Sabitlenmiş Tweet

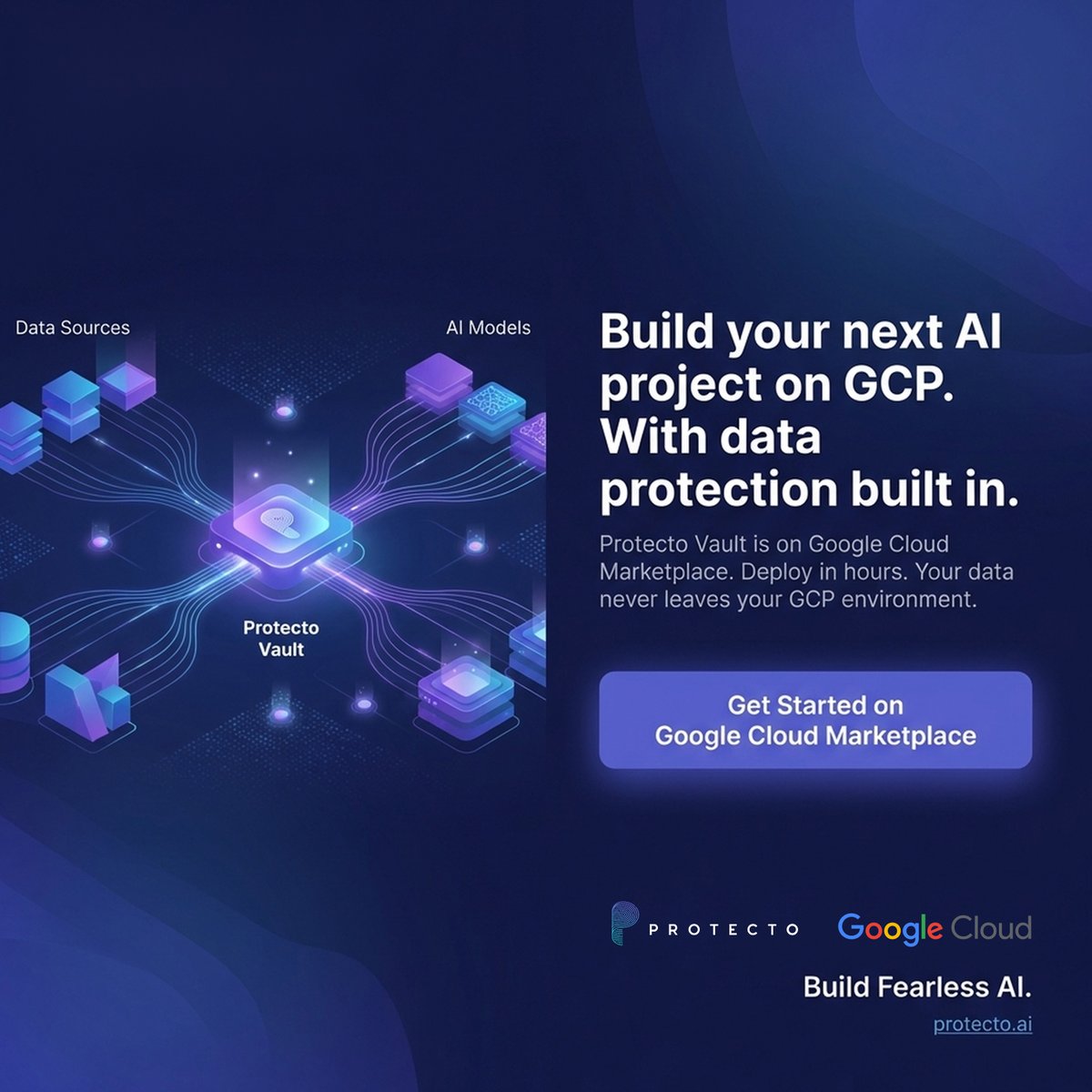
@ProtectoAi Vault is now on @gcloudpartners Marketplace. If you're running AI on GCP with sensitive data, this one's for you.
English
Protecto
817 posts


@ProtectoAi
Securing the future of autonomous AI. Privacy, trust, and control built into every decision. #AIPrivacy #DataSecurity #AgenticAI