Sabitlenmiş Tweet
Rick de Jager
105 posts


Rick de Jager
@rdjgr
CyberSecurity student at @TUeindhoven - CTF with Superflat / @0rganizers / ICC team Europe 22/23/24/25
Katılım Kasım 2018
652 Takip Edilen1.3K Takipçiler
Rick de Jager retweetledi

Meet our #DCTF26 speaker Rick de Jager (@rdjgr )! He will present "𝐙𝐞𝐫𝐨 𝐭𝐨 𝐑𝐂𝐄 𝐢𝐧 𝐚 𝐖𝐞𝐞𝐤𝐞𝐧𝐝: 𝐅𝐮𝐳𝐳𝐢𝐧𝐠 𝐎𝐥𝐝 𝐆𝐚𝐦𝐞𝐬 𝐟𝐨𝐫 𝐌𝐞𝐦𝐨𝐫𝐲 𝐂𝐨𝐫𝐫𝐮𝐩𝐭𝐢𝐨𝐧."
Mid-2000s videogames are a great target for finding RCE exploits. In this talk we'll pick a classic 2000's game, go over the process of fuzzing the game's server with a very fancy snapshot fuzzer, and fuzzing the client with the dumbest possible bit-flipper I could write in an hour. Both of these approaches lead to bugs that we'll exploit for remote code execution.
Free registration: events.dragonsec.si/dctf26/

English
Rick de Jager retweetledi
@LiveOverflow @_mixy1 If FIFA allowed robot players, and 99% of accomplished soccer players said "we hate this, this ruins our sport", would we all go "this is just what the the word 'soccer' means now"?
The community gets some say in what the word "CTF" means. And nearly noone there enjoys AI v. AI.
English
Rick de Jager retweetledi

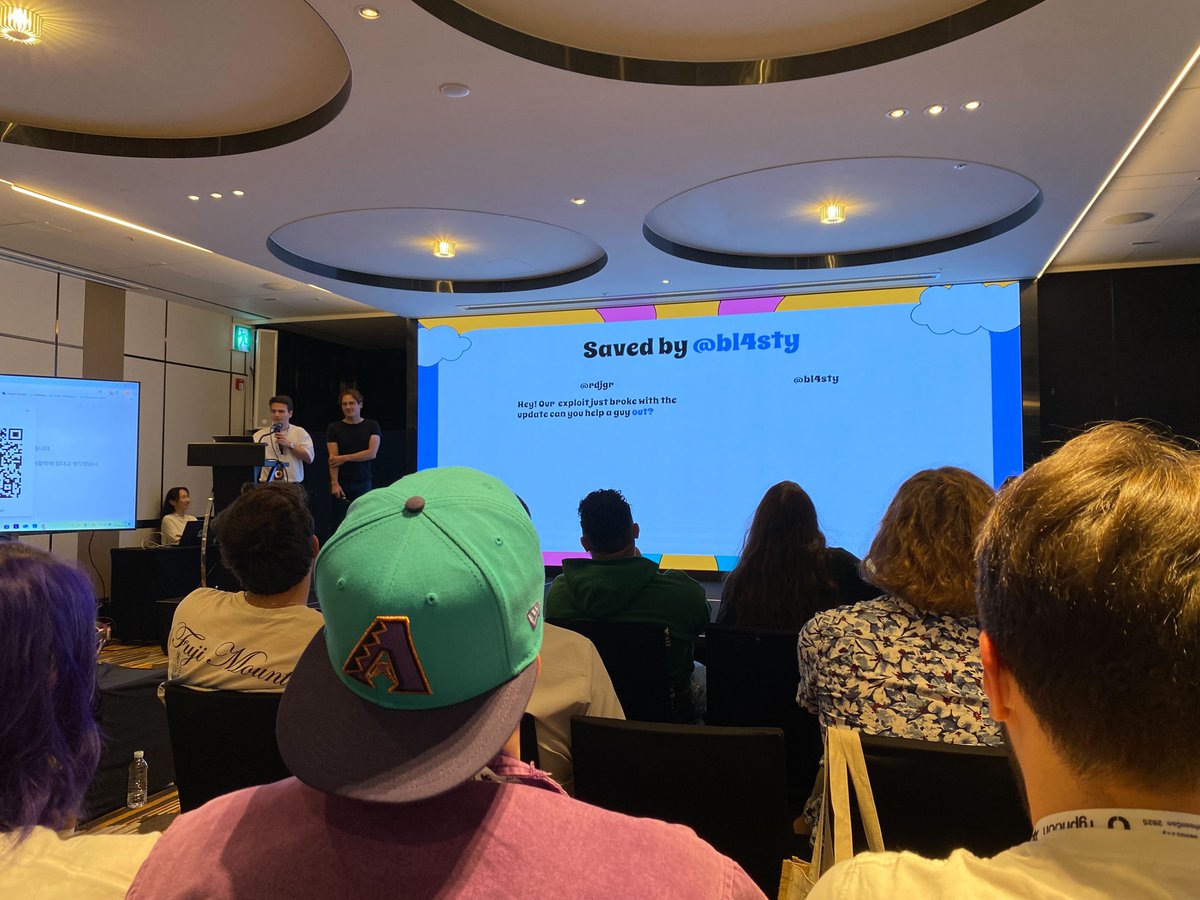
@rdjgr @DistrictCon Can confirm we have never seen RCT played like that before!
English

We (@arctic0x78 and I) ended up winning best meme target for this!
Many thanks to the Junkyard crew for running the competition. It's such a cool concept and I really enjoyed all the unhinged exploits people came up with!

