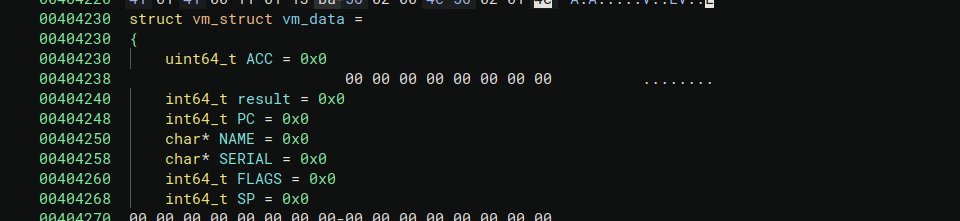
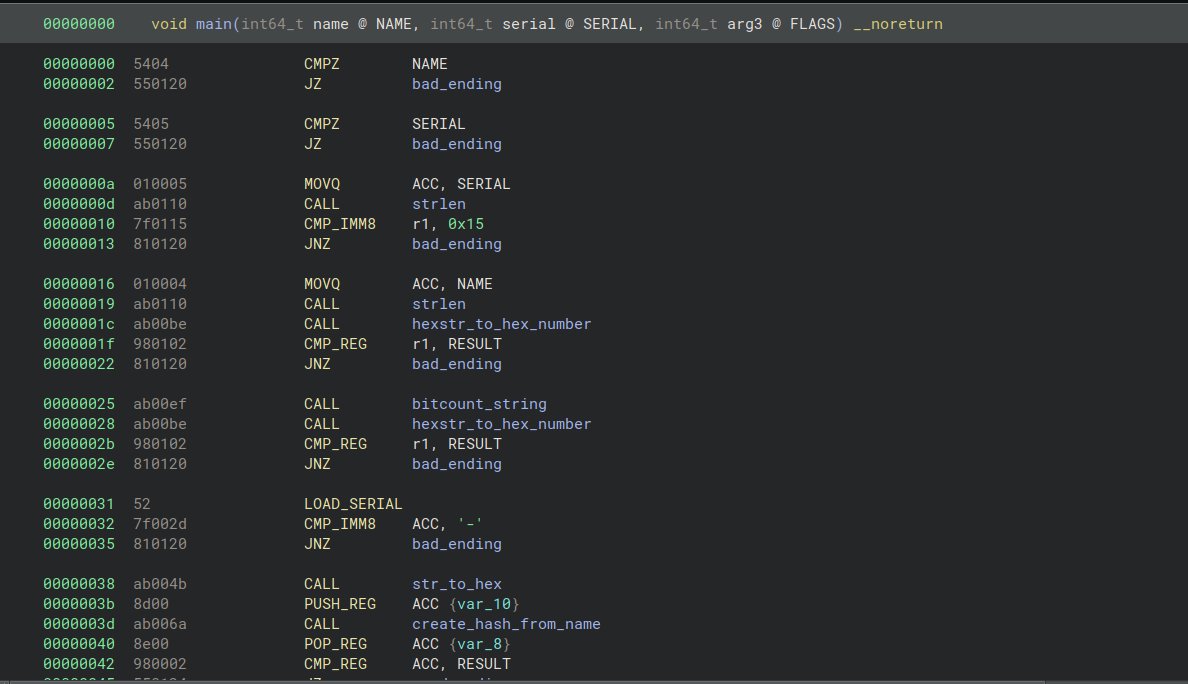
A hands-on look at Microsoft’s Independent Guest Virtual Machine (IGVM) format inside OpenHCL’s `openhcl.bin`.
We unpack the fixed header, variable headers, data layout, and how IGVM measurement supports Confidential Computing with SEV-SNP and TDX.
🔗blog.quarkslab.com/the-igvm-file-…
English