Natoshi
1.9K posts


Natoshi
@oxNatoshi
Crypto trader | Building AI things | Baguette 🇫🇷


We’re saying goodbye to Sora. To everyone who created with Sora, shared it, and built community around it: thank you. What you made with Sora mattered, and we know this news is disappointing. We’ll share more soon, including timelines for the app and API and details on preserving your work. – The Sora Team




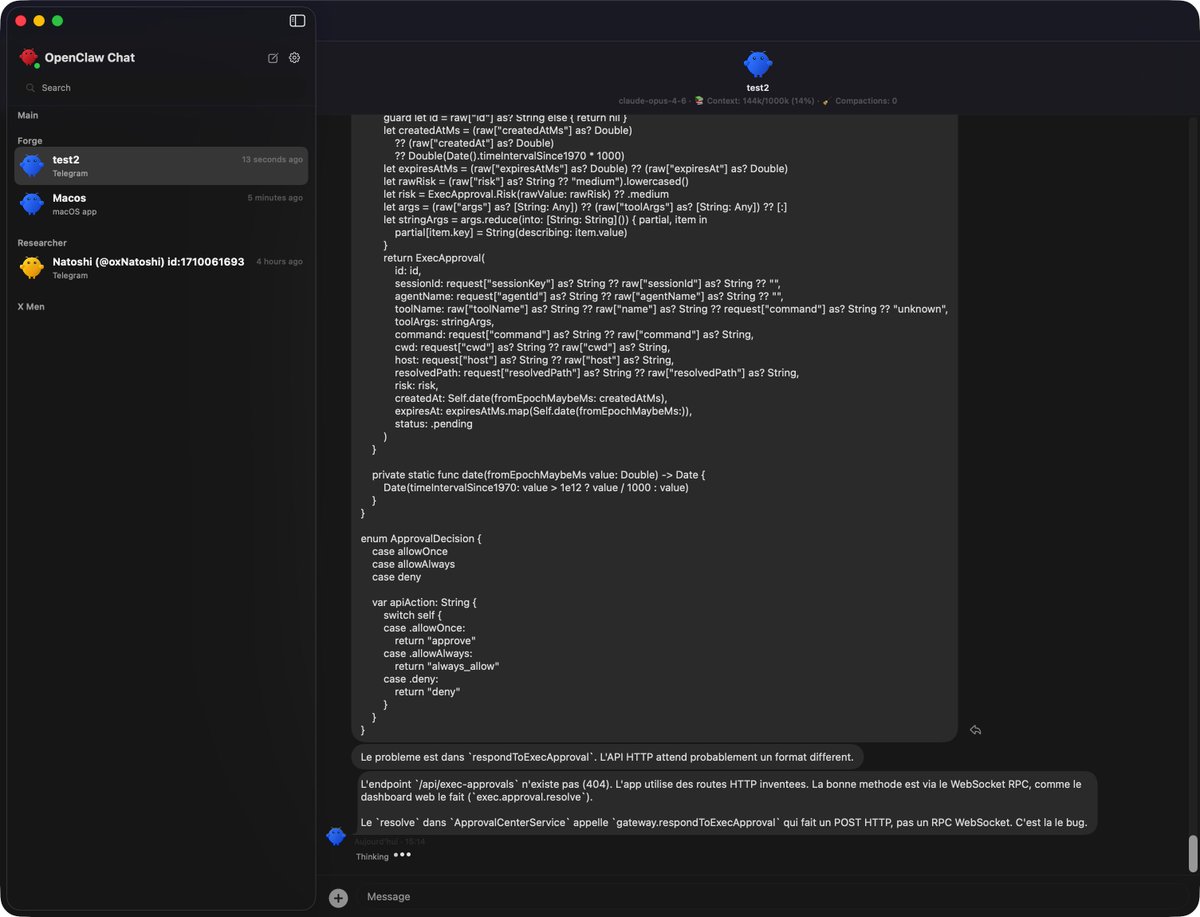
dead simple way to maintain openclaw. bugs, oauth expiring, worried it breaks while you're away. install codex app. set an automation. it checks and fixes your gateway on a schedule. new problem? fix once, add to prompt, never again. my prompt does these things: 1. SSH into the VPS, run four health checks 2. if something's wrong, apply the smallest safe non-destructive fix. no touching auth, no touching secrets 3. if it can't fix it or it's serious, write an incident report and send me a notification on telegram 4. on sundays, run a drift check for backups, root-owned residue, and journal error patterns the powerful thing about codex is that its login session can be shared directly with openclaw. oauth expiring? codex just renews it. solving this with other agents would be a much bigger problem. what you end up with is a maintenance expert that gets smarter over time. every new problem you solve gets added to the prompt, so it knows how to handle it next time. token cost is low too, each run takes about a minute. full prompt (sanitized, replace with your own server address): Maintain the OpenClaw gateway with a single conservative automation. Read local docs before making any claims about commands or fixes. SSH to your-server on port 22. Treat systemctl and journalctl as supervisor truth. Run openclaw status --deep, openclaw channels status --probe, openclaw cron status, and openclaw models status --check. Apply only the smallest safe non-destructive repair such as restarting openclaw-gateway.service, running openclaw doctor, repairing symlinks, or fixing accidental root-owned residue. If a significant issue is found, first write an incident markdown file with severity, impact, evidence, repair attempted, current status, and next action. Then deliver a short alert summary through your preferred notification channel. On Sunday morning, also run weekly drift checks for backups, root-owned residue, and recent journal error patterns. Leave one inbox summary that separates healthy state, repaired issues, incidents, alerts sent, and blockers requiring human judgment. Never expose secrets, never weaken auth or access policy.

never met a single person irl who uses openclaw







OpenClaw 2026.3.2 🦞 💬 Telegram live streaming 🔌 ACP subagents on by default 📄 Native PDF tool ✅ openclaw config validate 🇻🇳 Zalo rebuilt in pure JS 🔒 100+ security & stability fixes Sleep is a feature we haven't shipped yet. github.com/openclaw/openc…