024/0… 💸 Losses on ETH mainnet alone are staggering – and that's just the tip of the iceberg.
🧵 A thread on the findings and implications for users: 👇 (1/n)
English