English

May I present to you; a full copy of doom, running inside of a Rollercoaster Tycoon 1 save game exploit ✨
Thanks for everyone that came to check out our @DistrictCon Junkyard talk! We had a lot of fun putting it together. (check the thread for slides / exploit)
English
Rick de Jager retweetledi

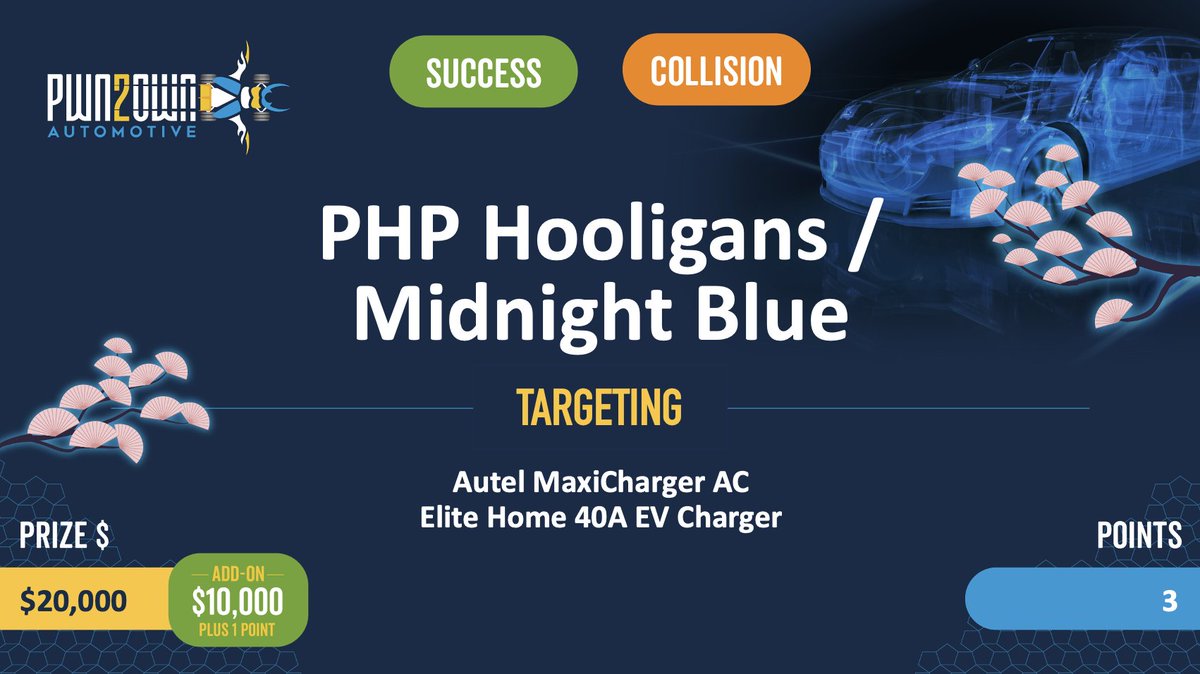
Collision! PHP Hooligans / @midnightbluelab targeted the Autel MaxiCharger AC Elite Home 40A with the Charging Connector Protocol/Signal Manipulation add-on, hitting a full collision on a two-bug chain, earning $20,000 USD and 3 Master of Pwn points. #Pwn2Own #P2OAuto
English
Rick de Jager retweetledi
We are announcing the results of ICC TOKYO 2025!
The overall rankings are: 1st place - TEAM EUROPE, 2nd place - TEAM ASIA, and 3rd place - US CYBER TEAM!
The winner of Jeopardy was TEAM EUROPE, and the winner of A&D was EUROPE! #icctokyo2025




English
Rick de Jager retweetledi

We have another collision. The PHP Hooligans did exploit the QNAP TS-453E, but the bug they used was previously seen in the contest. They still earn $10,000 and 2 Master of Pwn points. #Pwn2Own

English
Rick de Jager retweetledi

We have another collision. The PHP Hooligans used a buffer overflow to exploit the Phillips Hue Bridge, but the bug had been previously seen in the contest. They still earn $10,000 and 2 Master of Pwn points. #Pwn2Own

English
Rick de Jager retweetledi

Confirmed! The PHP Hooligans used an OOB Write bug to exploit the Canon imageCLASS MF654Cdw printer. Their fifth round win earns them $10,000 and 2 Master of Pwn points. #Pwn2Own

