Sabitlenmiş Tweet
padi
491 posts



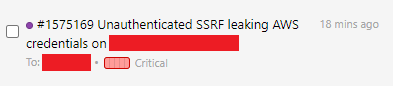
@m411k_ @zh1x1an1221 AI performs well in terms of coverage, but for complex logical vulnerabilities such as JIT bugs, it struggles to construct a PoC.
Researchers need to shift their mindset to discover vulnerabilities that AI cannot find.
Hope this helps.
English

Information warfare is deeply interesting to me, it’s becoming increasingly obvious that there is competition over control of the values, narratives, and the movement of the cultural zeitgeist. I believe the shift that we’ve seen to decentralised systems (namely social media and how information is disseminated) has made this not only more pervasive, but far more visible. It’s fascinating to see people I know building broad foundations of geopolitics based on what must be at least partially the product of soft power operations. I think it’s only been a lot more recently that the western axis is realising there’s a game being played here for a while that they weren’t fully appreciating not only in the pervasiveness, scope, reach, and influence of these operations but also the difficulty of responding to them in free and open societies.
English
padi retweetledi

@Cryptycore @Hacker0x01 Stay passionate and curious. That’s the main takeaway. Certifications will not find bugs for you.
English
padi retweetledi

I finally did it!! CVE in Chrome!!! (Davi Antônio)
chromereleases.googleblog.com/2026/03/stable…
Română
Yay, I was awarded a total of $16,000 bounty (for 3 different bugs) on @Hacker0x01! hackerone.com/a92847865 #TogetherWeHitHarder #Mar26
English
padi retweetledi

geohot.github.io//blog/jekyll/u…
This is a really good read. I like how this guy brings a lot of what he speaks on back to this idea of “creating more value than you consume”.
English
padi retweetledi
padi retweetledi

@rez0__ @stokfredrik Its a new bar for low hanging fruits. So it will be a field day until its cleaned up. Then my guess is that a few high level AI users will own that space, just like a handful hackers control the regular automation space today. The rest of us will keep picking here and there
English
padi retweetledi

Olá pessoal! De volta ao YouTube aos poucos. Neste vídeo vamos entender como criar excelentes reports de bug bounty, o básico sobre Markdown e analisar alguns exemplos teóricos.
youtube.com/watch?v=uUEasS…

YouTube
Português
padi retweetledi

Caso você tenha dúvidas sobre como escrever um report de qualidade para programas de bug bounty, o @paulogmota_ acabou de lançar o que você precisa! Segue o link do youtube: youtu.be/uUEasSyIurs #bolhasec

YouTube
Português
padi retweetledi

I finally let Claude do my pentest this week. Full 5-day engagement, zero human input. Here's what the client got: 😏
clawd.it/posts/10-repla…
#bugbounty #pentesting #AI #cybersecurity #infosec #claudeai
English
padi retweetledi

I used to struggle to read more than 50 pages of a book before giving up and never touching it again, so I started setting micro goals. Reading just five pages a day felt like progress. If I finished five, I was satisfied and could put the book down.
By the end of the year, I had read 4,200 pages. I realised that all I needed was to take the pressure off and just begin. It’s like going to the gym. Sometimes just putting on your workout clothes makes it harder to quit, even if you haven’t left the house yet.
A few months ago, I used the same approach for bug bounty hunting. I was feeling burned out / jaded, so I set a micro goal to hunt for just one hour each day with real focus. This small goal built momentum, and I often ended up hunting longer. Even when I stopped after an hour, I felt good about it. I found many bugs, succeeded in an LHE, got into more LHEs, and earned some great bounties.
Give it a try. Set micro goals and don’t put too much pressure on yourself. Just focus on completing that small goal with real effort, or at least on learning something new. If it doesn’t work out one day, you can always try again the next.
English