Sabitlenmiş Tweet
RST Cloud
12K posts


RST Cloud
@rst_cloud
Threat intelligence solutions for businesses of all sizes
Sydney, New South Wales Katılım Ocak 2015
89 Takip Edilen636 Takipçiler

#tireport #ExtractedDiagrams
The key diagram for the report (ML Classifier):
code: 3, schema: 2, table: 1, windows: 6, chats: 3

English

#threatreport #HighCompleteness
DragonBreath: Dragon in the Kernel | 22-04-2026
Source: ransom-isac.org/blog/dragonbre…
Key details below ↓
🧑💻Actors/Campaigns:
Golden_eyed_dog
Apt31
Dragon_breath
Winnti
I-soon_leak
Silver_fox
💀Threats:
Byovd_technique, Roningloader, Cobalt_strike_tool, Hive_ransomware, Burntcigar, Gh0st_rat, Catena, Winos, Krbanker, Valleyrat, Donut_loader, Supply_chain_technique, Process_injection_technique, Process_hollowing_technique,
🎯Victims: Cybersecurity vendors, Enterprise endpoints, Chinese speaking users
🏭Industry: Telco, Energy, E-commerce, Iot, Software_development, Government, Healthcare, Aerospace, Retail
🌐Geo: China, Guangdong, Chinese, Hong kong, Norwegian
📚TTPs:
⚔️Tactics: 4
🛠️Technics: 12
🧨IOCs:
- File: 7
- Hash: 6
💽Software: Windows kernel-mode driver, LetsVPN, ollama, Windows kernel, Windows service, Microsoft Defender for Endpoint, etsVPN to, Huorong, ma.sys, ong; PPL, ...
🔢Algorithms: sha256
🔠Functions: Payload, CreateService, CreateFile
🗂️Win API: ZwTerminateProcess, SeDebugPrivilege, CreateFileA, CreateServiceA, SeLoadDriverPrivilege, PsGetProcessImageFileName, KeStackAttachProcess, PsGetProcessPeb, RtlInitUnicodeString, PsSetCreateProcessNotifyRoutineEx, ...
⚙️Win Services: CVD, MsMpEng
💻Platforms: x64
YARA: Found
#threatreport:
The analysis details a significant 0-day "Bring Your Own Vulnerable Driver" (BYOVD) vulnerability in the Windows kernel-mode driver named *dragoncore_k.sys*, signed by Zhengzhou 403 Network Technology Co., Ltd. This driver exposes an unauthenticated IOCTL interface, allowing any process with local administrative rights to terminate processes running at Ring 0, including those protected by Microsoft's Protected Process Light (PPL) feature. This capability effectively undermines endpoint detection and response (EDR) and antivirus (AV) solutions.
The investigation identifies Zhengzhou 403 Network Technology as a potential shell company linked to the Dragon Breath APT (APT-Q-27) ecosystem. Secondary attribution connects it to APT31, further highlighting the intricate associations of state-sponsored cyber activities. The driver was compiled in November 2024 and showed signs of rapid operational deployment, supported by evidence that its GlobalSign EV certificate was revoked for abuse after receiving a valid WHQL signature. Its infrastructure suggests it operates in conjunction with malicious activities, such as the distribution of malware via a "letsvpn-3.12.3.exe" sample that mimics legitimate software to evade suspicion.
The vulnerability stems from inadequate privilege and context validation in the driver’s IOCTL handler, which does not authenticate the integrity level of the calling thread nor does it ensure that the process being targeted is PPL-protected. Exploitation can be initiated via malicious dropper executables which deploy the driver and facilitate termination commands, effectively disabling security measures from EDRs and AVs. The primary exploitation chain is designed to seamlessly bypass defenses by registering the driver as a Windows service.
Furthermore, the analysis elaborates on the malicious capabilities embedded within the *dragoncore_k.sys*, including a sophisticated process inspector and memory modification engine. This malware can alter command-line parameters of targeted processes without leaving traces, targeting established detection frameworks employed by EDR solutions. The driver has similar functionality to another vehicle in the Dragon Breath APT repertoire, *ollama.sys*.
Shared command-and-control (C2) infrastructure has been identified, with multiple samples communicating through the same C2 endpoint, indicating coordinated attack patterns across various malicious payloads. The shared certificates and the geographical registry location of Zhengzhou 403 raise red flags about its legitimacy. The analysis further ties the company's founder, Zhang Liye, to personnel associated with APT31, reinforcing the connection between this commercial front and state-sponsored cyber threats.
The report highlights immediate measures to combat the threats, including blocking the identified driver by hash, employing strict access controls, and proactively monitoring for unusual behavior indicative of ongoing exploitation attempts. Overall, *dragoncore_k.sys* represents a formidable threat to enterprise security, combining advanced evasion techniques with robust operational ties to known APT entities. The examination calls for a deeper understanding of the signing entities as part of broader threat intelligence efforts, suggesting that cybersecurity measures must evolve beyond conventional vulnerability assessments to include analysis of company structures and signing practices indicative of malicious intent.

English


#threatreport #HighCompleteness
Dissecting FudCrypt: A Real-World Malware Crypting Service Analysis | 19-04-2026
Source: ctrlaltintel.com/research/FudCr…
Key details below ↓
💀Threats:
Dll_sideloading_technique, Native_loader, Screenconnect_tool, Polymorphism_technique, Uac_bypass_technique, Clickfix_technique, Kleenscan_tool, Amsi_bypass_technique, Metasploit_tool, Junk_code_technique, Hellsgate_technique, Procmon_tool, Icmluautil_tool, Dll_injection_technique,
📚TTPs:
⚔️Tactics: 7
🛠️Technics: 17
🧨IOCs:
- Domain: 5
- File: 72
- IP: 10
- Path: 5
- Registry: 6
- Command: 1
- Coin: 1
- Hash: 7
💽Software: Windows Defender, PostgreSQL, Redis, MinIO, Docker, r Compos, , r, runni, md, Zoom, ...
🪙Crypto: bitcoin
🔢Algorithms: rc4, aes-256-cbc, sha256, bcrypt, zip, aes, md5, base64, xor
🔠Functions: UAC, Win32, is_safe_to_run, CMSTPLUA, SetRegDword, ReadAllBytes, Set-Location
🗂️Win API: GetAdaptersInfo, WerReportCreate, DWriteCreateFactory, timeGetTime, timeBeginPeriod, timeEndPeriod, GetProcAddress, LoadLibraryW, AmsiScanBuffer, LoadLibraryA, ...
📜Programming Languages: python, powershell
💻Platforms: x86, x64
#threatreport:
FUD Crypt operates as a Cryptor-as-a-Service platform, facilitating the creation of malware deployment packages for subscribers who pay between $800 and $2,000 monthly. Users can upload any Windows executable, which FUD Crypt packages with advanced techniques aimed at evading detection and achieving persistence on targeted systems. The malware features automatic DLL sideloading, in-memory bypasses for Windows Defender components, silent UAC elevation, and Tamper Protection circumvention using Group Policy alterations on enterprise systems.
The platform's infrastructure is supported by four Azure Trusted Signing accounts that certify operator-controlled binaries. It comprises a fleet of agents, with 32 agents documented in a command history that indicates extensive use of PowerShell and command execution methods. Core elements of the service include sideloading techniques with up to 20 undocumented DLLs, emphasizing polymorphic encryption involving XOR and RC4, along with custom transformations to obscure payloads per build.
The malware utilizes sophisticated methods for evasion, such as AMSI and ETW interference, achieved through direct memory patches and hardware breakpoints, enabling silent execution of malicious activities under the guise of legitimate system processes. This threat has established a tight build pipeline, using proprietary scripts to download payloads from Docker-exposed services and execute them stealthily. The payloads often utilize established products like ScreenConnect for remote access, but they are delivered through various methods, including phishing.
The architecture also supports anti-analysis measures, with hardcoded checks against known sandbox environments, while using tricks like "module stomping" to manipulate legitimate DLLs in memory. Furthermore, the malware employs a three-stage loader that helps maintain operational security and evade detection during execution.
While the techniques utilized by FUD Crypt may not be groundbreaking, the seamless integration of their service — combining advanced crypting capabilities, automated testing, and operational infrastructure for malicious deployments — presents a sophisticated threat landscape. The possibility for customization and tailored user experiences increases the risk posed by this platform, making it a noteworthy aspect of current cyber threat intelligence.

