Rumata888
261 posts

Rumata888
@rumata888
Security Team Lead at @aztecnetwork. @CTFZone organizer. Love cryptography, fuzzing, breaking systems. Views are my own.

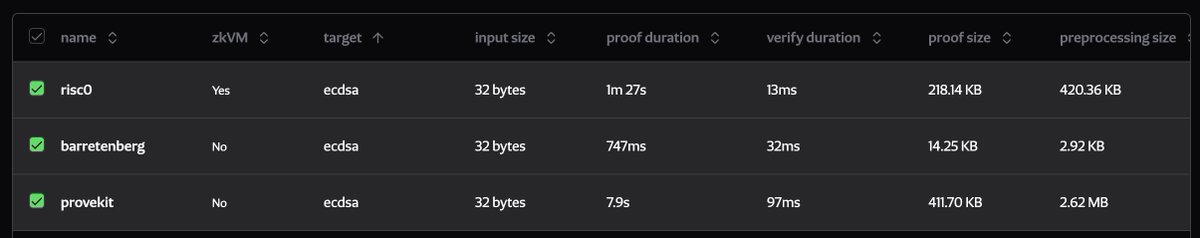
Aztec can do exactly this. All of it. I’m so happy. I can’t stress how exactly Aztec can do this. Fast client-side proving on desktop and mobile, well under 1GB RAM. Native, private account abstraction is already built into Aztec. Think of a way to authenticate a user… Eth signature / Safe multisig / Sign in with google / email / password=Hunter2 / a live video of your cat / a signature from Vitalik telling you he’s proud of you? You can build Aztec smart contracts that can do this today. You’ll be able to provide your users with familiar and private access to Ethereum.












CertiK recently identified a series of critical vulnerabilities in @krakenfx exchange which could potentially lead to hundreds of millions of dollars in losses. Starting from a finding in @krakenfx's deposit system where it may fail to differentiate between different internal transfer statuses, we conducted a thorough investigation with three key questions: 1/ Can a malicious actor fabricate a deposit transaction to a Kraken account? 2/ Can a malicious actor withdraw fabricated funds? 3/ What risk controls and asset protection might be triggered by a large withdrawal request? According to our testing result: The Kraken exchange failed all these tests, indicating that Kraken’s defense in-depth-system is compromised on multiple fronts. Millions of dollars can be deposited to ANY Kraken account. A huge amount of fabricated crypto (worth more than 1M+ USD) can be withdrawn from the account and converted into valid cryptos. Worse yet, no alerts were triggered during the multi-day testing period. Kraken only responded and locked the test accounts days after we officially reported the incident. Upon discovery, we informed Kraken, whose security team classified it as Critical: the most serious classification level at Kraken. After initial successful conversions on identifying and fixing the vulnerability, Kraken’s security operation team has THREATENED individual CertiK employees to repay a MISMATCHED amount of crypto in an UNREASONABLE time even WITHOUT providing repayment addresses. In the spirit of transparency and our commitment to the Web3 community, we are going public to protect all users' security. We urge @krakenfx to cease any threats against whitehat hackers. Together, we can face risks and safeguard the future of Web3. #Web3 #Security #Transparency