Root Evidence
25 posts



Most organizations don't know which vulnerabilities will actually cost them money. They're managing thousands, patching by severity scores, and still getting breached.
At RSA, our co-founder @RSnake sat down with Yahoo Finance's Tech Edge to talk about what tech-enabled underwriting actually looks like and why clean, financial-risk-driven data changes things entirely.
If you're in security, risk, or underwriting, this one's worth 10 minutes.
🔗 tech.yahoo.com/cybersecurity/…
English

AI is going to find more vulnerabilities. That much is clear.
What’s less clear, and often overstated, is whether that actually leads to more exploitation.
Attackers have never been constrained by a lack of vulnerabilities. They are constrained by what is worth their time.
That hasn’t changed.
Jeremiah wrote about why that matters here: rootevidence.com/blog-posts/the…

English

Full coverage shouldn’t mean full noise.
We’re building a faster, more cost-effective way to monitor exposure and focus on what actually matters.
Evidence Scan helps you see the vulnerabilities that lead to real-world loss, not just the ones that fill dashboards. Apply to preview Evidence Scan here: preview.rootevidence.com
English

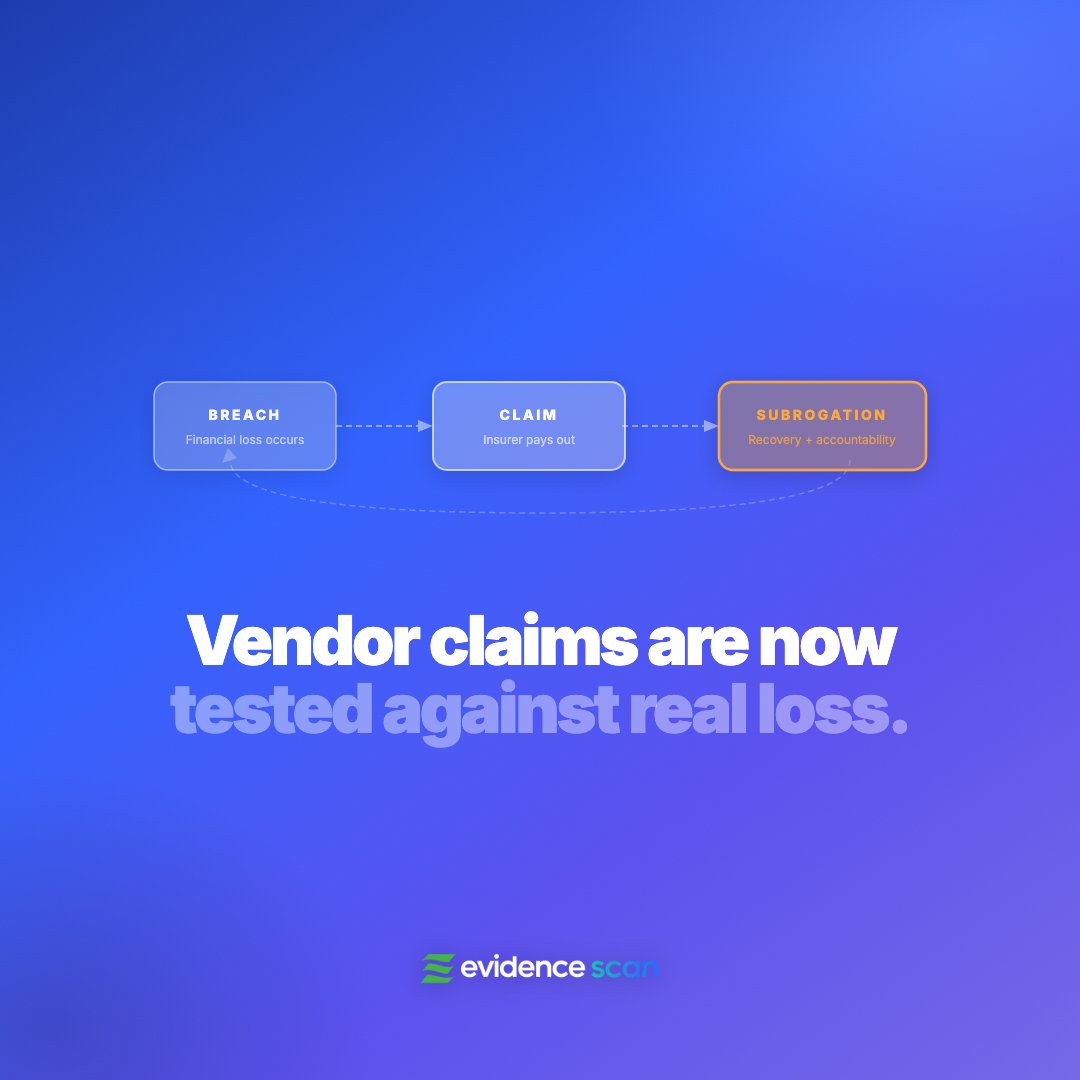
The security industry has never had a real accountability mechanism.
Vendors self-evaluated. Analysts rated. And when breaches happened, there were rarely financial consequences for getting it wrong.
That’s changing. When insurers pay out a claim and pursue recovery, the question is no longer whether a control sounded credible. It’s whether it actually reduced the likelihood or impact of loss. Now those claims can be tested against real outcomes, and vendors are starting to be held to it.
Robert Hansen breaks down what this means for security, insurance, and the future of the market.
Read the full blog: rootevidence.com/blog-posts/sub…
English

