Pawel Foremski
1.2K posts


Pawel Foremski
@pforemski
Internet infrastructure security and performance: #IPv6, #BGP, #DNS, #DDoS. @ https://t.co/Jz50nu108t + @DomainTools + @bgpfixorg












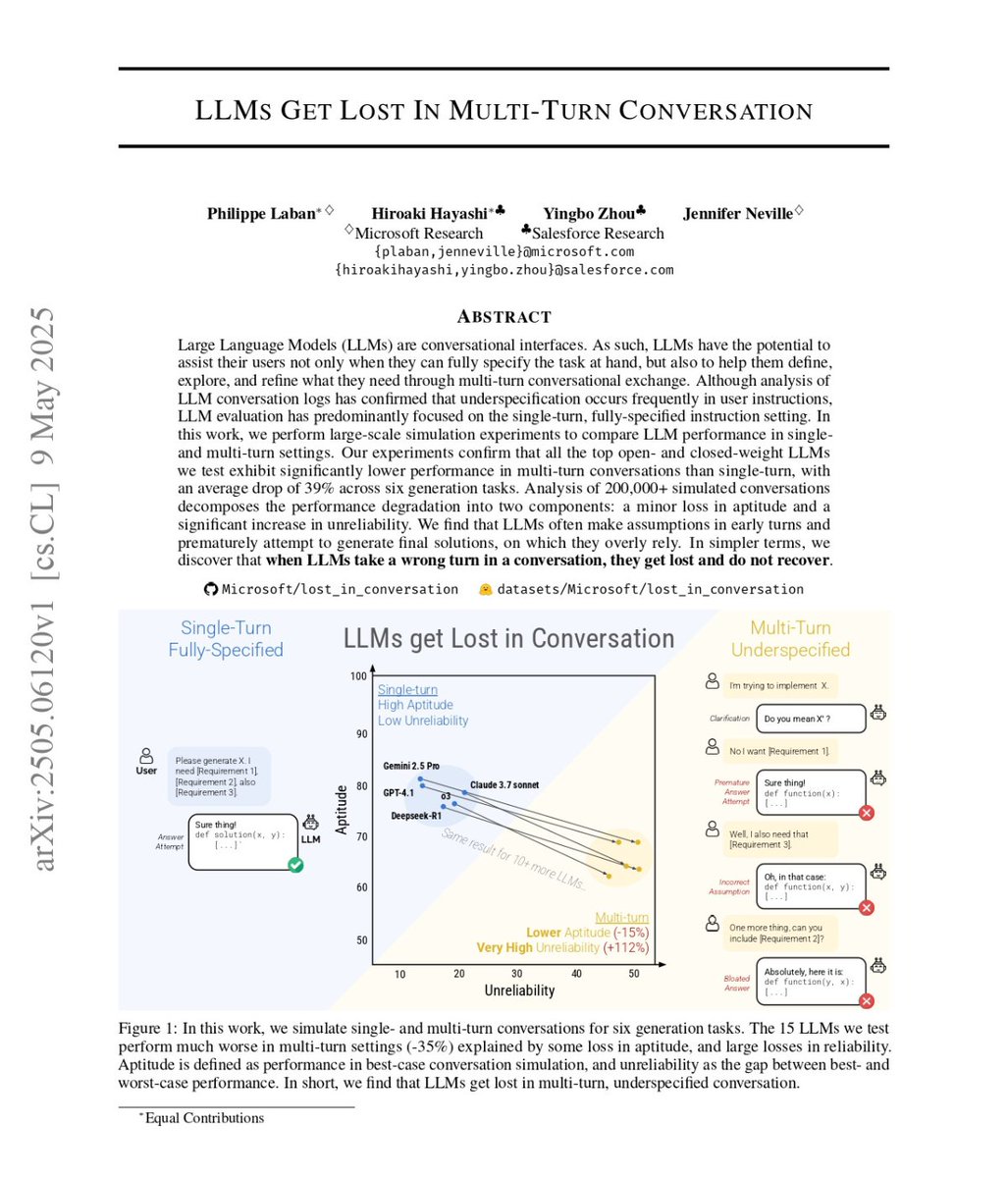
Terence Tao put it plainly: there is no evidence that LLMs exhibit genuine creativity. Yes, they have solved some Erdős problems. But these are low-hanging fruit, questions that attracted little attention and that yield once the right existing techniques are applied. That is not creativity. That is search plus recombination. Yes, LLM outputs can look impressive. But look at who is impressed: typically non-experts. Experts know very well that LLM performance gets terrible when you approach the frontier of human knowledge. And this is not a temporary gap. It reflects a structural limitation. We do not fully understand human creativity. But we do know a key property: Conceptual leaps: the ability to generate new representations, not just recombine existing ones. LLMs do not do this. They interpolate in representation space. They operate within existing conceptual frameworks; they do not create new ones. This is why we haven’t “yet seen them take the next step”.

JUST IN: Meta announces they'll be shutting down the Metaverse, after pouring $80,000,000,000.00 into the project.