david retweetledi

Copy-Fail? More like Copy-Fixed. 🛑
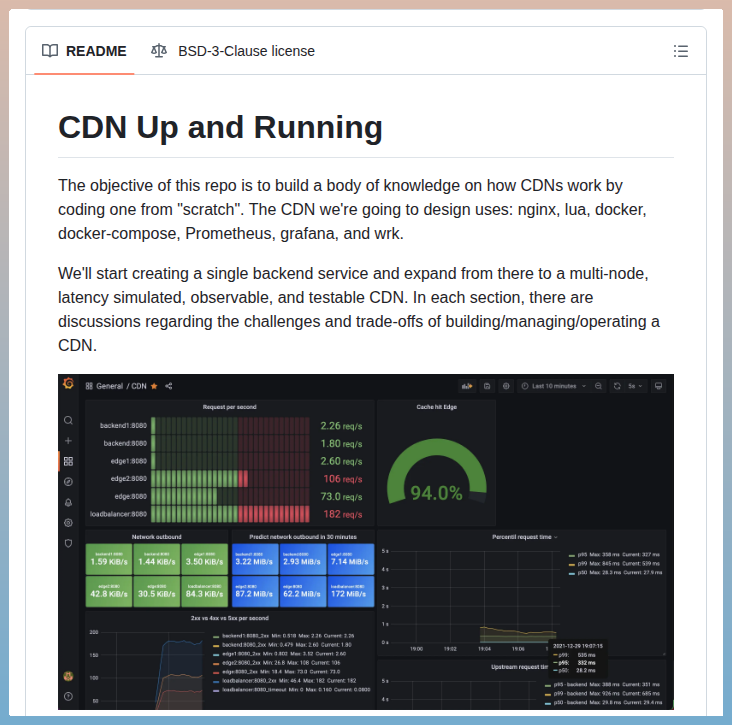
At @DECIX , our customers depend on our availability and integrity. So when the Linux "Copy-Fail" vulnerability popped up, we took it super seriously and patched things up immediately.
But our engineers don't just patch; they innovate. 🧠
During the mitigation process, one of our brilliant system engineers identified a completely alternative way to block the vulnerability using ftrace. Because it’s been supported in the kernel since 2013, it’s an incredibly accessible solution for the broader community.
We love a clever fix. Check out the GitHub repo below, try it yourself, and hit us with your feedback!
👉 github.com/philfry/cve-20…
English