roots.io
774 posts


@rootswp
Advanced tools for professional WordPress developers 🔧 https://t.co/aWZDsySk6l Tweets by @retlehs


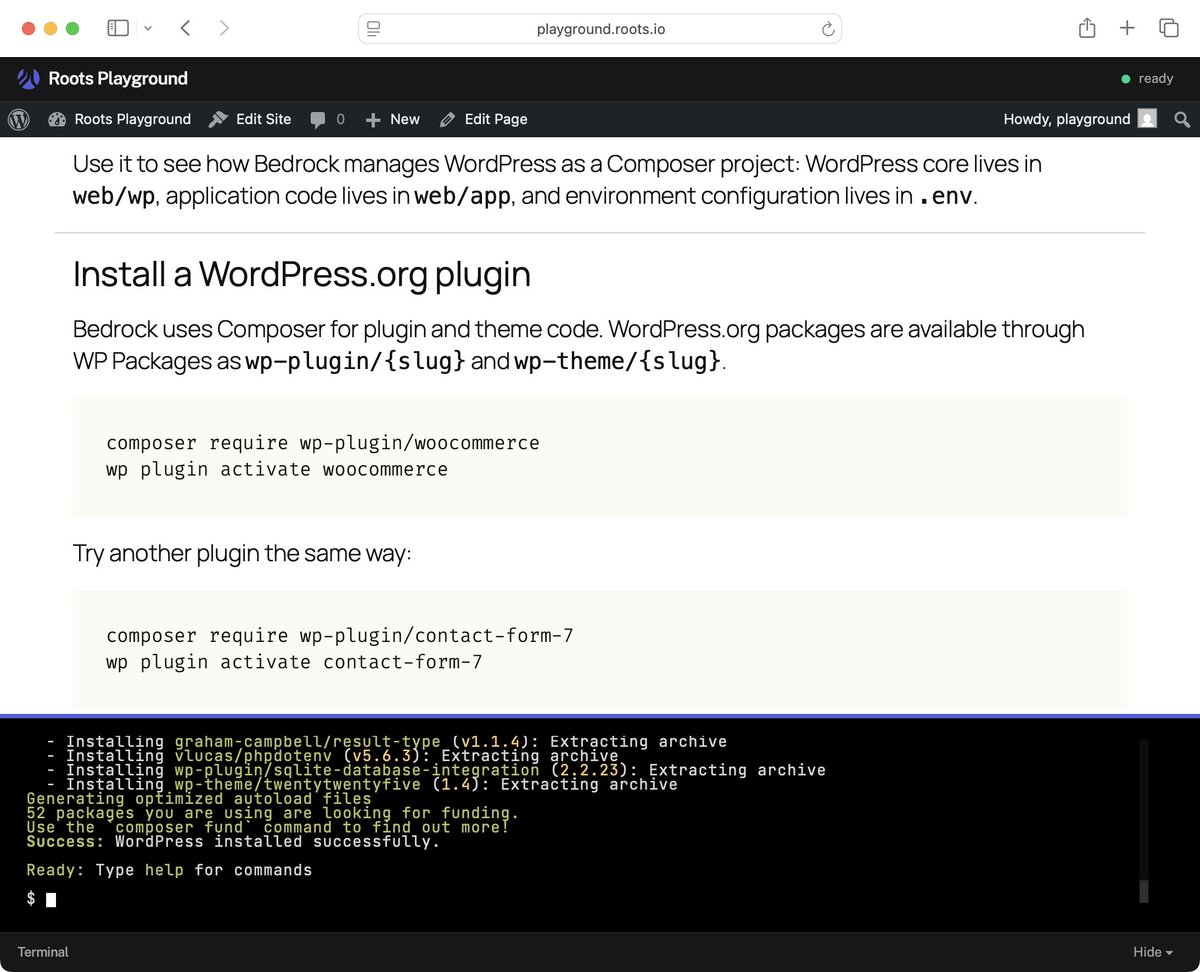
For folks using the 𝚛𝚘𝚘𝚝𝚜/𝚠𝚘𝚛𝚍𝚙𝚛𝚎𝚜𝚜 package, you can swap to 𝚛𝚘𝚘𝚝𝚜/𝚠𝚘𝚛𝚍𝚙𝚛𝚎𝚜𝚜-𝚏𝚞𝚕𝚕 to test the latest 7.0 RC:





WordPress 7.0 Release Candidate 3 is available for testing. The final release is scheduled for May 20, 2026. Test it now and report any issues before launch. wp.me/pZhYe-5lg


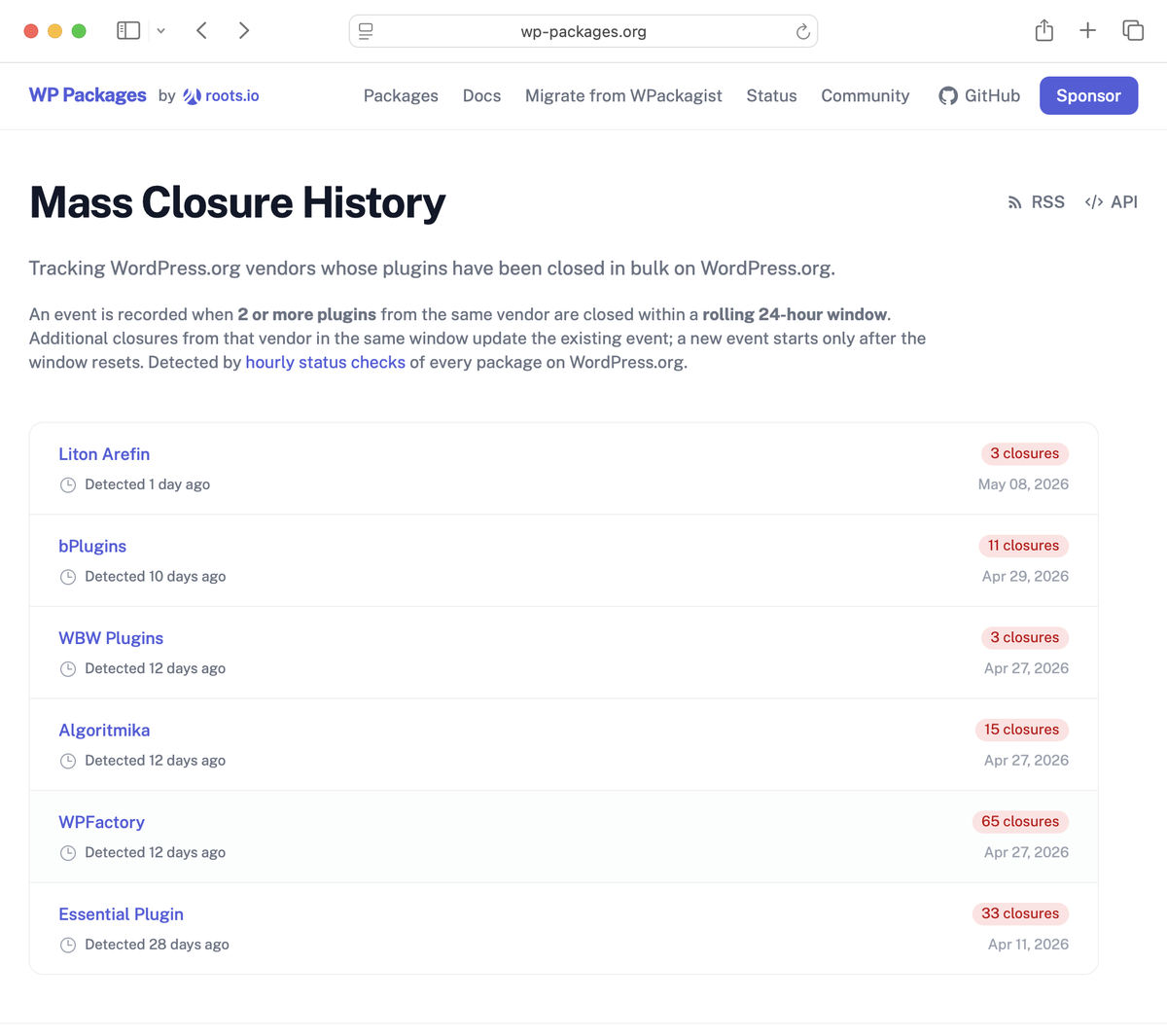
3 ways WordPress plugins break non-standard installs: - Hardcoded wp-content paths - Direct wp-load.php includes - Assuming WP lives at the root roots.io/wordpress-plug…