English

#threatreport #LowCompleteness
The cPanel Situation Is… | 01-05-2026
Source: censys.com/blog/the-cpane…
Key details below ↓
💀Threats:
Mirai, Hiddentear,
🎯Victims: Cpanel and whm systems, Hosting providers, Vps providers
🔓CVEs: CVE-2026-41940 \[[Vulners](vulners.com/cve/CVE-2026-4…)]
- CVSS V3.1: *9.8*,
- Vulners: Exploitation: True
Soft:
- cpanel (<86.0.41, <110.0.97, <118.0.63, <126.0.54, <130.0.19)
🤖LLM extracted TTPs:`
T1110.001, T1190, T1486
🧨IOCs:
- Hash: 1
- File: 10
💽Software: cPanel, anel, Twitter
🔢Algorithms: sha256
🗂️Win API: ARC
💻Platforms: x86
#threatreport:
The recent disclosure of CVE-2026-41940, a critical pre-authentication bypass vulnerability in cPanel/WHM, has led to significant implications for the security of these systems. This vulnerability allows unauthenticated attackers to bypass authentication controls and gain elevated access, which could facilitate subsequent exploitation. Following its disclosure on April 29, 2026, there was a marked increase in malicious activity targeting cPanel and WHM. Data from Censys indicates that approximately 80% of the newly malicious hosts observed on May 1 were running these applications, a stark deviation from normal activity patterns.
Two primary attack vectors have emerged in relation to this vulnerability. The first involves the deployment of Mirai variants that are executed after systems are compromised. The second vector appears to be a ransomware campaign that modifies files by encrypting them and appending a .sorry extension. The rapid increase in reports of ransomware activity correlates with a substantial number of cPanel hosts that are unnecessarily exposing files via open directories, indicating that large-scale automated exploitation is likely in progress.
Investigations revealed that the surge in malicious classifications was largely concentrated among hosts operated by VPS and hosting providers using cPanel. Initially, the comparative analysis of malicious activity indicated that cPanel systems contributed a negligible fraction to the total before May 1, but this drastically changed as nearly 15,000 new malicious cPanel instances were added in a single day, highlighting the vulnerability's exploitation.
Further examination of the malware reportedly associated with these exploits pointed to a variant of Mirai named nuclear.x86. However, analysis of the binary indicated that while the exploits for cPanel were not directly integrated into the malware, it is utilized as a staging ground for post-exploitation activities.
An alarming development tied to ransomware was detected, with over 7,000 cPanel servers showing newly created open directories, where files ended with the .sorry suffix—a common trait of ransomware activity. This file extension and structural pattern raise strong concerns regarding a coordinated ransomware attack leveraging the cPanel vulnerability, which appears to be evolving as more infected systems are observed.

English

#threatreport #MediumCompleteness
Oluomo: Microsoft OAuth AiTM Phishing Using a Naturalization-Form Lure | 22-04-2026
Source: censys.com/blog/oluomo-mi…
Key details below ↓
💀Threats:
Aitm_technique,
🎯Victims: Microsoft users, Immigration professionals, Government immigration services, Nonprofit organizations, Individuals in the naturalization process, Business websites
🏭Industry: Foodtech, Education, Government, Entertainment
🌐Geo: Chile, Ecuador, Belarus, Australia, India, Singapore, New zealand, Australian, Peru
📚TTPs:
⚔️Tactics: 1
🛠️Technics: 0
🤖LLM extracted TTPs:`
T1036.005, T1528, T1557, T1583.001, T1583.006, T1584.004
🧨IOCs:
- Domain: 57
- File: 15
- Url: 11
- Hash: 1
- IP: 8
💽Software: Microsoft content
🔢Algorithms: sha256
🔠Functions: skipWaiting
📜Programming Languages: javascript
#threatreport:
The OLUOMO phishing campaign, detected since late November 2025, employs a sophisticated Adversary-in-the-Middle (AiTM) technique to harvest Microsoft credentials and session tokens. The operation consists of two distinct stages: initially, a phishing lure is served from compromised legitimate websites, while the second stage utilizes an AiTM proxy running on Azure Web Apps to intercept Microsoft’s OAuth flows in real-time. The lure prominently features a U.S. Petition for Naturalization, likely chosen for its emotional and cultural resonance with specific target audiences involved in the U.S. immigration process.
The campaign's infrastructure is geographically distributed yet operationally coherent, with compromised domains located in countries such as Chile, Australia, Belarus, and New Zealand. These first-stage phishing sites lead users to a malicious proxy on Azure, which impersonates Microsoft’s legitimate login page using a lookalike domain: orgid.com, designed to mimic portal.microsoftonline.com. This setup allows attackers to leverage the inherent trust associated with legitimate services, as they are not exploiting vulnerabilities within individual platforms like Imgur, Azure, or Microsoft, but rather assembling phishing elements from these trusted providers.
Upon interaction with the phishing lure, victims are instructed to enter their email addresses; this data is captured and redirected to a malicious endpoint. The second-stage proxy engages a service worker to manage credential theft. It manipulates real Microsoft's OAuth login flow by injecting an additional script that notifies the attacker when the login page has rendered, enabling the systematic collection of credentials.
Monitoring efforts revealed the campaign's breadth, illustrating the complexity of the phishing pipeline combining various trusted entities. A significant insight from this operation is that attackers have cleverly constructed a trust chain, forcing victims to confront a series of legitimate services that obscure the malicious intent. The operational architecture underscores how cyber threats evolve, blurring the boundaries between compromised and legitimate infrastructures. Without access to the phishing email telemetry used for initial delivery, which likely plays a crucial role in the targeting mechanism, it remains speculative as to whether the campaign specifically targets immigration professionals or a wider audience.
Ultimately, the OLUOMO campaign exemplifies an evolving threat landscape where attackers effectively exploit legitimate services to execute sophisticated phishing operations that challenge conventional detection methods. The behavioral analysis of this phishing technique highlights the need for enhanced vigilance and protective measures that go beyond traditional phishing awareness campaigns, addressing the tactics that rely on the sophistication of and reliance on legitimate service ecosystems.

English

#threatreport #LowCompleteness
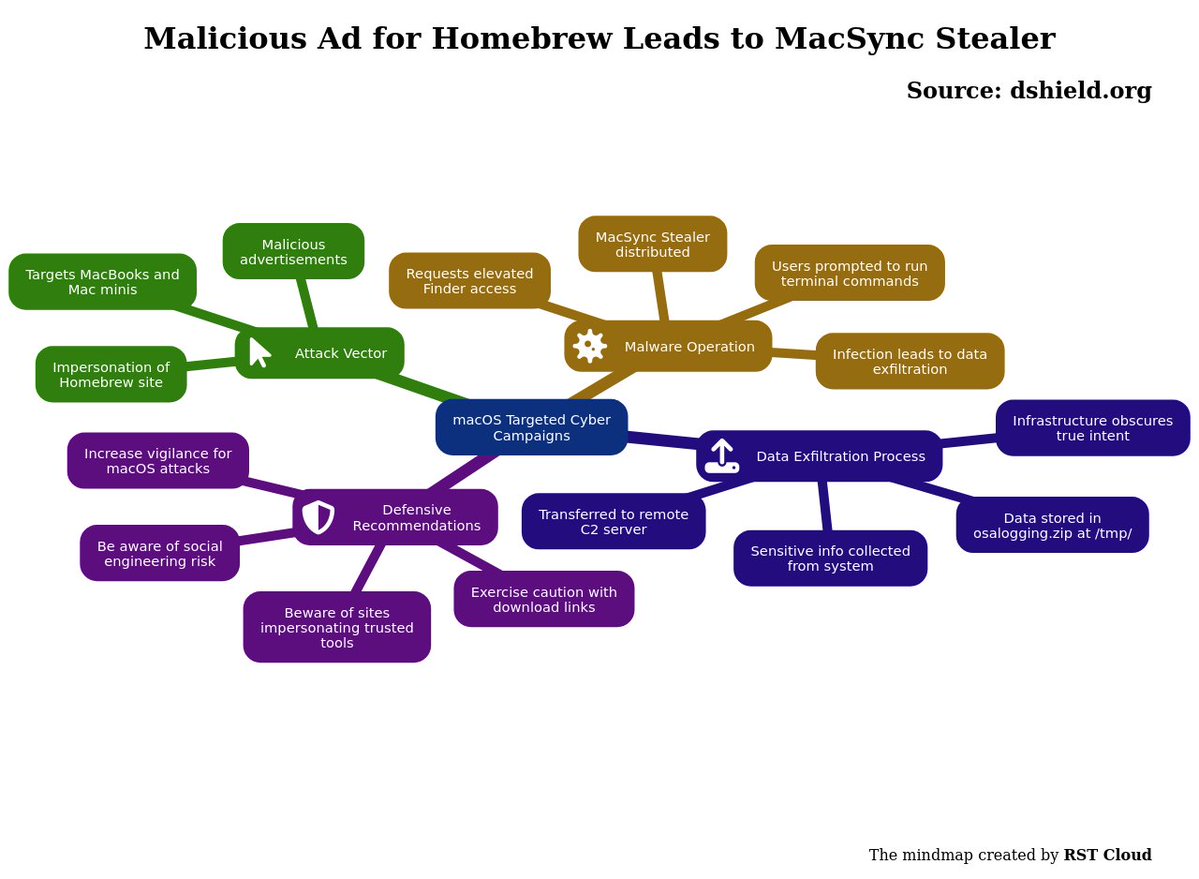
Malicious Ad for Homebrew Leads to MacSync Stealer | 01-05-2026
Source: dshield.org/diary/Maliciou…
Key details below ↓
💀Threats:
Macc_stealer,
🎯Victims: Macos users
🤖LLM extracted TTPs:`
T1005, T1036, T1041, T1059.004, T1105, T1204.001, T1204.004, T1560
🧨IOCs:
- Url: 3
- Domain: 1
- Hash: 3
💽Software: macOS
🔢Algorithms: sha256, zip, base64
#threatreport:
Recent trends indicate an increase in cyber campaigns targeting macOS devices, particularly MacBooks and Mac minis. A notable case involves a malicious advertisement that directs users to a fraudulent webpage impersonating Homebrew, a popular third-party package manager for macOS. This malicious ad was observed on April 30, 2026, leading unsuspecting victims to a site that claims to support Homebrew but instead promotes the MacSync Stealer malware.
The page in question, still active as of May 1, 2026, contains deceptive scripts that encourage users to download malware disguised as legitimate software. Specifically, users are misled into copying and pasting commands into their terminal, enabling the infection process. Once executed, the malware prompts the Terminal app for elevated access to the macOS Finder, facilitating its installation.
During the infection phase, MacSync Stealer operates by collecting sensitive information from the compromised host. The data is temporarily stored in a file named `osalogging.zip` located in the `/tmp/` directory, which is then transmitted to a command-and-control (C2) server, signaling successful data exfiltration. The underlying infrastructure is designed to disguise the malicious intent, making it challenging for users to recognize the threat.
Cybersecurity stakeholders are advised to remain vigilant and skeptical of search results that offer downloads for software, particularly when impersonation is involved. This case emphasizes the need for heightened awareness regarding potential attacks leveraging social engineering tactics within the macOS ecosystem.
English