A few moments from RSA last week with the Evidence team. Always time well spent connecting with others in the industry! @RSnake @greg_reber


English

When 49% of CVEs are rated "High" or "Critical" but under 1% have been tied to real-world financial loss, the gap isn't in the tools. It's in the class of evidence teams have access to. Proxies can't replace observed outcomes.
The question most VM programs still can't answer clearly is "Are we clear of every vulnerability that has historically led to financial loss?"
🔥 Evidence Scan is built to answer that question, grounded in breach data, claims activity, and documented adversary behavior. The goal isn't a shorter backlog, but a defensible position: clear of every vulnerability that has historically caused a breach, and able to prove it to the board.
Learn more here: preview.rootevidence.com

English

Most companies are buried in vulnerabilities, but they still get insured by cyber insurance carriers.
That should make you pause.
Insurers aren’t counting CVEs. They’re pricing risk based on what actually leads to financial loss. And the data is clear: only a tiny fraction of vulnerabilities ever make it that far. So why are VM teams we still prioritizing as if they all matter?
Jeremiah Grossman breaks this down in his latest blog.
Read it here: rootevidence.com/blog-posts/com…

English

In case you missed it, Evidence Scan just dropped. Here's what it actually changes in VM.
Vulnerability management has always had an evidence problem, not a discipline problem. The signals we've relied on (CVSS, KEV, exploit predictions) are reasonable proxies, but what they don't tell you is which vulnerabilities have historically appeared in breach investigations and insurance claims. That's the gap Evidence Scan closes.
Instead of a backlog of thousands, it surfaces FIREs (Financial Risk Exposures), which are vulnerabilities that are publicly exploitable and historically tied to real financial loss. The signal is binary. You have it or you don't. No scores, no confidence intervals, no maybes.
Most vulnerabilities in your environment have never caused a breach. Evidence Scan focuses on the small fraction that repeatedly have.
The Enterprise Preview for Evidence Scan is now open to a limited number of organizations. If you manage a VM program and want to see what the historical claims data shows in your environment, apply here: preview.rootevidence.com

English

Security teams are drowning in vulnerabilities, but only a small fraction ever lead to real financial loss.
🔥 We call those FIREs: Financial Risk Exposures.
Evidence Scan turns vulnerability management on its head. Instead of handing you a to-do list of thousands of bugs, it surfaces the FIREs you actually need to put out:
✅ Publicly Exploitable: If an attacker can’t reach it from the internet, it’s not a FIRE.
✅ Proven With Claim Data: If insurers haven’t seen it cause a loss, it’s not a FIRE.
✅ Binary Signals: You either have this vulnerability or you don't. No scores, no confidence intervals, no maybes.
We’re opening the Enterprise Preview of Evidence Scan to a small number of organizations. If you want to focus on the vulnerabilities that actually cause loss, apply to try Evidence Scan today.
Apply here: preview.rootevidence.com
English

Thanks for all the love on our announcement yesterday! In case you missed it, we just opened the Enterprise Preview for Evidence Scan.
We’ve been working behind the scenes with cyber insurers to answer a simple question: which vulnerabilities actually lead to real financial loss? We're not talking about the thousands that show up in other scanners, but the tiny fraction that repeatedly lead to breaches. Evidence Scan surfaces those exposures so teams can focus on fixing what actually matters.
If you want to learn more about the Enterprise Preview and the idea behind loss-first vulnerability management, you can read the full announcement here.
rootevidence.com/blog-posts/ann…

English

Thousands of "critical" vulnerabilities, but only a fraction lead to real breaches. Evidence Scan surfaces FIREs, the exposures tied to real-world financial loss. 🔥 Enterprise Preview now open. businesswire.com/news/home/2026…
English

Something new is coming.
We’ve been quietly working on a different way to think about vulnerability management. One grounded in evidence instead of noise.
We will share more soon.
If you want to be first to hear the news, sign up for our newsletter here: rootevidence.com
English

But there’s reason to be optimistic. Together, we can build a new approach that actually helps security teams focus on what matters most.
Read our thoughts here: rootevidence.com/blog-posts/the…
English

Vulnerability management is broken.
Security teams are buried in data, starved for context, under-resourced, and told to prioritize the un-prioritizable.
@jeremiahg and @RSnake listened to 100+ security practitioners and pulled out the biggest challenges they face every day.
English

Hot take: Not all exploitation leads to risk.
If an adversary can’t monetize it, it doesn’t matter if they’re testing for it.
In @RSnake's latest blog, he digs into why exploitation ≠ loss.

English
