𝘼𝙧𝙢𝙞𝙨𝙖𝙚𝙡𓁹
1K posts


𝘼𝙧𝙢𝙞𝙨𝙖𝙚𝙡𓁹
@phenomenware
Est Ing.Soft | Embrace FOSS, Go Alt.


Pues ahí lo dejo.

le tienen mucho respeto a la palabra ingeniero sólo xq les cuesta matemática





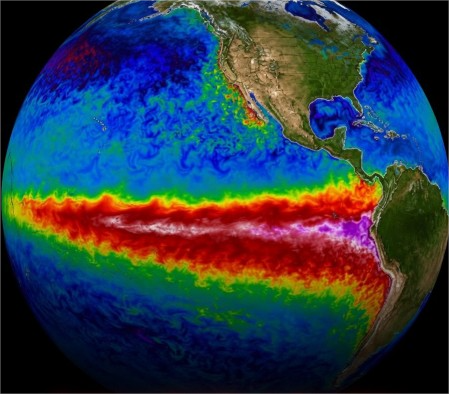
🚨: A super El Niño is forming in the Pacific - the biggest since the recorded history Get ready for extreme winters since 1877!


‼️#URGENTE "Debo ser honesta: todavía me sorprende que hay personas que no les gusta ver a una mujer avanzar, salir adelante o cumplir sus metas. Y que en vez de alegrarse por este tipo de logros, buscan minimizarlos, atacarlos o hacerlos ver como que no son suficientes”, señaló Lavinia Valbonesi, esposa del presidente Noboa, en medio de cuestionamientos por la obtención de su título universitario en menos de un año.

‼️#URGENTE "Debo ser honesta: todavía me sorprende que hay personas que no les gusta ver a una mujer avanzar, salir adelante o cumplir sus metas. Y que en vez de alegrarse por este tipo de logros, buscan minimizarlos, atacarlos o hacerlos ver como que no son suficientes”, señaló Lavinia Valbonesi, esposa del presidente Noboa, en medio de cuestionamientos por la obtención de su título universitario en menos de un año.


🚨 NEW: Zohran Mamdani to invest $122M in NYC public schools, hiring 1,000 additional teachers.



🚨 🇪🇨 CYBERINTELLIGENCE ALERT: ALLEGED DATABASE LEAK - PEDIDOS365.COM "UNCONFIRMED" ⚠️ EXPOSURE OF 137,000 CRITICAL USER RECORDS A massive leak has been detected involving the database belonging to the website pedidos365.com, an order services platform in Ecuador. The threat actor claims to have exfiltrated critical information that compromises the privacy of thousands of users. The threat actor has provided samples via downloadable links; as of now, these have not yet been inspected for evaluation. 🎯 Affected Institution: Pedidos365 (Ecuador). 👤 Threat Actor: tbabi. 📂 Data Volume: 137,000 database records. 📅 Detection Date: May 13, 2026. 📂 Case Identifier: #6108. 📊 LEAK ANALYSIS 🧩 Geographic Scope: The breach primarily affects citizens and businesses within Ecuador. 🔗 Connection to Other Attacks: The same threat actor, tbabi, has been simultaneously linked to other high-profile leaks, such as Lucid Solutions (United Kingdom) and teamgram.net (Dark Web). 🛡️ MITIGATION AND RECOMMENDATIONS 🛑 Password Changes: Pedidos365 users are advised to change their login credentials immediately. ⚠️ Social Engineering Vigilance: Due to the potential exposure of phone numbers and email addresses, affected individuals should remain alert for phishing attempts or SMS-based scams (smishing). ⚡ MONITORING 🌐 Monitoring System: analyzer.vecert.io #CyberSecurity #DataLeak #Ecuador #Pedidos365 #DataBreach #PII #VECERT #CyberAlert #Tbabi #CyberIntelligence





🚨 🇪🇨 CYBER THREAT ALERT: POTENTIAL SERVER COMPROMISE – SOMOS BDA (BANCO DEL AUSTRO) ⚠️ DETECTION OF SUSPICIOUS FILE UPLOADS AND POTENTIAL BACKDOOR [STATUS: EMERGING THREAT / UNCONFIRMED] Activity has been detected from the group BROTHEROOD CAPUNG (BCI) targeting the domain somosbda.ec, a platform associated with employees and collaborators of Banco del Austro in Ecuador. Evidence suggests that the attackers have successfully breached the server's upload directory. 🎯 Affected Institution: Somos BDA / Banco del Austro. 👤 Threat Actors: BROTHEROOD CAPUNG (BCI). 📅 Detection Date: May 14, 2026. 📊 ACTIVITY ANALYSIS (UNCONFIRMED) The incident presents indicators of a compromise involving the upload of unauthorized files: 🧩 Shell/Backdoor Upload: A URL has been identified pointing to a file with an apparently executable extension located within the /uploads/ directory. Although definitive technical confirmation is pending, the phrase "Shel nya ampas" used by the actor suggests the successful deployment of a Web Shell or Backdoor to maintain persistence. 🔓 Credential Risk: The affected page is a login portal ("Log In - Somos BDA"). A backdoor in this location could be used to intercept credentials belonging to bank employees and collaborators (Internal Phishing or Formjacking). 🛡️ MITIGATION AND RECOMMENDATIONS 🛑 Directory Isolation: It is recommended to immediately restrict access to—and script execution within—the /uploads/ directory on the affected server. ⚠️ File Audit: Conduct a thorough inspection of recently uploaded files to identify and remove any Web Shells or malicious code. ⚡ MONITORING 🌐 Monitoring System: analyzer.vecert.io #CyberSecurity #BancoDelAustro #SomosBDA #Backdoor #WebShell #Ecuador #CyberAlert #VECERT #BCI #DataBreach