#threatreport #LowCompleteness
The New Hacking Tool That Lets Anyone Launch Their Own Spyware Company | 30-04-2026
Source: certosoftware.com/insights/the-n…
Key details below ↓
🎯Victims: Android users, Mobile device users
🌐Geo: New york
🤖LLM extracted TTPs:`
T1402, T1408, T1417, T1429, T1430, T1512, T1513, T1626.001
🧨IOCs:
- Hash: 5
💽Software: Android, WhatsApp, Viber, Telegram, Google Play
#threatreport:
Certo has identified a new Android surveillance tool called KidsProtect, which functions as a Remote Access Trojan (RAT). This tool allows operators to gain near-total control of a victim's smartphone without their knowledge. Once installed, the software runs in the background, enabling capabilities such as live call recording, audio streaming via the device's microphone, GPS tracking, reading SMS messages, logging keystrokes, and accessing photos and contact lists. Importantly, it can also trigger the front and rear cameras remotely and block user uninstallation through registering itself as a Device Administrator.
The app disguises itself under the guise of parental control, yet its advertisement speaks openly to its surveillance capabilities. The analysis of the app's APK has confirmed its extensive permissions requests, including ACCESS_BACKGROUND_LOCATION, RECORD_AUDIO, CAMERA, and READ_SMS, among others, showcasing its invasive functionality. A key point in the malware's operation is its use of the Accessibility Service permission, which is often misused in Android malware for intercepting and reading app content, including passwords.
To ensure its effectiveness, the installation instructions for KidsProtect include disabling Google Play Protect, the built-in malware scanner designed to prevent harmful software installations. Additionally, the app requests SYSTEM_ALERT_WINDOW and REQUEST_IGNORE_BATTERY_OPTIMIZATIONS, allowing it to run persistently in the background by preventing the system from shutting it down due to power-saving measures. The presence of a BootReceiver component guarantees that the spyware automatically restarts after device reboots, maintaining its control over the device consistently.
The model of offering such surveillance technology as a white-label solution poses a considerable threat as it allows various actors to easily rebrand and sell the software, thereby complicating enforcement efforts against such tools in the stalkerware market. This is particularly significant in light of increasing legal scrutiny against similar operators, suggesting that without tackling the core technology, interventions may have limited long-term effectiveness. The situation highlights a growing challenge in countering the proliferation of spyware that is becoming increasingly accessible to anyone willing to pay for it.

English

#threatreport #MediumCompleteness
TeamPCP-Linked Supply Chain Attack Hits SAP CAP and Cloud MTA npm Packages | 29-04-2026
Source: socket.dev/blog/sap-cap-n…
Key details below ↓
🧑💻Actors/Campaigns:
Teampcp
💀Threats:
Supply_chain_technique, Shai-hulud, Dead_drop_technique,
🎯Victims: Sap cap ecosystem, Developers, Ci cd environments
🌐Geo: Russian
📚TTPs:
⚔️Tactics: 3
🛠️Technics: 0
🤖LLM extracted TTPs:`
T1003.007, T1005, T1027, T1059.006, T1078.004, T1102.001, T1105, T1140, T1195.001, T1528, ...
🧨IOCs:
- File: 6
- Command: 1
- Hash: 5
- Url: 1
💽Software: PostgreSQL, Bitwarden, CIRCLECI, TRAVIS, Kubernetes, claude, Slack, Telegram, Discord, VSCode, ...
🔢Algorithms: xor, sha256, aes-256-gcm, md5, zip, pbkdf2
🔠Functions: __decodeScrambled
📜Programming Languages: python, javascript
#threatreport:
A recent supply chain attack linked to the threat actor team known as TeamPCP has been identified in several npm packages related to SAP's Cloud Application Programming Model (CAP) and cloud deployment tools. This attack endangers developers and CI/CD environments due to the compromised packages, which download and execute unverified binaries.
The malicious payload, referenced as execution.js, is a highly obfuscated JavaScript file of approximately 11.7 MB. It employs complex encoding techniques such as PBKDF2 for sensitive data, with 200,000 iterations utilizing a specific salt. The payload has multiple layers of obfuscation, making meaningful identifiers unrecoverable. Additionally, the malware is designed to halt execution if the environment is set to a Russian locale, and it exhibits conditional branching based on CI/CD platform environment variables.
The exploitation targets include SSH keys, cloud credentials from major providers, developer configuration files, environment files, cryptocurrency wallets, and chat application data. In CI runners, the payload extracts sensitive information directly from memory, bypassing any masking mechanisms implemented by the CI platforms.
Data exfiltration is executed by encrypting the harvested credentials with a hardcoded RSA public key and AES-256-GCM. Compromised data is uploaded to a GitHub repository created under the victim's account, following a specific naming scheme that has been reused in previous TeamPCP attacks. For self-propagation, the malware uses stolen npm tokens to inject the execution.js payload into other packages maintained by the victim, a move that indicates prior mapping of the SAP CAP.js dependency graph.
Persistence mechanisms involve creating backdoor files in developer tooling that re-execute the payload at project openings in integrated development environments (IDEs). Compared to previous iterations of TeamPCP's malware, this variant's persistence method has shifted to IDEs, rather than relying on traditional system startup files.
The attack has three variants of the execution.js payload, each targeting different packages, revealing incremental advancements in capabilities. This activity is consistent with TeamPCP's history of targeting development tools and environments, including GitHub, cloud, and CI/CD credentials. Key attribution signals include the use of specific engineering choices in the malware code and modus operandi that align with prior incidents of TeamPCP-related supply chain compromises.
Organizations are advised to monitor for unusual access patterns related to the installation of npm packages, particularly those associated with the execution of the malicious scripts. Detecting suspicious activities in cloud metadata services and from tools related to JavaScript execution will be crucial in mitigating the impact of this evolving threat.

English

#threatreport #HighCompleteness
Hackers Are Attempting to Turn ComfyUI Servers Into a Cryptomining Proxy Botnet | 06-04-2026
Source: censys.com/blog/comfyui-s…
Key details below ↓
💀Threats:
Xmrig_miner, Lolminer, Gh0st_rat, Supportxmr, Gminer, Ethminer, Httpx_tool,
🎯Victims: Comfyui instances, Cloud infrastructure, Ai art community
🏭Industry: Healthcare
🌐Geo: China, Russian, Guangdong
📚TTPs:
⚔️Tactics: 4
🛠️Technics: 0
🧨IOCs:
- Url: 5
- IP: 6
- File: 42
- Domain: 2
- Coin: 1
- Hash: 6
💽Software: crontab, curl, systemd, Docker, Redis, torch, Linux, Jupyter notebooks, Uvicorn, Jenkins, ...
🪙Crypto: monero, conflux
🔢Algorithms: ed25519, base64
🔠Functions: check_host, readdir, _anti_hisana
🗂️Win API: ARC
📜Programming Languages: python
💻Platforms: amd64, arm
#threatreport:
An active campaign has emerged targeting unauthenticated instances of ComfyUI, a graphical interface used primarily for running AI models, particularly in the realm of AI art generation. Security researchers from Censys ARC identified over 1,000 publicly accessible deployments that are vulnerable to remote code execution (RCE) due to improper configurations, specifically those allowing arbitrary Python code execution via custom nodes. Attackers utilize a purpose-built Python scanner that systematically probes major cloud IP ranges, automatically deploying malicious nodes if exploitable ones are absent.
Once compromised, hosts are enlisted into a dual attack structure: a cryptocurrency mining operation using XMRig for Monero and lolMiner for Conflux, alongside a Hysteria v2 proxy botnet, managed through a Flask-based command-and-control (C2) panel. The malware, termed ghost.sh, exhibits sophisticated behaviors for evasion and persistence, including fileless execution techniques and disguising its processes as legitimate kernel threads. Updated versions of the scanner, particularly v8.2, introduce two backdoor mechanisms that ensure continual infection—one masquerading as a GPU Performance Monitor that re-downloads the payload every six hours.
The exploitation mechanism primarily hinges on the vulnerability of ComfyUI's architecture, where malicious payloads can be injected through custom nodes that accept raw Python code. If no such nodes are installed, the scanner checks and installs a malicious ComfyUI-Manager module to facilitate exploitation. Known as GHOST v5.1, the installed script employs various tactics for operation and resilience. For instance, it uses techniques like memfd_create for memory-backed execution, and LD_PRELOAD to hide its presence by injecting itself into other processes. To ensure survival against removal attempts, ghost.sh deploys an inotify guard and creates scattered copies of itself throughout the filesystem, all while masking its activities from system monitoring tools.
In terms of competitive tactics, the GHOST malware identifies and neutralizes other mining processes by killing them using an extensive blacklist and employing iptables to block known mining pool connections. It also implements mechanisms to hijack other botnets, specifically targeting a competitor identified as Hisana by overwriting its configurations with the attacker’s own mining pool details.