English

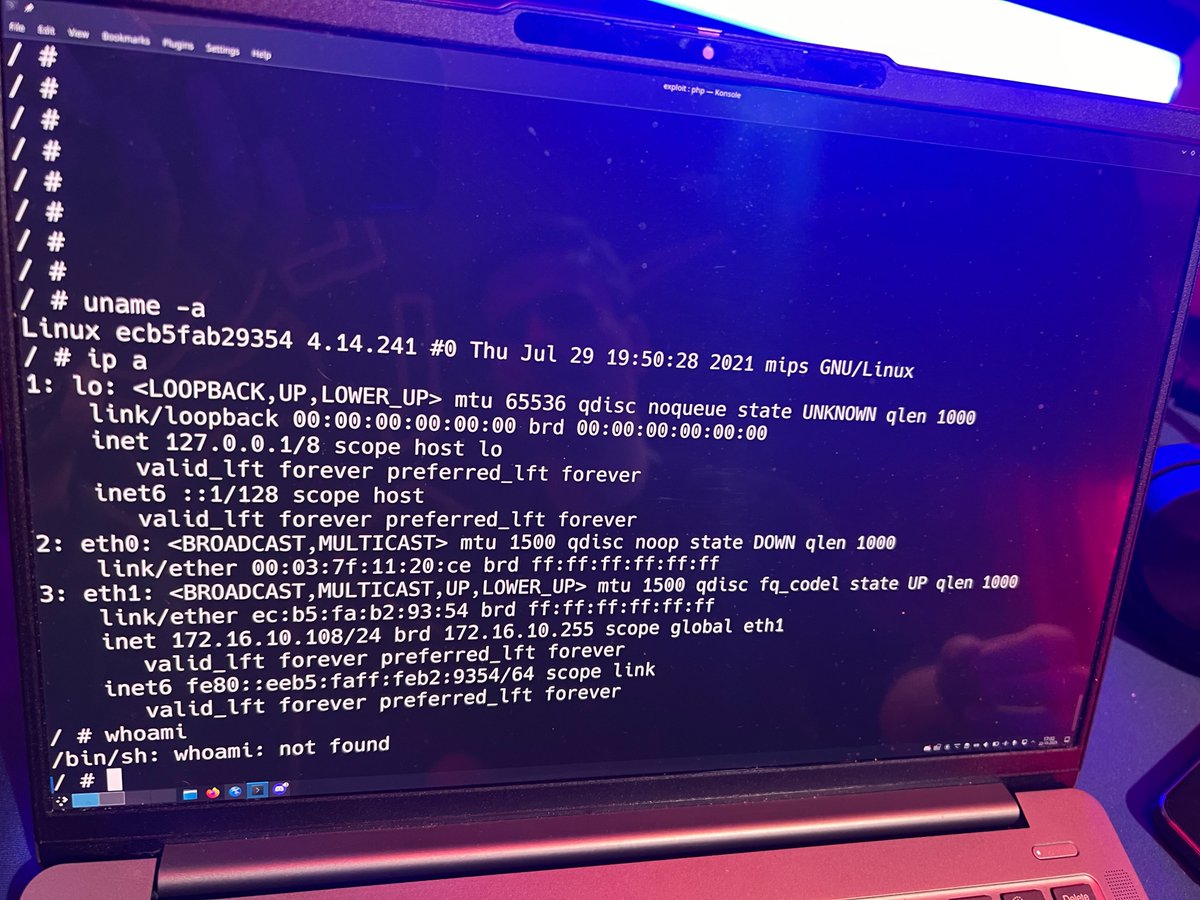
Writing an exploit? 3 days.
Getting a hold of a security contact? 50 days and counting.
Dropping a PoC in a random support ticket to meet the Junkyard deadline? Priceless. ✨
Ryan Speers@rmspeers
We still have some spots open for DistrictCon junkyard speakers! Not only do you have a chance to show off your awesome work on an end of life target that needs attention – or laughs – but also we are giving out cash prizes to winners!!!
English
Rick de Jager retweetledi

[ZDI-25-711|CVE-2025-8320] (Pwn2Own) Tesla Wall Connector Content-Length Header Improper Input Validation Remote Code Execution Vulnerability (CVSS 8.8; Credit: PHP Hooligans) zerodayinitiative.com/advisories/ZDI…
English
Rick de Jager retweetledi

Rick de Jager retweetledi
Rick de Jager retweetledi
Rick de Jager retweetledi

We’re delighted to welcome @rdjgr & Carlo Meijer to #TyphoonCon2025! 🎤🔥
Be sure to join us in Seoul on May 29-30 for their amazing talk!
🔗 typhooncon.com/agenda
English

@h0mbre_ yeah I hope they either expand the attack surface to include userspace privesc or significantly increase payouts. $10-20K for a non-userns kernel bug feels pretty low compared to IoT and automotive bounties.
English