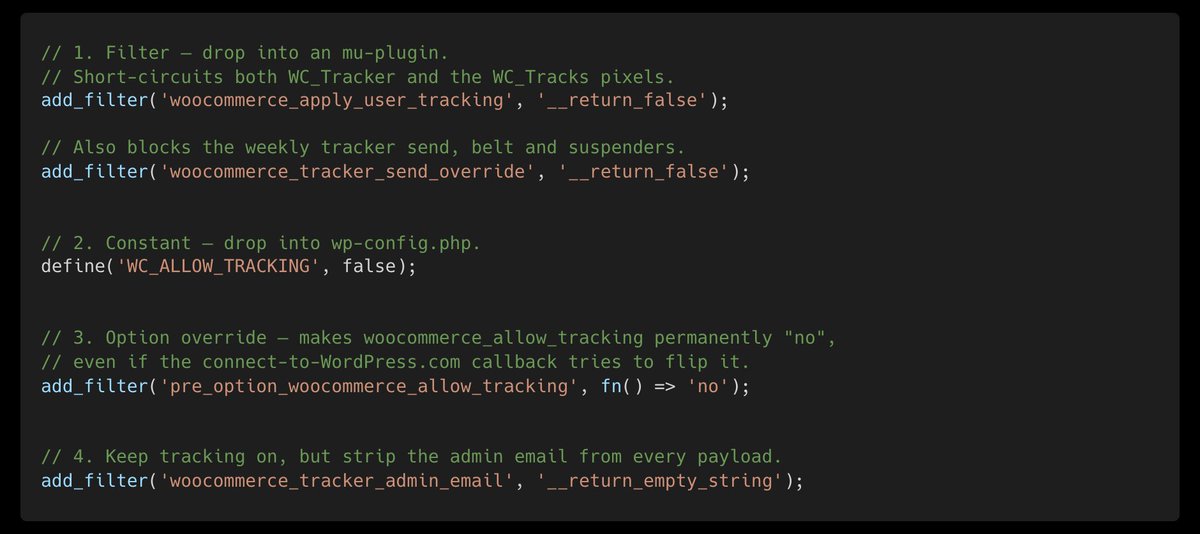
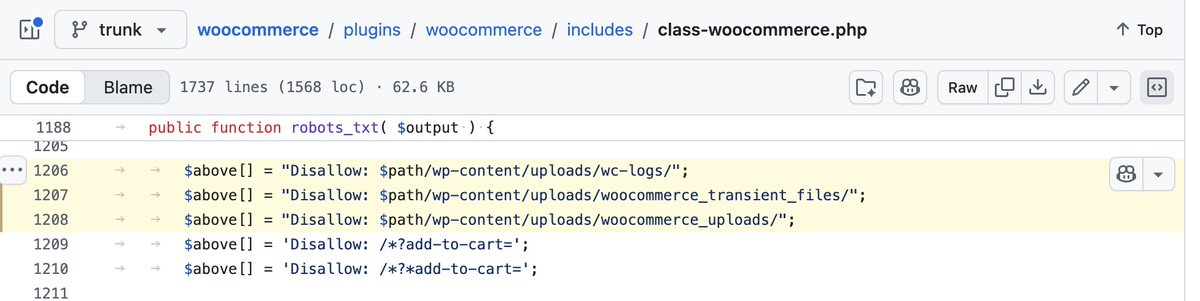
Fun fact: WooCommerce collects your sensitive information without asking for consent. Luckily, it merely consists of about 1000 data points. Let's dive into it... 🧵 Disclosure: I'm a WooCommerce Marketplace partner.