English

#threatreport #HighCompleteness
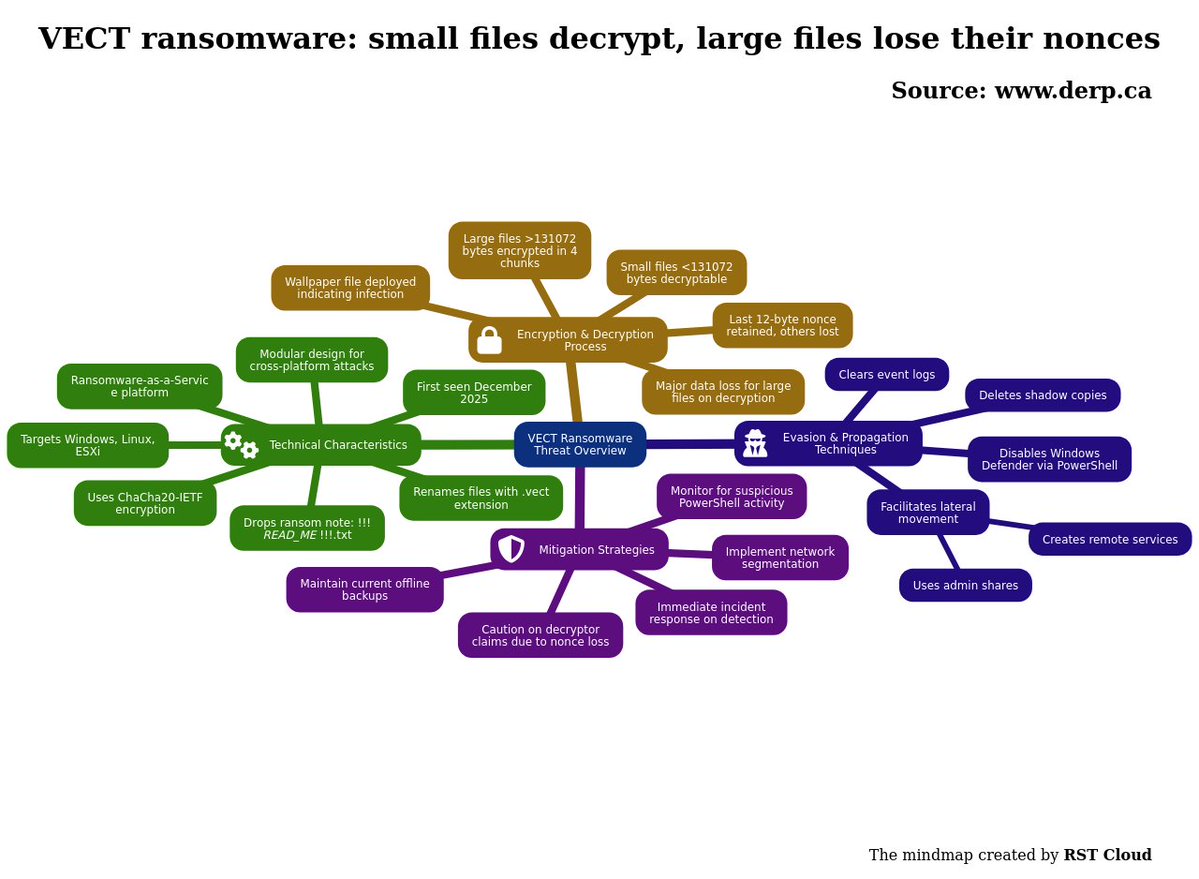
VECT ransomware: small files decrypt, large files lose their nonces | 02-05-2026
Source: derp.ca/research/vect-…
Key details below ↓
🧑💻Actors/Campaigns:
Vect
Teampcp
💀Threats:
Supply_chain_technique, Shadow_copies_delete_technique, Wevtutil_tool, Qtox_tool,
🎯Victims: Security, Software development, Developer infrastructure, Cloud infrastructure
📚TTPs:
⚔️Tactics: 3
🛠️Technics: 0
🤖LLM extracted TTPs:`
T1021.002, T1021.006, T1047, T1053.005, T1059.001, T1059.003, T1070.001, T1070.004, T1078, T1112, ...
🧨IOCs:
- File: 14
- Path: 3
- Command: 4
- Hash: 6
- Url: 1
- Domain: 1
💽Software: Linux, ESXi, Trivy, LiteLLM, Kubernetes, Windows PowerShell, Telegram
🔢Algorithms: md5, poly1305, base64, sha256, sha1, chacha20-poly1305, chacha20
🔠Functions: Set-MpPreference
⚙️Win Services: MSSQLSERVER
📜Programming Languages: powershell
💻Platforms: x64
#threatreport:
VECT ransomware represents a complex and emerging threat operating as a ransomware-as-a-service (RaaS) platform. Initiated in late December 2025 and publicly claiming victims by January 2026, VECT has a modular design that supports attacks across Windows, Linux, and VMware ESXi environments. The malware utilizes the ChaCha20-IETF encryption algorithm for file encryption, specifically employing raw ChaCha20 for its encryption routine.
The operational architecture displays unique characteristics, particularly with file sizes exceeding 131,072 bytes, where the malware processes files in four chunks but only retains the last 12-byte nonce, leading to significant data loss upon attempted decryption of larger files. Conversely, files smaller than this threshold are decryptable without issue due to their simpler handling processes. The VECT ransomware is specifically known to rename encrypted files with a .vect extension and includes a ransom note titled "!!!_READ_ME_!!!.txt", alongside a wallpaper file indicating encryption activity.
Behaviorally, VECT employs various techniques to evade detection and hinder recovery efforts. It disables Windows Defender features through PowerShell commands, deletes shadow copies to eliminate recovery points, and systematically clears system event logs to obscure its activities. Additionally, embedded within its code are commands facilitating lateral movement across networks, such as utilizing admin shares and creating remote services. This shows that VECT not only encrypts files but also has the capability to propagate through networked environments, increasing the scope of its impact.
With regards to recovery options, attempts to use a decryptor based on public claims have been met with caution, as a significant portion of nonce data critical for decryption of large files is not preserved during the encryption process. This raises substantial challenges for victims seeking to restore their files, as recovery of the encrypted data without complete nonce information is practically impossible.
In summary, VECT ransomware exemplifies a sophisticated threat with clear operational strategies involving advanced encryption techniques, stealth-based evasion methods, and capabilities for lateral movement within compromised networks. As such, organizations should adopt strict preventive measures, including maintaining up-to-date backups and monitoring for anomalous PowerShell activities to mitigate potential risks associated with this evolving ransomware variant.
English

#tireport #ExtractedDiagrams
The key diagram for the report (ML Classifier):
code: 2, windows: 2, schema: 2, table: 1
English

