Sabitlenmiş Tweet

👋 Hello & Welcome! I'm an aspiring Network Security Engineer documenting my entire journey from beginner to professional. No gatekeeping, just learning in public.
My mission is to achieve mastery in network and security fundamentals, integrate automation principles into daily tasks, and contribute to the future of network design in the age of Cloud ☁️ and AI 🤖.
On this feed, you can expect:
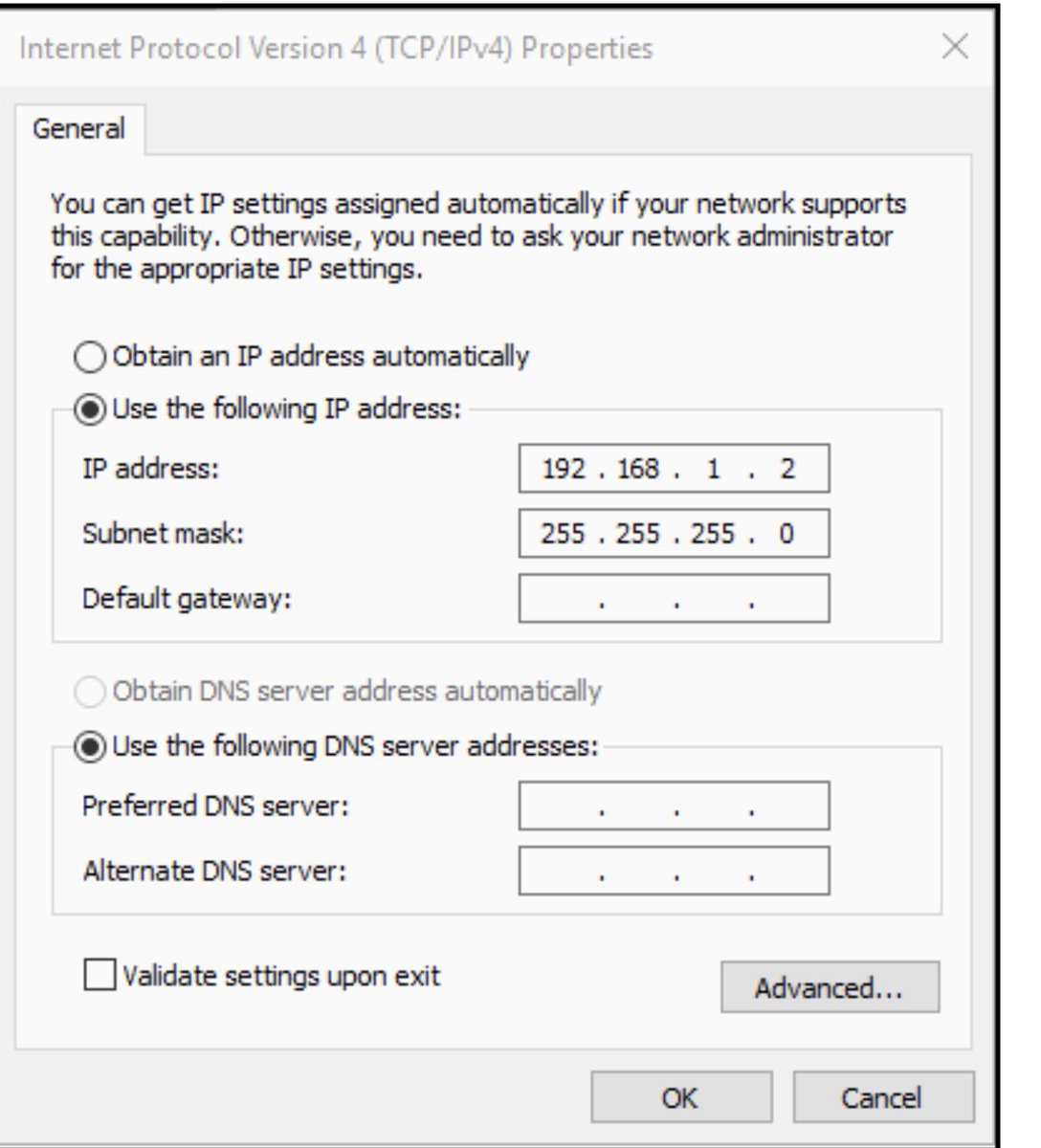
🔹 Clear explanations of core concepts (OSI, Subnetting, Routing etc...).
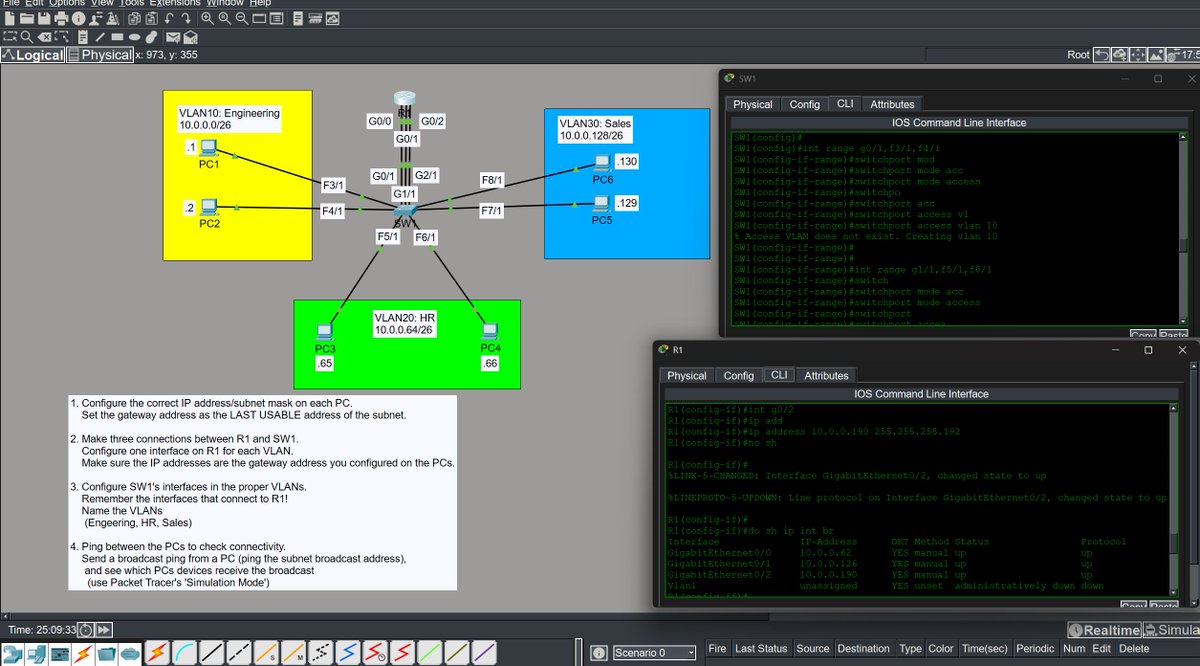
🔹 Home Lab builds & configuration troubleshooting.
🔹 Insights into the future of network management and design.
🔹 Honest struggles and lessons learned along the way.
If you are a beginner, let's learn together.
If you are an expert, your advice is gold.
Hit the Follow button 😃 and let me know your favorite networking command below! 👇
English