100,000+ stores run this WooCommerce plugin. I doubt any of them know their payments are broken. Any store with $1M ARR could be missing $700k+ in revenue. If you run WooCommerce Subscriptions, check your store. Yesterday, I reported a bug to WooCommerce that silently broke subscription payments after a product switch. Then I got worried: if they missed something this obvious, what else did they get wrong? So I started auditing. Within hours, I had found three more bugs. There were 121 affected subscriptions, and $43,274 in lost revenue. Here's what I found. WooCommerce Subscriptions has an internal flag that controls whether a subscription charges the customer automatically or waits for them to pay manually. When a customer checks out with (for example) Stripe or PayPal, this flag should be set to "automatic." If it isn't, subscription renewals silently stop working: no charge is attempted, no failure email is sent, and the subscription goes on hold until the customer notices and pays manually, or doesn't and churns. Bug 1 (stale cache): After saving subscription dates, the order cache was never cleared. Subsequent saves could serve a stale object with the flag still set to its default: manual. Fixed in subscriptions-core 6.9.0. Bug 2 (broken HPOS backfill): Missing getter/setter methods prevented subscription metadata from being properly synced to postmeta in HPOS when data sync is enabled. Fixed in subscriptions-core 6.5.0. Bug 3 (unnecessary re-fetch): wcs_create_subscription() returned a freshly fetched instance from cache/DB instead of the already-configured object. Any unsaved state, including the corrected flag, was silently discarded. Fixed in subscriptions-core 7.1.0. These three combined accounted for roughly 7% of all subscriptions created at checkout that were silently born broken, despite the customer paying successfully. For 7+ years (we have data from 2017–2024). Automatic payments NEVER fired for these subscriptions. Users never got renewal emails, either. The only way to know they were broken was if the customer noticed they lost access and contacted support, or if the merchant audited their database manually. Bug 4 (switch): When a customer upgrades or downgrades their subscription, the switcher flags the subscription as manual renewal; it only corrects the flag if the payment gateway changes. A customer switching plans while keeping the same gateway (e.g. Stripe to Stripe) cements the flag stuck on manual. I discovered this two days ago, when I found a happy customer in the store overview that I had just helped upgrade, with multiple valid cards on file, put "On Hold" because of a missed payment. For years, I've offered to help WooCommerce improve its code quality and performance. I dry-run code: I find bugs by reading. All four of these bugs are clearly visible in the source without needing to use the software. They could have been caught early. They weren't. The incompetence is immeasurable (well, actually, with the diagnostic queries in my next post, it might be measurable). Our store is small. WooCommerce Subscriptions powers hundreds of thousands of stores. If 7% of subscriptions were silently broken across even a fraction of them, we're looking at potentially millions of dollars in spoiled revenue industry-wide that could have been prevented. Perhaps even billions. None of this was disclosed well or at all. No admin notice. No email. No advisory. The fixes shipped under vague changelog lines like "Make sure we always clear the subscription object from cache after updating dates" and "Ensure proper backfilling of subscription metadata." One fix was labeled "Dev" instead of "Fix." Two don't appear in the GitHub release notes at all. No remediation tool or diagnostic query was provided. Store owners have NO way to know they're affected unless they manually audit their database. The woocommerce-subscriptions-core repo was archived in May 2025 after the code was absorbed into WooCommerce core — making the fix history harder to trace. If you run WooCommerce Subscriptions and used HPOS before mid-2024, check your store. Queries are linked in the tweet below.