#threatreport #HighCompleteness
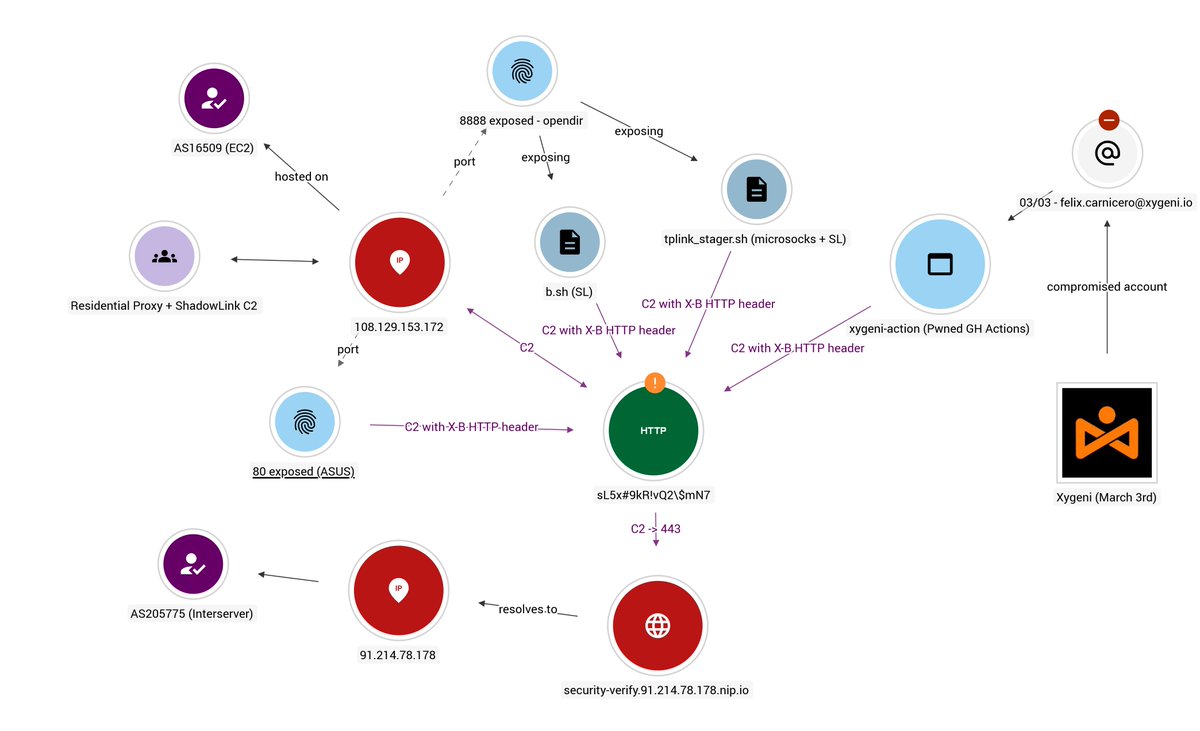
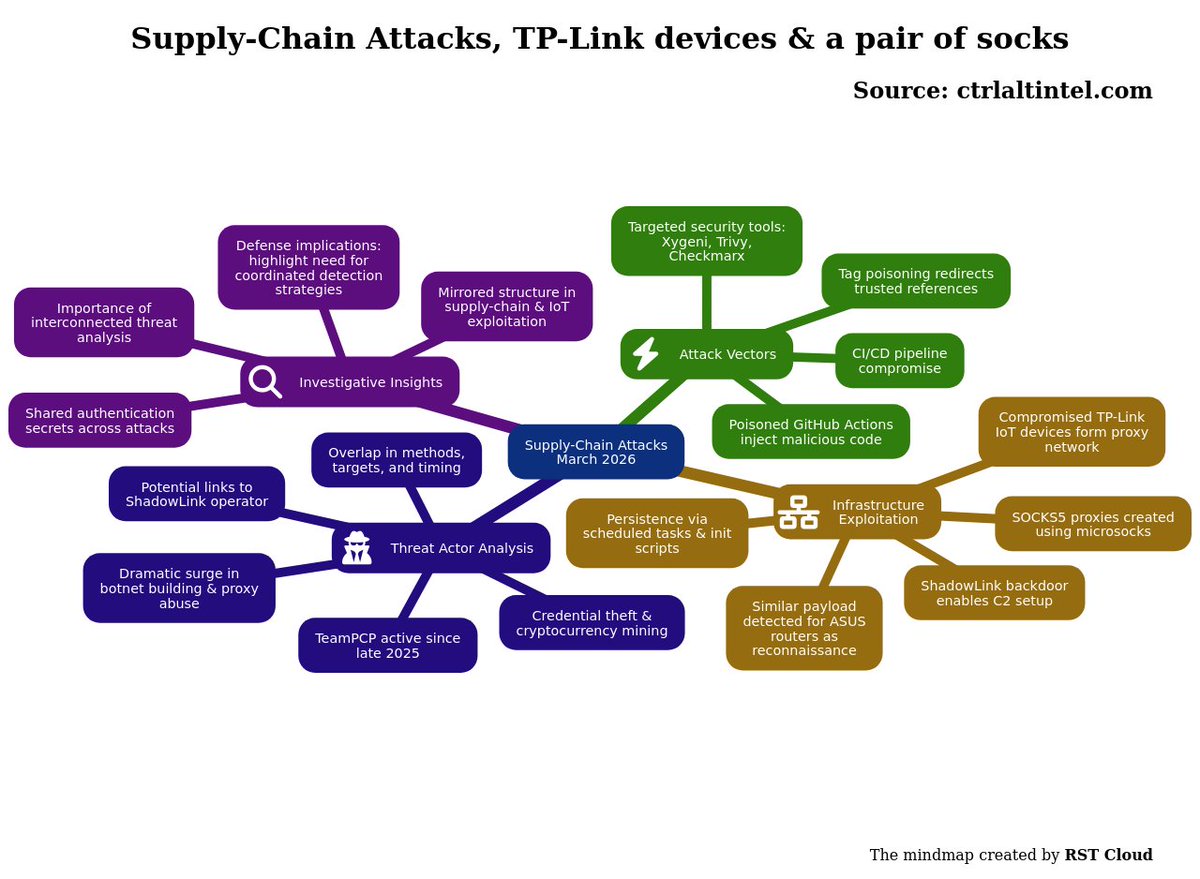
Supply-Chain Attacks, TP-Link devices & a pair of socks | 10-04-2026
Source: ctrlaltintel.com/research/Proxy…
Key details below ↓
🧑💻Actors/Campaigns:
Teampcp
Fancy_bear
💀Threats:
Supply_chain_technique, Residential_proxy_technique, Dns_hijacking_technique, Microsocks_tool, Shadowlink_tool, Starkiller_tool, Empire_loader, React2shell_vuln, Xmrig_miner, Frpc_tool,
🎯Victims: Application security companies, Security vendors, Ci cd pipelines, Iot devices, Tp link routers, Asus routers, Fortiweb firewalls, Servers
🏭Industry: Iot, Telco
🔓CVEs: CVE-2025-55182 \[[Vulners](vulners.com/cve/CVE-2025-5…)]
- CVSS V3.1: *10.0*,
- Vulners: Exploitation: True
Soft:
- facebook react (19.0.0, 19.1.0, 19.1.1, 19.2.0)
CVE-2024-21833 \[[Vulners](vulners.com/cve/CVE-2024-2…)]
- CVSS V3.1: *8.8*,
- Vulners: Exploitation: True
Soft:
- tp-link archer_ax3000_firmware (<1.1.2)
📚TTPs:
⚔️Tactics: 10
🛠️Technics: 24
🧨IOCs:
- IP: 3
- Domain: 1
- Hash: 3
- File: 4
💽Software: Trivy, Redis, Docker, Unix, crontab, systemd, Alibaba Cloud Aegis, Linux, Kubernetes, curl, ...
🔢Algorithms: sha256, base64
📜Programming Languages: python
💻Platforms: mips, arm, x86
#threatreport:
In March 2026, cybersecurity teams faced a series of supply-chain attacks affecting multiple application security companies, with notable incidents linked to poisoned GitHub Actions used to inject malicious code into continuous integration and continuous deployment (CI/CD) pipelines. The attacks primarily targeted security scanning tools, including Xygeni, Trivy, and Checkmarx. Investigations into these breaches revealed a connection to a cybercriminal group named TeamPCP, which has been active since late 2025.
The investigation uncovered that a threat actor, initially tracking residential proxy networks established using compromised TP-Link IoT devices, was also behind a supply-chain attack on Xygeni. Compromised TP-Link routers were found to be running a backdoor named ShadowLink, facilitating a command-and-control (C2) setup that mirrored the malicious code injected into Xygeni's GitHub Actions. This ShadowLink protocol was notable for its shared authentication secrets and consistent structure across both the IoT exploitation and the supply-chain attack.
The TP-Link stager script, tplink_stager.sh, was specifically devised to exploit the CVE-2024-21833 vulnerability found in TP-Link routers, allowing the threat actor to establish a SOCKS5 proxy using the microsocks tool. This approach included masquerading the proxy process as a kernel worker thread and achieving persistence on compromised routers through scheduled tasks and initialization scripts. In parallel, a similar payload was identified for ASUS routers, which functioned as a reconnaissance tool to gather device information before full deployment.
TeamPCP's infrastructure exploitation strategy entailed building extensive SOCKS proxy networks from compromised devices, utilizing techniques like tag poisoning in GitHub Actions to redirect trusted version references to malicious commits. Evidence suggests that TeamPCP's activities dramatically surged in late 2025, exploiting vulnerabilities across multiple platforms and constructing a sizeable botnet aimed at various malicious objectives, including credential theft and cryptocurrency mining.
Although the connections between the ShadowLink operator and TeamPCP remain unclear, both exploit similar targets and methods, particularly around proxy network construction. The insights derived from this analysis suggest that the ShadowLink operator may either be a team member of TeamPCP or a separate actor operating under similar methodologies. Given the overlap in the timing of the attacks, techniques employed, and the target profiles, this case presents an intriguing aspect of modern cyber threats—which exemplifies the growing complexity and interconnectivity of cybercriminal operations. Understanding these threads could be vital for future defense strategies and threat detection efforts.
English

