Pi3cH
591 posts


Pi3cH
@pi3ch
@SecTalks.org and @SecDim.com Founder. @UNSW.edu Senior Lecturer. https://t.co/kEjY1ONlMj


In December 2025, CVE-2025-68665, a high-severity vuln was reported on LangChain that could result in arbitrary code execution. We investigate how it was patched. Read about it here: secdim.com/blog/post/lang… #appsec #langchain #securecoding #programming

In June 2025, a vulnerability (CVE-2025-48432) was discovered in Django that allowed remote adversaries to tamper with logs, compromising log integrity. 👉 Read more: secdim.com/blog/post/thre… 👉 Our Blog: secdim.com/blog/ #appsec #securecoding #python #programming

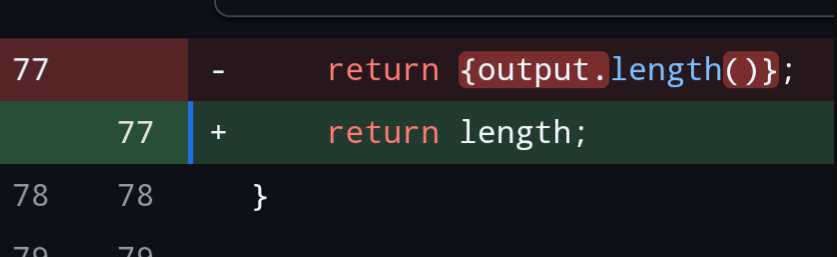
In December 2025, a critical vulnerability dubbed MongoBleed was disclosed. Mismatched length fields in Zlib-compressed protocol headers allow unauthenticated heap memory disclosure. 👉 Check it out via Holiday 7×7 Wargame: play.secdim.com/game/holiday-2… #appsec #mongodb #mongobleed



@secdim @BlackHatEvents Arsenal AI wargame 2025 winners


🔄 This is how you get hyper-relevant secure code learning labs based on identified vulnerabilities from GitHub Advanced Security using SecDim MCP - All without leaving your IDE! 👉 secdim.com/news/secure-co… #github #security #learning #ai

At SecDim we've always believed secure code learning should be seamless, frictionless and hyper relevant. Today, we're taking that mission one step further: Introducing the SecDim Model Context Protocol (MCP) server. 👉 Go check it out: secdim.com/news/secure-co… #appsec #ai #mcp

Model Context Protocols are increasingly important for LLM contexts. However, they introduce new vulnerabilities. We made challenges for them. Available for free for everyone to try for a Limited Time! 👉 Go try them out now: discuss.secdim.com/t/model-contex… #ai #appsec #securecoding