Qazi Anwar
164 posts



Break out your OWN Docker container. Give yourself more LOVE. healinghackers.org #pwnreality #readthecode #naturalmatrix #selfcare #hacktheplanet #revshell #higherself
English

@yesimxev No problem I'll drop a debug version soon, give me some time
And also can you give me the last kismet debug logs with android kernel dmesg
I think we are very close because we saw wlan0 initiated in the last logs
English

@yesimxev No prob
I was working on NFC security
Can I contribute a new tab in the nethunter apk?
English

@yesimxev @Xiaomi @kalilinux @offsectraining @androidmalware2 Can't wait to port that on my 6t
Hope it works 😁
English

QCACLD-3.0 wireless injection is working on the @Xiaomi Mi A3 running @kalilinux NetHunter with kernel 4.14.x along with OnePlus Nord, POCO X3 Pro, Redmi Note 10, also Samsung A73 on kernel 5.4.x! Stay tuned for updates 📱📡 Credits below ⬇️ @offsectraining @androidmalware2
English

@yesimxev Hey I was watching the last logs you provided by the watch and in the logs I think we successfully managed to trick kismet configuring wlan0
We see
INFO: Data source 'wlan0' launched successfully
Can you pull out the dmesg
English

@yesimxev I'm sure the watch will be having a bcmdhd.ko located in the vendor somewhere
I think It is a prebuilt out-of-tree vendor module, compiled separately by Mobvoi against their private kernel tree and shipped in the vendor partition. The defconfig is irrelevant to it.
English

@pr0misc The watch doesn't use modules tho. So rmmod won't work. It's all builtin i guess? + bcm43436b0 fw, or some use bcm43438a1 fw. The first bootloops with the matching raspberry fw (very different version) the second works with rpi fw out of the box. Anyway, I'll try, thanks! 🤙
English

@yesimxev here is the zip
in android terminal:
su
rmmod bcmdhd
insmod /system/lib/modules/brcmutil.ko
insmod /system/lib/modules/brcmfmac.ko
and in nethunter terminal:
iw phy phy0 interface add mon0 type monitor (or what ever the iface is)
ifconfig mon0 up
drive.google.com/file/d/1Xh0ByH…
English

@yesimxev libnexmonkali wasn't playing nice with Kismet on the watch, so I tried a bypass: replaced stock brcmfmac with Nexmon's 4.9.y driver, manually edited cfg80211.c to fix API struct mismatches for the twp3 4.9.232 kernel headers, and successfully compiled the .ko loadable modules
English

@yesimxev yup i know but
I did tried and managed to cross-compile the open-source brcmfmac.ko driver against your 4.9.232 headers. The 43436b0 chip translates as a 43430 (same as the Pi 3), which means it should run the nexmon patched fw natively
English

@yesimxev hello again
its been a while
i was thinking if ticwatchpro holds an opensource brcmfmac driver
like inside the RPis are having, there is a completely different approach using the nexmon patched brcmfmac.ko module which is enough for everything
that wipes the LD_PRELOAD workaround
English

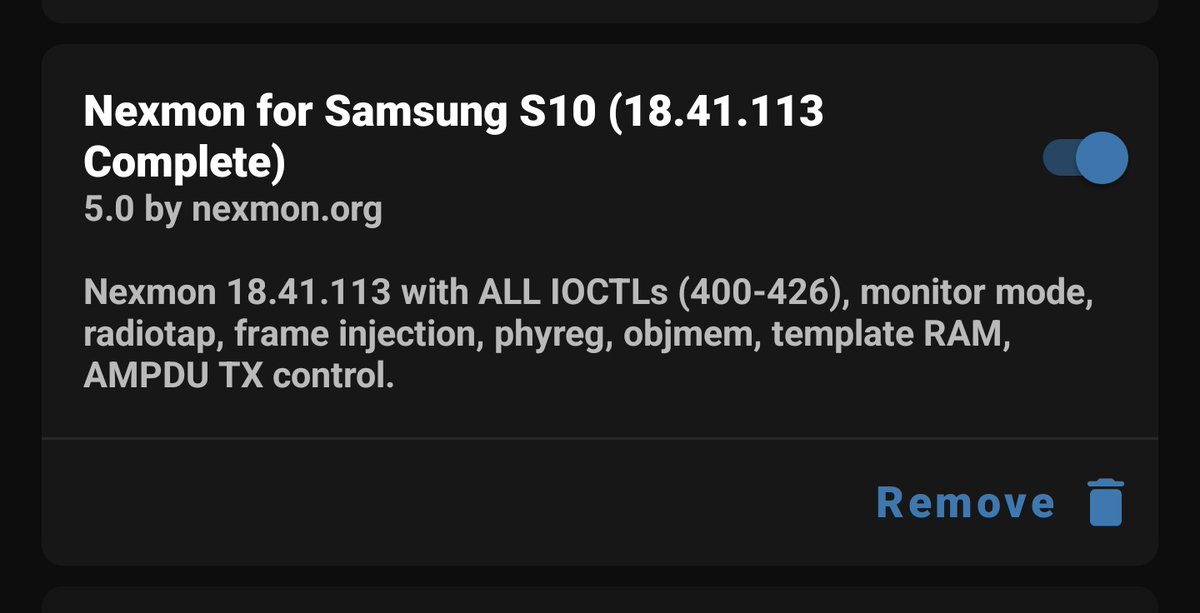
@yesimxev Yes it's experimental but the modifications are not done to libnexmonkali, but to the Nexmon patches instead for an new recompiled fw
I have an earlier version which I compiled with all necessary Ioctls and for maximum enhanced injection range
English

@pr0misc Better this time :) No fw crash, no reboot, tried channel 1 and all channel too pastebin.com/9u5ideTg
English

@yesimxev yes try using these inside android terminal
su
svc wifi disable
stop wpa_supplicant
stop wificond
and then nexutil -m2
and then in nethunter terminal
LD_PRELOAD=/path-to/lib.so kismet -c wlan0 --channel-hop=false --channel=1
lets try with just one channel first
English

@yesimxev Ok this looks interesting
Can you try using svc wifi disable
Like on s10
English

@pr0misc Great! I think even the original libnexmon needs some 5ghz patches, because airodump won't scan for those, unless specifically switched by nexutil -k. The above also caused reboot, I added dmesg log to the paste pastebin.com/CVZjgahd
English
Qazi Anwar retweetledi

The @kalilinux NetHunter hacker's smartwatch finally gets audio support! Now you can make calls with the TicWatch Pro 3, just like an agent 😎⌚📡 Install this kernel through recovery github.com/yesimxev/nethu… @Mobvoi_Official @offsectraining @androidmalware2 @kimocoder

English

@yesimxev check this and i have some good news too
we are very close to get full functionality over 5ghz networks inside nethunter chroot directly soon enough
drive.google.com/file/d/1hjrQc6…
English