#threatreport #HighCompleteness
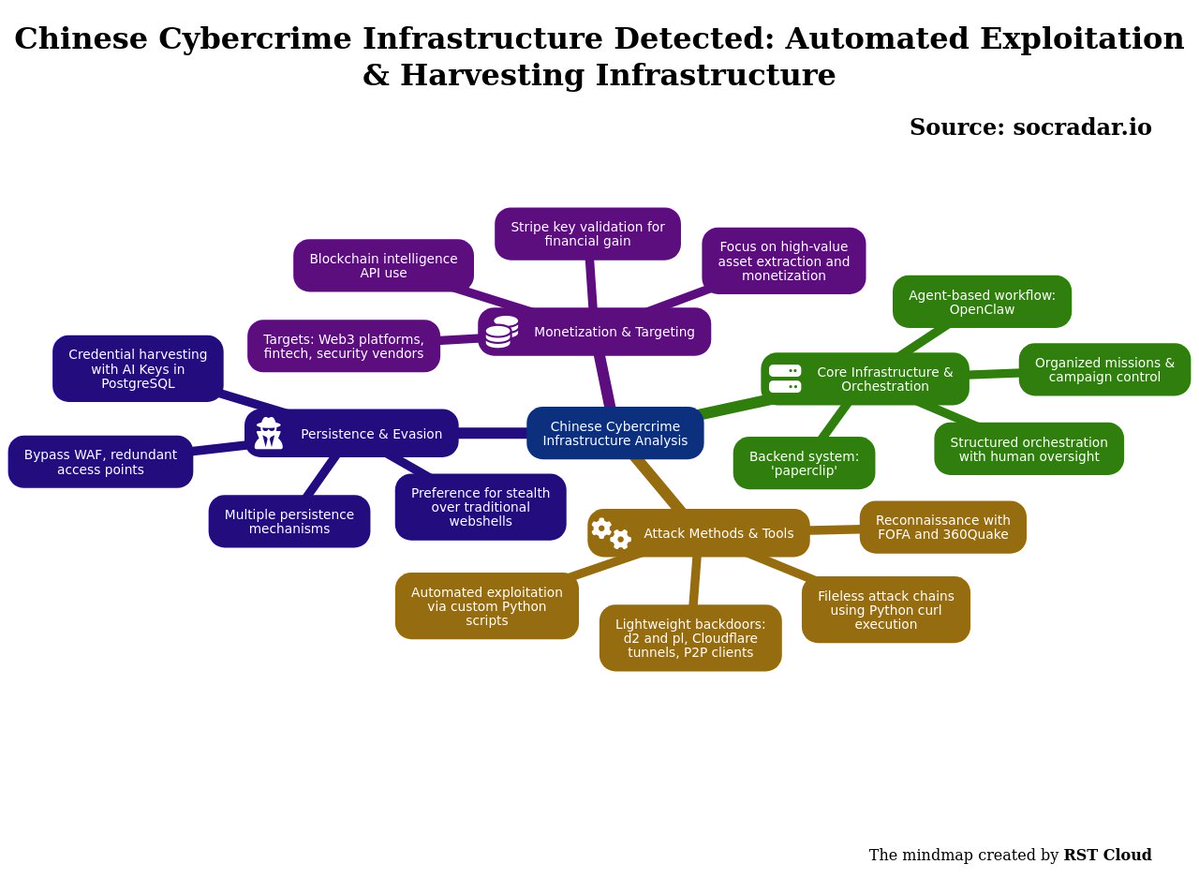
Chinese Cybercrime Infrastructure Detected: Automated Exploitation & Harvesting Infrastructure | 03-05-2026
Source: socradar.io/blog/chinese-c…
Key details below ↓
💀Threats:
React2shell_vuln, Log4shell_vuln, Credential_harvesting_technique,
🎯Victims: Web3 platforms, Fintech services, Security vendors
🏭Industry: Financial
🌐Geo: Chinese
🔓CVEs: CVE-2025-66478 \[[Vulners](vulners.com/cve/CVE-2025-6…)]
- CVSS V3.1: *Unknown*,
- Vulners: Exploitation: True
CVE-2021-44228 \[[Vulners](vulners.com/cve/CVE-2021-4…)]
- CVSS V3.1: *10.0*,
- Vulners: Exploitation: True
Soft:
- siemens 6bk1602-0aa12-0tp0_firmware (<2.7.0)
CVE-2025-55182 \[[Vulners](vulners.com/cve/CVE-2025-5…)]
- CVSS V3.1: *10.0*,
- Vulners: Exploitation: True
Soft:
- facebook react (19.0.0, 19.1.0, 19.1.1, 19.2.0)
📚TTPs:
⚔️Tactics: 3
🛠️Technics: 0
🤖LLM extracted TTPs:`
T1005, T1027.010, T1059.006, T1059.007, T1078, T1082, T1105, T1190, T1213, T1572, ...
🧨IOCs:
- File: 4
- IP: 1
- Domain: 2
- Url: 8
- Email: 3
💽Software: nClaw , en, OpenClaw, PostgreSQL, trycloudflare, curl, nClaw
🔢Algorithms: base64
📜Programming Languages: python
#threatreport:
The SOCRadar Threat Research Team has identified a sophisticated Chinese cybercrime infrastructure that combines automated exploitation with structured orchestration and monetization methods. Central to this operation is a backend system known as ‘paperclip’ paired with an agent-based workflow system called OpenClaw, which allows operators to manage and execute cyber campaigns through organized missions.
The attack strategy hinges on extensive internet reconnaissance using tools like FOFA and 360Quake, where FOFA identifies high-value targets such as Web3 platforms, fintech services, and security vendors, while 360Quake conducts technical fingerprinting of vulnerable services. Once targets are selected, the attackers utilize custom Python scripts to automate exploitation processes. These scripts can execute commands like environment variable dumps, bypass web application firewalls (WAF), and execute actions in parallel across numerous targets, with the core aim being reliable remote code execution rather than merely detecting vulnerabilities.
Credential harvesting is facilitated through AI Keys stored in a PostgreSQL database. To maintain persistent access, the attackers have deployed various mechanisms including Cloudflare tunnels, P2P clients, and backdoors (d2 and pl), ensuring they can access their targets stealthily and redundantly. A particularly noteworthy aspect of their operations is the fileless execution chain designed to deploy command-and-control agents seamlessly, using specific Python commands to curl and execute payloads from URLs.
The orchestration of operations is meticulously structured, featuring stages such as planning, reconnaissance, validation, and reporting, all under human control, illustrating a deliberate integration of automation with manual oversight. The monetization of stolen data through blockchain intelligence APIs and Stripe validation allows attackers to analyze cryptocurrency addresses and test stolen Stripe keys for accounts with available balances, facilitating the targeting of high-value assets.
The infrastructure's scale is underscored by the notable preference for deploying lightweight backdoors compared to traditional webshells, indicating an evolutionary shift in cybercrime tactics towards more efficient and stealthy operations. Overall, this development signifies a broader trend in cybercrime towards highly organized, automated systems that effectively harmonize exploitation, extraction, and monetization, suggesting a critical need for evolving defensive strategies that account for these integrated methodologies.
English

#threatreport #LowCompleteness
Threat Brief: CVE-2026-41940: Critical cPanel & WHM Authentication Bypass Actively Exploited in the Wild | 02-05-2026
Source: catonetworks.com/blog/threat-br…
Key details below ↓
💀Threats:
Seo_poisoning_technique,
🎯Victims: Hosting providers, Website owners, Managed hosting customers, Organizations that rely on hosted web assets
🌐Geo: Japan, Ireland
🔓CVEs: CVE-2026-41940 \[[Vulners](vulners.com/cve/CVE-2026-4…)]
- CVSS V3.1: *9.8*,
- Vulners: Exploitation: True
Soft:
- cpanel (<86.0.41, <110.0.97, <118.0.63, <126.0.54, <130.0.19)
🤖LLM extracted TTPs:`
T1053.003, T1056.007, T1136, T1190, T1491.002, T1505.003, T1565.001, T1566, T1584.001
🧨IOCs:
- IP: 8
💽Software: cPanel
🔢Algorithms: base64
📜Programming Languages: javascript
#threatreport:
CVE-2026-41940 is a critical authentication bypass vulnerability affecting cPanel & WHM (WebHost Manager) versions released after 11.40, including related products such as DNSOnly and WP Squared. This vulnerability permits an unauthenticated remote attacker to gain unauthorized access to hosting control panels, which poses significant risks to hosting providers and website owners. The exploitation of this flaw can lead to unauthorized administrative access, manipulation of hosted content, database and email account access, new user creation, deployment of web shells, and other malicious activities. The wide prevalence of cPanel and WHM in managing numerous domains amplifies the potential impact of a single compromised server.
Diving into the technical specifics, the vulnerability allows attackers to exploit session handling mechanisms. When an attacker attempts to log in through the endpoint /login/?login_only=1, even a failed login results in the server creating a pre-authenticated session and returning a whostmgrsession cookie. Attackers can then utilize this behavior by injecting Base64-encoded data into the Authorization header, which corresponds to session attributes that can be written into the server-side session file. This manipulation not only enables unauthorized access but also allows the attacker to effectively bypass authentication through the subsequent reading of the modified session file.
The vulnerability has been assigned a critical severity rating with CVSS v3.1 scores of 9.8 and CVSS v4.0 scores of 9.3, categorizing it under CWE-306 for missing authentication. Patch releases have been made available by cPanel, and institutions are advised to implement these patches urgently. Additionally, during the interim period before patching, it is recommended to restrict inbound traffic to specific ports (2083, 2087, 2095, and 2096) as a protective measure.
Observed exploitation attempts have been detected, prompting proactive defenses from organizations like Cato, which has implemented intrusion prevention system (IPS) signatures to thwart these attacks. These measures include monitoring and virtual patching against the vulnerability. Ongoing surveillance by cybersecurity analysts is crucial given the possibility of post-exploitation abuse leveraging platforms affected by the vulnerability. The presence of approximately 1.5 million internet-exposed cPanel instances, based on Shodan data, highlights the urgency for organizations to secure their systems against CVE-2026-41940.

English

#threatreport #MediumCompleteness
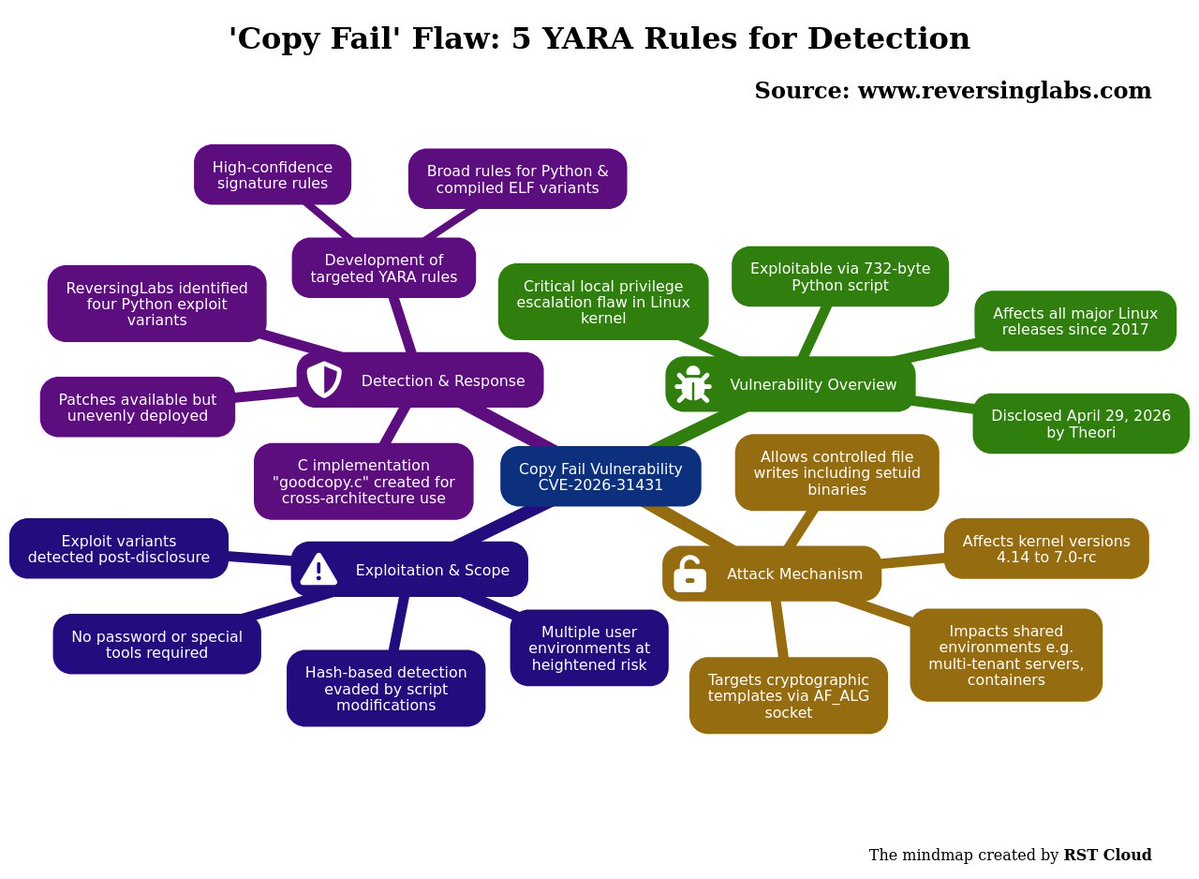
'Copy Fail' Flaw: 5 YARA Rules for Detection | 02-05-2026
Source: reversinglabs.com/blog/copy-fail…
Key details below ↓
💀Threats:
Copyfail_vuln,
🎯Victims: Server infrastructure, Cloud computing, Enterprise workloads, Multi tenant servers, Ci/cd pipelines, Container clusters
🔓CVEs: CVE-2026-31431 \[[Vulners](vulners.com/cve/CVE-2026-3…)]
- CVSS V3.1: *7.8*,
- Vulners: Exploitation: True
Soft:
- linux linux_kernel (<5.10.254, <5.15.204, <6.1.170, <6.6.137, <6.12.85)
📚TTPs:
⚔️Tactics: 2
🛠️Technics: 0
🤖LLM extracted TTPs:`
T1027, T1027.002, T1027.008, T1027.009, T1059.004, T1059.006, T1068, T1105, T1548.001, T1611, ...
🧨IOCs:
- File: 2
- Hash: 21
💽Software: Linux, Twitter, Ubuntu, Kubernetes, curl, PyInstaller
🔢Algorithms: aes, sha256, sha1, hmac, cbc
🔠Functions: splice, sendmsg
🗂️Win API: PIE
📜Programming Languages: javascript, python
💻Platforms: riscv64, amd64, arm
YARA: Found
#threatreport:
The Copy Fail vulnerability, assigned CVE-2026-31431, is a critical local privilege escalation flaw found in the Linux kernel and was disclosed by Theori on April 29, 2026. It affects all major Linux distributions released since 2017 and allows any user with a local account to gain full administrative control without the need for passwords or any special tools. The exploit is a minimal 732-byte Python script that can be reliably executed on any affected system.
The underlying mechanism of Copy Fail is a logic bug involving the kernel's support for cryptographic templates, specifically reachable through the AF_ALG socket interface. By manipulating this interface, an attacker can perform a controlled write operation that can affect essential files, including setuid binaries like /usr/bin/su. This exploit is exceptionally dangerous in environments where multiple users or workloads share the same kernel, such as multi-tenant servers and container clusters.
The scope of the vulnerability encompasses Linux kernel versions 4.14 through 7.0-rc. Although patches are available, they had not been deployed across all distributions at the time of the disclosure. The ease of exploitation means that systems remain exposed until they are updated. The attack can escalate quickly if an attacker already has access to the Linux environment.
ReversingLabs reported that they had identified several instances of the vulnerable exploit shortly after its public disclosure, including four distinct Python samples derived from the original proof of concept. These samples were variations of the initial script, exhibiting changes such as altered line endings or minor whitespace adjustments that did not influence their functionality. This variation indicates the limitations of hash-based detection methods, as the same underlying code can yield different hashes with trivial modifications.
In response, ReversingLabs developed targeted YARA rules to combat the Copy Fail threat. These ranged from high-confidence rules that detect exact matches of the original proof of concept to broader rules aimed at identifying variants and compiled ELF binaries associated with the same exploit. One notable derived work is a C implementation called goodcopy.c, which allows for targeting different architectures and includes enhanced cleanup measures to reset the page cache post-exploitation, thereby preventing follow-up attacks.
English

#tireport #ExtractedDiagrams
The key diagram for the report (ML Classifier):
windows: 9, chats: 2, code: 7, schema: 2, table: 1

English

#threatreport #MediumCompleteness
EtherRAT Distribution Spoofing Administrative Tools via GitHub Facades | 14-04-2026
Source: atos.net/en/lp/cybershi…
Key details below ↓
🧑💻Actors/Campaigns:
Lazarus
Contagious_interview
Muddywater
Oilrig
💀Threats:
Etherrat, Seo_poisoning_technique, Azcopy_tool, Dead_drop_technique, Procdump_tool, Bitvise_ssh_tool, Dameware_tool, Securecrt_tool, Superputty_tool, Screenconnect_tool, Nssm_tool, Etherhiding_technique, Tsundere,
🎯Victims: Enterprise administrators, Devops engineers, Security analysts, Corporate environments
🏭Industry: Financial
🌐Geo: North korean, Iranian
📚TTPs:
⚔️Tactics: 1
🛠️Technics: 0
🤖LLM extracted TTPs:`
T1001.003, T1027, T1027.010, T1027.013, T1036, T1059.003, T1059.007, T1070.004, T1071.001, T1102.001, ...
🧨IOCs:
- File: 8
- Path: 2
- Url: 1
- Coin: 2
💽Software: PsExec, Azure Data Explorer, Sysinternals, Process Explorer, FSLogix, Node.js, curl, Etherscan
🪙Crypto: ethereum
🔢Algorithms: aes-256-cbc, zip
📜Programming Languages: javascript
#threatreport:
In March 2026, a highly sophisticated cyber threat campaign was discovered by the Atos Threat Research Center, which specifically targets high-privilege IT personnel like enterprise administrators and security analysts. The attackers employ a dual-layered GitHub repository distribution method, leveraging Search Engine Optimization (SEO) poisoning to manipulate search results for administrative utilities, directing victims to malicious MSI installers masquerading as legitimate tools. This approach maximizes the campaign's resilience, allowing the attackers to evade takedown efforts by keeping the malicious code on secondary repositories while the primary facade remains benign and SEO-optimized.
The malware delivered through this campaign, identified as EtherRAT, functions as a Remote Access Trojan (RAT) designed for stealth and persistence. It utilizes decoy installers that impersonate essential infrastructure tools such as PsExec, AzCopy, and Sysmon, targeting systems with elevated permissions to facilitate lateral movement within corporate networks once compromised. This strategic choice is coupled with a psychological approach, as security professionals might unwittingly download these malicious tools while diagnosing other potential issues.
A critical feature of the EtherRAT is its decentralized Command and Control (C2) mechanism, which relies on blockchain technology. Upon execution, the malware queries a public Ethereum RPC endpoint associated with a specific smart contract address to retrieve its C2 server address, enabling the attackers to change their command infrastructure without needing to re-deploy malware across already infected systems. This method enhances resilience against traditional countermeasures aimed at blocking specific domains or IP addresses.
The malware is structured in multiple stages, beginning with an obfuscated dropper script executed with high privileges, which prepares the environment for subsequent stages executed in memory. The RAT hides within legitimate Windows processes, ensuring it remains unobtrusive, and performs operations like communication with the C2 server through disguised requests, making detection challenging. This low-profile operational tactic, combined with its reliance on periodically querying the Ethereum blockchain for C2 addresses, enables sustained control and management of infections without noticeable disruption.
Atos researchers have linked this campaign to previous operations by state-sponsored actors, notably the Lazarus Group, indicating a more complex and methodical approach focused on long-term infiltration rather than immediate exfiltration of data. The news of this campaign underscores a significant evolution in cyber threat tactics, where resilience, evasion, and operational patience take precedence over conventional, high-velocity malware operations.
Consequently, proactive measures are being taken to disrupt this campaign through formal takedown actions targeting the identified malicious schemes, aiming to hinder further exploitation and protect enterprise environments from these advanced threats.

English

#threatreport #LowCompleteness
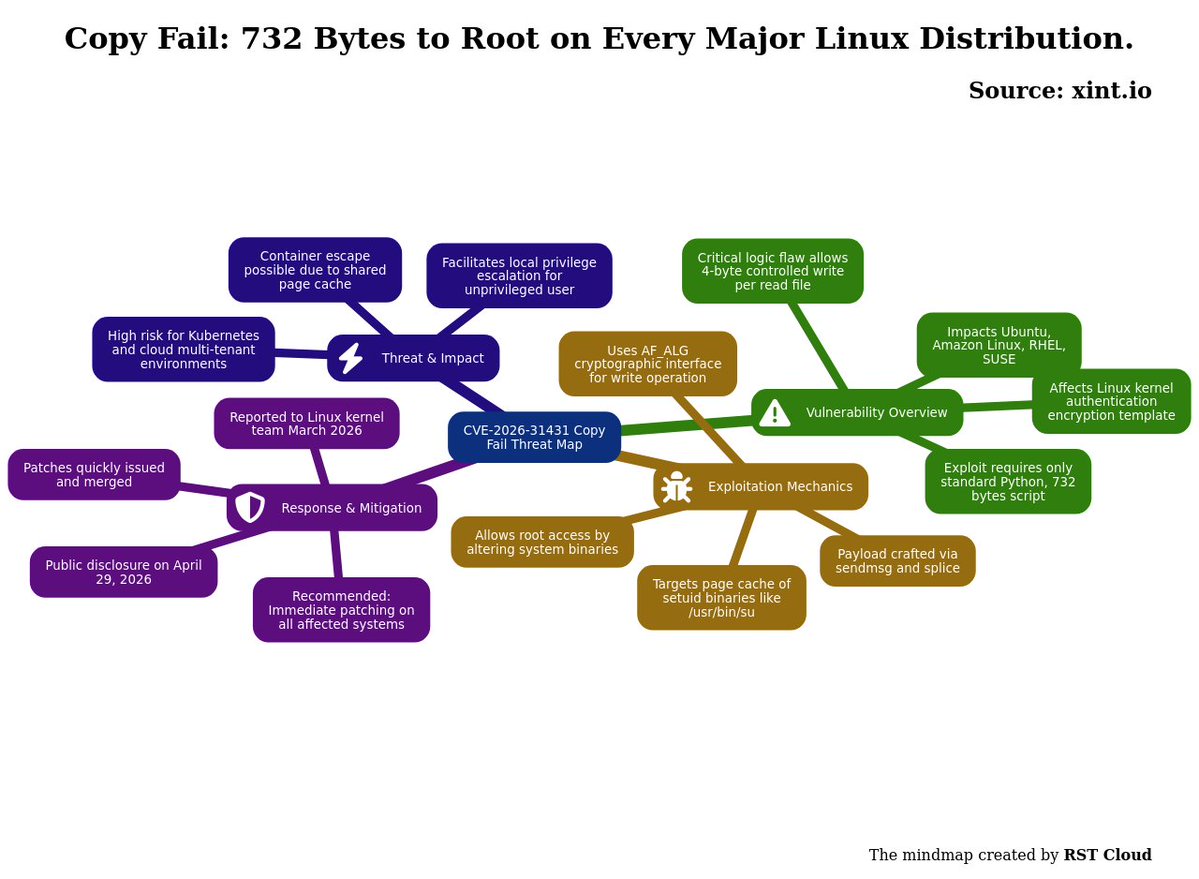
Copy Fail: 732 Bytes to Root on Every Major Linux Distribution. | 30-04-2026
Source: xint.io/blog/copy-fail…
Key details below ↓
💀Threats:
Copyfail_vuln, Dirty_cow_vuln, Dirty_pipe_vuln,
🎯Victims: Linux distributions, Kubernetes platforms, Cloud computing
🔓CVEs: CVE-2016-5195 \[[Vulners](vulners.com/cve/CVE-2016-5…)]
- CVSS V3.1: *7.0*,
- Vulners: Exploitation: True
Soft:
- canonical ubuntu_linux (12.04, 14.04, 16.04, 16.10)
CVE-2026-31431 \[[Vulners](vulners.com/cve/CVE-2026-3…)]
- CVSS V3.1: *7.8*,
- Vulners: Exploitation: True
Soft:
- linux linux_kernel (<5.10.254, <5.15.204, <6.1.170, <6.6.137, <6.12.85)
CVE-2022-0847 \[[Vulners](vulners.com/cve/CVE-2022-0…)]
- CVSS V3.1: *7.8*,
- Vulners: Exploitation: True
Soft:
- linux linux_kernel (<5.10.102, <5.15.25, <5.16.11)
📚TTPs:
⚔️Tactics: 2
🛠️Technics: 0
🤖LLM extracted TTPs:`
T1059.006, T1068, T1548.001, T1611
🧨IOCs:
- File: 5
💽Software: Linux, Ubuntu, Kubernetes, Android
🔢Algorithms: aes, hmac, sha256, cbc
🔠Functions: splice, read, mmap, execve, recvmsg, sg_chain, crypto_authenc_esn_decrypt, crypto_authenc_esn_decrypt_tail, sendmsg, recv, ...
📜Programming Languages: python
#threatreport:
CVE-2026-31431, identified as "Copy Fail," is a critical logic vulnerability in the Linux kernel’s authentication encryption template, which enables an unprivileged local user to perform a controlled 4-byte write into the page cache of any readable file. This vulnerability was disclosed by Xint Code and is applicable across all major Linux distributions, including Ubuntu, Amazon Linux, RHEL, and SUSE. The exploit can be executed with a simple 732-byte Python script, leveraging functionalities from standard library modules, making it particularly notable for its simplicity and portability.
The root of "Copy Fail" lies within the Linux kernel’s handling of cryptographic operations combined with page cache management. Specifically, the exploit manipulates the AF_ALG interface, widely used for cryptography, to execute a deterministic write that alters the page cache without racing conditions or erroneous timing windows. This straightforward approach distinguishes it from previous privilege escalation vulnerabilities like "Dirty Cow" and "Dirty Pipe," which involved more complex conditions and specific version dependencies.
The mechanism of exploitation involves a targeted write into the page cache of a setuid binary, specifically /usr/bin/su, which is present in the major distributions since 2017. The attack operates by constructing a payload that is sent in chunks through sendmsg() and splice(), where particular parameters are carefully chosen to ensure the payload is inserted into the system's binaries. Once the payload is injected, executing the modified binary grants root access.
Additionally, the implications of this vulnerability extend beyond mere local privilege escalation; the shared nature of the page cache allows for a potential container escape, impacting Kubernetes environments substantially. Therefore, Copy Fail poses a significant risk, especially in multi-tenant cloud infrastructures where a compromised container could lead to broader system access.
The vulnerability was reported to the Linux kernel security team in March 2026 and swiftly acknowledged, with patches proposed and committed to the mainline kernel shortly thereafter, demonstrating a proactive response to mitigating the risk. Public disclosure occurred on April 29, 2026, following the establishment of an effective remediation timeline.
English

#threatreport #LowCompleteness
Defending Against CORDIAL SPIDER and SNARKY SPIDER with Falcon Shield | 02-05-2026
Source: crowdstrike.com/en-us/blog/def…
Key details below ↓
🧑💻Actors/Campaigns:
Cordial_spider (🧠motivation: information_theft)
Snarky_spider (🧠motivation: information_theft)
💀Threats:
Aitm_technique, Residential_proxy_technique, Nsocks_tool,
🎯Victims: Software as a service, Information technology
📚TTPs:
⚔️Tactics: 5
🛠️Technics: 0
💽Software: Android, Linux, macOS, QEMU, HubSpot
💻Platforms: intel
#threatreport:
Since October 2025, CrowdStrike's Counter Adversary Operations has reported a significant evolution in cyberattack methods, particularly through the activities of two adversarial groups, CORDIAL SPIDER and SNARKY SPIDER. These groups primarily execute fast-paced, SaaS-oriented attacks that effectively evade traditional endpoint security measures. Utilizing voice phishing, or vishing, they manipulate victims into visiting adversary-in-the-middle (AiTM) pages designed to look like legitimate single sign-on (SSO) portals; this enables them to harvest authentication credentials and session tokens directly as users log in.
These AiTM pages are crafted to closely resemble genuine login interfaces, tricking victims by offering an experience consistent with legitimate access. This tactic allows them to leverage trusted SaaS environments while minimizing detection risk. Upon gaining initial access, these threat actors often establish persistence by registering attacker-controlled multi-factor authentication (MFA) devices. They frequently remove existing MFA configurations before adding their own, with SNARKY SPIDER favoring a Genymobile Android emulator for its MFA capabilities, while CORDIAL SPIDER employs a mix of mobile devices and a QEMU-based Windows setup.
To evade detection further, SNARKY SPIDER implements a strategy to suppress any notifications related to compromised accounts. This involves creating inbox rules that automatically delete security alerts and correspondence containing keywords associated with suspicious activities. This tactic diminishes the likelihood of discovery and enables prolonged unauthorized access.
The main objective for these groups centers on large-scale data exfiltration from various SaaS platforms, including SharePoint and Google Workspace. They have been observed conducting targeted searches to uncover sensitive data, indicative of their focus on critical business information. To facilitate their operations without raising alarms, they utilize commercial VPN services and residential proxies, which obscure their traffic and make it appear normal.
Despite some organizations enhancing their endpoint defenses, the nature of these attacks highlights a detection gap, particularly at the identity provider (IdP) and SaaS levels. Notably, CrowdStrike's Falcon Shield is designed to address this gap by employing advanced anomaly detection techniques that distinguish between legitimate and malicious activities. The tool maintains extensive visibility across the SaaS stack and incorporates understanding derived from user behaviors and specific platform configurations. Falcon Shield enhances this capability through the classification of anonymization services and monitoring of access via non-enterprise infrastructure, thus aiming to provide precise attributions of suspicious activities.

English
